Could VeraCrypt become the next TrueCrypt?
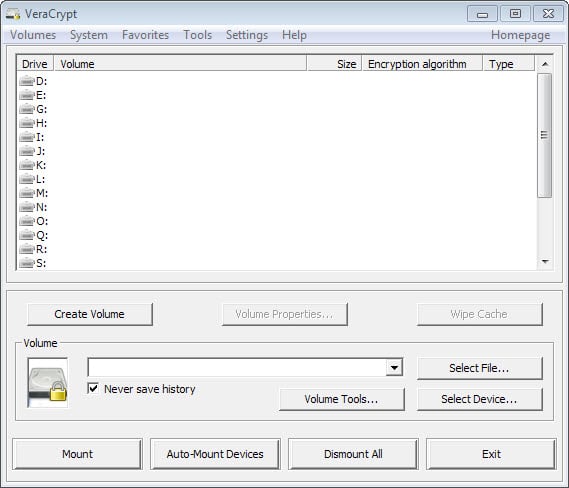
VeraCrypt is an encryption software that is a fork of TrueCrypt. What is meant by that is that it is based on TrueCrypt source without being a mere clone of the program.
Since it is based on the popular application, it offers pretty much the same feature set that TrueCrypt makes available. This includes creating encrypted containers on hard drives and encrypting entire partitions or drives including the system partition.
According to IDRIX, the company behind VeraCrypt, it adds security enhancements to the algorithm that "makes it immune to new developments in brute-force attacks".
For example, when the system partition is encrypted, TrueCrypt uses PBKDF2-RIPEMD160 with 1000 iterations whereas in VeraCrypt we use 327661. And for standard containers and other partitions, TrueCrypt uses at most 2000 iterations but VeraCrypt uses 655331 for RIPEMD160 and 500000 iterations for SHA-2 and Whirlpool.
The downside to those changes is that it takes longer to open (read mount) encrypted partitions. The actual performance of mounted drives is however not affected by this.
Another downside is that the storage format is not compatible with TrueCrypt's storage format which means that you will still have to find a way to convert TrueCrypt partitions to VeraCrypt format.
The stop of TrueCrypt development affects VeraCrypt. Since it is based on TrueCrypt source,it is now up to IDRIX to continue development of the application. Previously, the company could use new features introduced by the TrueCrypt team which is not an option anymore at the time of writing.
The "TrueCrypt is insecure" message may also affect user perception or at least doubt when it comes to VeraCrypt. While the -- ongoing -- audit has not found any major security issues in its first stage, it may still keep some users from giving VeraCrypt a true, considering that it is based on the same source as TrueCrypt.
Mounir Idrassi, IDRIX founder and developer behind VeraCrypt on the other hand does not seem devastated by TrueCrypt's end of life statement. Quite the contrary; he told us that he had big plans for the application and believes that development could continue more quickly than before.
A Mac OS X and Linux version will be released this summer for instance, and there is development ongoing to implement SHA-2 key derivation for the encryption of system partitions.
Idrassi believes that VeraCrypt will benefit from TrueCrypt's security audit to correct any weaknesses or issues found by the audit. While this may require lots of work, he hopes that other developers may contribute to the VeraCrypt project to speed these things up.
It will be interesting to see how VeraCrypt evolves in the coming months. If things to as planned, it could rise to become a very popular TrueCrypt alternative.


















Anyone hear of Lavabit? Read their story carefully before you start trusting a new encryption software. Let’s face it – the US Government is on an inquisition, out to eliminate any and all personal privacy and data privacy. Witness the FBI free-ranging the entire globe over the last 5 years, yes beloved Obama years, to destroy download sites and TOR. And to take control of the Internet.
Veracrypt showing up right when the Truecrypt founders just disappear is wierd as hell, and highly suspicious.
Good point, Jim. Those were my exact thoughts.
Hi,
I use Truecrypt 7.1a under Kubuntu.
I know that TC is no longer being developed and was wondering if I should migrate to Varacrypt or stay with TC?
Advice please
Hi I agree.We had better to integrate all the compiler into one team on one platform .
And who build a google talk account (group talk) in order to let us talk about the TC/VC instantly.
i think i know why the new format isnt compatible with this from old truecrypt, but if trucrypt.ch make a second fork of tc than cooks all developers there own little soup. it should be better if developers there want work one fork. combine manpower…
Don’t have a portable version?
Mr. Brinkmann.
Thank you for this VC review as I (we) was in eager anticipation of it!
TR
You are welcome ;)
Well, TrueCrypt.ch will also be working on an OSS fork.
So there’s plenty of choices
https://www.grc.com/misc/truecrypt/truecrypt.htm
Worth being read, as all Gibson’s articles are.
^^^ indeed .. and listen to anything Bruce Schneier has to say about it ( https://www.schneier.com/ )
and for your amusement >> http://www.schneierfacts.com/ :)
Until that TrueCrypt audit will be finished, there are too many questions and very few answers… All we can do now is wait. In other words, if I am willing to trust a TrueCrypt fork, why not continue to use the old TrueCrypt?
Conversely if you’re willing to trust TrueCrypt why not use the better supported and more advanced fork?
Makes sense.
Makes sense.