Internet Explorer vulnerable, Security Advisory 2794220 released
Microsoft has released security advisory 2794220 which details a vulnerability in the company's web browser Internet Explorer that may allow attackers to execute code remotely on affected systems if the vulnerability is exploited successfully. What makes this a pressing matter for users of the Windows operating system is that it is already exploited in the wild according to Microsoft's Response Communications Group Manager Dustin Childs.
The security vulnerability affects Internet Explorer 8 and earlier only, and systems with IE9 or IE10 are not vulnerable. What this means is that Windows 8 users are not affected by the vulnerability at all, as the default version of the system is Internet Explorer 10. All other versions of Windows may be affected by the vulnerability as they ship with Internet Explorer 8 or earlier versions depending on the version.
Attackers need to convince users to open a specially prepared website in Internet Explorer to exploit the vulnerability, which can happen via links in emails, instant messengers, social networking sites or other means. It appears to be enough to view attack sites in Internet Explorer 8 or earlier.
The vulnerability is a remote code execution vulnerability that exists in the way that Internet Explorer accesses an object in memory that has been deleted or has not been properly allocated. The vulnerability may corrupt memory in a way that could allow an attacker to execute arbitrary code in the context of the current user within Internet Explorer. An attacker could host a specially crafted website that is designed to exploit this vulnerability through Internet Explorer and then convince a user to view the website.
Microsoft has posted several mitigation options for users of Internet Explorer 8 or earlier to protect the Windows operating system from the exploit.
- Windows Vista and Windows 7 users can upgrade the system browser to Internet Explorer 9 to protect it against the vulnerability.
- Installation of the excellent EMET, Enhanced Mitigation Experience Toolkit, will block the exploit from being executed if configured properly.
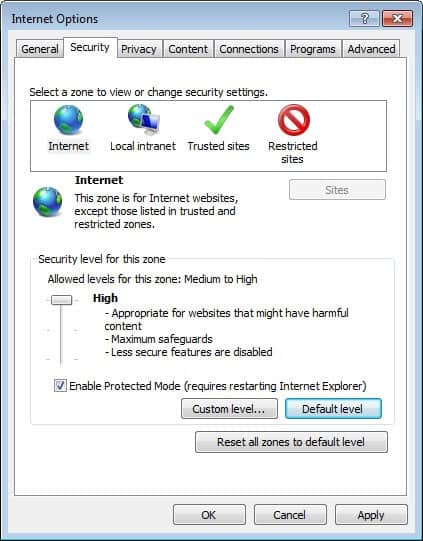
- Setting Internet Explorer's security zone settings for the Internet and local Intranet to high will block the exploit code from running on the system. Options to change the security zone settings are available in the Internet Options which you can access from the Control Panel or Internet Explorer menu (press Alt if the menu is not shown, select Tools > Internet Options).
- You can alternatively configure the browser to prompt before Active Scripting contents are run.
You can read up on the vulnerability advisory here on this page on the Microsoft website.













Internet Explorer has No ABP or NoScript. It is a No GO!!!! Sorry but I am sticking with Firefox.
The majority of people just need an address bar and a few tabs, the extras are for heavy users like us ;)
But if you look around, you can find gems that allow IE to run userscripts and have the same experience as adblockplus ;) The last one is a real gem if you can find it. It’s exactly like abp, but it’ll cost you for the privilege.
For maximum compatibility with some sites, I use Internet Explorer in conjunction with Sandboxie. I used to fire up a VMWare instance and log in. But I found Sandboxie to be much more convenient to use. I believe Ghacks had a give away of Sandboxie recently. I loved trying it out so much I bought licenses. Have been using it for a couple of years now. Works great. Especially for the non-technical members of the family.
Samdboxie is great for that, I agree.
What browser do you use?
If you haven’t use IE in months, then you should definitely give IE10 a try. Their Trident engine is vastly improve and surpass Gecko by a large margin. In my experience, it’s on the same performance level as Webkit.
IE10’s Charkra is a big improvement too. But it’s all about the layout renderer which is pretty good on IE10.
There are one or two sites that rendered a bit off in my bookmarks, but that could all due to developer codes optimized for older IEs and not recognizing IE10 presence just yet.
IE10 is a big step forward, but it is not as customizable as Firefox, Opera or Chrome.
How many of Ghacks readers use IE ?
I have not used it for months.
Last time I checked about 25%