LinkedIn Hacked, Are You Affected?
LinkedIn yesterday confirmed that there was a breach of security, and that member passwords were dumped by the attackers. The password hashes have been posted on the Internet in a 250 Megabyte text file, and it is generally assumed that people have started to break the hashes to reveal the underlying passwords. All in all, about 6.5 million LinkedIn user accounts are affected by this.
LinkedIn itself has taken counter measures to protect affected users accounts from being compromised. Probably the biggest protection in this regard is that affected account passwords have been invalidated, so that they can't be used anymore to log in to LinkedIn.
All affected members will receive an email from LinkedIn that contains instructions on how to reset the account passwords. LinkedIn notes that these emails will not contain links, to avoid copy cat emails that use this for phishing. It basically comes down to reseting the user account password to receive a new one. Affected members will furthermore receive a second email from LinkedIn's customer support team that is explaining the situation to them.
While LinkedIn is doing everything they can to resolve the issue and protect their user's accounts, it needs to be noted that users who have used the password on multiple sites need to change the password on all sites where they did so.
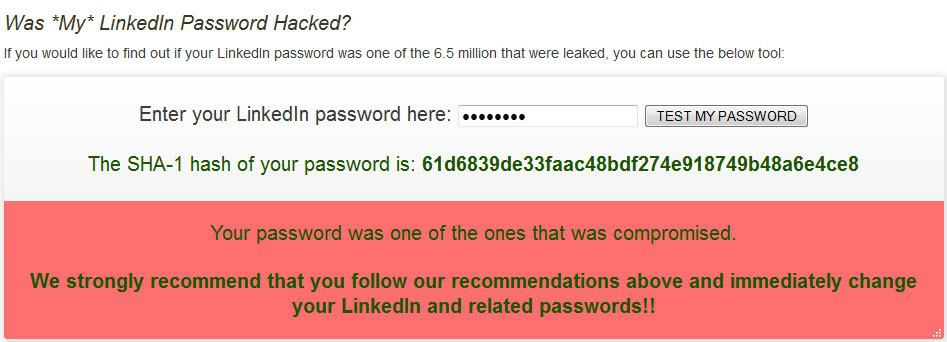
The LastPass company got their hands on the hashes and have created a small online test that you can use to see if your password is on the leaked list or not. Just head over to the site and enter your LinkedIn password there. You can naturally enter a password that you are curious about instead, just to see if it has been used by any of the members.
To sum it up:
- Check your password at the LastPass password checker, or head over to LinkedIn and try to log in.
- If the password has been compromised, follow the reset password instructions and reset your LinkedIn password first
- Head over to other websites where you have been using the same password and change it there as well.
I personally would recommend using a password manager like KeePass which offers several advantages over conventional methods. You can use it for instance to create secure unique passwords for every service that you sign up for to avoid situations where the same password is shared on multiple services.
Has your LinkedIn account been affected by the password breach? If so, what have you done to resolve the situation?
Advertisement












I have been busy passing information and advice to all my colleagues. I have changed all the passwords on sites where I used the same credentials. LinkedIn has combined my private account and my business account, so I also have to change all related private accounts… (tonight..). A caveat here is that many websites have started accepting your email address as substitute for your once chosen login id. You might not be aware of this.
Mine wasn’t. Changed it anyway.
Just checked. My password had been compromised. Changed it to a much random one… thanks a bunch Martin :)