Aegis Authenticator: open source Google Authenticator and Authy alternative
Aegis Authenticator is an open source application for Google Android devices to generate and manage two-step verification tokens for online services. The app has an import option, extra security options and several nice to have features that make it worth a closer look.
Many Internet services support two-factor authentication by now. It is an optional security feature in most cases, which adds a second layer of protection to account sign-ins. Sites still require username and passwords, but also a code to complete the login process.
Authenticator apps like Aegis Authenticator, or popular options such as Google Authenticator, Authy or Microsoft Authenticator, may generate these codes on mobile devices. These apps offer better security than email or SMS-based options.
Twitter announced recently that it will disable the SMS-based method for its free users, and users may use the opportunity to switch the method to Authenticator Apps.
Aegis Authenticator
Aegis Authenticator, like any other authenticator app, needs to meet certain security standards. The developers note that the vault is encrypted with AES-256-GCM and that it supports the industry-wide standards HOTP and TOTP. It is compatible with Google Authenticator, which means that its data can be exported for Google Authenticator.
What sets it apart from most popular choices is that it is fully open source. The developers have added password and biometric protections to the app on top of that, which means that access to the database is locked until the password is entered.
New services may be added in a number of ways. Besides the option to scan QR codes on websites directly, Aegis Authenticator supports entering details manually and importing them from other authenticator apps on the device. The last option may require root access, however, which most Android users may not have on their devices.
Imports from a good dozen major authenticator apps are supported. The list includes Authy, FreeOTP, Google Authenticator, Microsoft Authenticator, Steam and even plan text imports.
Aegis Authenticator supports extra features, such as groups, auto lock functionality, or panic trigger support using Ripple.
Aegis Authenticator Download
Aegis Authenticator is available on GitHub, on the free marketplace Fdroid, and on Google Play. Installation is straightforward from all three locations and should not pose any issues for Android users.
Use of the authenticator app
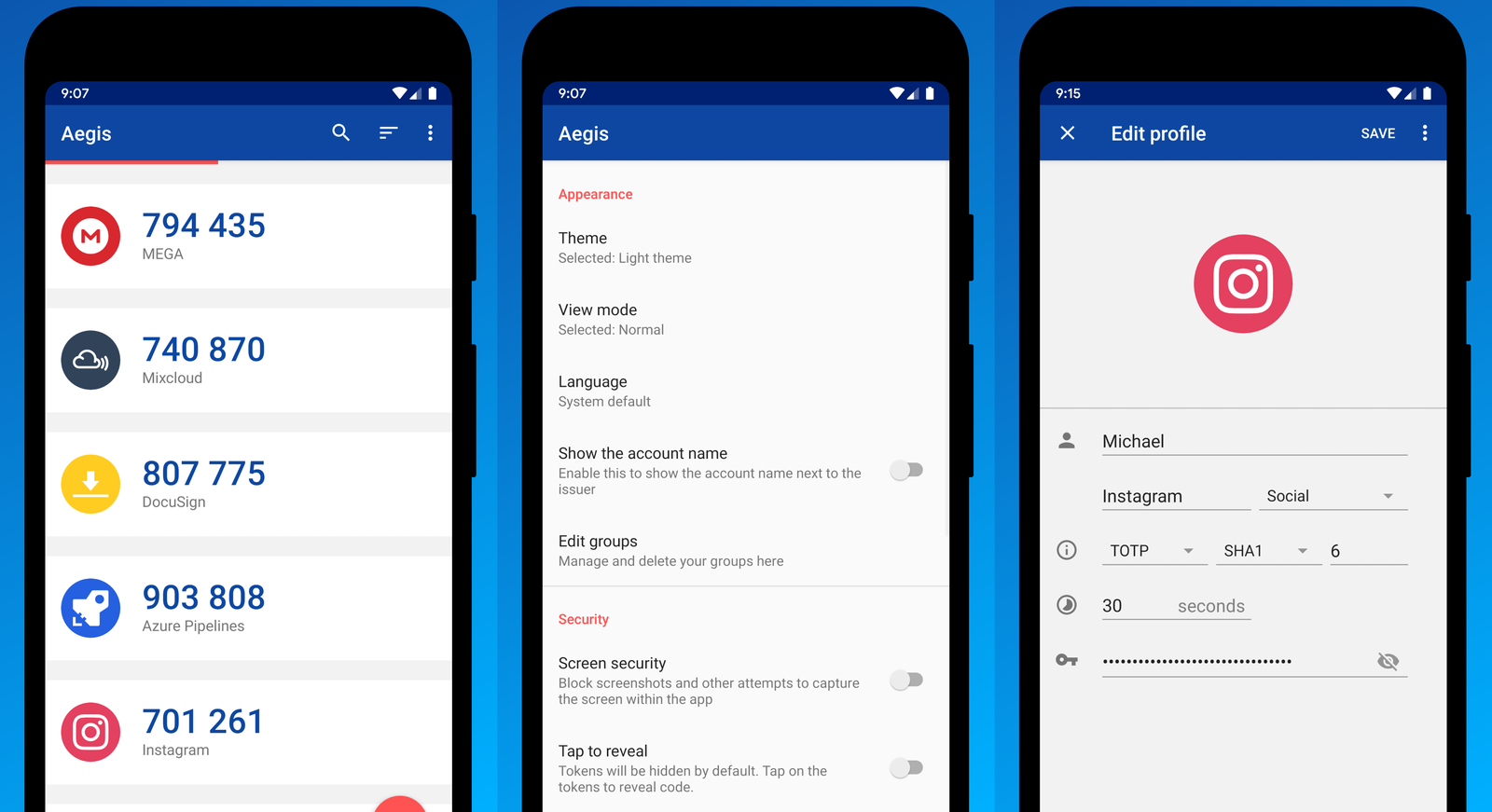
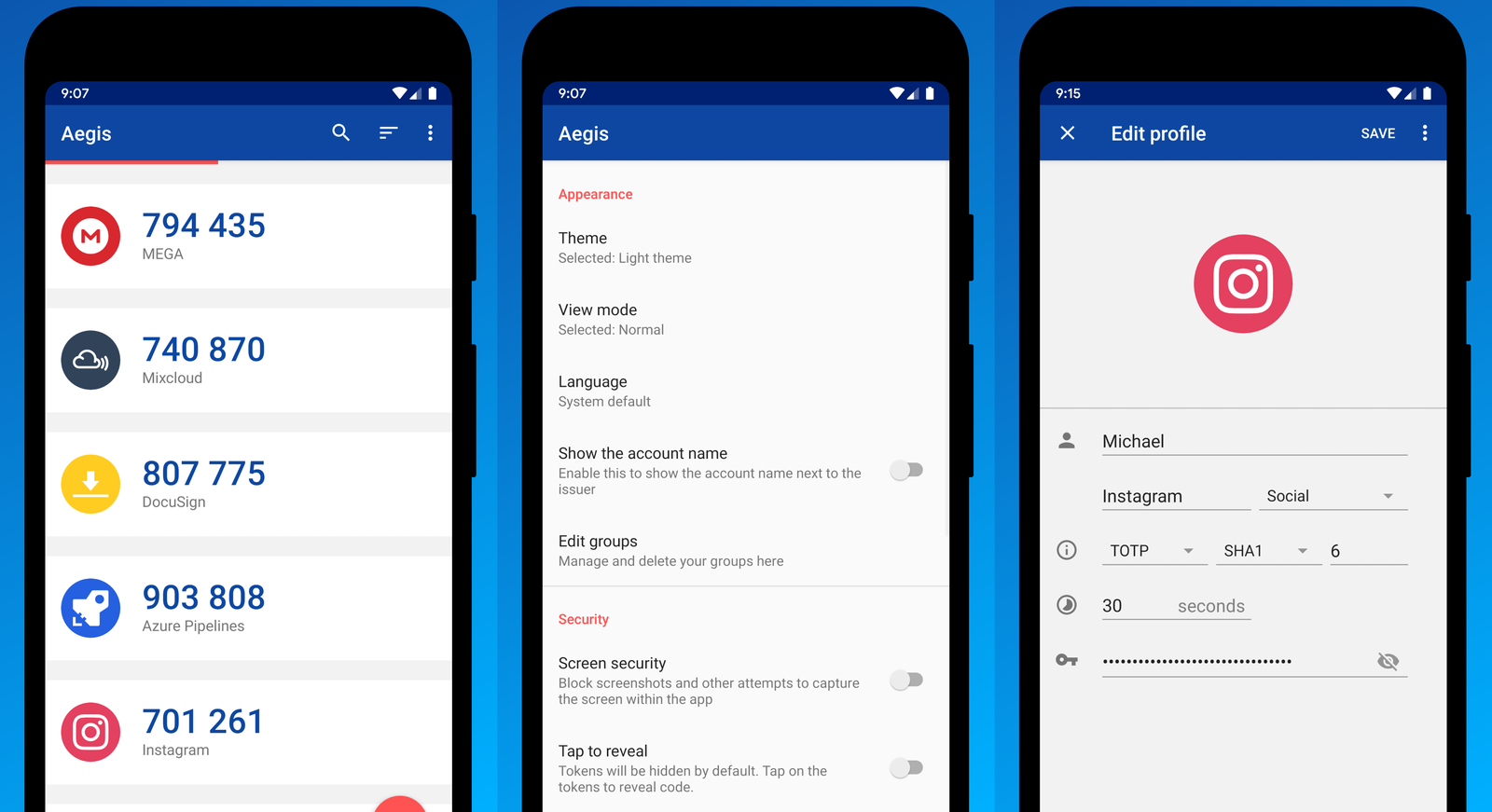
A password needs to be set up on first start of the app to protect the contents from prying eyes. The app displays all services on its frontpage .
First time users may want to open the Settings on first run to adjust some of them. There, they may change appearance, security and usability features. Some of the options found there include copying tokens with a tap, minimize the app on copy, or enable the automatic backups feature of the app.
Aegis Authenticator does not sync data to the cloud by default. There is an option under backup to enable Android cloud backups.
Migration from one authenticator app to another can be a time-consuming process, if direct imports are not available on the device. It usually involves disabling two-factor authentication at the service's website and setting it up again.
Adding new services to the app is a quick process. It does require scanning the QR code that sites and services display when two-factor authentication is set up.
Verdict
Aegis Authenticator is a well-designed app that is easy to use. Its import functionality makes it stand out, but it may require root depending on the authenticator that data needs to be imported from. Password protection, its open source nature, and several other security features make it stand out from the masses of other apps that serve similar purposes.
Now You: which two-factor authentication app do you use, and why?

























I use the good ol’ FreeOTP, also open source (Red Hat) and available on F-Droid.
@thanks
This is the kind of comment we did not come for!
I look forward to reading your awesome posts
@thanks
I am sure your articles would be much more interesting. I look forward to reading them!!!
I use Aegis. Thanks for the article.
Great article!
This is the kind of stuff we come for! I don’t know what’s been happening to this site lately with so much crap being posted by new people.
I use Raivo, same concept, open source.
I like FreeOTP+ from F-Droid.
I have tried to use Aegis Authenticator twice but I am not able to import the data from Google Authenticator. There is a message that says Google is encrypting the data and it is not retrievable without risking errors.
The fact that its on fdroid makes it trustworthy in my eyes. I don’t trust anything from github on a phone unless its from a big company like Brave or Mozilla. And I definitely don’t trust anything from the Google Malware Store.
Your comment shows that you have no real idea about what is trust worthy and what isn’t.
The Github link “should” be the source code for the app you got from fdroid.
Should because who’s to say the fdroid release wasn’t modified by whoever packaged it.
By using the actual Github source you could audit the code and package it yourself if you wanted to trust the code explicitly.
Also fdroid is no more “safe” than any other app store.
I would argue that the Google store is safer than fdroid actually in terms of the way they continually scan packages in their repositories.
fdroid allows anything to be published. Why do you think all the packages refused by Google because of safety issues end up on fdroid.
I’m using Yubico Auth ’cause I use their keys.
I’ve been using Yubikeys for a decade and I never heard that they released an MFA app. Thanks for sharing!