Here comes the next Spectre vulnerability (Spectre V4 CPU)
If you thought that you are done patching your devices against Meltdown or Spectre exploits, you might want to reconsider. Patches for some hardware configurations and operating systems were released by Microsoft, Intel and hardware manufacturers ever since the vulnerabilities were revealed in early 2018.
Hot on the heels of the news of newly discovered Spectre Next Generation vulnerabilities comes news of a new threat that Microsoft and Google disclosed recently.
AMD published a whitepaper which you may access here.
Intel published information on the company's Newsroom website about Spectre Variant 4. The new vulnerability affects processors by Intel, AMD and ARM and uses speculative execution just like other Spectre variants disclosed earlier this year.
The web browser is the most likely attack vector for Variant 4 as the researchers demonstrated the vulnerability in a language-based runtime environment.
Like the other GPZ variants, Variant 4 uses speculative execution, a feature common to most modern processor architectures, to potentially expose certain kinds of data through a side channel. In this case, the researchers demonstrated Variant 4 in a language-based runtime environment. While we are not aware of a successful browser exploit, the most common use of runtimes, like JavaScript, is in web browsers.
Intel is not ware of exploits in the wild and believes that mitigations deployed by browser developers to protect or mitigate against previous Spectre variants help mitigate Spectre Variant 4 attacks as well.
Still, Intel and the company's software partners, offer "additional mitigation for Variant 4". In other words, microcode and software updates. OEM manufacturers received beta versions of the microcode update already and Intel announced that it plans to release the final versions in the coming weeks.
The company plans to release the update in an off-state by default giving customers the option to enable it, or not. The updates won't affect performance of systems they are installed on in off-state. System performance may drop by 2% to 8% in benchmarks if the mitigation is enabled according to Intel.
The same update includes microcode that protects against Spectre Variant 3a. Intel made the decision to bundle the two updates to "streamline the process for our industry partners and customers".
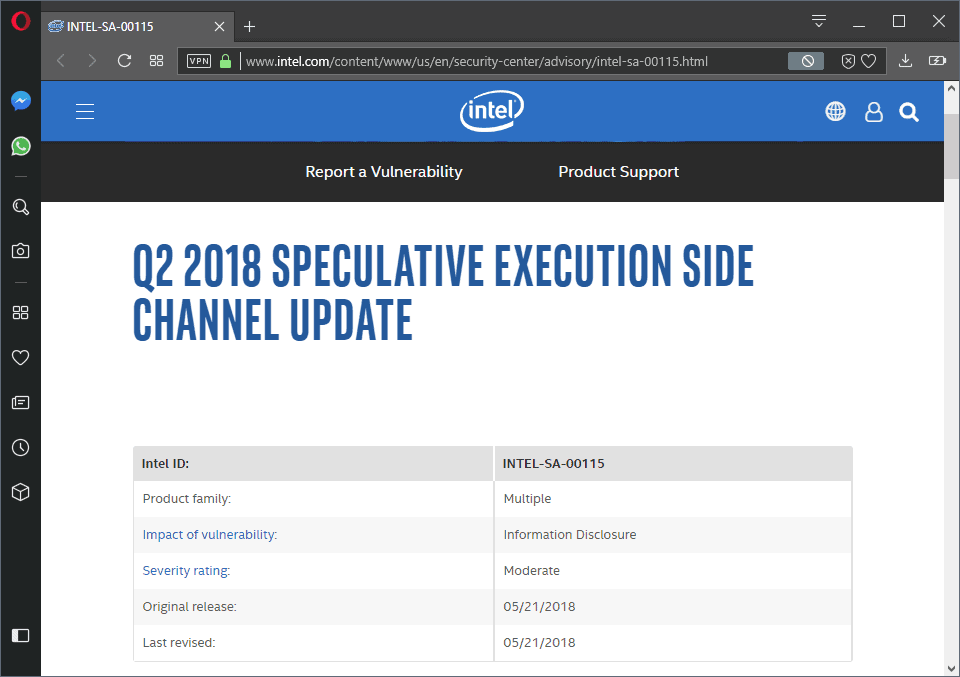
Additional information about affected products is available on the Q2 2018 Speculative Execution Side Channel Update page on Intel's Security Center website. The page lists all affected Intel processors, recommendations, and other information.
Related articles
- New InSpectre release reveals if microcode updates are available
- Ashampoo Spectre Meltdown CPU Checker
- Check Linux for Spectre or Meltdown vulnerability
- Find out if your Windows PC is affected by Meltdown/Spectre vulnerabilities


















Well, I’m patched for now with no visible performance loss. Yet as others have said, there is no real long-term fix without a new CPU that is free from this ongoing threat.
As such, being that I will have to eventually upgrade, I’m likely going to wait even longer until those CPUs also support AV1. That looks to be happening in 2020. And even without this threat, I likely would have upgraded just to get AV1 support anyway, so no big deal there.
Also, as for security threats until then, as need be, I will just stop using the web for anything financial and such. I know that may be hard for some, but it’s no big deal for me, and I actually see it as luxury I can afford, if it comes to that, and I think it has.
For Linux folk:
#cat /proc/cpuinfo
and scroll down to: “bugs”
……And then:
#cat /sys/devices/system/cpu/vulnerabilities/*
and/or:
#head /sys/devices/system/cpu/vulnerabilities/*
It doesn’t fix anything, but it does show vulnerabilities and what not.
Very good approach Richard, only thing I would add is using Sumtra PDF reader instead of Adobe.
They say with many of the Spectre and latest exploits that there are no known attacks.
The key word here is “known”. Hackers would probably need to be sophisticated to exploit systems but would we ever know that we have been hacked.
It seems the later the hardware here the more your system is probably under threat.
You are probably safer with a C2D processor here with the 2 threads and the limited CPU architecture.
Obviously this will surely be addressed over the next couple of years we hope.
Core 2 Duo processors aren’t impacted here. I will keep using that laptop in preference to a Sandy Bridge Laptop.
The newer the hardware and software the more sophisticated the malware and the less secure the system apparently.
@shawross
You think?
Intel Core 2 Duo Processors: T6400, T6500, T6670, T8100, T8300, T9300, T9400, T9500, T9550, T9600, T9800, T9900, SU9300, SU9400, SU9600, SP9300, SP9400, SP9600, SL9380, SL9400, SL9600, SL9300, P7350, P7370, P7450, P7550, P7570, P8400, P8600, P8700, P8800, P9500, P9600, P9700, E7200, E7300, E8190, E8200, E8300, E7400, E7500, E8400, E8500, E8600.
These chips are vulnerable to the Spectre and Meltdown flaws for the rest of time. Intel is not providing fixes for them.
Source:
https://www.rockpapershotgun.com/2018/04/05/intel-stop-meltdown-spectre-updates-for-old-cpus
If you have an unpatched CPU, then expect that at some point in the future some malware that will own you.
I’m not going to recommend that anyone not apply the firmware/BIOS updates but I have to this point not used any on my computers nor do I have any plans to do so in the future. For Win7 OS updates I have for the last year and a half been doing the Security Only updates and apply those updates only after Woody Leonhard gives the go ahead. I’ve been following Woody’s advice for about 10 years over @ “https://www.askwoody.com/”. After applying the Feb. updates I decided to roll back to the Dec. updates because at the time it was just a cluster with one botched update after another starting with “Total Meltdown”. I just recently, May 10th, applied the OS updates, up till April. I have not yet applied the May updates. And I’m using “InSpectre” to reduce the performance impact of the Meltdown patch. I haven’t had to deal with a bad update on any of my computers since my Windows XP days and I’ve been using Win7 since it was released. All that said, I also haven’t seen a virus, trojan or even a single malware object on Win7, on my hardware.
This is just my opinion, but for years I’ve thought that the most important security software on my computers is the browser, how it is configured and most importantly, what extensions are being used. I’m not saying anyone should do it but I would be fine not running anti-virus software if the OS wouldn’t constantly complain about it. On Win7 I’ve only ever used MSE and Malwarebyte’s Anti-Exploit, that’s it. I don’t have flash installed, if a website needs flash I’ll open Chrome Dev. I don’t view PDFs in a browser, I instead use Adobe Reader with js (javascript) disabled. If I don’t know you I won’t open your email attachment and even then I’ll think about it.
I use uBlock Origin in all of my browsers and have been using since it had to be downloaded from github, long before it was available on AMO (addons.mozilla.org). I globally block iframes and many sites have 3rd party js disabled. Why do some websites need to connect to 50-60 different domains? That’s crazy! The only other security extension I use is No-Script Suite Lite which is only used as a js whitelist and because it automagically disables js when visiting a new website, unwanted redirects are no longer a big security threat.
Those people not using a content blocker in their browser should be keeping all of their software updated, including the OS, and should think very hard about having system backups.
I bought this desktop two years ago next week and I’m still in a major way seriously pissed that at that time MS started saying they would end support for Win7 Skylake CPU’s early. So… instead of getting the Win7 Pro desktop I found with a Skylake Core i7, I got one with a Haswell Core i5. And then… after I made my purchase, Redmond decided to not go ahead with their plan to end support early, for Skylake, on Win7. WTH? Point being, I downgraded my CPU when I bought the desktop and the odds of my downgrading again with a firmware update are slim to none. To be honest, I would very much like some “personal interaction” with whoever is responsible for the whole Skylake support on Win7 fiasco. With everything that has happened in the last two years, am I supposed to want to use the Win 10 Pro license that came with my desktop? They’re joking right? The odds of me purchasing any MS product in the future is non-existent and my next OS change will likely be Linux Mint, if I don’t stay on Win7.
Install NoScript or uMatrix and you should be fine on browsers.
I think they need to redesign CPU’s and GPU’s in a way where everything is software and the chip only act as hardware providing performance and stuff, basically things only hardware can do, everything else becomes software. So with this redesign if we want to upgrade CPU or GPU we simply update the software Linux OS inside CPU and GPU. Changing the CPU and GPU on hardware level won’t be needed as often. With this you can install any number of CPU’s or GPU’s on firmware as they will be just Virtual CPU like software.
Dark what you’ve just said is one of the most insanely idiotic things I have ever heard. At no point in your rambling, incoherent response were you even close to anything that could be considered a rational thought. Everyone reading your comment is now dumber, for having read it. I award you no points, and may God have mercy on your soul.
Hate to wade in on something that’s none of my business, but dark’s comments indeed really do not make much sense.
We’re all on a learning curve, that’s the way I see it.
What a great way to promote future processors that avoid all these issues. If you update your current processor, you bring it to a crawl. So you’d better buy a new one when they come out.
I’ll take my chances. I’ve had Windows updates turned off my Win7 machines for quite a while now. I feel that my best protection is regular backups. That way I avoid the havoc caused by MS meddling with my system and breaking things. Too often applications I depended on have been broken never to be useful again.
But Intel is secure that only the CPU on his page are affected?
Nice…after installing all current and future patches my 5820k’s performance will be on par with old C2D’s or P3’s.
At the beginning of this year I took a wait and see approach regarding updating my Windows 7 PC. I wanted to update at the end of April, but MS managed to break the OS more than fixing it, so I did not update.
I’m so happy with my decision, seriously. Let them bash their heads against a wall until, if, they’ll ever fix it. I have no desire to install any updates until the end of this year. Seeing what a shitshow has been since January 2018 in the MS Windows Updates land, I simply can’t believe they’ll get it, somewhat, right on their first try now either.
I’m also using the Simplix’s Update Pack from December 2017 to update any fresh Windows 7 installations I’m doing – hence bringing the OS up to date without breaking it.
BIOS updates too! Forgot about them. Nothing past December 2017.
Given the performance hit with the fix, I am seriously going to consider letting go of that vulnerability. I know that these are security risks but sometimes I do think that these are actually remote and might only happen to you if someone actually targets you. I am happy just running my antivirus and not patch the vulnerability at processor level.I want to keep my PC up to par to run a few games. Let Amazon and Microsoft patch their server farms.
What do you think ? I might be wrong and I would actually like to hear what others think. @martin?
Thank you all for your replies. Lots of interesting views and comments. As you guys mentioned, security is a personal choice as well. I will skip these upcoming fixes for spectre v4 at least for this year. Better have a PC that performs rather than a secure one which crawls
@ Raj
https://wiki.ubuntu.com/SecurityTeam/KnowledgeBase/Variant4
“Mitigations
Some mitigations for Spectre v2 also help to mitigate some of the effects of this vulnerability, for example, the reduction in timer precision in browsers renders this variant much more difficult to exploit.
The Speculative Store Bypass vulnerability can be mitigated by setting the newly defined Speculative Store Bypass Disable (SSBD) bit in the IA32_SPEC_CTRL Model-Specific Register (MSR) of x86 processors. Support for this mitigation requires updated microcode for Intel processors.
In Ubuntu, SSBD is OFF by default because it is not needed by most programs and carries a notable performance impact. A prctl() has been added (PR_SPEC_STORE_BYPASS) that enables developers to opt into the mitigation on a per process basis. Applications using a seccomp filter will be implicitly opted into the mitigations. This means that strict and devmode snaps, processes inside of LXD containers, sandboxed processes of the Firefox and Chromium browsers, among some other processes running in a default Ubuntu install on x86 processors, will have the SSBD mitigation enabled out of the box.
Users can explicitly opt-in to SSBD mitigations, on a system-wide basis, by booting with the spec_store_bypass_disable=on boot parameter. See the Mitigation Controls page for details on available boot options. ”
_ _ _ _ _ _ _
Since Ubuntu 18.04 uses Snaps, mitigation for Spectre v4 via kernel updates is enabled by default. Users can disable the mitigation by editing the kernel boot parameters.
Given that there’s an inherent conflict between usability and security (whether in the computer space or not), I think that everyone has to decide for themselves the level of security that they’re comfortable with. I don’t think there’s a right or wrong answer here — it’s a very personal decision.
However, I also think it should be an informed decision. You should know the ramifications of your decisions.
For instance, this: “might only happen to you if someone actually targets you.” is incorrect. These vulnerabilities will be used in targeted attacks, of course, but they will be used to an even greater degree in a scattershot manner. If you’re interested in obtaining things like CC numbers, your best strategy is to attack as many systems as you can.
Personally, when it comes to Spectre-class attacks, I’m not losing a lot of sleep over patching them up, mostly because these are going to keep coming on a regular basis until the CPUs are physically replaced with ones that don’t have such a vulnerability. All of the patches for these things only address specific methods of attack after they’ve been discovered, but there are a very large number of possible methods of attack remaining.
Also, you can beef up your other defenses to mitigate your exposure to Spectre-class attacks. Mostly, this consists of doing what you should be doing anyway — be extremely cautious about what programs you run, and don’t allow Javascript (or other code served to you from a server) to execute unless you’re *very* sure that it’s OK.
Even just blocking Javascript connected with advertising and avoiding going to sketchy websites can get you pretty far.
@ John Fenderson
Coming new CPUs, eg the 9th-gen Intel Cannon Lake or 10th-gen processors, will likely have all the mitigations and performance-hits for Meltdown & Spectre built-in.
Ubuntu 18.04 already has all the mitigation and performance-hits for Meltdown & Spectre(v1 and v2) built-in. Similarly for Win 10 Version 1803.
The issue is that until the CPU is redesigned, there is no blanket mitigation that can be applied. This is an arms race, as each specific attack that leverages the CPU problem is created, a mitigation is created to stop it. But another, different attack (leveraging the same issue) will be created that the mitigation doesn’t stop.
Rinse and repeat. This is a hardware problem that can’t be resolved with software in a comprehensive way.
On the upside, attackers have to run code on your machine to perform the attack, so being extremely cautious about what code gets executed is an effective defense across the board.
The Intel report states…
The following Intel-based platforms are POTENTIALLY impacted… (emphasis mine)
And Martin notes…
Intel is not (a)ware of exploits in the wild.
Why take medicine for an illness that doesn’t exist?
For the same reason you inoculation against Polio and the measles.