QBot malware exploits Windows WordPad EXE to take over
The QBot malware has recently been observed using a sophisticated technique to infect computers by taking advantage of a DLL hijacking vulnerability in the widely used Windows 10 WordPad program. By leveraging this flaw, the malware can evade detection from security software, making it a significant concern for users and organizations alike.
This article delves into the intricacies of DLL hijacking and the specific methods employed by QBot, shedding light on the potential risks and impact of this malware.
What is DLL hijacking?
DLLs, or dynamic-link libraries, are essential files containing functions that multiple programs can utilize simultaneously. When an application is launched, it searches for the required DLLs in designated Windows folders and loads them accordingly.
Notably, DLLs located in the same folder as the executable are given priority and loaded before others. This hierarchy provides an opportunity for malicious actors to exploit DLL hijacking vulnerabilities.
QBot exploitation of WordPad DLL hijacking
QBot, initially recognized as a banking trojan but later evolving into a versatile malware dropper, has established partnerships with ransomware groups like Black Basta, Egregor, and Prolock. Together, they target corporate networks for extortion attacks.
According to ProxyLife, a Cryptolaemus member and security researcher, QBot malware has recently launched a phishing campaign utilizing a DLL hijacking vulnerability within the Windows 10 WordPad executable, write.exe.
A malicious chain of events
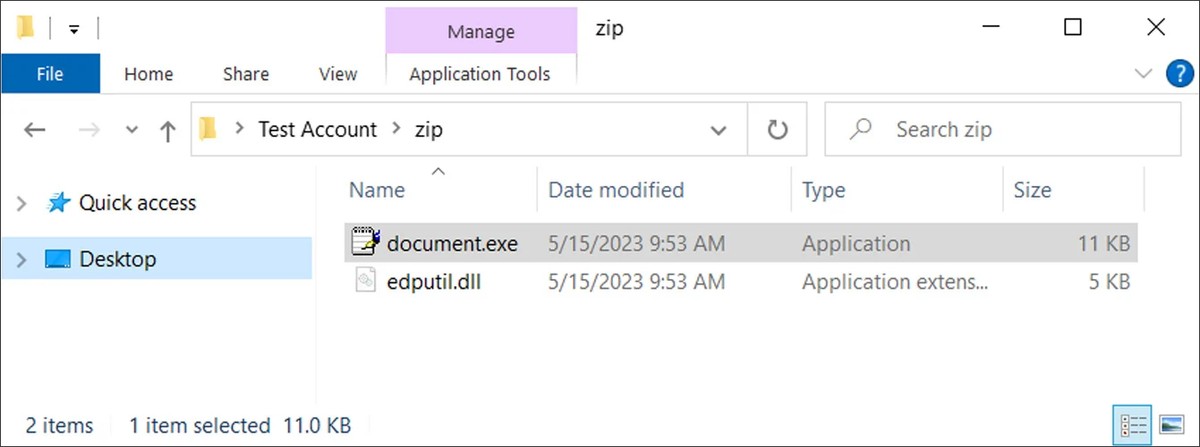
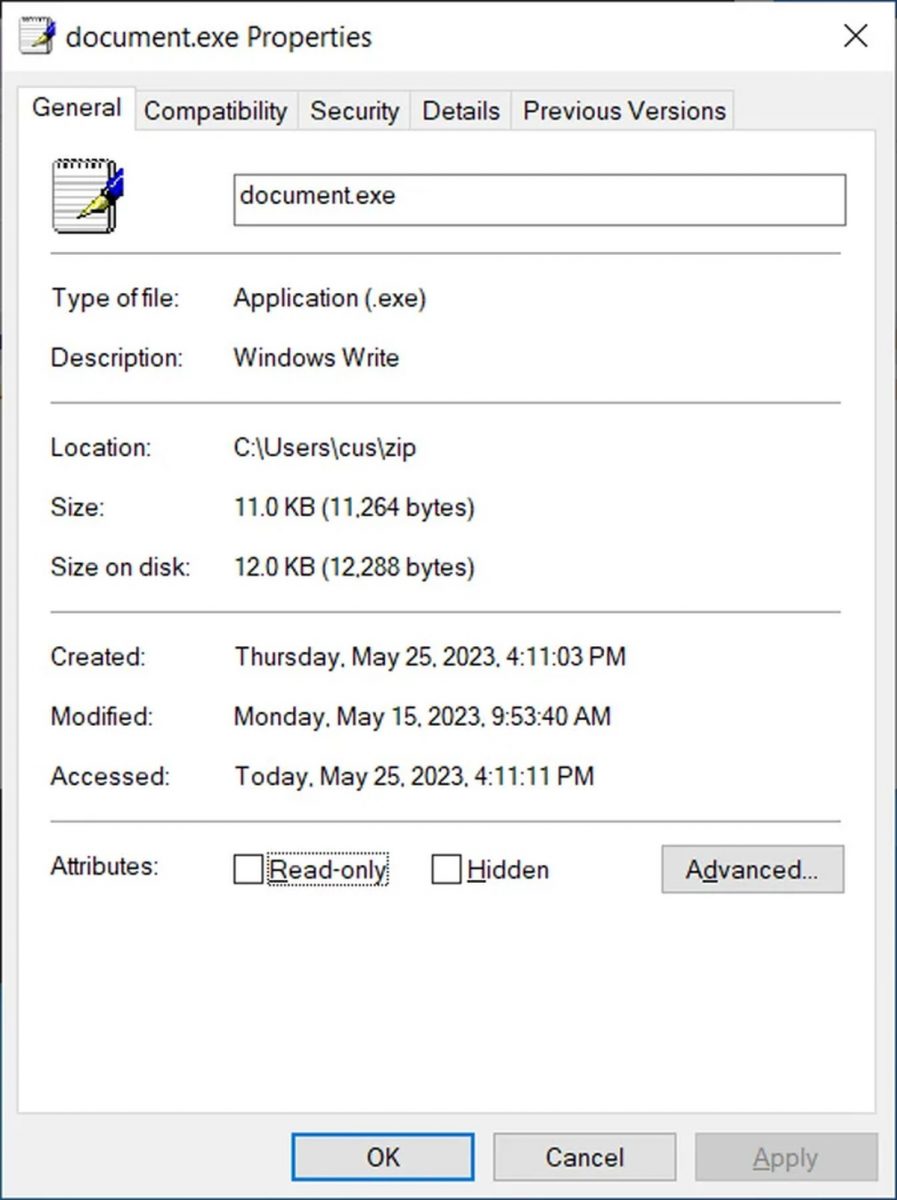
When a user clicks on a download link contained in the phishing emails, a ZIP archive is fetched from a remote host. Inside the archive, two critical components are present: document.exe (disguised as the Windows 10 WordPad executable) and a DLL file named edputil.dll, which enables DLL hijacking. Further investigation reveals that document.exe is, in fact, a renamed copy of the legitimate Write.exe executable used to launch the Windows 10 WordPad document editor.
Upon execution, document.exe attempts to load the genuine DLL file, edputil.dll, usually found in the C:\Windows\System32 folder. However, instead of strictly checking for the DLL in that specific location, document.exe prioritizes loading any DLL with the same name found in its own folder.
Seizing this opportunity, threat actors create a malicious version of edputil.dll and place it in the same folder as document.exe, ensuring that the malware is loaded instead.
Exploiting the loaded DLL
Once the malicious DLL is loaded, the QBot malware proceeds to use C:\Windows\system32\curl.exe to secretly download a DLL file disguised as a PNG image from a remote host. This deceptive file, when executed through rundll32.exe, unleashes the true capabilities of the malware.
QBot now operates silently in the background, stealing emails for future phishing attacks and downloading additional payloads such as Cobalt Strike, a popular toolkit used by threat actors to gain initial access to compromised devices. By infiltrating trusted programs like Windows WordPad, QBot manages to evade detection and carry out its malicious activities.
Advertisement



















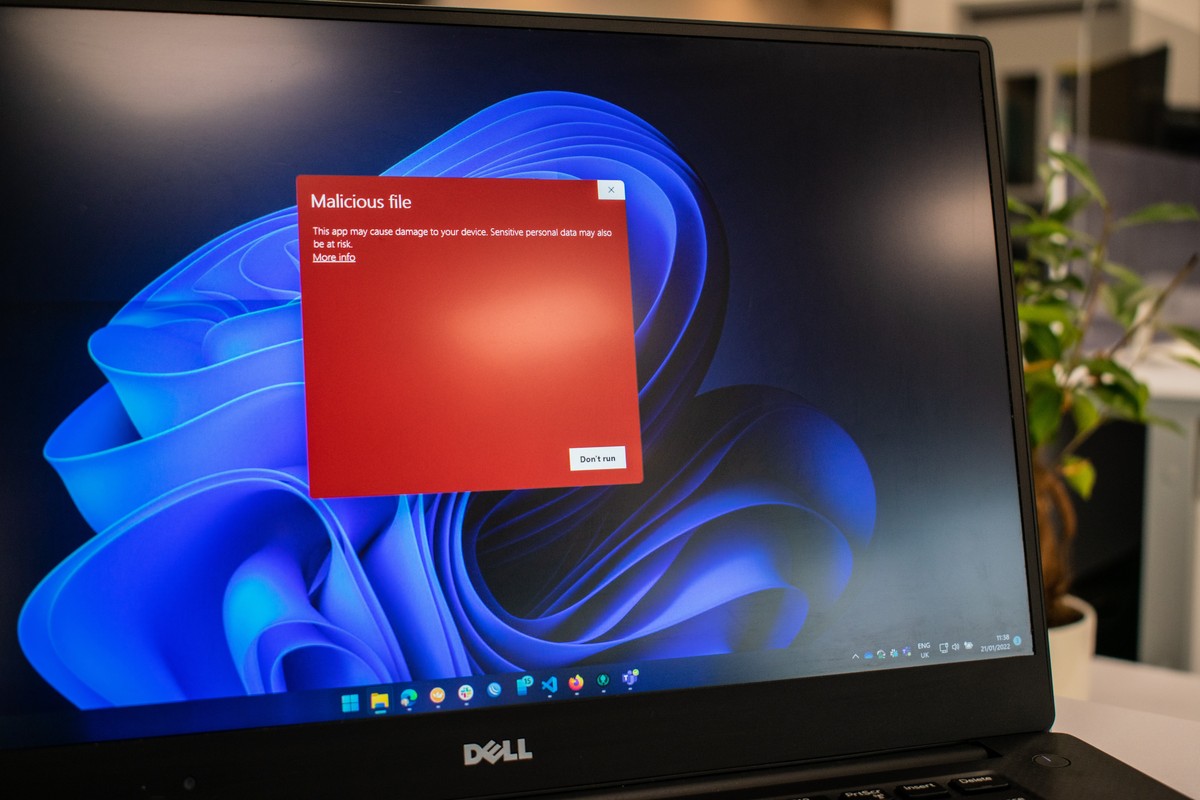
I wonder if Defender will block this malware as good as it appears in the photo above.