Check whether your PC is infected with the Emotet malware
The malware Emotet was detected for the first time in 2014. Back then, it was designed as a banking trojan to steal sensitive information. The malware evolved over time and added more malicious activity such as spamming to its arsenal through "loading" functionality.
A loader is designed to gain access to a system to load additional payloads on the system for malicious activities. Emotet uses command and control servers to receive updates, and it contains several mechanisms to avoid detection.
Emotet continues to be a threat thanks to built-in updating capabilities. The malware's last reemergence was detected in July 2020.
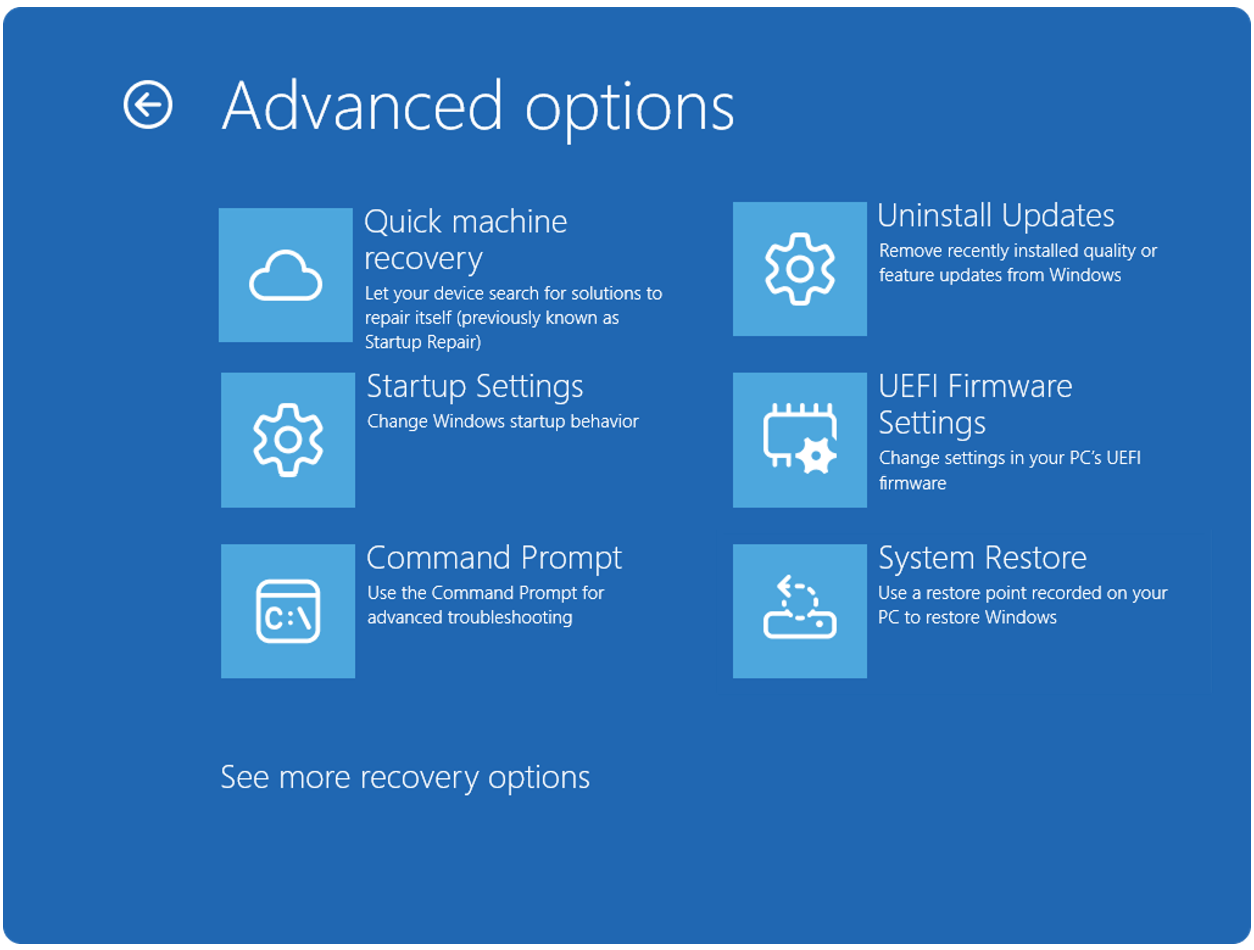
Windows users who want to find out if a Windows PC is infected with Emotet have several options. Antivirus solutions, e.g. Malwarebytes or Windows Defender, detect Emotet and prevent it from attacking the system successfully.
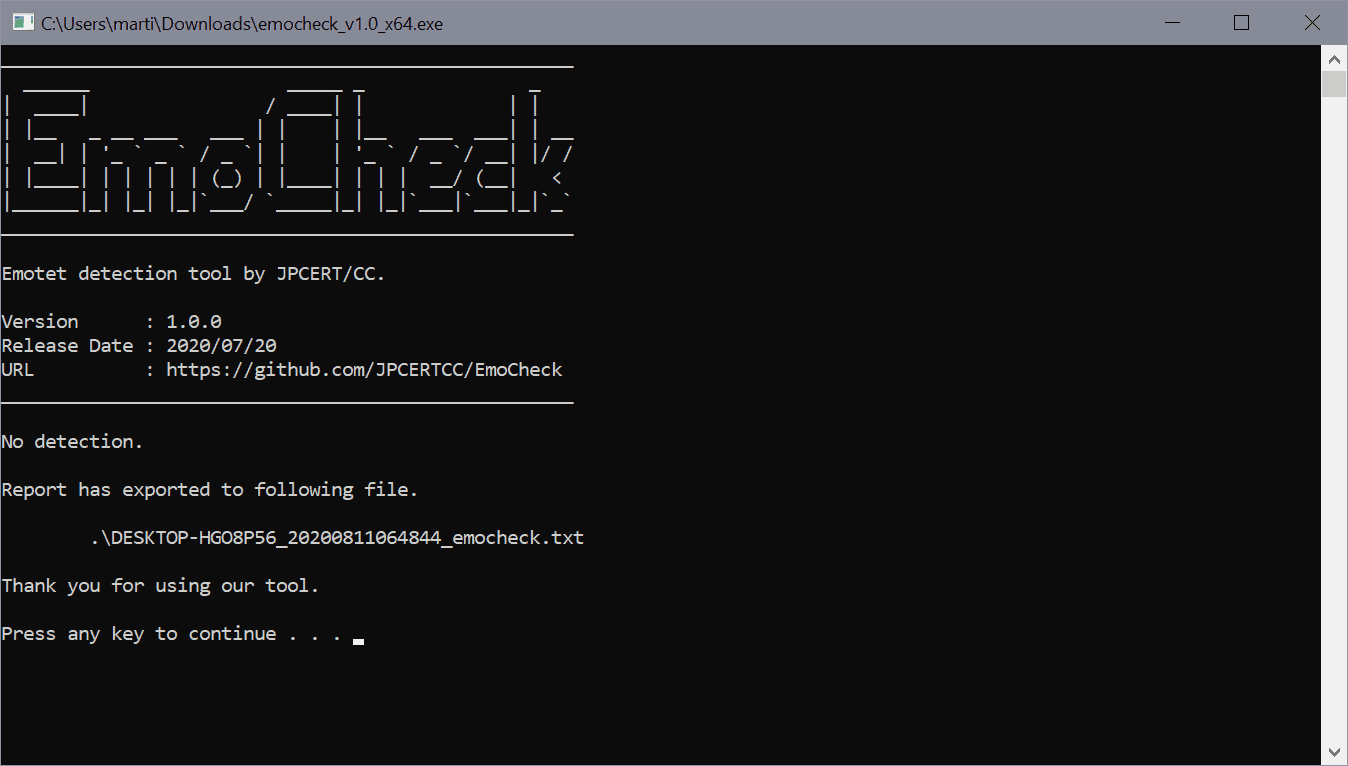
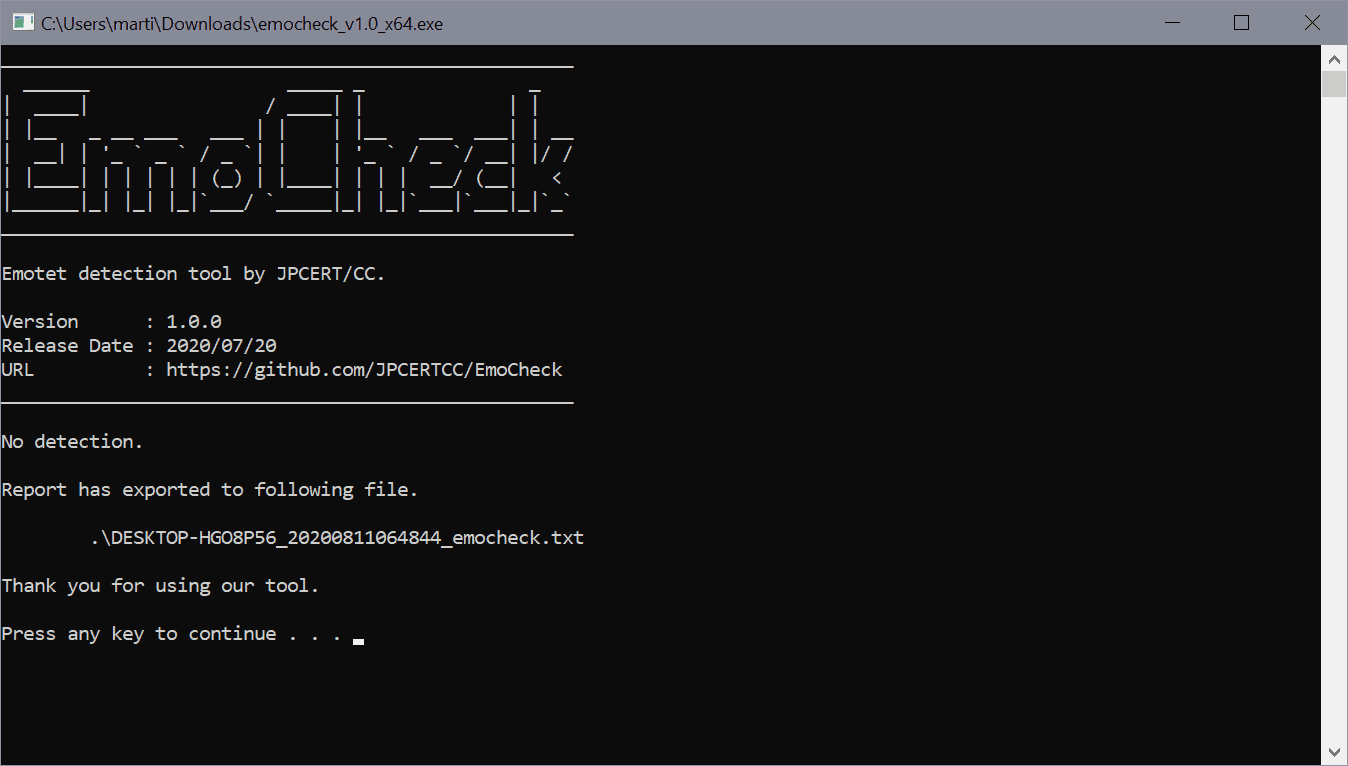
You may also run the open source tool EmoCheck if you just want to find out if a system is infected.
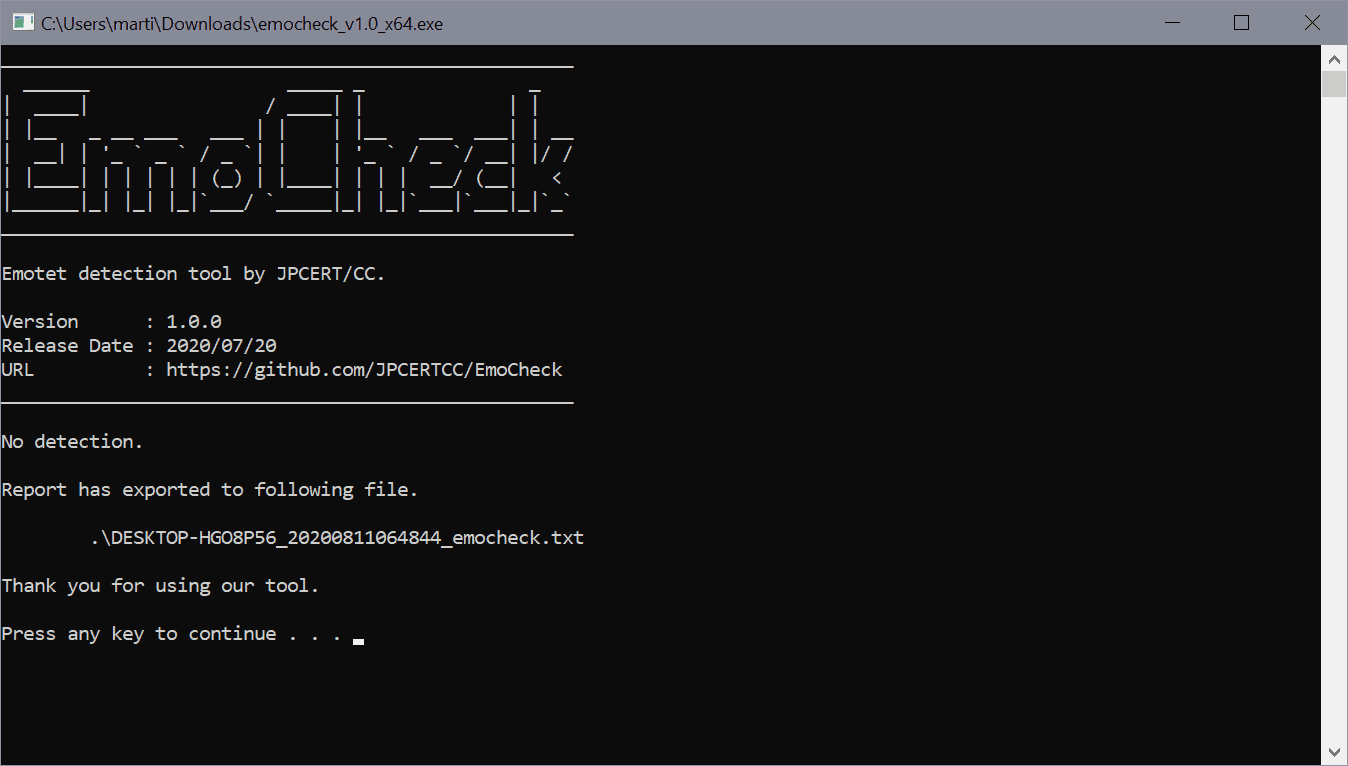
The portable tool scans the system for Emotet characteristics to reveal if it is infected. All it takes is to download the 32-bit or 64-bit version of EmoCheck from the GitHub project site and run it on a Windows system.
The program displays the result of the scan in the interface and saves a text log file on the system as well. You can also run it from the command line using parameters such as /quiet, /json, or /output path, to run the program without console output, export the data as a JSON file, or change the default output directory.
The developer explains how EmoCheck detects the Emotet malware on GitHub, and what the different program versions added.
(v0.0.1)
Emotet generates their process name from a specific word dictionary and C drive serial number. EmoCheck scans the running process on the host, and find Emotet process from their process name.(added in v0.0.2)
Emotet keeps their encoded process name in a specific registry key. EmoCheck looks up and decode the registry value, and find it from the process list. Code Signing with Microsoft Authenticode.(added in v1.0)
Support the April 2020 updated of Emotet.
Obfuscated code.
Closing Words
EmoCheck offers a quick way to find out if a Windows system is infected by the Emotet malware. You don't need the program if your resident antivirus solution detects all the different iterations of the malware, as the system is protected against it in this case.
If you are not certain if that is the case, you may run EmoCheck to find out if the system is infected or not. First thing to do if the system is infected is to disconnect it from the network/Internet to remove the malware afterwards using an antivirus solution that detects and cleans it.
Now You: Which security software do you use, and why?













Most users in the Netherlands at least use their mobile for online banking.
I can’t imagine a use for a program that detects only one virus among the many that exist. It’s like a dictionary with only one word.
ESET flagged, quarantined, and I OKed deletion of emotet on one of my PCs when I was running the July update for the Adobe Flash Player a month ago. That was my sign that it was time to remove Flash Player from all of our PCs. : )
I use no security software with Windows 7 & ESU.
Hello:
I use Malwarebytes (Premium); Microsoft’s native Windows Defender Security Center and Acronis’ Ransomware protection.
I haveen be using these in tandem for a few years now . . . and do far so good!
I stopped using the free standalone Anti-Virus programs a long time ago . . . not really effective these days, anyway.
I do NOT miss these!
i
Eset.
Seems any decent AV would detect emotet, not going to run this.
“Which security software do you use, and why?â€
Eset internet security (Because of the reason that free antivirus (combined with a firewall, the results get even worse if that’s already possible) over the last few decades at least gave and still give a very bad result, I will never use them..)
I use specific Eset internet security because there always high in all rankings.
Personally I think that Kaspersky’s total security is pretty good too.
Btw Windows defender beats eset and as computer technician i saw a lot of computers with eset compromised…
Interesting, I’ve been doing this for 20 years and my experience has been the exact opposite of yours.
Anonymous,
Which Eset version do you refer to?
What I notice from most users I help, which started in the period with ZX81, commodore pet, apple II, Epson Hx20, HP80, etc, is that those so-called “Free” (Watch out those “free antivirus” are not really free) antivirus are always causing much more problems than their opponents the paid versions.
When I compare the hours I (And other people from the same firm and also from other firms) are spending with the so-called “Free” and paid versions its always twice as much.
I mean not only the instal time, the tuning time, the repair time but also explaining time.
I am sorry that I can’t find a link right now but when I find the link I wanted to post here I will catch up with you.
You found viruses for the ZX 81 ? :)
I m not talking about the past but let s say in the last 2 years i think Windows defender is a good choise, of course nothing is really free u pay in exchange of ur data like everything including ur paid av, btw i saw a lot of pc with eset antivirus and powershell scripts running in background collecting data with no warning…
Aaaaaand we can trust this developer becaaaaause….? Yeah it’s on GitHub where the code can be reviewed by anyone, sure.. But HAS anyone reviewed it? What if running this tool actually infects you with Emotet? There, I said it. Now go quick and download/run it before it gets taken down. =)
I trust it, because the source is available, it’s by a known industry entity (Japan Computer Emergency Response Team’s Coordination Center), and both kaspersky and bitdefender gives the binary an a-ok.
Same here, but internet security
“Which security software do you use, and why?”
Using Kaspersky A/V (paid).
The best A/V for years.