Firefox 85.0.1 fixes a critical security issue and bugs
Mozilla released Firefox 85.0.1 Stable and Firefox ESR 78.7.1 to the public on February 5, 2021. The new browser versions are already available and will be installed automatically on most systems thanks to the build-in updating functionality of the browsers.
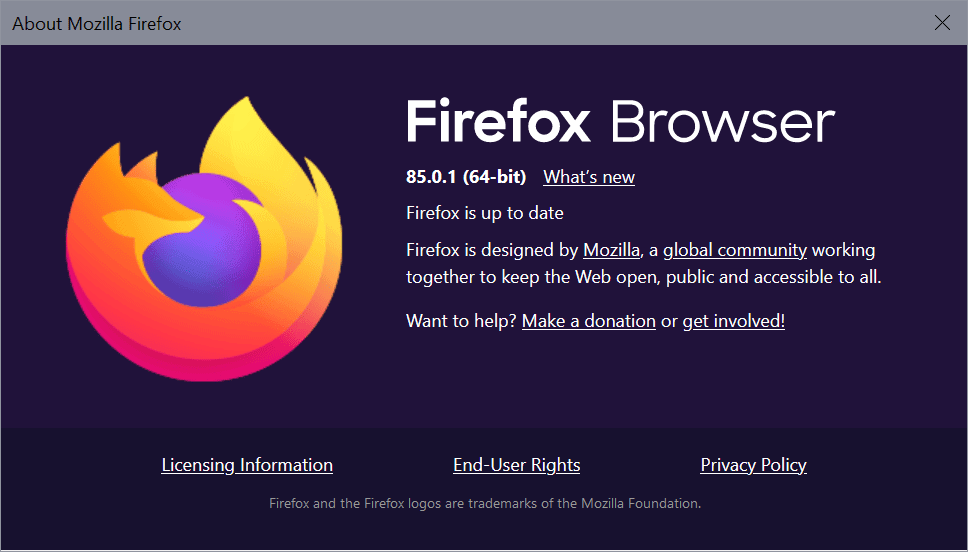
Standalone downloads are provided on the Mozilla website. Select Menu > Help > About Firefox to display the currently installed version of the browser.
Firefox 85, the last major release of the browser, was released on January 26, 2021.
Firefox 85.0.1 release information
Firefox 85.0.1 and Firefox ESR 78.7.1 are security updates first and foremost. Mozilla patched a single security issue in both versions of the browser.
The vulnerability, Buffer overflow in depth pitch calculations for compressed textures, has received the severity rating critical, the highest rating available. Mozilla notes that the issue affects Firefox running on Windows machines only, all other supported operating systems are not affected by the issue.
Firefox 85.0.1 fixes five non-security related bugs in the browser next to that.
Two address crashes of the browser: the first when authenticating to websites using SPNEGO on macOS devices with Apple Silicon CPUs, the second in case of an unexpected Cache API state.
Linux users who tried to launch Flatpack or rpm Zoom client from Flatpack in Firefox 85 noticed that they could not do so anymore. The third fix of the new release addresses that issue by fixing external URL scheme handlers when using the Firefox Flatpack.
Mozilla engineers implemented a change in Firefox 85.0.1 that prevents access to NTFS special paths when using the browser; Mozilla notes that the access could lead to filesystem corruption.
The final fix prevents Firefox from printing an extra sheet of paper at the end of certain documents. The bug reporter on Bugzilla@Mozilla experienced the issue when printing PDF documents with the setting layout.display-list.improve-fragmentation set to enabled.
You find the official release notes here.
Firefox 85.0.1 fixes several issues that affect specific operating systems only. The security fix affects Windows, one of the crashes only Mac devices with Apple Silicon processors, and the external URL scheme handlers only Linux systems














Finally able to dig up a blog with an explanation on why the boolean string for encrypted SNI in stable FF 85. Mozilla was removed. Encrypting only the SNI extension provided incomplete protection and so they’re implementing encrypted client hello (ECH) to replace ESNI.
Mozilla and their “trr” team should try harder focusing on broadcasting important issues to their users. So far as I can tell, it’s been an uncoordinated effort. And talking about boolean, the searches made on Mozzilla Support necessitate boolean searches. It should’nt have to be that way to narrow down hundreds of results.
https://blog.mozilla.org/security/2021/01/07/encrypted-client-hello-the-future-of-esni-in-firefox/
@Martin Brinkmann A few questions.
Just noticed the boolean string ‘network.security.ensi.enabled’ was removed in Version 85.0.2. Without knowing what potential consequences could result by manually adding the encrypted ENSI boolean script back in using about:config, what exactly would be the risk factor involved here? Can manually adding ensi be safely reset by just removing the string if after adding the feature it had an affect on the normal operation of FF?
There doesn’t appear to be any published info concerning why the ensi feature was removed. Could it have been because this recent security fix resulted in a temporary removal but the boolean string is planned to be added back in during a future security update ?
The “latest security patches” that apply to Firefox will inevitably also apply to “TorBrowser, Thunderbird, SeaMonkey, Pale Moon, Basilisk, Waterfox, Waterfox Classic” that use Firefox as a platform.
Pale Moon
Version 29.0.1 (64-bit)
User Agent Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0) Gecko/20100101 Goanna/4.8 Firefox/68.0 PaleMoon/29.0.1
OS Windows_NT 10.0
https://www.palemoon.org/releasenotes.shtml
Release notes
v29.0.1 (2021-02-06)
This is a security and stability update.
Basilisk
Version 52.9.2021.02.06 (64-bit)
User Agent Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0) Gecko/20100101 Goanna/4.8 Firefox/68.0 Basilisk/20210206
OS Windows_NT 10.0
https://www.basilisk-browser.org/releasenotes.shtml
Release notes
These release notes are summaries of the most important changes for public releases.
v2021.02.06 Published 2021-02-06
This is a development, bugfix and security update.
Waterfox
Version G3.1.0
User Agent Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:78.0) Gecko/20100101 Firefox/78.0 Waterfox/78.7.0
OS Windows_NT 10.0
https://www.waterfox.net/blog/waterfox-G3.1.0/
Updated to Gecko esr78.7 (includes security patches)
Waterfox Classic
Version 2021.01.1
User Agent Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:56.0) Gecko/20100101 Firefox/56.0 Waterfox/56.4
OS Windows_NT 10.0
https://www.waterfox.net/blog/waterfox-2021.01-release/
Latest security patches, backported from Firefox ESR 78.7+
Tor Browser
Version 10.0.11 (Firefox 78.7.1esr)
User Agent Mozilla/5.0 (Windows NT 10.0; rv:78.0) Gecko/20100101 Firefox/78.0
OS Windows_NT 10.0
https://blog.torproject.org/new-release-tor-browser-10011
This version updates Firefox to 78.7.1esr for Windows. This release includes important security updates to Firefox.
SeaMonkey
Version 2.53.6
User Agent Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:60.0) Gecko/20100101 Firefox/60.0 SeaMonkey/2.53.6
OS Windows_NT 10.0
https://www.seamonkey-project.org/releases/seamonkey2.53.6/
Additional important security fixes up to Current Firefox 78.6 ESR and a few enhancements have been backported.
Thunderbird
Version 78.7.1
User Agent Mozilla/5.0 (Windows NT 10.0; rv:78.0) Gecko/20100101 Firefox/78.0
OS Windows_NT 10.0
https://www.thunderbird.net/en-US/thunderbird/78.7.1/releasenotes/?uri=/thunderbird/releasenotes/&locale=en-US&version=78.7.1&channel=release&os=WINNT&buildid=20210203182138
End users tend to express negative opinions about updates for applying “Security Patches”, but not only Mozilla but also other product developers and providers recognize the need for “Security Patches”.
Things can never be “perfection”.
For more than 4.6 billion years since the creation of the earth, even living things are destined for “evolution and selection.”
After all, because it is a technology created by humans, there is no end to corrections and improvements.
Whatever the security bug fix did, it affected the encrypted ESNI features (using Cloudflare’s browser test, with Firefox 85.0.1 it fails the Encrypted ESNI test. In some cases, it may remove the ‘network.security.esni.enabled’ boolean script setting in “about:config” settings.
FYI, Firefox 85.0.2 is out today !
>>Mozilla engineers implemented a change in Firefox 85.0.1 that prevents access to NTFS special
>>paths when using the browser; Mozilla notes that the access could lead to filesystem corruption.
Isn’t this a Windows 10 only problem? If it is so, they should specify it.
> Isn’t this a Windows 10 only problem?
No, it’s a particularly nasty NTFS bug that affects Windows going back to XP at least:
https://www.bleepingcomputer.com/news/security/windows-10-bug-corrupts-your-hard-drive-on-seeing-this-files-icon/
Needs to be fixed by Microsoft ASAP!
There is a temporary fix for this issue on Bleeping Computer –
https://www.bleepingcomputer.com/news/microsoft/windows-10-ntfs-corruption-bug-gets-unofficial-temporary-fix/
Does anyone else lots of trouble getting Google Duo to work properly in Firefox? I’m getting calls where pressing the ‘Accept’ button doesn’t do anything – wondering if this is a recent bug…
I’ve read that chrome also made an urgent update in version 88.0.4324.150
for some critical security fix they call CVE-2021-21148 (zero-day vulnerability). they only say it was an active threat that been widely used.
This particular CVE fix has now been rolled out to the Kiwi browser for Android too thankfully.
Another critical security bug:
https://www.mozilla.org/en-US/security/advisories/mfsa2021-06/
Critical level means that “Vulnerability can be used to run attacker code and install software, requiring no user interaction beyond normal browsing.”:
https://www.mozilla.org/en-US/security/advisories/
They never say for how long the security hole existed. It existed in the browser until it was fixed. This one is not the exception, they find some or high level ones at almost every release. Meaning there are many more that are inside right now and that *they* haven’t found yet, but *others* have. I believe that Chrome has the same problem.
Add to that that those companies do probably disclose those bugs to the NSA for exploitation against us before fixing them.
They have no real incentive to be more cautious with security before updates, all the competitors have the same problem, and in fact the more bugged, the more dependent we are on their updates and the more work it is to maintain an ethical fork.
So when these Mozilla/Google bastards tell us that we have to accept their software as is including all their own corporate malware features because according to them “forks are not secure because fewer eyes are looking for security bugs”, in spite of them getting security patches from upstream, do not trust them. All browsers are security nightmares, the most likely to be attacked are the most used ones, so we’d better use ungoogled and unmozilla’d ones that at least we know won’t contain Google and Mozilla’s own malware components.
Blah blah blah…………………..
What exactly is preventing YOU from coding, developing, writing, creating YOUR own browser, OS, or anything else for that matter? Lack of intelligence? Lack of skills?
Most likely, it’s the simple fact that it’s so much EASIER to condemn, criticize or complain about what others are doing or have done.
+ [Editor: removed, please no personal attacks]
@ Anonymous
Fair comment.
At least you are even handed and did not write a chapter of “War and Peace” with all sorts of links to obscure articles about Firefox tucked away on remote corners of the Internet.
Thank you. Mind you, bastards was not strong enough :)
You can run Fx in sandboxie-plus which is free now.
How hwrd is it to own zoom these days?
You can zoom any picture you want these days for free.