Microsoft releases PowerShell script to address Windows Bitlocker vulnerability

Microsoft has released a PowerShell script for Windows 10 and 11 devices to address a BitLocker security feature bypass vulnerability.
Microsoft confirmed the issue on November 8, 2022. It is tracked as CVE-2022-41099. Successful exploitation of the issue allows attackers to bypass BitLocker Device Encryption protections on the system storage device, according to Microsoft's description. Physical access to the device is required to exploit the vulnerability and access the encrypted data.
Microsoft released a security update for the issue, but system administrators had to install it to the Windows Recovery Environment manually up until now.
Tip: Microsoft released security updates for all supported versions of Windows this week.
PowerShell scripts address the BitLocker bypass
Microsoft's newly released PowerShell scripts aims to automate the updating process. All system administrators need to do is run the PowerShell script on Windows 10 or 11 devices to patch the Windows Recovery Environment and protect it against potential exploits of the security issue.
Two PowerShell scripts are available. Both serve the same purpose, but the target Windows versions are different. PatchWinREScript_2004plus.ps1 is the recommended script. It is compatible with Windows 10 version 2004 and later versions, which includes any Windows 11 version.
Microsoft notes that the script is more robust than the other, and that administrators may want to run it, provided that the device that needs fixing runs a supported version of Windows.
Older Windows 10 devices, those running Windows 10 version 1909 or earlier, need a different script. Microsoft notes that the second script should execute on more recent versions of Windows 10 and 11 as well.
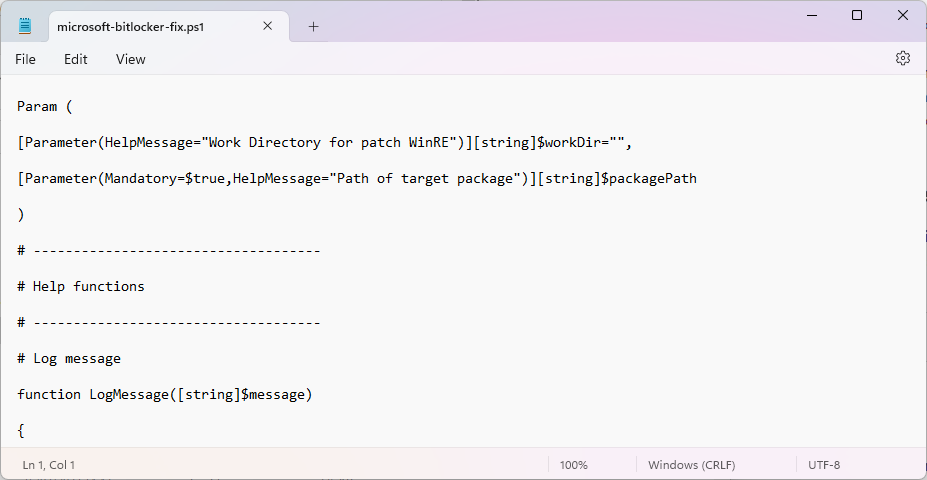
Only the source codes of both scripts are displayed on the Microsoft support website. Users need to copy the entire script and paste it into a plain text file on the device. The file needs to be renamed from .txt to .ps1, to make it a PowerShell script.
The script performs the following steps to address the issue:
- It mounts the existing WinRE image (WINRE.WIM).
- The image is updated with the Safe OS Dynamic Update package from the Windows Update Catalog. This update needs to be downloaded manually for the operating system and specified using the packagePath parameter.
- The WinRE image is unmounted.
- It reconfigures the BitLocker TPM protector if present.
System administrators may run the script with two parameters:
workDir -- <Optional> Specifies the scratch space used to patch WinRE. If not specified, the script will use the default temp folder for the device.
packagePath -- <Required> Specifies the path and name of the OS-version-specific and processor architecture-specific Safe OS Dynamic update package to be used to update the WinRE image.
Closing Words
The BitLocker vulnerability requires local access to the Windows PC to exploit the issue. While that makes it less of a threat for many users, it may still be a good idea to run the PowerShell script to protect the device against attacks.
It is recommended to create a system backup before running the script. If things go wrong, it can be used to restore the previous state of the system.
Now You: do you use BitLocker? (via Neowin)



















the script will accept anything as the packagepath and run through its process and say success, at least on my machine it does. so I have no idea if it actually worked.
Why don’t they apply the scripts using WSUS as unattendant update? OMG people!
Because not everyone uses BitLocker?
My bad, I didn’t read the article thoroughly and my mind was thinking this was BitWarden. Didn’t get enough sleep last night, I guess…