Facebook Phishing Scam In The Wild
If you have created a popular Internet service you know that it is not always a blessing and that a lot of hard work is usually involved in the maintenance of said service.
This becomes apparent especially when you have to deal with security related issues like phishing attacks. Facebook is without doubt one of the most popular sites on the Internet these days, and it therefore comes as no surprise that the service is regularly attacked.
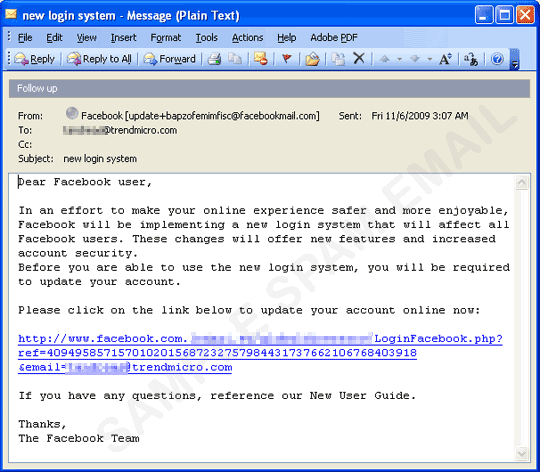
Trend Micro reports about yet another Facebook phishing attack that is currently in the wild. The attack begins - like most phishing attacks - by mass mailing potential Facebook users informing them that they need to update their Facebook login credentials.
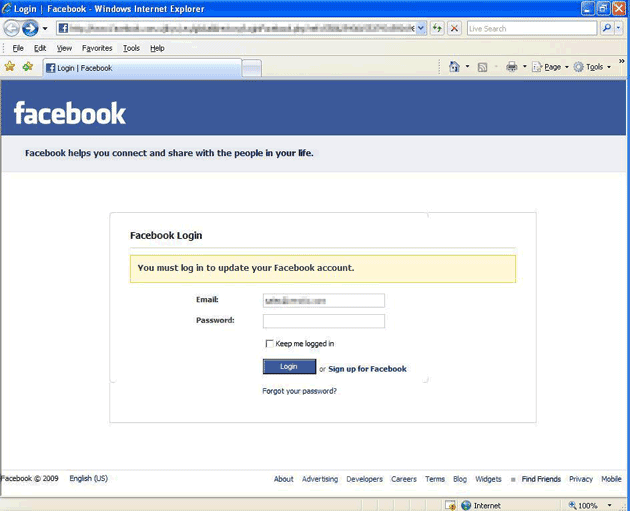
A link is provided in that email, and if a user clicks on the link, a website is loaded that looks exactly like Facebook does. While it resembles the Facebook website visually, it is a fake site.
What's interesting here is that the email address field of the login form is already filled out so that Facebook users only need to enter the Facebook password to complete the process.
Since the attack is carried out by email, the attackers have the email address of users already, and use it on the site to improve user confidence that they are on the right site. If you look closely at the link in the email, you will notice that it is part of the address that is loaded.
A click on the login button will open a new page that lists a link to an update tool which installs a trojan on the user's system.
It attempts to access a Web site to download a file which contains information where the Trojan can download an updated copy of itself, and where to send its stolen data. This configuration file also contains a list of targeted bank-related Web sites from which it steals information. Note that the contents of the file, hence the list of Web sites to monitor, may change any time.
It attempts to steal sensitive online banking information, such as user names and passwords. This routine risks the exposure of the user’s account information, which may then lead to the unauthorized use of the stolen data.
It is interesting to note that the attack's main purpose is not to steal Facebook authentication information, but to plant the trojan on the user's system instead.
The blog post offers security tips on how to distinguish legit from phishing emails. Users who are interested in those can visit the blog post; the most important lesson once again is however to avoid clicking on email links especially when you are in doubt.






















someone is always using my Facebook account I don’t know what to do
I got this phishing from the gmail account too. :(