How to encrypt partitions with DiskCryptor
I have been using TrueCrypt ever since I discovered the encryption software years ago to protect data from being accessed by third parties. It is a great open source software that has functionality to create encrypted data containers or partitions, including the system partition the operating system is installed on.
Update: DiskCryptor has not been updated in a while and while that does not mean that it does not work anymore at all, it is certainly something that users and administrators need to be aware of. As one user pointed out recently in the comments, DiskCryptor is not compatible with GUID Boot partitions with UEFI. I suggest you check out VeraCrypt instead. End
DiskCryptor is, as the name implies, another encryption software that offers functionality to encrypt disk partitions. That's a disadvantage compared to TrueCrypt and not the only difference between the two applications. TrueCrypt for instance is available for Windows, Mac and Linux, while DiskCryptor only for Windows. The software furthermore supports a portable mode which DiskCryptor does not as well.
As far as the advantages of DiskCryptor go, it supports keyfiles for full disk encryption and can place bootloaders on external devices like USB Flash drives. Another interesting fact about DiskCryptor is that partition backups only take up the data space and not the space of the partition's overall storage capacity. If you backup a 1 Terabyte drive that is encrypted with TrueCrypt, you end up with a 1 Terabyte backup. With DiskCryptor, you'd end up with a backup that is only as large as the data that is stored on the partition. This reduces the time it takes to create the backup and the storage requirements.
How to encrypt partitions with DiskCryptor
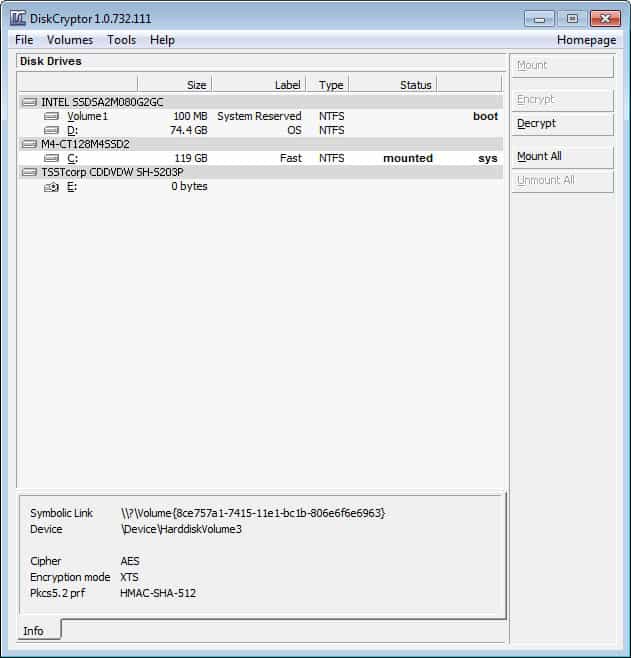
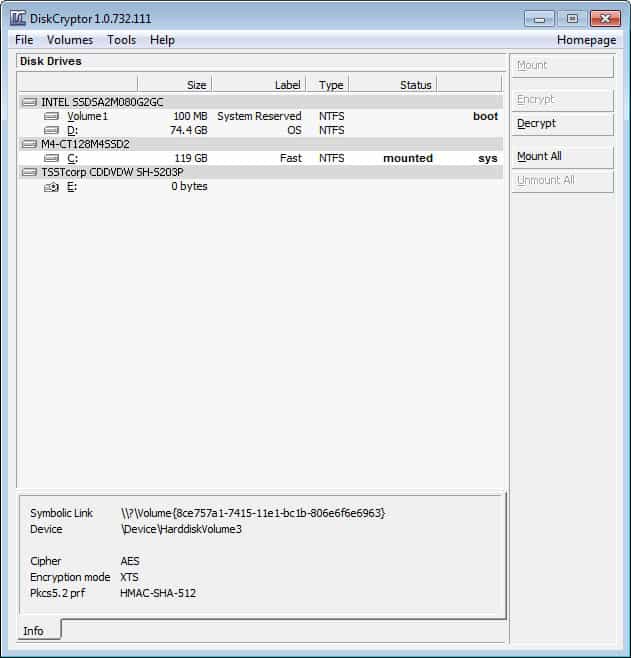
It is actually very easy to encrypt a partition with the disk encryption software. The program needs to be installed on your system, and requires administrative privileges to run. It will load the list of connected hard drives and partitions, indicating the system partition and boot partition on the screen as well.
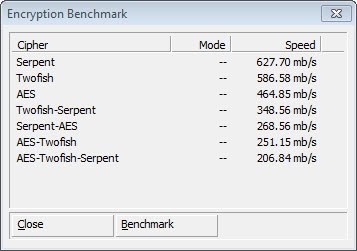
First thing that you may want to do is click on Tools > Benchmark to benchmark all available encryption algorithms. This is important as it directly correlates to the time it takes to encrypt the selected partition. The program supports AES hardware acceleration and cascading algorithms. Please note that the actual encryption process is slower than the speed outlined in the benchmark as you have to factor in disk reads and writes, whereas the benchmark does not.
Once you have done that, it is time to select a partition that you want to encrypt. This is done with a click on the selected partition and the selection of encrypt on the right sidebar menu. Select the algorithm that you want to use, and whether you want to use the program's Disk Wipe feature. The disk wipe feature does not erase unused or used space. What it does is the following:
What "Wipe Mode" does, is that it prevents possibility to recover data by examining residual magnetic energy, which can be done on a specialist equipment. When in "Wipe Mode", DiskCryptor reads each sector's data, wipes the sector, and then writes the encrypted data back to it. So any data that was there before, including deleted files, will still be there when the encrypted volume is later mounted.
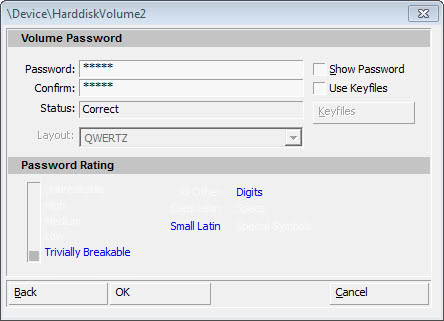
You are then asked to enter a password, select a keyboard layout and optionally select to use a keyfile as well. The program displays a password rating right on the screen. It is recommended to select a secure password consisting of numbers, upper and lower case letters and special characters. Make sure you select the right keyboard layout as you may otherwise run into troubles when you enter the password to mount the encrypted drive.
The program starts the encryption of the drive afterwards. This can take a long time depending on the size of the drive and its speed. It took about 40 minutes to encrypt the main 120 Gigabyte drive of the test system.
If you have encrypted the operating system partition, you are asked to enter the password on boot. Windows will only boot if you enter the correct password.
What I recommend you to do in addition is to backup the headers of all partitions that you have encrypted. The developers of DiskCryptor furthermore recommend to create a LiveCD with DiskCryptor included for emergencies.























Good article EXCEPT it is dated and now most new laptops in 2018 use GUID Boot partitions with UEFI.
BEWARE! DiskCryptor DOES NOT WORK WITH THIS. Even though I thought I read every damned article before I applied this to a client’s Dell laptop… I sadly find out after the fact.