Brave update improves script blocking and Google Sign-In privacy

Brave Software published a new version of its Brave web browser today. Brave 1.51 adds several privacy-focused features to the browser or improves existing ones.
The new version of Brave browser is available already. It should be updated automatically on most devices, but desktop users may load brave://settings/help or select Menu > Help > About Brave to run a manual check for updates. The page that opens displays the current version as well. A restart is required to complete the update.
The official release notes provide a good overview of the changes in the browser. While there are many changes related to Web3, and Brave's integrated crypto-functionality, there are also many improvements in other areas of the browser.
One of the main ones adds individual script allowing to the browser. Many Brave browser users may not know that Brave includes functionality to block scripts that websites want to run. The feature is disabled by default and may be turned on with a click on the Shield icon and toggling Block Scripts in the interface that opens.
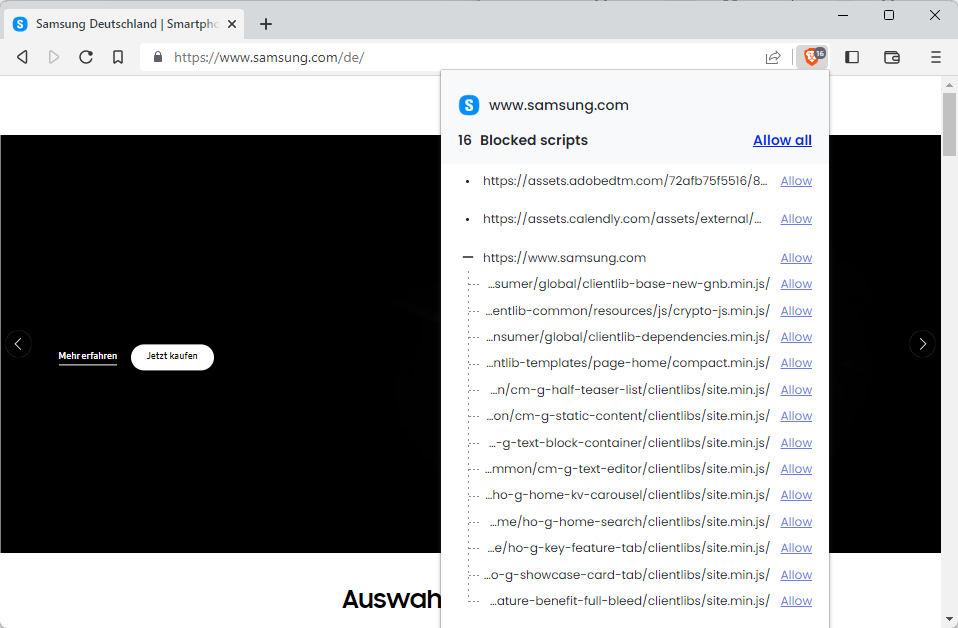
Starting in Brave 1.51, the new version just released, Brave users may now allow some of these scripts. Blocked by default once enabled, some scripts may be required for site functionality, and users may now select to enable these instead of giving the site a carte blanche in this regard.
The functionality is not as sophisticated as that provided by NoScript Security Suite or uBlock Origin, but it gives advanced users more control over the script blocking and allowing functionality.
Another new feature gives users of the browser more control over Google Sign-In requests on third-party sites. We reviewed the feature back in March 2023 already and you may want to check out the article for additional details on the new functionality. In a nutshell, Brave users may now allow sign-in requests on a per-site basis instead of globally. It is a big gain for privacy, provided that the Brave user signs-in to third-party (non-Google) web services using a Google account.
Brave 1.51 comes with a few additional feature improvements. The browser's Speed Reader displays a time to read estimate now and has wider columns for improved readability, Linux users get media notifications for player controls, and captive portal detection has been enabled.
The browser's HTTPS by Default mode will fall back to HTTP now, if the upgrade from HTTP to HTTPS is causing issues, and the browser has been updated to the latest Chromium version next to that.
Closing Words
Brave Software continues to improve the web browser. The new feature to allow individual scripts is a welcome step for advanced users and the highlight of the release.
Now You: have you tried Brave Browser recently?
















May I ask the experts around here an amateur question: what’s the point of all the efforts to hide/spoof your fingerprint if they see your IP address? And the reverse of that: why would I care about fingerprints if they DON’T see my IP address, as is the case (allegedly) with the TOR browser?
Again, to an average user like myself, that sounds similar to Herbert Wells’s “The Invisible Man” paradox where the power of invisibility is all but an illusion; in fact, it strips you from your power.
Where is the line between online privacy and sheer madness and paranoia?
>”why would I care about fingerprints if they DON’T see my IP address”
Because it’s a fun cat-and-mouse game to play. Sometimes it’s refreshing to play the role of the “mouse”.
I don’t really personally care, but then again my fingerprint is constantly changing due to different factors, including the javascript that I allow or disallow at different times for different reasons. And my browser (Pale Moon) has a ‘canvas.poisondata’ config option that causes constant fingerprint changes. So, good luck tracking me through fingerprinting. And I have an extension that disallows cookies or immediately deletes them. Possibly some trillion dollar mega-tech corporations can track me, but like I said, I don’t care enough to do anything special to hide.
@Cor Invictus, may a non-expert bring his answer on the ground he’d be directly concerned by your comment?
Hiding/spoofing is perhaps exaggeratedly evoked for the reason that it participates to tracking in correlation with identification. Of course we’re all fingerprinted and if fingerprinting intervened only in identification than indeed what would be the point given a user’s IP says it all?
I think that for those concerned it is less the fact of being recognized than the fact of being tracked that bothers them : I won’t put a mask when returning to a shop but at the same time I don’t want to have stickers on my back of all the shops i previously visited. Question is, can I do that while being fingerprinted? Those who answer no get to focus on fingerprinting, those who answer yes believe that fingerprinting is in fact secondary when one’s attention should focus on tracking by limiting it (total eradication seems impossible), be it by blocking interconnections between sites, defeating tracking links with ad-hoc tools that send you to the terminus without visiting an intermediary, which make you arrive without a sticker on the url stating where you come from … and so on. Limiting access to third-party sites is essential, blocking cookies as well, especially those of third-parties, filtering scripts : imperative …
Secundo : “why would I care about fingerprints if they DON’T see my IP address, as is the case (allegedly) with the TOR browser?” Because even without your IP address, data-collection may tighten the boundaries of yourself, your life, locality, habits and finally your identity itself. Not to mention that if you’ve been spotted because of a lack of privacy settings and tools, whatever the Tor paths, sites you visit will know that they’ve spotted you already and may laugh of discovering you with a new mask.
So indeed, total privacy requires both : a top-notch OS/browser privacy/security environment AND an excellent VPN or rather a Tor connection in my view but, again, I am NOT an expert. Not being one prevents me from assertions but not from trying to do the best I can within the best I imagine on the basis of what i read, discover, experiment.
@Tom Hawack, Thank you for the reply. It makes sense.
Theoretically, TOR should then be the panacea, and yet, from what I’ve read so far, some people were caught doing illegal stuff because “using TOR makes you stand out like a sour thumb”. I don’t know the cases in point, but the sour thumb analogy keeps popping up over and over again.
At the end, I still can’t shake the feeling that the whole “hiding” online attempt is totally impossible, where TOR appears to be what they call a “red herring”. I don’t know.
I feel like with every effort to counter their tracking and profiling, we’re actually forcing them to get better, and thus unconsciously contributing to our detriment. And with all the TOR’s and VPN’s they’re seducing us to do exactly that. The future will tell.
a) anyone can take from madaidan anything they like that reinforces their presuppositions. He sings the praises of Windows and Chrome and yet in his super-secure Whonix project uses GNU/Linux and a Firefox based browser. Should we do as he says or do as he does?
2) The reason Chrome/chromium has such a large number of security flaws and actively exploited vulnerabilities is sloppy programming in nearly every case. Has nothing to do with the size of their market share. There are many other mega-large projects that don’t have remotely the number of flaws. When was the last time that international credit card processing software had actively exploited vulnerabilities that allowed crime gangs to bounce along and redirect any of the billions of daily transactions they please? Never. And yet you can bet that the crime gangs are constantly poking and testing it, looking for weaknesses.
D) This comment did not need a section “D”, but I am adding it here for the balance and beauty it brings to the comment’s structure. Think of it as comment feng shui.
I dunno but Brave is recommended a lot by folks despite things like Vivaldi having more features. Brave wallet is something i dislike and so is this shield/script blocking thing. Doesn’t uBlock Origin accomplish the same?
They are trying stuff with Brave news and search but few folks use it as of now.
@Kirk
> Doesn’t uBlock Origin accomplish the same?
The adblocking part yes, but Brave also does other things for privacy too like fingerprinting protections, partitioning of local data, protection against pool attacks, it also removes Google connections from the browser itself similar to Ungoogled Chromium… uBlock Origin is comparable to one limited aspect of Brave only.
Plus, adblocking extensions will be neutered when Google makes Manifest V3 mandatory. Brave’s built-in adblocker is not an extension and will thus continue to work as it does now.
Unless you use Firefox. I know the Brave * will deny it, but it is the truth. He’ll use the same tired trope about how Google controls Firefox and they will force them to drop v2 support, but as of now, facts do not support that belief. See link below. He will call Martin a liar and he will also attempt downplay Brave’s heavy use of Google services. Finally, he will use personal attacks that will include the words shill, lol and lmao.
https://www.ghacks.net/2022/09/24/mozilla-reaffirms-that-firefox-will-continue-to-support-current-content-blockers/
Here I am again!!! Who is posting as me?
I get that the Chrome based Brave browser has to support some Google based features, but does someone who uses Google to sign into third party websites really care about privacy?
@Jek they/them Porkins
> I get that the Chrome based Brave browser has to support some Google based features
Yeah, so does Firefox, if you mean the option to use Google websites and to create and use a Google account within the browser. LOL.
What do Google signs-ins have to with Firefox? This story is about Brave. Stop letting Firefox live rent free in your head, you’ll be a lot happier. Instead of ranting about Firefox, do you think someone who uses Google to sign into third party websites really cares about privacy? And can you answer with using personal attacks LOL?
@Jek tHeY / tHeM Porkins
Hey tHeY / tHeM, actually it’s you who came here under a Brave-related article, pestering it with your BS. So it seems like Brave is living in your head rent free and I am merely reacting to your nonsense comment.
> What do Google signs-ins have to with Firefox?
What do Google sign-ins have to do with Brave (your original comment)? Any browser can be used to sign in, including Firefox. You are talking nonsense. Stop trolling.
@Iron Heart
“What do Google sign-ins have to do with Brave”
Look at the the title of the article.
“Brave update improves script blocking and Google Sign-In privacy”
@Iron Heart
– Hey tHeY / tHeM, actually it’s you who came here under a Brave-related article, pestering it with your BS. So it seems like Brave is living in your head rent free and I am merely reacting to your nonsense comment.
I am talking about Brave because this story is about Brave. The only one talking about Firefox is you. Check the posts yourself and see.
– What do Google sign-ins have to do with Brave (your original comment)? Any browser can be used to sign in, including Firefox. You are talking nonsense. Stop trolling.
I never said that. Check again and see. You are suffering from Firefox mind virus.
@Iron heart
Does someone who uses Google to sign into third party websites really care about privacy?
@Anonymous
> Does someone who uses Google to sign into third party websites really care about privacy?
No.
@Iron Heart
What does Brave supporting Google 3rd party sign-ins have to to with Firefox? This story has nothing to do with Firefox.
Stop letting Mozilla live rent free in your head, you’ll be a lot happier.
Google sign-in protection is welcome. Glad Brave is following Firefox’s TCP.
I hate chrome based browsers but if they released a version of Brave without the crypto stuff, I could see myself switch from Firefox. But it’s still chrome and that is the kill switch for me. Anything Google controls, owns, or dictates what I can and can’t do will never be installed my my system or on my phone. Period.
@J. Tripper
> I hate chrome based browsers but if they released a version of Brave without the crypto stuff, I could see myself switch from Firefox.
Or you could just go through the settings of Brave quickly and turn off all crypto-related items, that’s what a lot of Brave users do. Why create a fork? Further, you don’t need to switch from Firefox. Some people like @John G. above keep Brave around for websites that are incompatible with Firefox.
Brave can enable Tor networking and anti-fingerprinting, which sounds good until you realize that top security researcher madaidan refuses to use it in his high security project Whonix. Instead madaidan uses the Firefox-based Tor browser, due to Brave’s high number of chromium-based security exploits and its inferior anti-fingerprinting.
@Andy Prough
Funny how you continually push the misinformation that Whonix uses the Tor Browser Bundle because of Firefox (on which the TBB is based) supposedly having better security, when in fact, they are using the Tor Browser Bundle due to its common(!) fingerprint, which has nothing to do with security = resistance against outside exploitation through malware. Brave is a general purpose browser and everyone who has ever used Tor knows that you are besieged by captchas when you use it, this is not good at all. Also, in all seriousness, what do you know about security, as a Pale Moon user? Moonchild Productions has distributed malware-infested binaries for months without anyone (including you) noticing, I would not take security or privacy advice from their community.
Here are madaidan’s actual reflections on Firefox vs. Chromium security, for anyone interested:
_https://madaidans-insecurities.github.io/firefox-chromium.html_
I’ve just discovered top security researcher madaidan’s articles about privacy and security.
He seems to consider that a truly valid protective environment is only that provided by the browser, that dedicated extensions, user settings regarding privacy and security can be defeated by sites’ workarounds and basically only add user specifics to fingerprinting ; as i’ve perceived it besides Tor no browser can be truly improved externally because, again, improving is not the way to go when the only way to consider is what a browser has in its core, natively.
Tough. I happen to wonder if all the privacy and security settings, enhancements, extensions for which I spend time and effort are rally worth it, if i’m not totally out of browsers’ reality, if i’m not day-dreaming … and now i read madaidan’s articles about privacy and security which would bring an answer to my wondering, and the sort of answer i feared.
Really tough.
@Tom Hawack
‘Tough. I happen to wonder if all the privacy and security settings, enhancements, extensions for which I spend time and effort are rally worth it, if i’m not totally out of browsers’ reality, if i’m not day-dreaming … and now i read madaidan’s articles about privacy and security which would bring an answer to my wondering, and the sort of answer i feared.’
There is one fundamental flaw with madaidan research which in my humble opinion discredits him as a security researcher and makes him more of a sheep.
Madaidan recommends using Windows or MacOS. Why? because they have numerous security improvements over Linux. What about privacy in those operating systems madaidan? Well you can disable telemetry in settings and check it with Wireshark. Same goes for Android – use either GrapheneOS(a very good custom ROM) or don’t use any custom ROM. Well madaidan GrapheneOS can be installed on a Pixel device only which are overpriced(it depends on what is overpriced which can vary between users) but more importantly involves buying a Google product. Other option – don’t use any custom ROM, just use default ROM. Although there are numerous studies which have shown amount of connections an Android device makes to Google servers even without using a Google account on a new device. So you have two options – first use a GrapheneOS, okay that’s a good option. Second use default ROM – laughable option.
madaidan recommends Windows and yet says to not use Firefox because security is weak. Well which browser is suffering from zero day exploits on a daily basis? Also don’t use Firefox because anti-fingerprinting in Firefox is ineffective. Well if you use any Chromium browser, even Vanadium and Brave, you have unique fingerprint anyway. Plus there are Google restrictions on them even if you remove Google connections which can be done in Firefox by user in default settings anyway. Madaidan recommends using a chromium browser which has unique fingerprint for its individual user, reduced customisation, more security issues and less privacy measures available to user. You don’t customise Firefox because it creates a unique fingerprint. First that’s wrong, a fingerprint is already unique in default settings and second RFP exists for those needs. Even if a user doesn’t want RFP or complex settings use default settings since TCP is available and customise it for your needs. Even a customised Firefox is equivalent in terms of fingerprinting when compared to Brave and you’d be using your browser in ways you want.
Madaidan recommends – you don’t customise software and let the experts at Microsoft, Apple and Google do it for you. That’s the biggest red flag. He is a false security researcher. What about fingerprinting in default Android or Windows or MacOS, nevermind privacy? You’re perfectly fine using a Windows OS, not Linux but it is not fine to use Firefox. Which carries more threat – Windows or Firefox? Also give me some real world examples of Firefox security exploitation. I haven’t mentioned Tor yet because Tor is just a network protocol designed to hide traces of your internet connection paths and yet madaidan mixes it with Firefox at every given chance, like a browser is intertwined with a network protocol.
@Yash
> Madaidan recommends using Windows or MacOS. Why? because they have numerous security improvements over Linux. What about privacy in those operating systems madaidan?
Have you missed the fact that madaidan prefaces his security-related articles with a short note that the inclined reader is to keep security (= resistance against outside exploitation via malware) and privacy (= resistance against data collection) apart? Those are not the same thing, and in the following, you continue to confuse or deliberately conflate them.
> but more importantly involves buying a Google product
The ethics of buying a Google product are not the concern of the GrapheneOS project. What the project aims to do is to provide a reasonably secure operating system, and that can only happen on the most secure hardware currently available. That this hardware happens to be manufactured by Google is totally secondary. Other smartphones e.g. do not allow relocking the bootloader and don’t feature the Titan M security chip, just to name two examples.
And as they frequently point out, you always have the option to buy refurbished.
> Other option – don’t use any custom ROM, just use default ROM. Although there are numerous studies which have shown amount of connections an Android device makes to Google servers even without using a Google account on a new device.
You confuse privacy with security (again). Madaidan only discusses the latter in the article you are referring to. Default ROMs receive timely security updates and have e.g. verified boot which gets permanently broken by LineageOS, allowing advanced malware to persist across reboots. This is a security issue independently of privacy.
> Second use default ROM – laughable option.
Not from a security-focused perspective.
> madaidan recommends Windows and yet says to not use Firefox because security is weak. Well which browser is suffering from zero day exploits on a daily basis?
Hey, there is this OS called TempleOS, I have not seen security issues reported on it yet! Must be pretty darn secure then, right? Especially compared to Windows! Or maybe it just isn’t targeted by anyone, because no one uses it? Hmm…
Same is true for Firefox, you know. Firefox is set to be less used than Opera in the near future, their community is currently busy crying about it here: _https://old.reddit.com/r/firefox/comments/137ephs/firefoxs_desktop_market_share_is_on_track_to_fall/_ Why should anyone write malware for an irrelevant product? Why do you expect it to be as targeted as Chromium is, given its proven irrelevance?
Now you will probably tell me: “I’m irrelevant, therefore I’m secure!”, to which I reply that this is not madaidan’s concern. madaidan compares the code bases of each project, the respective strengths and weaknesses of the actual code(!), and not the statistical likelihood of exploitation, like amateurs do.
> Also don’t use Firefox because anti-fingerprinting in Firefox is ineffective. Well if you use any Chromium browser, even Vanadium and Brave, you have unique fingerprint anyway.
Firefox is unique by default and is also unique when you cluelessly modify it according to some user.js (and probably applying further mods of your own on top of that). Brave at least protects some values by default.
> Plus there are Google restrictions on them even if you remove Google connections which can be done in Firefox by user in default settings anyway.
Care to elaborate?
> Madaidan recommends using a chromium browser which has unique fingerprint for its individual user, reduced customisation, more security issues and less privacy measures available to user.
Brave does not have a persistently unique fingerprint, for the values it protects. Less privacy is flat out false. Less security is flat out false. Customization is irrelevant as it’s personal preference, unless you mean about:config tinkering, in which case: Welcome to uniqueness again.
> You don’t customise Firefox because it creates a unique fingerprint. First that’s wrong, a fingerprint is already unique in default settings and second RFP exists for those needs.
“I am already unique, therefore I can’t do further damage by modifying Firefox left and right.” – What kind of logic is that? We are here for substantial improvements, not for placebo. D. Micay says that FF users modify their browser because it gives them the good feeling to have “done something” without it actually reducing uniqueness in the end. I agree.
RFP exists in FF in order to shift the maintenance burden from the Tor Project to Mozilla Corp., it was never meant for you to play around for it. It exists for the Tor Project whose aim is ultimate privacy (no matter the breakage) and who consequently enable it by default(!!!).
> Even a customised Firefox is equivalent in terms of fingerprinting when compared to Brave and you’d be using your browser in ways you want.
Actually no, because a modified Firefox sticks out as such while default Brave (for the values it protects) does not.
> Madaidan recommends – you don’t customise software and let the experts at Microsoft, Apple and Google do it for you.
Inaccurate. madaidan supports and promotes open source and is developing a major open source project (Whonix) himself. He tells you that the ability to verify claims made about a product is important, and open source enables this. At the same time, open source projects can and do have shortcomings. What is he supposed to say when Firefox or perhaps Linux lack several exploit mitigations? Their open source nature does absolutely nothing to change this fact, a fact that is actually relevant to his analysis, contrary to your ramblings.
> You’re perfectly fine using a Windows OS, not Linux but it is not fine to use Firefox. Which carries more threat – Windows or Firefox?
False dichotomy. Due to the broken desktop security model, Firefox (as many other programs) runs with elevated privileges. If you compromise Firefox, you can also likely compromise the OS due to the privileges Firefox runs with.
> Also give me some real world examples of Firefox security exploitation.
Do you pay attention? Even with its limited relevance, several emergency updates of Firefox still patch security issues that occurred in the wild, regular updates too. That’s not the point though. madaidan analyses the potential of exploitation for that codebase, and not statistical likelihoods or singular reported incidents.
May I say that your comment is erroneous in various ways and that it is proof of this blog’s fall from grace?
@Iron Heart
You need to understand there are two different ways to achieve security –
1. You use GrapheneOS or secure OS in desktop and you don’t have to worry about privacy since these projects provide security without comprimising privacy.
2. You create a walled garden like Microsoft, Google do and you provide security. Unfortunately these companies don’t give a toss about user privacy and they make money primarily by selling ads gathering user data in the process. Also Windows, Chromium and Android suffer with zero day exploits on a weekly basis. Even if you use Apple products, these Apple products are the very definition of user privacy violation and prison styled walled garden.
This is where madaidan is wrong. You can talk all security stuff and that’s fine. However you can’t selectively pick fight against Firefox, Linux, other custom ROMs in Android by naming baseless security issues which doesn’t have evidence of real world exploitation, when all the evidence of security issues mainly arrive in Chromium and other big tech products. Firefox, LineageOS and main Linux distros have been around for years and these have been tested, but of course madaidan doesn’t accept that.
‘You confuse privacy with security (again). Madaidan only discusses the latter in the article you are referring to. Default ROMs receive timely security updates and have e.g. verified boot which gets permanently broken by LineageOS, allowing advanced malware to persist across reboots. This is a security issue independently of privacy.’
You do know most of the smartphones sold currently are from Chinese companies unless you live in US. There have been revelations of user data transmissions and the fact that some default apps can’t be disabled makes it even worse. And I haven’t even mentioned underlying issues besides default apps. GrapheneOS is fine but you don’t discredit other ROMs when most default ROMs don’t receive timely updates. LineageOS also supports devices when even their manufactures don’t. Even GrapheneOS doesn’t provide that. Which is more secure then!
Plus unless malicious actors have possession of your device, in that case any device including even Whonix, GrapheneOS is doomed, unlocked bootloaders doesn’t affect devices having custom ROMs or other Linux issues madaidan mentioned.
‘Why should anyone write malware for an irrelevant product? Why do you expect it to be as targeted as Chromium is, given its proven irrelevance?’
Thank you for your ignorance, not shared by security researchers. How many zero day exploits Chromium had this month anyway!
‘Plus there are Google restrictions on them even if you remove Google connections which can be done in Firefox by user in default settings anyway.’
Can you customise your Chromium like Firefox? you can’t. Plus safebrowsing can be disabled in main settings, not about:config stuff, and it’s not a privacy issue anyway. What is Brave doing for manifest V3 changes? For reference, Firefox will support extensions even then. How about addons in Android? This Google sign-in protection feature? Firefox had that since version 86. Plus TCP is lightning years ahead of even these new Brave features and it is available to all users. Uniqueness through add-ons? Affects all browsers but Chromium browsers are more affected, there is even a website where Chromium browsers get tagged when adblocker is detected. So much for your Brave’s fingerprinting protections. What about customising your browser through CSS? CSS doesn’t affect your fingerprint afterall. And I haven’t mentioned about:config yet because you seem irritated by it although there are only two prefs in user.js which affect your fingerprint – RFP and WebGL. Both reduce uniqueness and even Brave tries to copy it but so far because of Chromium, it has failed.
‘Brave does not have a persistently unique fingerprint, for the values it protects. Less privacy is flat out false. Less security is flat out false. Customization is irrelevant as it’s personal preference, unless you mean about:config tinkering, in which case: Welcome to uniqueness again.’
This is false. Visit any website that collects entropy data, then share your results. Brave is not unique. There isn’t even a homogenous pool for Brave users nevermind with other Chromium users. Because there isn’t a pool possible in Chromium browsers.
‘False dichotomy. Due to the broken desktop security model, Firefox (as many other programs) runs with elevated privileges. If you compromise Firefox, you can also likely compromise the OS due to the privileges Firefox runs with.’
Like wtf lol.
You seem to be harmonious with madaidan’s opinions. Good for you. Like madaidan recommends – use GrapheneOS or other secure OS for desktop. I agree with that. Madaidan also recommends Windows, MacOS, iOS, default Android ROMs with infrequent updates and limited support, Brave browser with no add-ons. Sounds like a productive life especially when it comes to browsers.
@Yash, thanks for that input. I don’t have the required knowledge to face up a top security researcher’s assertions even if, naively, some of those martially exposed by madaidan did trigger a slight, irrational discomfort so to say. I read your arguments. Indeed, to make it as short as i understand it, madaidan’ insistence on the pros of Windows, the cons of Linux, the pros of Microsoft, the cons of Firefox is perceived here — basically given my ignorance — as potentially if not biased at least excessive.
It’s always hard to find knowledge associated to intellectual honesty and lucidity, be they disconnected. It’s even tougher to find a technological (or other) truth when experts happen to disagree themselves : I wouldn’t be surprised to discover another “top security researcher” who’d disagree with madaidan’s assertions and argument that disagreement with what would seem as rational and objective.
From there on I’ll bounce on that ounce of incertitude to carry on with my privacy/security crusade :=) but more than ever free of any certitudes and open-minded to what could defeat some of my present beliefs.
@Tom Hawack
> as potentially if not biased at least excessive.
He backs it up with actual sources, contrary to you or Yash. How is it excessive?
> It’s even tougher to find a technological (or other) truth when experts happen to disagree themselves : I wouldn’t be surprised to discover another “top security researcher” who’d disagree with madaidan’s assertions and argument that disagreement with what would seem as rational and objective.
While it’s good to read more than one stance, what do you expect to hear from other security experts / researchers in this case? The exploit mitigations madaidan says are missing won’t magically appear out of nowhere, just because you are talking to someone else. And picking and choosing opinions based on one’s whims, wishes, or preferences, is what a biased and amateurish person who is not actually interested in the facts would do. I mean, go ahead, try to find someone who tells you that Firefox is in fact this highly secure browser that no one else can match, I wonder if you’ll find anybody with a certain level of expertise actually saying this and providing evidence for it.
> From there on I’ll bounce on that ounce of incertitude to carry on with my privacy/security crusade :=) but more than ever free of any certitudes and open-minded to what could defeat some of my present beliefs.
I’ve recently read a comment where someone looked at your dozens of installed extensions and changed preferences and joked that any website you visit would be able to greet you by name, based on that highly unique fingerprint. In all honesty, I chuckled. Because it’s so accurate. Your setup is far removed from “private” if stateless tracking is used on you (so not cookies or anything else locally manageable by you).
@iron Heart, I took a breath and read you ’till the end, whatever the effort.
> “I’ve recently read a comment where someone looked at your dozens of installed extensions and changed preferences and joked that any website you visit would be able to greet you by name, based on that highly unique fingerprint. In all honesty, I chuckled. Because it’s so accurate. Your setup is far removed from “private” if stateless tracking is used on you (so not cookies or anything else locally manageable by you).”
That’s quite an assertion and the comment you mention was wrong. Sites cannot discover the extensions I use and most of my tweaks are only modified prefs. I get a fingerprint, we all do, but no more than with an out-of-the-box Firefox instance. Whatever one’s IP remains the main signature. If I do nevertheless add privacy extensions (i.e. CanvasBlocker), if I block 3rd-party cookies together with First-Party Isolation rather than Firefox’s defaults it is mainly for when surfing via a browser-only VPN. Otherwise the simple IP says it all as for my visits, though far less when it comes to tracking via scripts, cookies, session/local storage, IndexedDB.
We try. As I said and repeat no certitudes here so please give me a brake with yours, ok?
@Iron Heart, I had written ” is perceived here — basically given my ignorance — as potentially if not biased at least excessive.” : “is perceived here, basically given my ignorance”. Perception and stated as such. What more would you require to not mistake an assertion with a general impression. Why do you always have to create clashes as if you needed them to state your truth? I’m searching, my friend, only searching. There’s what you say and the way you say it. Be civilized for a change.
Don’t pay attention to him or his personal attacks. I suspect Martin allows him to ignore the comment section rules because he knows when Iron Heart insults a poster, they will come back to respond. which is more clicks for him.
Don’t fall for it.
Wow! I’m reading this article for the first time, and someone answered as me. LOL
Oh well, I can’t believe how long it’s been since I’ve actually had a reason to post on Ghacks. Heck, even “Shaun” doesn’t seem to post as many articles anymore. I used to come here everyday, whereas now a whole week goes by without me even reading Chacks.
It’s a good point Tom, and one of the main reasons I’m thinking of switching my secondary browser from Librewolf to the Mullvad browser. The thing about Mullvad browser is that it already has everything I would want in a Firefox-based browser – the strongest anti-fingerprinting along with built-in uBlock and noscript. I can use it without changing a thing.
I know that you’ve listed your browser requirements and that Mullvad does not fit them all that well, so I’m assuming your journey will probably continue. An interesting thing to note is that the work that you and Martin and a bunch of the earlier Ghacks commenters did in coming up with the Ghacks user.js, which morphed into the arkenfox user.js, is privacy settings that are now used in Librewolf, Tor browser and Mullvad browser. So in an interesting way there’s been a complete cycle of going from the hacking you were previously doing to some of us being presented with a complete turn-key privacy browser.
> arkenfox user.js, is privacy settings that are now used in Librewolf, Tor browser and Mullvad browser
Except actually the Tor project came up with most of the configuration and Mullvad is actually partnered with the Tor Project. It’s only correct for LibreWolf. But hey, who cares, right?
Isn’t Mullvad just meant for users of Mullvad VPN; also, IIRC , it’s a reskin of Tor, right?
>”Isn’t Mullvad just meant for users of Mullvad VPN”
No. Anyone can use it, with or without any VPN.
>”also, IIRC , it’s a reskin of Tor, right?”
No. It is a browser that uses some of the same technology as the Tor Browser for anti-fingerprinting and other privacy concerns. It does not require the Tor network protocol, whereas the Tor Browser does require that you use the Tor network protocol. If you use the Ghacks search box at the top of this page, you’ll find that Ghacks has two recent articles on this browser where you can find out a lot more information.
I dislike some things about Chrome, however here in my country the Chromium based browsers are the only ones that are enabled to run the national identification card directly after a clean install. Nothing to add, nothing needed, just install and just use it with no issues at all. The configuration and the procedures to run the national DNIe with Firefox can be the worst experience ever. That’s the reason of near all people here use Chrome (and some enterprises are still using IE11 due to a few old major Java requirements, and minor ones like SilverPluging). By the way, Brave is also able to run the DNIe with no single issue, a match point already.
Firefox isn’t supported for some sites, sadly. It didn’t used to work for MS Teams for me back in the day.
For some sites though, spoofing the user agent usually via an add on works.
Also, all these features are old, there are more important features being implemented in Nightly recently. Couple days ago Brave released the sidebar Chat AI summarize feature and yesterday finally Bitcoin backend was released, until it gets proper UI and all that, same with keyboard customization, it still needs a UI in settings and all that.
Pinned tabs across windows is also nice and commander in the omnibox instead of being a separate bar was also added couple months ago.
And then Playlist and vertical tabs being WIP, and VPN being improved by finally getting the Wireguard integration instead of relying in OS APIs, which was buggy and terrible in Windows, they want to let users launch Brave VPN outside the browser and all that as well.
So they are more exciting things than Google sign-in permissions.
Even the “Added support for scriptlet arguments with quotes or backslashes”, is more exciting because the scriptlets injection filters, especially ##+js(rc…) will finally work 100%.
The Block Script feature was removed years ago because it was buggy and not working as intended and now it was re-added. One of the problems it had in the past was that it wouldn’t allow scripts properly, mostly inline scripts.
It does what it is supposed to do, temporary allow Scripts if necessary, so I don’t get this “The functionality is not as sophisticated as that provided by NoScript Security Suite or uBlock Origin”, when it is obvious that’s not what Brave Team wants.
If people want to be more ‘sophisticated’ about it, they can use the Adblocker, preferably with CSP, since CSP will not override existing Network filtering rules, but Network filter rules would be fine as well.
That’s how it is done and it works fine if people want. If you want easy buttons to do the same in one click, then no, but it doesn’t mean it can’t be done in Brave. In fact, if you use the Block Script in uBlock panel, you will see how console says it is doing CSP internally.
So, manually writing rules is not going to kill anyone if people really want to do something globally or in specific sites.