Firefox 72.0 release information
Firefox 72.0 is the latest stable version of the web browser; it was first released on January 7, 2020 which makes it the first stable release of the web browser in 2020. The next stable release, Firefox 73.0, is scheduled to be unveiled on February 11, 2020.
All Firefox channels are updated around the same time; this means that Firefox Beta, Dev and Nightly, as well as Firefox ESR will also receive updates. Firefox Beta and Dev are moved to version 73.0, Firefox Nightly to version 74.0, and Firefox ESR to version 68.4.
Check out the overview of the Firefox 71.0 release in case you missed it.
Executive Summary
- Tracking Protection blocks fingerprinting scripts by default for all users.
- Notification requests are toned down to reduce user frustration.
- Picture-in-Picture mode is now also available on Mac and Linux devices.
Firefox 72.0 download and update
The official release date for Firefox 72.0 is January 7, 2020. Users will be able to download and install the new version of Firefox on that day, or use the built-in automatic update functionality to get Firefox updated automatically.
Note: the browser may not be available officially at the time of writing but it will become available later on January 7, 2020.
Once released, you may run a manual check for updates in Firefox by selecting Menu > Help > About Firefox. Firefox opens a new window that runs a check for update and either suggests to download and install it, or does to automatically.
The following pages list direct downloads for supported Firefox channels.
Firefox 72.0 Changes
Making notification requests less disruptive
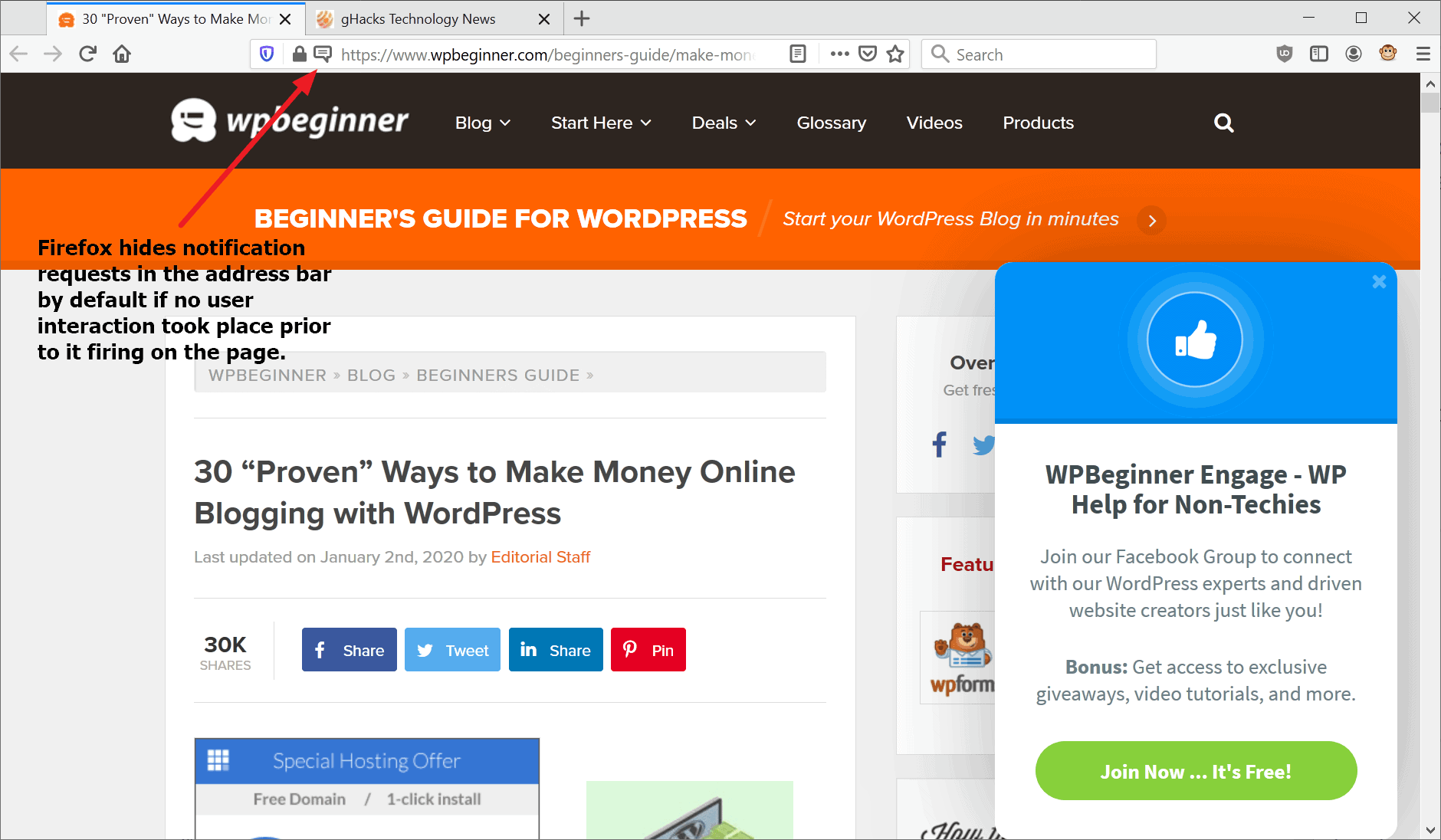
Many sites display notification requests to users to be able to send push notifications to the users system. Designed as a way to update users, the feature has been abused by a lot of sites that display requests the moment the page is loaded requiring users to interact with the request.
That's a bad user experience and browser makers decided to tone this down to improve the experience. Instead of displaying the popup prompt, Firefox displays an icon in the address bar instead if the user did not interact with the page prior to the notification request firing.
Regular notification prompts are displayed if the user interact with the site, e.g. if a link or button was clicked on the page and the notification request fires after that.
Other changes
- The built-in Tracking Protection of Firefox blocks fingerprinting scripts by default for all users to improve privacy further.
- Mac and Linux users that use Firefox may use the picture-in-picture mode of the browser now.
- Windows administrators may enable (experimental) support for loading client certificates from the operating system's certificate store. This is done by setting the preference security.osclientcerts.autoload to true.
- It is no longer possible to block the loading of images from individual domains.
Firefox for Android
- not yet released
Firefox 72.0 known issues
- none at the time of writing.
Developer Changes
- The timings tab of the Network Monitor of the Developer Tools shows queued, started, and downloaded times for resources.
- Scratchpad has been removed.
- CSS Shadow Parts are now enabled, CSS Motion Path has shipped.
- Notification.requestPermission() and PushManager.subscribe() can only be called after user gestures.
- MediaDevicers.getDisplayMedia() can only be called in response to user gestures.
- BatteryManager interface no longer exposed to web content.
- HTTP Public Key Pinning is no longer supported.
- image/webp added to default HTTP Accept header.
- X-Content-Type-Options: nosniff applies to top-level documents (some pages may be downloaded instead of rendered).
Security updates / fixes
Security updates are revealed after the official release of the web browser. You find the information published here.
Additional information / sources
- Firefox 71 release notes
- Add-on compatibility for Firefox 72
- Firefox 72 for Developers
- Site compatibility for Firefox 72
- Firefox Security Advisories
- Firefox Release Schedule





















On a slightly different slant to other posts…
Does anyone else do as I do? That is, ignore round-number FF updates?
When I see an update to – say – FF 72, I just ignore it. On the basis that within days I can bet my boots I’ll be offered 72.01 ?
hi Martin.
Firefox 72.0.1 just came out today January 8:
https://www.mozilla.org/en-US/firefox/72.0.1/releasenotes/
which fixes this new security flaw mentioned in this new Mozilla security advisory:
https://www.mozilla.org/en-US/security/advisories/mfsa2020-03/
@EP: There is about it.
https://www.ghacks.net/2020/01/08/firefox-72-0-1-fixes-a-security-vulnerability-that-is-actively-exploited/
The support for userChrome.js is ending in v72.
Well, not really. In fact it is -moz-binding which stops working for good in Firefox 72, but userChromeJS (uc.js scripts) can still be running.
Fortunately I’ve found the alternative method at “https://github.com/xiaoxiaoflood/firefox-scripts”
This method works with Autoconfig. Well explained on the developer’s page.
I felt quasi desperate when launching FF72 and noticing that none of my userChrome scripts were active. I rely on those scripts, so handy. xiaoxiaoflood did a great job with his userChromeJS environment install procedure. Really : great.
Otherwise, no problem with FF72. But the one month update cycle is short, too short. Depending on the update’s content and given I tweak FF enormously (Ghacks-user.js but not only), I happe, to spare several hours getting the whole thing done. Not everyone can spare so much time, not to mention the bother.
Tom, you can’t imagine how you save my (FF) life.
As you, I was desperate, completely for my part. At this point, I was even resigned.
I was in a perspective where FF71 was going to remain my main browser indefinitely.
But thanks to you, I can finally upgrade to 72 without concession.
Thank you. Thank you. Thank you. Thank you. Thank you. Thank you!
@Marcin, exactly the same here : I was just about to flip back to FF71, cosmic words traveled through my brains, I think some of them even made their way to my mouth. Then I took a big breath, imagined a sexy silhouette to help me recover a zen attitude, and started searching. What I shared above was all found on Reddit.
When I realized that xiaoxiaoflood’s method worked perfectly I felt the same gratitude as you. I think all gratitude is to be addressed to xiaoxiaoflood, great developer. By the way he has a few userChromJS scripts of his own, worth discovering.
for the love of god, bring back the added bar!
How to disable local storage now? Pref dom.storage.enable removed from FF72.
Uninstalling and turning back to FF 68 ESR. Best way imho to still using Firefox. 🙄
does that mean that privacy.resistfingerprinting is now obsolete, i.e integrated into default firefox config?
ETP’s (Enhanced Tracking Protection) fingerprinters list = to block some known scripts from running
privacy.resistFingerprinting = provides some protection from scripts actually interrogating your browser/device
Two completely different things
@pants
would ublockorigin and vpn do the same job?
@Femail
The first/best defence against FPing is to block the scripts. I am not an expert on ETP’s list, but it’s created using information from OpenWPM crawls (among other sources) – which I think only looks at the landing page of sites, and I think the list only blocks third party scripts. But it’s always changing and Firefox will ramp it up: so don’t get me wrong, this is still great for most people.
Depending on how you configured uBO, you may or may not get any mileage out of ETP’s fingerprinters – but it can’t hurt to leave it on. There is no need to fiddle with it.
A VPN has nothing to do with fingerprinting (excl. IP harvesting)
@pants
thanks for your reply.
I do configure ublock.
I block thirdparty and thirdparty frames & scripts
but often I have to modify from site to site.
I also checkmarked Anti-facebook List & Fanboy’s Social Blocking list.
my concern regards whether this might conflict with FF’s list?
I never fiddled with privacy.resistFingerprinting ( a different thing according to your explanation above ). I still remember the discussion here at ghacks, and decided back then, that I wasn’t skilled to mess with this cofinguration ).
What’s the difference?
More Info on any about:config options that may have been added or removed and that’s necessary information. I’m still on 70.0.1 and holding once again to properly do my vetting on FF 72.0!
FF sure requires some extra tweaking to get things like Popups properly disabled to a better degree than FF’s standard UI check box methods and that requires more trips to about:config. Maybe an about:config change log where any new additions and deletions are noted. And what was the older version of FF still allowed the update nagging to be disabled?
These monthly browser updates become quite boring. Rarely it is coming some update which is interesting
This update has the new California privacy law which include telemetry opt-out and deleting all personal data harvested by FF.
“Firefox users may disable Telemetry in the browser’s Settings. All that is required is to load about:preferences#privacy directly or open Menu > Options > Privacy & Security, and uncheck “Allow Firefox to send technical and interaction data to Mozilla†(which will automatically disable personalized extension recommendations in the browser. Firefox users who don’t want the browser to be included in studies may also uncheck that option on the page….
Mozilla will inform users who disable Telemetry in Firefox that data that was collected previously will be deleted automatically. The deletion may take up to 30 days to complete…”
This update is broken for me.
The Addons Extensions page is truncated, with a small scrolling section at the top. There’s barely enough space to view one extension, and the top of the page is also moved upwards, so clicking the gear icon only displays the bottom half or so of the menu.
The tabs are now also broken, with the close X in the center of the tab.
Removing my userChrome.css file does nothing to fix the broken tabs or Extensions page.
Once again, and other rubbish failure from Mozilla.
Same problem here! Tabs and addonpage are messed up.
Setting “layout.css.xul-box-display-values.survive-blockification.enabled” to “true” solved the problems!
@Mingus, ‘layout.css.xul-box-display-values.survive-blockification.enabled’ is true by default, at least on FF72: no idea of this setting’s value previously to FF72 given this is the first time I hear about it.
Anyway, if setting ‘layout.css.xul-box-display-values.survive-blockification.enabled’ to true solves your problem this means it had been set to false previously.
@Albert McCann, “Once again, and other rubbish failure from Mozilla.” … or from the user.
No such problems here with FF72. There’s obviously an intruder; you mention that removing your userChrome.css file didn’t resolve the issues so it has to come from somewhere else. Check your add-ons, plugins if any. The issues seem to concern only the display so indeed CSS is the first explanation that comes in mind, but you say you’ve tested that unsuccessfully. Odd.
I have exactly the same issues. Upgrade from v.71 to 72. And I did not have an active userChrome.css.
Everything is working fine for me.
Maybe it’s just your computer?
https://ftp.mozilla.org/pub/firefox/releases/72.0/
I don’t use Firefox (nor Chromium based browsers for that matter). Too much calling out to various IP addresses. For instance, Firefox always connects to Amazon servers, and sometimes to Google’s, even with only a blank page. Pale Moon doesn’t show such misbehaviour (with the same privacy and security settings). Therefore Firefox will never be my default browser again, unless perhaps the developers change this.
@Gerard,
Pale Moon was serving malware from their official servers in July 2019 & it’s based on Firefox 38 ESR (so you are using Firefox, but a VERY OLD [customized] version, that’s not supported by Mozilla anymore, since the current ESR is Firefox 68 ESR).
All major browsers on Windows are based on Gecko (Firefox) or Blink (Chrome & Chromium clones [Opera, Vivaldi, Brave, etc.).
As Kubrick mentioned you can use about:config to stop Firefox from calling out, but you’re going to lose Google Safe Browsing, so your trading privacy for security (it’s up to you to determine which is more important).
The Ghack user.js will also stop Firefox from contacting other websites, but it’s pretty advanced, so be warned.
As i wrote, Google is not a serious problem in my case. Amazon is the real problem. Firefox always phones out to Amazon servers. I don’t want that. Pale Moon doesn’t have this problem.
BTW, I have disabled “safe browsing” and use other methods for protection and security.
@notanon
Pale Moon 28.x is actually based on Firefox 52 ESR, with many web compatibility improvements backported to it. It also gets the most recent security patches from the Firefox ESR release branch. I don’t know why “supported by Mozilla” is a criterion at all, on many occasions Moonchild has output higher quality code than Mozilla, and at times has even fixed bugs that are still present in Firefox (color grading being one of them).
It’s true that the Pale Moon archive server was hacked by a third party according to Moonchild, but it needs to be noted that the current Pale Moon versions from the main website were never affected, meaning you “only” got a virus if you wanted to install an older version of Pale Moon than the current one. I am not defending the Pale Moon project at all, but making it seem like the standard Pale Moon installer was affected at some point is disingenuous on your part.
Last but not least, Mozilla’s own add-on site has delivered malware-infested add-ons to thousands upon thousands of Firefox installations so far, because they can’t be bothered to actually check add-ons for malware infestations, or to remove them when they are reported!
@Iron Heart, I didn’t realize Pale Moon was based on Firefox 52 ESR, my bad & my sincere apology (I don’t use Pale Moon myself, so I really don’t keep up).
Firefox is currently on Firefox 68 ESR, and alot of code has changed (for the better) since the legacy, pre-Quantum Firefox 52 ESR. AFAIK, Firefox does not patch/support Firefox 52 ESR anymore, so how can you be certain that Pale Moon (based on the obsolete, deprecated Firefox 52 ESR) is fully patched against security vulnerabilities??? The answer is … you can’t … all you have is Moon Child’s word (because Mozilla doesn’t comment of Pale Moon or Waterfox, AFAIK).
It’s not uncommon for forks to omit security patches if it suits them/breaks their forked code).
For example, Linux Mint notoriously refused to apply Ubuntu security patches when it interfered/broke Cinnamon (Mint’s GUI).
How can you be certain that Moon Child has applied all the Firefox security patches to Pale Moon (or if it’s even possible to patch Firefox 52 ESR with the current Firefox patches, if Mozilla refuses to write custom patches for Firefox 52 ESR/Pale Moon (which is almost certainly the case)?
That just the first problem with Pale Moon.
The second problem is that Pale Moon couldn’t even give dates of when they were serving malware out of their official servers (likely because they didn’t keep server logs, otherwise, you would know when the infected software was first sent out to users & when you stopped serving infected software).
Do you really trust an person or organization that is so incompetent that they would serve malware out of their official servers AND didn’t keep server logs???
Even when Linux Mint was serving malware out of their official servers, they could report the exact start & ending date, because they kept server logs. BTW, it was only a few days for Linux Mint, not the extended period of time that clueless Pale Moon was serving malware.
BTW, Iron Heart, Firefox NEVER has sent out malware for their browser, unlike Pale Moon.
What you’re talking about is Mozilla AMO, which Mozilla stopped checking every web extension, a courtesy it stopped recently. Whereas Chrome has never checked any of it’s web extension AFAIK, & there’s been exponentially more malware served from Chrome’s web extension store than Firefox’s Mozilla AMO.
Trying to compare Pale Moon serving malware from their official browser download site to Mozilla’s AMO (same problem with Chrome’s web extension store) is a false equivalency.
If you choose to use Pale Moon, that on you, but don’t pretend that Pale Moon is somehow better or even on the same level as Firefox, because it’s not. It’s an old, unsupported, tweaked version of Firefox & the current version of Firefox has seen vast improvements since Firefox 52 ESR.
@Notanon Which means, as nobody has the right to offend/attack/harass minorities, rest assured you will be watched and examined, and actions – IF applicable – WILL be taken.
What are you? Some kind of browser fascist/racist? Grow up and stop acting like an underaged child which is additionally on Mozillas paylist. Mozilla stopped VERY long ago to be the good guys. THAT is the sad reality.
@Notanon You are a simple offending troll – would not be surprised if you have been the offending reddit troll who deleted his account which was called “TypicalTable” who was sending death wishes to people into Pale Moon’s Reddit section – and/or – “Roman” who spams in the Waterfox blog – and slightly edited as “roma6266 ” in the Pale Moon board.
Anyway that is not the point. Security backports are handled like in all forks, no matter if Waterfox from Firefox or Brave/Vivaldi from Chrome.
The organizations examine and fix the reported vulnerabilities and a bit later grand access to other browser maintainers so they can examine and fix the issues IF applicable.
As Pale Moon is not having latest Mozilla code in use, most issues regarding Mozillas new additions are NOT applicable in Pale Moon as they do not exist.
This is secure enough. If you want to see something really NOT secure, then complain about Firefox 52 – which neither is getting the security backports or additional enhancements.
Right now the Pale Moon team is porting Shadow Dom/Custom elements and required HTML5 features into the browser. Also THIS is not landing in Firefox 52.
You are a non-informed and redarded harasser who is on a crusade against everything which has features and does not bow down to minimalist and simple concepts.
@gerard.
Those can be stopped in about:config.Firefox uses google safebrowsing and will naturally connect to google as will the search engine too if you have it installed.
I use firefox as a back up browser as pale moon is my main navigator.
about: config? How? Google is not the main problem though. I never used it and google.com is in my hosts file (but that’s for named web adresses). The Amazon addresses are the big problem. The IP adresses phoned out to are never the same ones. The only way to stop this phoning out is by adding rules to the firewall and block entire IP ranges afaik.
There is something rotten in the state of Mozilla. Of course, Google is much worse. Pale Moon is much better.
[Windows administrators may enable (experimental) support for loading client certificates from the operating system’s certificate store. This is done by setting the preference security.osclientcerts.autoload to true.]
Does this mean, the Windows certificates are used instead of Mozilla’s or in addition to Mozilla’s?
Good question, I don’t know the answer as I did not have time to test it. Anyone else?
Thanks Martin for letting us know what is happening with the Mozilla Firefox 72 release
and particular nice to read that fingerprinting is advancing (By default now) and also really great is that the notifications are toned down on this way.
To bad that the dynamic scrollbars based on page color did not make it. Maybe in February?
Adaptive scroll bars made into this release, although apparently not for all websites. See the official qBitorrent website for example, the scroll bar should be blue. It seems to me that bright websites use the default colors while darker websites do use adaptive. I wonder how Firefox determines the colors form the website though. Or is it just simply the background color of the tag and automatically chooses an accent color for it?
Thanks Anoymous, For your explanation.
I am also wondering how Firefox determines the colors from each individual website.
I did not read anything about that also nothing about how long the website color adjustment (translating) to the Firefox 72 browser is taken on average?
Now today I am already working with the Mozilla Firefox 72.0.1 release.
Hopefully Ghacks.net (Martin & Ahwin) will tell us like always what’s that about?
Thank you mozilla.!
I always appreciate free software.Great companion browser to pale moon which is my main browser.
@Kubrick,
Pale Moon was serving malware out of their official servers in July 2019 & it’s based on Firefox 38 ESR, which is obsolete (we’re on Firefox 68 ESR).
Maybe you should consider retiring Pale Moon.
@notanon.
I fully understand the concern over that incident.I don’t use the archive anyway and a full explanation was given over at the pale moon forum.
As for retiring pale moon,This time next year i will have no choice as the 32bit edition will not be supported anymore.I am considering chromium as it’s replacement to accompany firefox.Not sure how much longer mozilla will continue support for 32bit.
Does Firefox 72 contain the new California privacy rules including telemetry opt-out, as promised by Mozilla ?
Yes
Does opting-out in your Windows Firefox also apply to Firefox on your Android phone–or do you have to do that separately? I have synching enabled.
Upcoming Firefox 100 changelog:
* Added chrome webinstaller
* Addons restricted as per policies of V3 manifest
* Google domains are whitelisted from all blocking
* Rival ad networks are blocked in tracking protection
* Users are blocked from browsing ghacks due to “hate speechâ€.
@Shania,
Are you a Google shill or do you have no life???
Enjoy your unblockable ads in Chrome when Manifest v3 is enforced in Chrome sometime in 2020.
I’ll be BLOCKING all those ads with uBlock Origin (which gorhill will stop developing for Chrome when Manifest v. 3 is enforced by Google).
@notanon
1) Mozilla will probably implement V3 as well, as compatibility with Chrome’s extension framework is a major goal of theirs. WebExtensions are meant to be a way to easily port Chrome extensions.
2) There are Chromium-based browsers like Brave which have built-in adblockers that do not rely on the altered API at all, one can use them as well.
3) There is PI-Hole as a last resort.
@Iron Heart, PI-hole doesn’t come close to what uBlock Origin does, and you know it.
Stop trying to mislead people.
And stop lying about Mozilla, they’ve said the opposite of what you posted. Where’s you’re proof???
Answer … there is no proof, because you’re just spouting lies.
@Iron Heart, posting lies again???
Mozilla has stated they will not be implementing Manifest v.3 content crippling removal of block webrequest.
As usually Iron Heart you’re spreading Chrome propaganda (lies) without sustantiation.
Most of this could happen. Especially the second and third point.