Mozilla still on track to enable DNS-over-HTTPS by default in Firefox
Mozilla published a list of requirements that companies need to meet if they want to be included as Trusted Recursive Resolvers for Firefox's upcoming DNS-over-HTTPS feature.
DNS-over-HTTPS aims to improve user privacy, security and the reliability of connections by sending and receiving DNS information using HTTPS.
Mozilla ran a Shield study in 2018 to test the DNS-over-HTTPS implementation in Firefox Nightly versions. The organization selected Cloudflare as its partner for the study after Cloudflare agreed to Mozilla's requirements to not keep records or sell or transfer data to third-parties.
Firefox users may configure DNS-over-HTTPS in the browser. Mozilla plans to make it the default in Firefox going forward; while that is beneficial overall, doing so comes with its own set of issues and concerns.
- Firefox will use the feature for DNS related activities and not the DNS configured on the computer. Means: local hosts files, resolvers, or custom DNS providers will be ignored.
- The selection of Cloudflare as the first partner was controversial.
Mozilla plans to make DNS-over-HTTPS the default in the Firefox web browser. Firefox users may still disable the feature once Mozilla makes the switch from off to on though.
The organization wants to select a number of companies for use as Trusted Recursive Resolvers in the Firefox web browser. To address concerns in regards to privacy, Mozilla created a list of policies that these organizations need to conform to.
- User data may only be retained for up to 24 hours and that needs to be done "for the purpose of operating the service".
- Aggregate data may be kept for longer.
- Personal information, IP addresses, user query patterns, or other data that may identify users may not be retained, sold, or transferred.
- Data gathered from acting as a resolver may not be combined with other data that "can be used to identify individual users".
- Rights to user data may not be sold, licensed, sublicensed or granted.
- Resolver must support DNS Query Name Minimisation (to improve privacy, the resolver does not send the full original QNAME to the upstream name server).
- The resolver must not "propagate unnecessary information about queries to authoritative name servers".
- Organizations need a "public privacy notice specifically for the resolver service".
- Organizations need to publish a transparency report "at least yearly".
- The company that operates the resolver should not block or filter domains unless required by law.
- Organizations need to maintain public documentation that lists all domains that are blocked and maintain a log that highlights when domains get added or removed.
- The resolver needs to provide an "accurate NXDOMAIN response" when a domain cannot be resolved and not alter the response, e.g. redirect a user to alternative content.
Mozilla's system will be opt-out means that it is enabled by default for all Firefox users if Mozilla does not change that prior to integration in Firefox Stable.
Now Read: Is Mozilla's new DNS feature dangerous?





















female,
Yes, you DO have to Worry!
Your VPN will Not be working for you in Firefox! If you complete the steps for this new thing.
(That is my understanding of what was said in the article and comments. Anyone please correct me if I am wrong, or add more info.)
@Martin Brinkmann
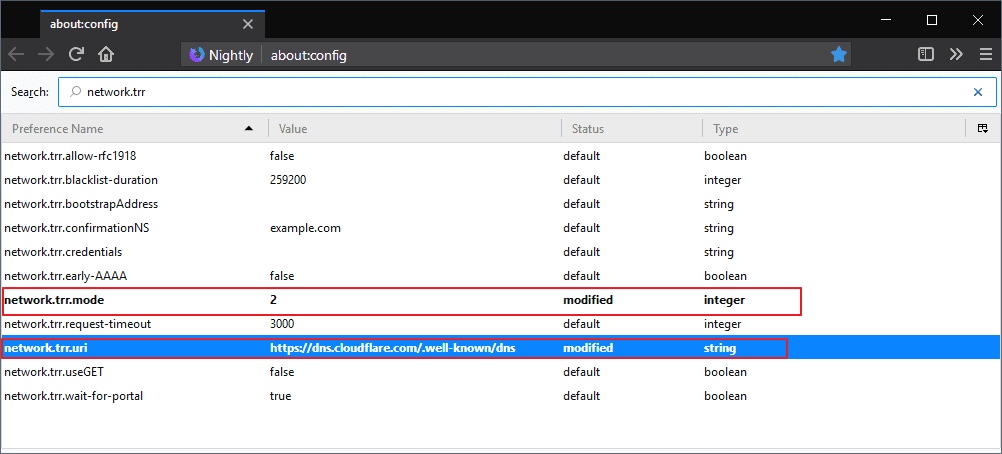
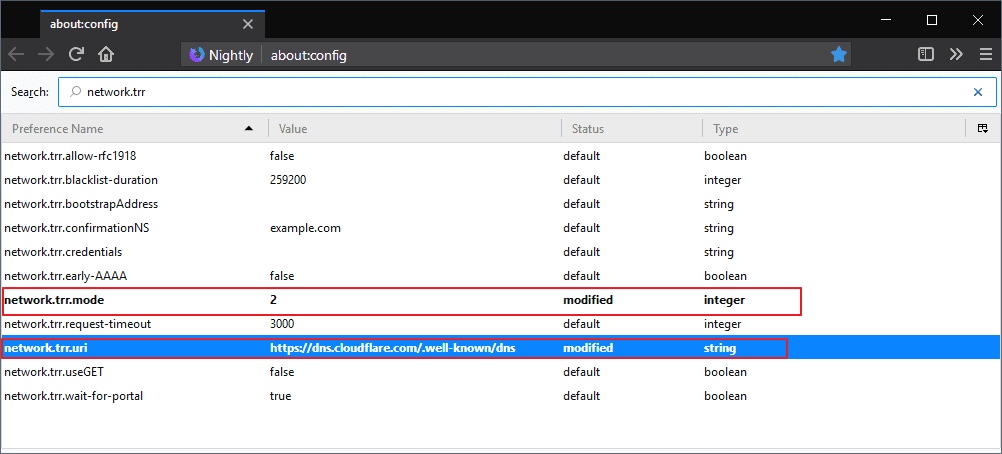
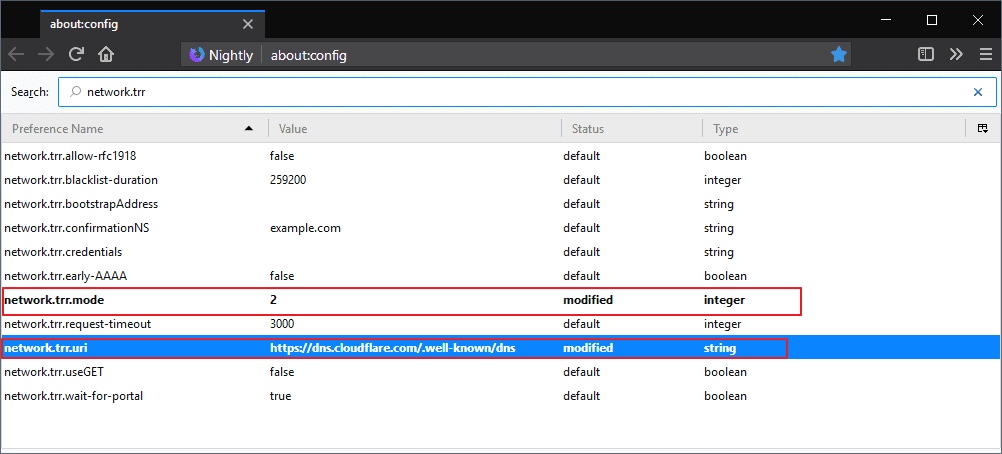
so if I choose to make the configuration in about:support shown in your post, I dont have to worry about the issues mentioned in the comments above? neither privacy nor security issues?
I use vpn
I suggest you follow the guide here: https://www.ghacks.net/2018/04/02/configure-dns-over-https-in-firefox/ and load the links that point to Mozilla and GitHub as well for verification.
@Martin Brinkmann
thank you for the link
Mozilla is just a foreground for Google, on of their main sponsors. When Google wants to do something not-so-nice they test the ground first with Firefox engineering team. If it goes silent they do it, if not they give up, at least for a while. Mozilla get the money, officially for the inclusion of some Google links and all are happy. Such features that break internet should be easy to enable / disable and be off by default, not hidden behind a flag that maybe removed some day.
Mozilla, the company who knows what is the best for you, who could transform a NO in YES against the sovereignty of the people (like Sarkozy and Hollande with the French European referendum). Mozilla, an elite wanting a Europe without copyright law against creators. Firefox, their instrument for a global control bypassing the hosts file in my back. Firefox Quantum, a “DANGEROUS” part yes of the globalized and soulless financial world at the image of its new childish pedagogical design. Don’t touch my DNS you M…
…private or ‘secure’ ?
8.8.8.8 System DNS or 1.1.1.1 Firefox DNS ? Euther way, you’re tracked!
‘Mozilla wants to select a number of companies for use as Trusted Recursive Resolvers in the Firefox web browser.‘
Trust in Google guys!
One thing that could be dangerous is the fact that when using a system-wide VPN, Firefox will still use its own DNS, bypassing the DNS server of the VPN. Not all users would be aware of that and even users aware of it could forget to turn it off.
.. and the hosts file bypass occurs with vpn proxies as well. That problem is solved by ubo as the entire hosts file loopbacked addresses can be added as a filter: myfilters or custom filter.
True, but needless to say we connect not only within Firefox and therefor a system-wide DNS protection needs to be available. Hosts files managed and by the OS and by uBO is redundancy unless I disable the OS Hosts blocking when running uBO … cumbersome, and inadequate given I may have other connections from other applications while running Firefox. Which is why I handle the Hosts file from Windows and delegate protection to uBO/Firefox for other than Hosts filter lists.
There’s also the fact that uBO doesn’t handle (such as, anyway) so-called behind-the-scene connections established by extensions, some of which may be undesirable yet blocked by the system–wide hosts file.
Also, DNS protection is provided system-wide by other means than the Hosts file, for instance applications such as PeerBlock which handle IP ranges : here that app handles at this time over 128,000,000 (128 million) IPs … no browser-specific extension could do that.
Which is why I intend to keep on managing DNS on the OS level and will never adopt whatever parallel resolver.
It is not dangerous, and there are quite a few dns providers that support it.
esni can also be enabled via about:config, but that is not yet widely implemented by dns providers. Cloudflare has it enabled and can be tested on their site.
Some alternative providers are listed here:
https://github.com/curl/curl/wiki/DNS-over-HTTPS#publicly-available-servers
Link is in the feature author’s original post at:
https://daniel.haxx.se/blog/2018/06/03/inside-firefoxs-doh-engine/
Having in-browser tools like this is usefull especially for mobile devices.
“Is Mozilla’s new DNS feature dangerous?”
I think so, yes. It’s a clear security problem in that it makes it very easy for malware, malicious sites, and advertising agencies to use it to help avoid detection and blocks.
I think it’s dangerous enough that I’ve already implemented a MITM packet inspector to prevent it from working in my home network.
I’m really angry with Mozilla for doing this.
DoH and similar solutions have to be done on OS level and not per application. thats ridiculous. imagine every net application uses its own dns infrastructure. either mozilla provides a dns tool that runs as system service (or adds hosts to dnsscrypt eg) or let it be. but not come with a solution that circumvents/ignores all the dns settings on the host.
@Anonymous:
I agree. If Mozilla had provided this as an OS-level tool, it would have been fine — great, even. But at the application level, this is a disaster in the making.
“Means: local hosts files, resolvers, or custom DNS providers will be ignored.”
So DNS-over-HTTPS by default will exclude dnscrypt-proxy and Acrylic services?
DOH and DOT replace DNScrypt.
I mean theoretically it’s a good Thing, should make it opt-in though. If they add a popup and actually ask the user, all would be satiesfied.
The problem is that most users probably would not be able to make an educated decision. Opting in automatically and informing the user (we enabled This, you can turn it off here) before any more connections are made might work best.
I agree that Mozilla should display a notification at the very least to users.
What caught my eye right when I opened this page was the innocuous use of the little word “track” in the title. From a SEO point of view, a true stroke of genius, Martin!
The article reports that “Mozilla plans to make DNS-over-HTTPS the default in the Firefox web browser.” and I truly disagree with that choice. Also, “Means: local hosts files, resolvers, or custom DNS providers will be ignored.”
Many “semi-technically inclined” users know at least and rely on the system’s Hosts files, configured by them to block hosts they’ve decided to block. If these users are not aware that a latest version of Firefox now includes DNS-over-HTTPS natively active they are bound to surprises.
“custom DNS providers will be ignored.” : I won’t accept that.
But but but … if Mozilla plans to include DNS-over-HTTPS natively, I just cannot accredit the idea it is for any other reason than the user’s safety. I won’t, at this time anyway, fantasize on yet another accusation of tracking users. Also, and although I personally dislike and avoid telemetry on the ground it’s application is likely to correspond to tracking, I couldn’t swear it is, or always is. But when there is a doubt in the mind of a non-specialist who happens to cherish privacy the principle of caution is worshiped even if it may appear as an over-reaction in some given schemes. There’s just too much craps on the Web and within applications themselves, be it privacy, be it security related that either you do nothing, you do too much… or you spend the time you don’t always have to start an extensive computing course.
This is like homepage ads in Firefox : claim that it was only experiments, keep low profile and wait that everybody forgets about the huge controversy, then do it again but even worse.
The first experiments were just experiments. Quite clearly, otherwise it would have already been implemented fully back then. But these experiments were never done with the goal to not implement this eventually.
DNS is an absolute privacy nightmare. DNS-over-HTTPS is certainly not free from problems, but I have yet to hear an argumentation why regular DNS was better over all.
@Anonymous:
I agree, DNS is a privacy nightmare. But we need to fix DNS, not engage in this DoH sort of nonsense.
“I have yet to hear an argumentation why regular DNS was better over all.”
From my point of view as the operator of my own network, DoH presents a serious security problem. It reduces my ability of me to protect my network by blocking the lookup of known bad domain names.
To protect my network, the existence of DoH means that I have to install an HTTPS proxy to man-in-the-middle that traffic in order to catch DoH lookups. This puts me in the less than wonderful position of having to decide which security I will weaken — I can reduce the protection of my end points by having to MITM them, or I can reduce the protection of my networks overall.
That sucks. But, being forced to choose, I choose to not to weaken the protection of my network overall.
“But these experiments were never done with the goal to not implement this eventually.”
Maybe, but they remained publicly ambiguous about their plan to make it the default and used this as a defense against critics ; just a few examples :
https://www.reddit.com/r/firefox/comments/94xanz/is_mozillas_new_dns_feature_really_dangerous/e3p748m/
> There are no plans to push this to release
(from a Mozilla employee)
https://www.reddit.com/r/firefox/comments/94xanz/is_mozillas_new_dns_feature_really_dangerous/e3rw4xu/
>This was an opt-in performance experiment to gather data on a feature that they MIGHT ship some day. Unless you possess a crystal ball or secretly work in Mozilla’s network team, you have precisely zero information on how that feature MIGHT eventually behave, IF it ever actually ships.
Likewise, many anti-features are tested as experiments so they can retract if the backlash is too strong, remember Cliqz and Mr Robot ?
“I have yet to hear an argumentation why regular DNS was better over all.”
If you’re genuinely interested, read
https://www.reddit.com/r/firefox/comments/b9q4wk/dns_over_https_add_on_icon_added_to_my_browser_is/ekb1j0p/
and the technical explanations that follow. Or
https://ungleich.ch/en-us/cms/blog/2018/08/04/mozillas-new-dns-resolution-is-dangerous/
How will this affect paid VPN users?
More privacy rape by US tech giants in business with Mozilla, with close to zero user benefit in exchange. They’ll soon get our browsing data and just promise to be nice with it, yeah we heard that before from them.
Sounds like you didn’t actually read the article. If you did, read again.
@Anonymous You don’t know what you are talking about. Thanks to DNS-over-HTTPS i’m able to visit websites that are blocked by my ISP. Cloudflare is just one of many options. I’m using SecureDNS.eu as my default DoH in Firefox. IMO it’s one of the best features that Mozilla has implemented in their browser.
@Malte
DnsCrypt
@Malte
You switching provider because of your censorship problem and understanding the privacy risk is ok. You didn’t even need Mozilla to do that actually, you’d better have done it at the OS level. But Mozilla switching everybody by default for their selected partners is not. It’s definitely an abuse of user trust.
It’s not true at all that there is no user benefit. But yeah, it’s always easy to complain.