How to change your Twitter password
Twitter revealed on May 3, 2018 that the company stored user passwords in plain text for a considerable amount of time. The company patched the issue and investigated potential breaches but concluded that there was "no indication of breach or misuse by anyone".
User passwords were "written to an internal log before completing the hashing process". While Twitter's investigation did not find indicators for abuse, it recommends that all Twitter users change account passwords and implement additional security protections if not activated already on the account.
This guide walks you through the steps of changing the Twitter account password. It furthermore points to additional security protections that you may want to enable on the account to improve security significantly.
Change the Twitter password
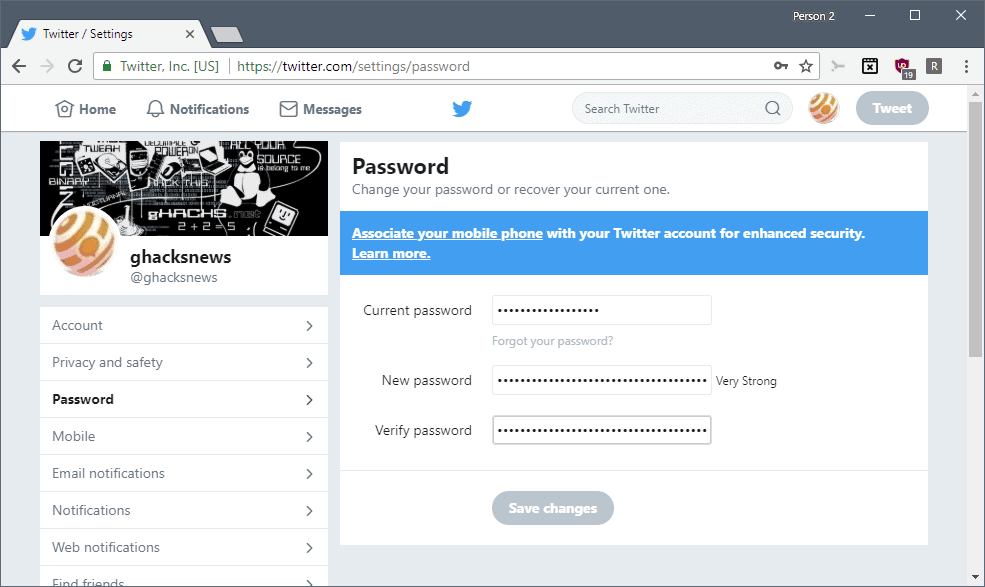
Complete the following steps to change your Twitter account password:
- Load https://twitter.com/settings/account directly. The page lets you change the Twitter account password directly.
- You can go to the page manually as well if you prefer that.
- Open the main Twitter website.
- Click on the account icon in the upper right corner next to Tweet, and select "Settings and privacy" from the menu.
- On the page that opens, select Password listed in the sidebar.
- Type or paste your old account password and twice the new password that you want to use from that moment on.
- Select "save changes" to apply the change.
Twitter checks if apps are linked to the account and suggests to review the applications. It is recommended that you do so as you may want to revoke access to any application which you don't use anymore.
Login verification
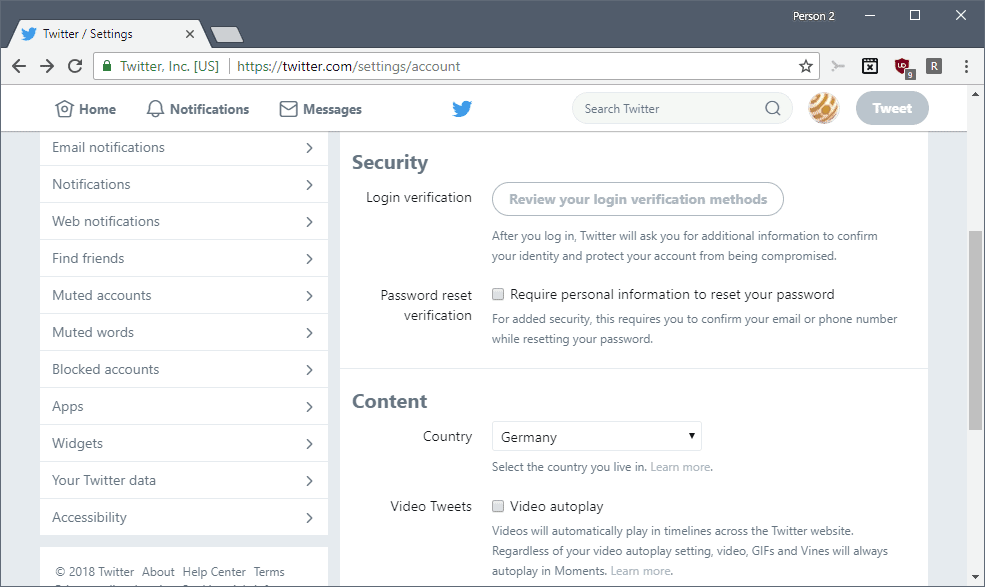
While changing the password is all that is required to protect the account from potential abuse of Twitter's faux pas, you may want to consider enabling login verification on top of that.
Login verification is a two-factor authentication scheme that adds a second verification step to the login on Twitter.
Note: Twitter sends SMS with codes to your phone when you sign in and you need to type the code to authenticate. It is required that you link the Twitter account to a phone because of that.
Here is how you enable the option:
- Load https://twitter.com/settings/account in the browser's address bar.
- Select "set up login verification" under Security on the page that opens.
- Skip the introductory page.
- Type the account password.
- Add a phone number by selecting the country and typing the phone number.
- Select "send code" to test the phone number and make sure it is correct.
- Type the verification code that Twitter sent to the phone.
- Select "get backup code". You may use these codes in case your phone is lost or that you don't have access to the phone anymore.
- Store the backup code in a secure location, e.g. password manager.
When you sign in to Twitter after setting up login verification, you start the process as usual but are asked to enter the code sent to your mobile phone in a second login verification step.
Now You: Do you use Twitter actively?
Related articles
- Download Twitter images and videos automatically
- How to enable Night Mode on Twitter
- How to disable autoplaying videos on Twitter
- Time to check your Twitter settings
- Twitter adds option to mute new accounts



















This is not news, the part with the guy that said the pws are cleartext doesn’t seem to be in it as it’s some sort of compilation, but anyway:
https://www.youtube.com/watch?v=rgyPpsX2B0g
I knew about this quite long. All the tech news sites copying the press release saying it was an error and mistake from twitter should be ashamed!
Mr. Snowden’s exposure case shocked the world.
Personal information that has leaked out is upset.
SNS is convenient, but risk is also a contradictory relationship.
SNS also exposed the issue of propaganda (alternatives fact) by President Trump USA.
I am away from SNS.
For the password,
I am using “KeePass Password Safe”.
Special characters, Cyrillic letters, Greek numbers are also combined and generated with the maximum number of characters (for example, 500).
Postscript
Key point of the password (personal opinion)
It is thought that character type and composition which are impossible to manually enter are important.
It is highly recommended to use passphrases instead of passwords wherever possible.
Easy to remember, easy to type, and infeasible to brute force.
For example, the phrase “infeasible to brute force” is the same length as a 25 character password with spaces being counted as special characters, yet you can easily remember it and type it out in a few seconds.
Remember, when it comes to security keys, it’s not complexity that’s important but pure length. Even a single character repeated 25 times is many orders of magnitude more secure than the most complex 13 character password imaginable.
@beemeup5 you could be right ONLY IF the primary method for braking passwords was brute force algorithm… But in reality this is the last method used. Every breaking password script that I encountered had used brute force as last option. First, are used password dictionaries that contain hundreds of millions and some other billions of ‘pre-cooked’ passwords. They are containing passwords already used and AI/ML made passwords on top of these, with variation of numbers and symbols instead of letters, shifting and much much more. Your 25 same char password will be guessed in less than one hour. The rule is: IF you think you’re smart, the algorithm will crack your password. The best tool to fight the algorithms is randomness. I know people don’t like it or are afraid of it, but it’s just math. And math (probabilities and true random algorithms) is the best weapon for every user.
tl;dr : to sustain my point, check 1111111111111111111111111 in https:/ /haveibeenpwned.com/Passwords…. it was already used 304 times before so NO 8,000,000 years to crack it, but just a few milliseconds :)
@STech
You should read my WHOLE reply to Yuliya, not just the first half. ;)
I already addressed the topic of advanced dictionary attacks and specifically said that mono-character passwords are not secure, especially if they’re just numbers. The 8 million year estimate is only for standard brute force. Context man. Context.
My point still stands. EXCLUDING mono-character passwords, pure length is more important than randomness. It doesn’t matter how random your password is if it’s only 8 characters long, that’s just math.
Passphrases are always better than passwords despite being far less “random”.
It’s good if a site support it. So far I found none, I always get these warnings: ‘Your password need to be x length’, ‘Your password is too long’, ‘Your password is too short’, ‘Your password need to contain symbols, elements, and something cool’.
@beemeup5 While I get your point. Passwords that I can’t remember are good too. All you need is a password manager. Every one has their own method and that’s OK, as long as they are unique, reasonably long and with high enough entropy.
>Even a single character repeated 25 times is many orders of magnitude more secure than the most complex 13 character password imaginable
What? o_____O NO!
1111111111111111111111111
is “infinitely” less secure than
nRD,}XM=~)YE
You don’t understand how brute force attacks work, which was the primary context of that statement. The simplest 25 character password will take an order of magnitude more time to brute force than a 13 character password of even the highest complexity.
Case in point according to https://howsecureismypassword.net/
1111111111111111111111111 = 8,000,000 years to crack
nRD,}XM=~)YE = 130,000 years to crack
Note that you chose to repeat a number, which is the simplest possible repetition as there are only 10 possibilities (0-9). Had you instead chosen to repeat a single letter 25 times, the time it takes to brute force jumps from a “paltry” 8 million years to 188 quadrillion years.
I should clarify that I don’t recommend using mono-character passwords as they are very easy to crack using advanced dictionary attacks which are the norm nowadays as brute force becomes exponentially untenable the further you go past the 10 character mark. However, all it would take to turn a trivial password into an extremely secure one is to swap a single one of those 25 repeated letters for a character from a different set, e.g. a “#”
aaaaaaaaaaaaaaaaaaaaaaaaa = 188 quadrillion years
aaaaaaaaaaaaaaaaaaaaaaaa# = 17 sextillion years (that’s 21 zeros btw)