Microsoft: Windows XP has the highest infection rate
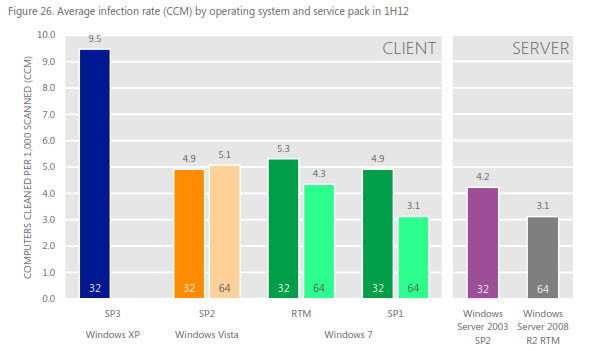
Microsoft has released its latest bi-annually Security Intelligence Report covering the first half of 2012 which offering a worldwide threat assessment for that period. One of the highlights of the report is the average infection rate of popular Microsoft client and server operating systems. According to the report, Windows XP SP3 systems are on average twice as likely to get infected as Windows Vista or Windows 7 systems. The system with the lowest number of average infections is the 64-bit version of Windows 7 SP1, with 3.1 infections per 1000 computers compared to XP's 9.5 infections per 1000 computer systems.
It is interesting to note that infection rates for 64-bit versions of Windows 7 are lower than infection rates for 32-bit versions of the operating system version.
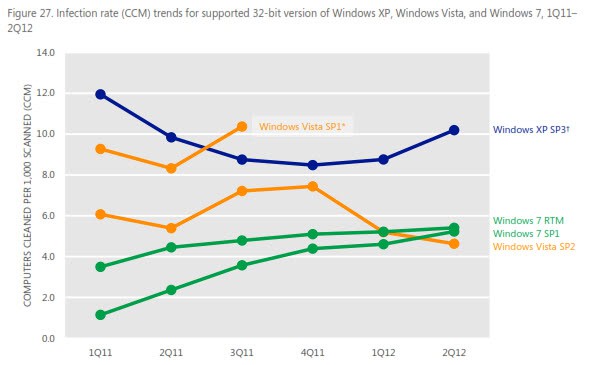
When you look at the trend chart, you will notice that the average infection rate of Windows XP and Windows 7 systems is on the rise, while that of Windows Vista has dropped significantly in the first half of 2012. Windows 7 infection rates only increased slightly in the first half though, while Windows XP infection rates made a huge jump to over 10.0 in the second quarter of 2012. This jump is attributed to the worm family Win32/Dorkbot and the trojan downloader Win32/Pluzoks by Microsoft.
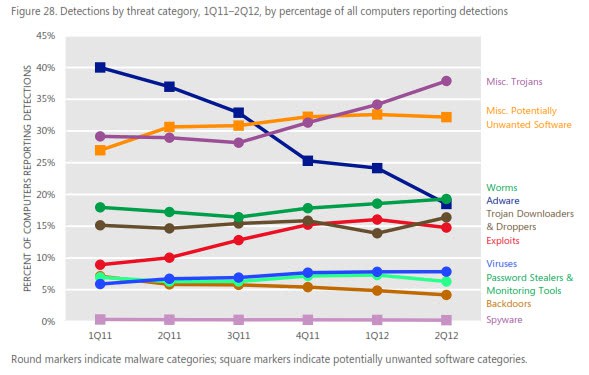
Miscellaneous trojans lead the thread category listing, followed by the potentially unwanted software, worms, adware, trojan downloaders and droppers and exploits.
- The increase in Miscellaneous Trojans, the most commonly detected category during both quarters, was driven by an increase in the generic exploit family JS/IframeRef and the rogue security software family Win32/FakePAV.
- Miscellaneous Potentially Unwanted Software detections remained consistent through both quarters. Win32/Keygen, a generic detection for tools that generate keys for various software products, was the most commonly detected family in this category.
- The Adware category has declined significantly over the past several quarters, from 1st as recently as 3Q11 to 4th in 2Q12. Significantly reduced detections of JS/Pornpop, Win32/Hotbar, and Win32/OpenCandy have been the biggest contributors to the decline.
- The Exploit category, which had been increasing gradually for several quarters, fell slightly in 2Q12. This trend corresponds to the increase and apparent peaking of the Blacole exploit kit.
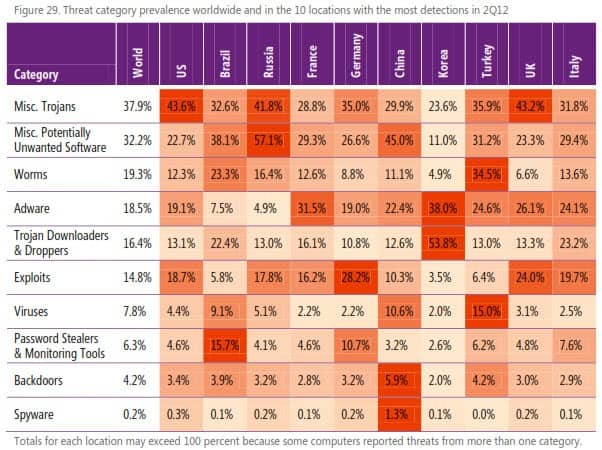
- The United States and the United Kingdom, two predominantly English speaking locations that also share a number of other cultural similarities, have similar threat mixes in most categories. The Miscellaneous Trojans category is more prevalent in both places than in others primarily because of detections of the English-language rogue security software family Win32/FakePAV, 72.7 percent of which involved computers in the US and UK. Exploits are somewhat more prevalent in the UK than in the US because of the Blacole exploit family, which was detected on proportionally more computers in the UK.
- In Russia, the Miscellaneous Potentially Unwanted Software category is especially prevalent, led by Win32/Pameseg and Win32/Keygen. Pameseg is a family of installers that require the user to send a text message to a premium number to successfully install certain programs, some of which are otherwise available for free. Currently, most variants target Russian speakers.
- Brazil has long had higher-than-average detections of Password Stealers & Monitoring Tools because of the prevalence of malware that targets customers of Brazilian banks, especially Win32/Bancos and Win32/Banker. In 2Q12, Brazil accounted for 69.9 percent of computer reporting Bancos detections worldwide, and 42.4 percent of computers reporting Banker detections.
- Korea had significantly higher-than-average detections of the Trojan Downloaders & Droppers and Adware categories, and significantly lower than-average detections of all other categories. The high level of Trojan Downloaders & Droppers detection was driven by large numbers of computers infected withWin32/Pluzoks. The high level of Adware detections was driven by Win32/Wizpop, which monitors users’ Web browsers and diverts requests for certain URLs to a Korean-language site. In 2Q12, 90.4 percent of computers reporting detections of Wizpop were located in Korea.
- Worms were especially prevalent in Turkey in 4Q11 because of Win32/Helompy, a worm that spreads via removable drives and attempts to capture and steal authentication details for a number of different websites or
services. The worm contacts a remote host to download arbitrary files and to upload stolen details. In 2Q12, 63.2 percent of computers reporting detections of Helompy were located in Turkey. For more information about Helompy and Turkey. - Worms and viruses were particularly prevalent in India, driven by detections of the generic worm family Win32/Autorun and the virus families Win32/Sality and Win32/Ramnit.
It needs to be noted that the report is looking at the big picture, and while that means that Windows XP SP3 systems have a higher average infection rate than Windows 7 systems, it does not mean that individual XP systems are more likely to get infected than Windows 7 systems. In the end, it comes down to updates, the software that is installed on the system, the security of the system, the user's activities and other factors.
You can download the full report from the Microsoft SIR website.
Advertisement
















dual boot, usually into xp, but sometimes into the original vista. vista is just annoying. but otherwise it is better.
http://www.google.com/search?q=uac+wsh+|+dep+efs+aslr+%2B%22security+features%22+xp+windows-6+|+vista+|+win7+cannot+%22only+on%22
User ignorance and permissions is the reason XP is more vulnerable than Win 7. Defaulting to an Admin account has been it’s problem since inception. icals was introduced in Vista to address the issue without requiring much effort from the dumb user.
It has nothing to do with being old or updates. It’s still being patched and is still used in mission critical environments. If you were to run XP as a Limited User you’d be less susceptible to malware than Windows 7 x64. The fact that I’m the first to point this out means user ignorance and misinformation is still a huge problem.
Well, under a good antimalware protection, XP is still the best. Most of the trading platforms using Win XP are more user-friendly, rock solid and most well tested. Win 7 may be a lot better but it also has many downsides.
I guess this is because there are so much users of xp and it is old.
XP has a higher infection rate…
All I can say is: Duh!
Of course it does – it’s a complete POS… Windows 7 is definitely superior to Windows XP in most respects.
I’m still running openSUSE Linux – which has probably a ZERO infection rate…
Oh, and the reason 64-bit has a lower infection rate is because 64-bit Windows does things differently and slows hackers down learning that. That won’t last forever.
I agree with RSH on the “duh” part, but for entirely different reasons. XP has had many, many more years of exposure. That alone ensures a higher infection rate. It would be more interesting to see how Win7 measures up when it is as old as XP. Then we can make a valid judgement of which is really the more secure OS. Win7 “should” win out, but all it would take is one serious flaw to tip the balance. Time will tell. For now though, this is just interesting data.
Windows 7 is ugly and slow. And Linux is boring. Why does Linux always get into articles. Nobody cares about that plain platform. XP is great.
Strangely enough I was just reading about that. Bit over my head though:
“A 32-bit number is large – it’s a little more than 4 billion. A 64-bit address is much larger number – roughly 18 pentillion and change (18,446,744,073,709,551,616). Not only does a 64-bit number let you address more memory, it also makes existing memory protection features such as ASLR (Address Space Layout Randomization) much more effective. Heap spray attacks, which are used by attackers to plant malicious code at predictable locations, become much more difficult because it isn’t practical to “fill up†a 64-bit address space – you’ll run out of memory and disk space long before any sizable fraction of the address space is sprayed.”
The theory is nice but in the real world Windows 7 64 bit is vulnerable as much
as XP. You don’t have to read Microsoft’s biased report (they want to kill vista,xp
and 7 in favor for Windows 8). Just go over last 3 years of the Microsoft’s monthly security
updates. Every XP security hole is found also in Vista 32/64, 7 32/64, server 2003,
2008, 2008r2 and starting next month in Windows 8 as well.
DEP, ASLR… are nothing but security lipstick on a pig and been since day one
hacked.
I wonder if the infection rate being higher for Vista 64-bit than 32-bit was due to people trying to find 64-bit versions of software/drivers on the internet?
Still, XP is the best operating system :-)
“This jump (inXP Spe) is attributed to the worm family Win32/Dorkbot and the trojan downloader Win32/Pluzoks by Microsoft.”…
No. The jump is attributed to Microsoft dumping the support and bugs fixing (no SP4)
for XP which still has ~45% Windows user base.
I kind of agree.
Despite “extended” support, I suspect MS will let XP crumble.
I have no proof, but I felt the same thing happened in the last years of Win9x.
Maybe there’s an emotional component to this. people don’t have enthusiasm for aging things. They like the fresher shinier stuff.
Along with that, people more willing to spend money will demand support for the shiny stuff.
This jump (inXP Spe) should be This jump (in XP Sp3)
“It is interesting to note that infection rates for 64-bit versions of Windows Vista or Windows 7 are lower than infection rates for 32-bit versions of the operating system.”
You mistook the chart. It should be:
“It is interesting to note that infection rates for 64-bit versions of Windows 7 RTM or Windows 7 SP1 are lower than infection rates for 32-bit versions of the operating system.”