Microsoft disables VBScript by default
Microsoft announced plans in 2017 to disable VBScript in Internet Explorer 11; the company deprecated the feature but kept it alive for certain environments back then to give organizations enough time to migrate resources that use VBScript to other technologies.
VBScript, which was introduced by Microsoft more than two decades ago, is an active scripting language that is modeled on Visual Basic.
It came to some fame in 2000 when a computer worm known as the I Love You or Love Letter Virus, used it to infect systems. Users would get emails with the subject linke ILOVEYOU and an attachment LOVE-LETTER-FOR-YOU.txt.vbs. Users who opened the attachment would infect their machines with the worm.
One of the problems back then was that Windows hid the actual extension of the attachment so that many Windows users believed that it was a harmless text file.
Infected PCs would send emails using the contacts list to spread to other machines. It would furthermore configure Windows to launch itself on start of the system and modify data in computer files.
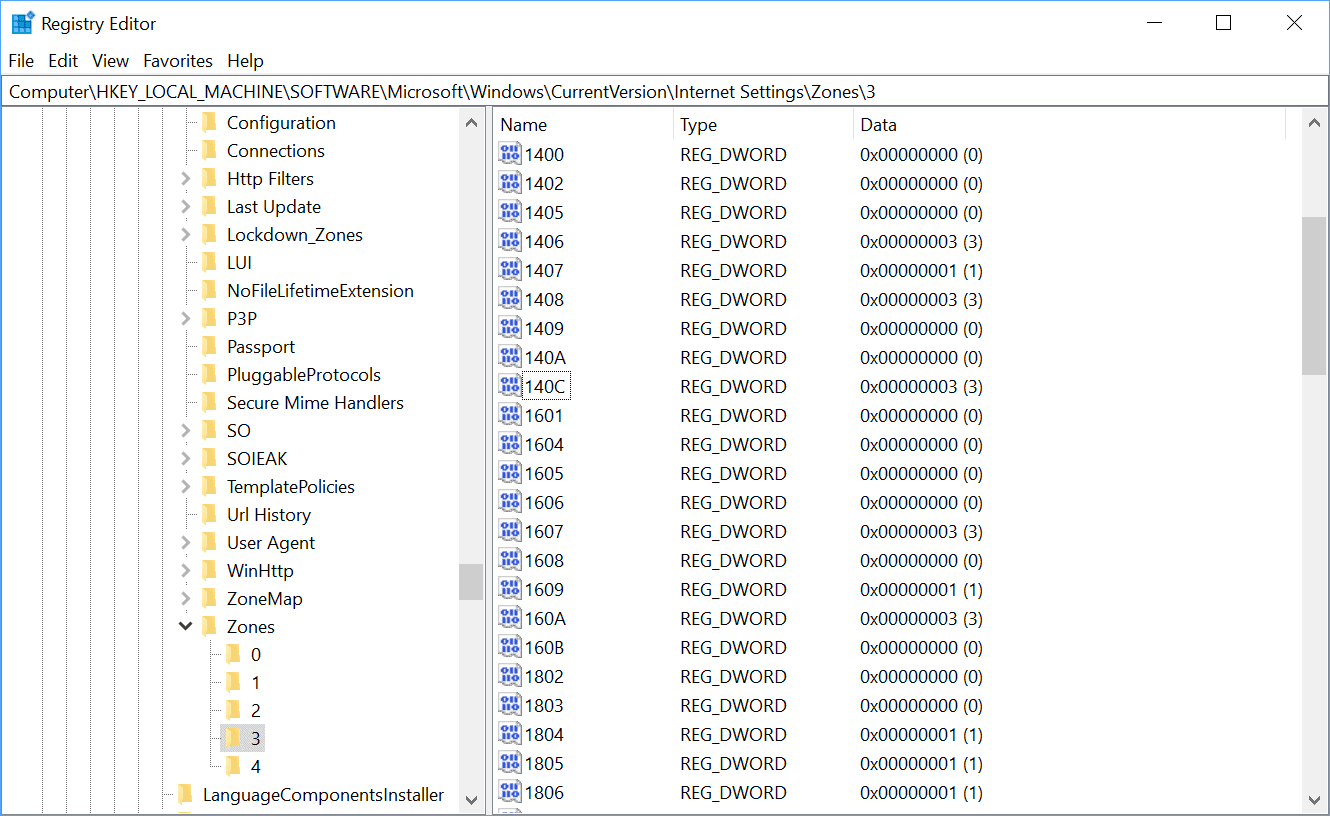
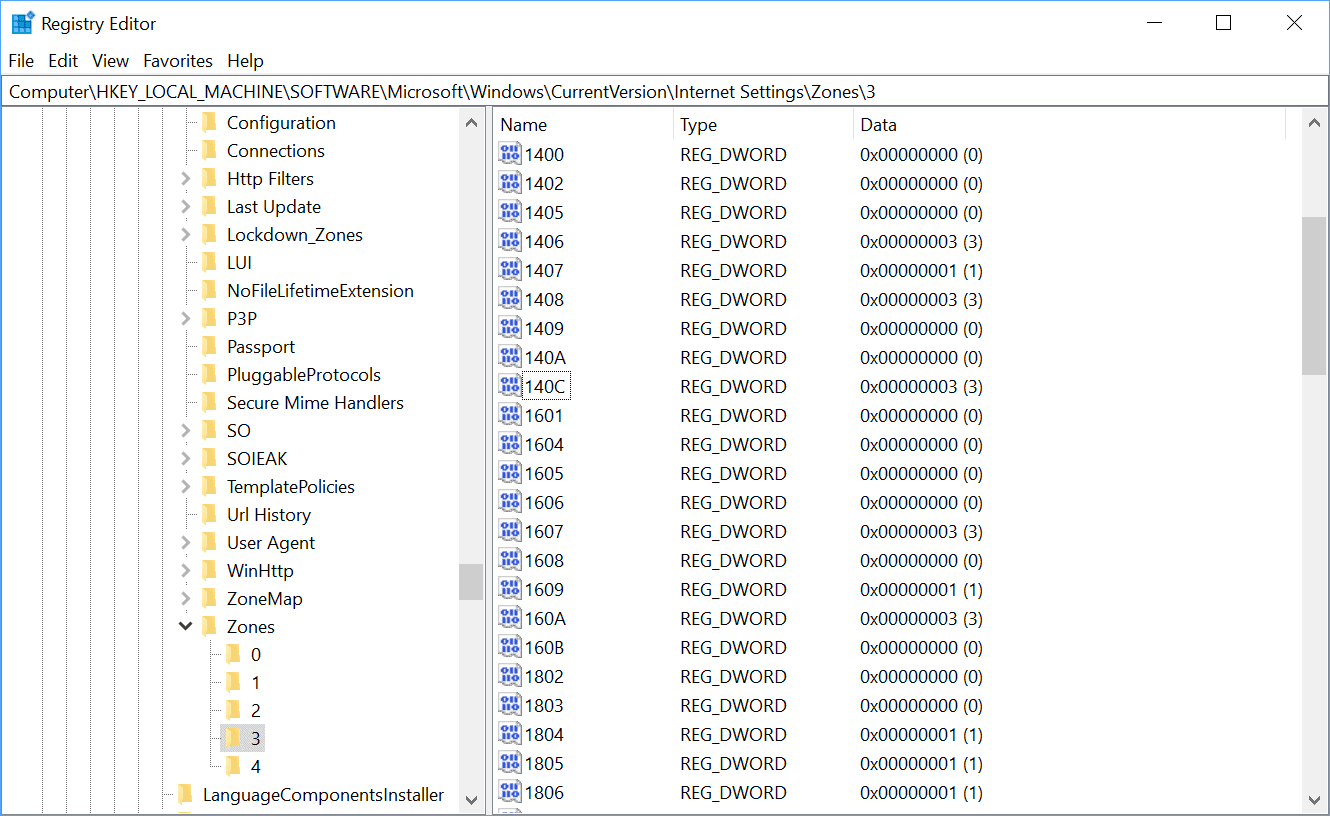
Microsoft recommended that Microsoft Internet Explorer users disable VBScript in the browser for the Internet Zone and Restricted Sizes Zone to protect the browser against attacks targeting VBScript.
Administrators and users had to disable VBScript in Internet Explorer manually at the time.
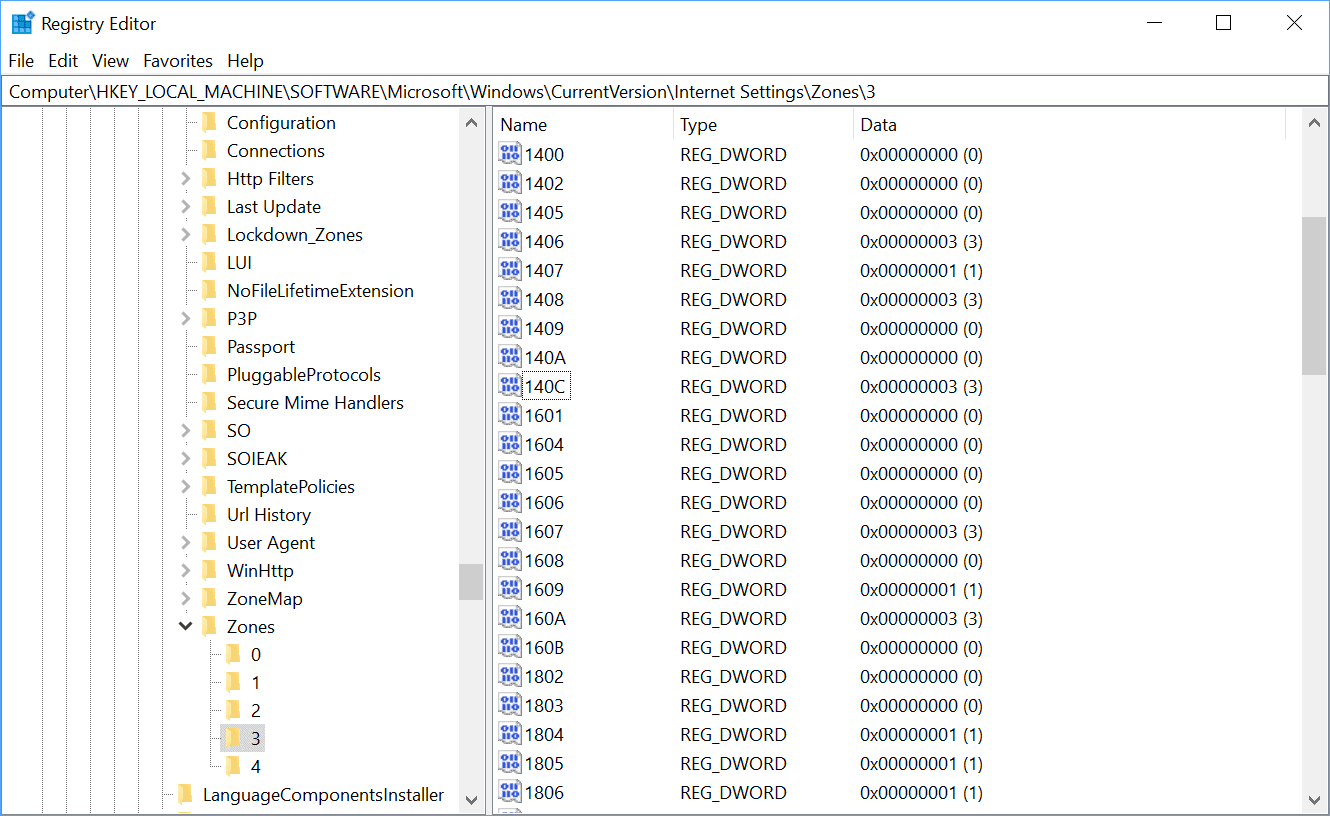
The July 2019 cumulative updates for Windows 10 disabled VBScript by default on machines running Windows 10. The coming August 2019 cumulative updates for Windows 7 Service Pack 1, Windows 8, and Windows 8.1, will do the same on these machines.
VBScript will be disabled by default for Internet Explorer 11 and WebOCs for Internet and Untrusted zones on all platforms running Internet Explorer 11.
VBScript won't be removed at this time though. Microsoft notes that it is still possible to enable it on machines if the legacy technology is still needed.
The settings to enable or disable for VBScript execution in Internet Explorer 11 will remain configurable per site security zone, via Registry, or via Group Policy, should you still need to utilize this legacy scripting language.
A support article on the Microsoft Support website provides details on the available options. In short: administrators may turn on VBScript using the Registry, Group Policy (Enterprise only), or site security zone.
Closing Words
The disabling of VBScript is a long overdue step on the Home system and user side; organizations can still allow it on certain systems if legacy scripts are still used.
Now You: when was the last time you encountered a VBScript?














I am 82 years old and my enjoyment is making stationery in Pain Shop and now with this last update I only get the Backgrounds showing I am not at all technically comprehensive so I need help from you to be able to enjoy my stationery.
For any machine that has access to the inet, the best security policy is to use your tool of choice to completely disallow execution rights of these 3 items.
C:\Windows\System32\cscript.exe
C:\Windows\System32\wscript.exe
C:\Windows\System32\WindowsPowerShell\*.*
If any are ever needed, allow execution to complete your task, then when done, set it back to disallow execution. btw, that’s disallow the entire WindowsPowerShell dir. This tip may never be needed. But, it is downright dangerous to have that tech avail on an inet capable machine.
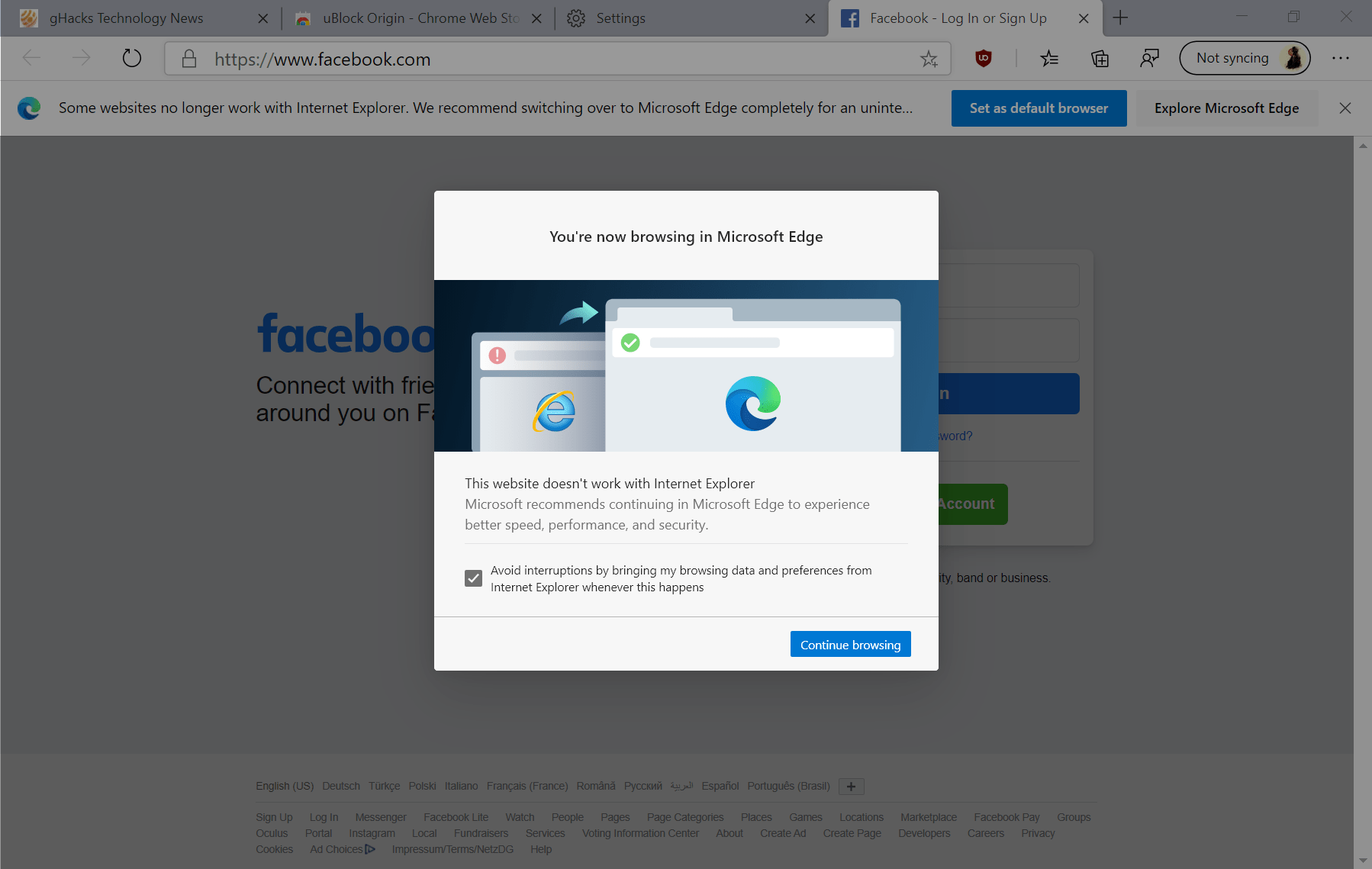
PS: About time MS, 20+ years of vbscript to run in a browser, sheeesh. And while we are at it, IE mode will be allowed in MS Edge… what could go wrong? If a tool is so powerful, that it can update the kernel and OS, you don’t want that tool to be used for internet browsing.
Running Win-7 PRO 64-bit.
I have written several, VBScripts over the years to manipulate bits and pieces in the registry.
In particular to loop thru a list of MRUs (file full names) and remove MRU items that no longer exist.
I hope I am not going to lose VBscript.
I no longer update Win-7, more trouble than its worth.
Where I might fall over if the Win-7 “rollups” tamper with clean installs on Win-7
( I MUST download a recent rollup and hide it under the mattress)
For those of you who don’t want to wait for the August update, M$ has instructions to disable it in the Registry: https://support.microsoft.com/en-us/help/4012494/option-to-disable-vbscript-execution-in-internet-explorer-for-internet
Would be crap.
Years ago I had to make a batch script and include that into a procedure, completely managed by batch scripts (the owners of that system really insisted on that), which generates a vbs script on the fly, executes it and then deletes the vbs script.
Nothing extensive, but it does make automatization a lot more convenient.
At first I thought this was referring to disabling VBS execution on the operating system, not just the browser. Makes sense from the IE standpoint, but not from an OS standpoint; VBS is still useful for scripting some things out in Windows without installing any external software.
Hot take: What if the web evolved to use VBScript instead of JavaScript?
File extensions like .vbs .mht .js and so forth should not only be disabled in IE. Force Windows 7/10 to execute them with Notepad only.
Good ol’ trick that gets the job done system wide.