Windows Security Emergency Patch to fix Flame loophole
You have probably heard about Flame, or Flamer, by now, a highly sophisticated and targeted malware that ran undetected for more than a year before it was discovered by security experts. As of now, many security vendors have updated their programs and tools to detect the malware, and we have shown you how you can scan your system for Flame to remove the malware if it is indeed installed on it.
A Microsoft analysis of the malware discovered that "some components of the malware have been signed by certificates that allow software to appear as if it was produced by Microsoft", and while Flame itself should not be an issue anymore for the majority of users, other malware that uses a more widespread approach could use the loophole to exploit Windows PCs.
According to Microsoft, the developers of Flame exploited "an older cryptography algorithm" to sign code as "if it originated from Microsoft". The Terminal Server Licensing Server which allowed customers to authorize remote desktop services, used that algorithm.
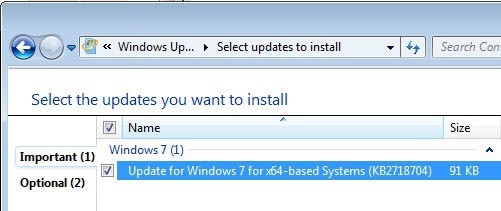
Microsoft therefor has released an update that is available on Windows Update and on the Microsoft Support website.
The update is available for all recent 32-bit and 64-bit client and server editions of Windows, from Windows XP and Windows Server 2003 all the way to Windows 7 and Windows Server 2008 R2. It has been released with an important rating, at least for 64-bit versions of Windows 7. Users are nevertheless asked to install the patch as soon as possible on their system. A restart is not required.
Microsoft in addition has changed the certificate issuing of the Terminal Server Licensing Service which can no longer issue certificates that allow code to be signed.
System administrators and security researchers who are interested in additional background information find additional information in a post at Microsoft's Security Research and Defense blog.
Advertisement















I wonder if this update will even install on an infected machine.
Anyone know if it removes the infection first on infected machines?
Patching the code will neutralize this malware package but without removal it could phone home and get it’s own “update”.
No, it doesn’t clean Flame. This patch just black list 3 Microsoft own CAs and fixes Terminal Server Licensing Service.
Thanks for the info., Martin. Downloaded and installed.
Although I ran the BitDefender tool that you posted here a few days ago and my system was/still is clean, this is an additional security measure!