Control Tracking with Baycloud Bouncer
Baycloud Bouncer is a web browser extension for Firefox, Chrome, and Edge, that give you full control over online tracking.
Online tracking, through the use of browser cookies or otherwise, is so common in this day and age that you are hard pressed at finding advertising services or popular sites that don't track users in one way or another.
Do Not Track was designed with good intentions. It is a value that is transferred with header information when programs connect to sites. If set, it tells the site that the user does not want to be tracked. Most modern browsers support Do Not Track. Google introduced Do Not Track in 2012 in Chrome, and Mozilla in 2011 in the Firefox browser.
For this to work however, sites need to support Do Not Track technically, and also support what it is supposed to do.
Mozilla revealed results of a study back in 2013 that showed that no more than 20% of users sent Do Not Track headers with their requests.
Baycloud Bouncer
Baycloud Bouncer is a WebExtension for various web browsers that implements the Do Not Track Consent API. Essentially, what that does is block tracking through the use of cookies unless consent has been given by the user.
This goes one step further than asking sites not to track, as it will block tracking unless allowed by the user of the browser.
Servers may use the API to prompt for permission, and if permission is granted, persistent cookies or other techniques may be used to track the user.
Baycloud Bouncer acts as a bouncer that controls this. It blocks any site from trying to set persistent cookies or use other means of tracking if explicit user consent has not been given.
Any embedded content, that means third-party content such as ads that are displayed on a site, are only given site-specific consent according to the description of the add-on.
Additionally, Bouncer will also enforce the Do Not Track signal and not only communicate it to the sites the browser connects to. This means that persistent cookies will only be allowed for a maximum of 2 hours if set.
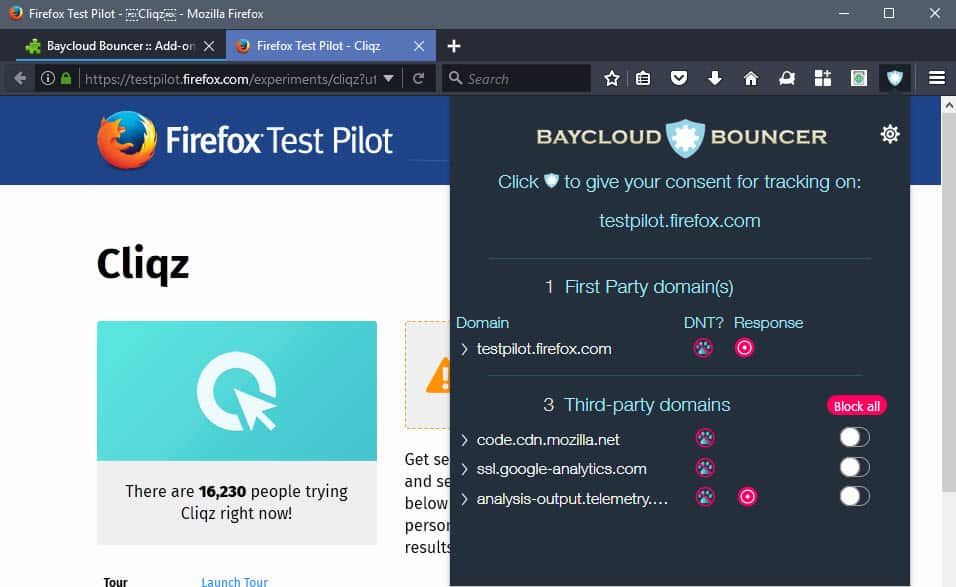
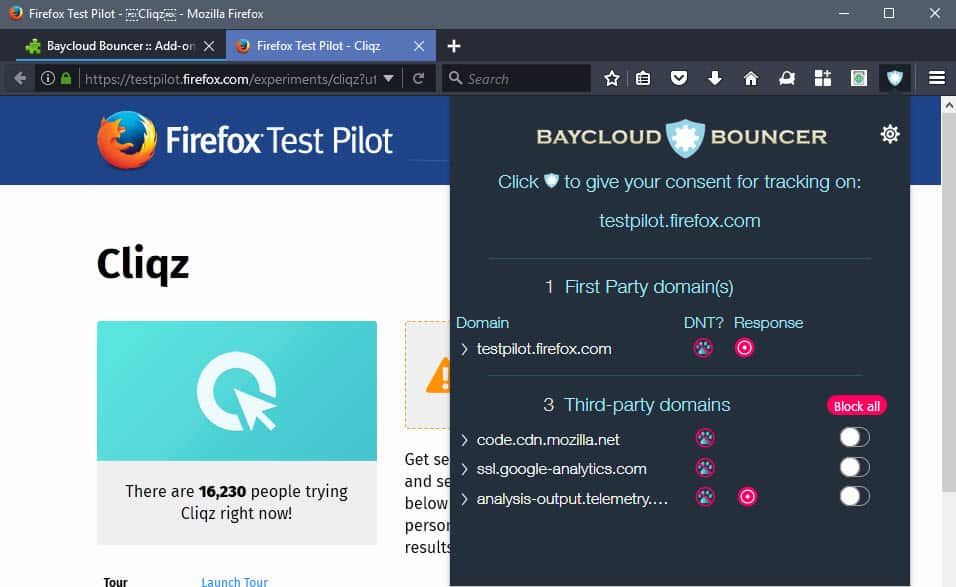
The application adds an icon the browser's main toolbar that you may click on to manage the behavior. The interface lists all first and third party domains connections have been made to, whether Do Not Track is supported, what a site's response was, and options to block specific sites directly.
You can allow a site to track you with a click in the interface, and revoke the permission as well again at a later point in time.
Options
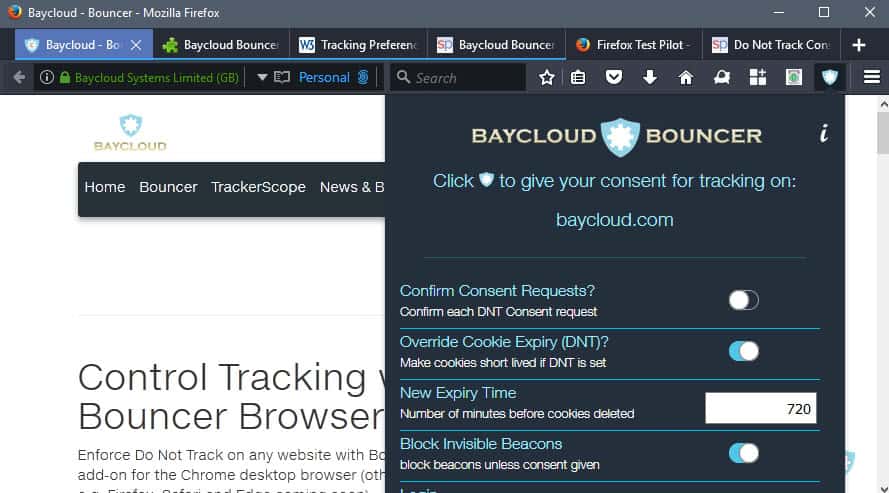
Baycloud Bouncer ships with a bunch of preferences and options to configure the extension's blocking of tracking further.
Here is a short overview of the supported options:
- Confirm Consent Requests -- Whether to confirm any consent request.
- Override Cookie Expiry -- If Do Not Track is set, let cookies expire after 720 minutes (change the time period).
- Block Invisible Beacons -- If no consent is given, block beacons that are not visible.
- Block if Pings are Detected -- Block if pinging is detected.
- Don't send 3rd party cookies -- Block third party cookies if Do Not Track is set.
- Changing Do Not Track also changes 3rd Parties -- If you whitelist sites, whitelist also applies to third parties.
- Notify Fingerprinting -- If Fingerprinting is detected, notify the user.
- Notify 1st party Fingerprinting -- Notify if first party fingerprinting is detected.
- Replace Path in Referer Header -- Whether to hide the referring site in the header.
BayCloud Bouncer can be downloaded for Mozilla Firefox from Mozilla AMO, and for Google Chrome for the Chrome Web Store.
Verdict
Baycloud Bouncer offers better protection against tracking than the Do Not Track header. Its extra features, besides that, and the flexibility it provides in regards to tracking, may make it attractive to some Internet users.
Even users who have disabled third-party cookies may find it useful, as it may help when it comes to first-party tracking, and other tracking methods as well.
Now You: How do you handle tracking on the Internet?
























I don’t have the technical expertise a lot of you have, but I have been using BLUR for several years. It says that it is blocking tracking by a number of sites, but I really don’t know. I wonder if any of you guys have tried BLUR and would mind giving me your opinion as to if it is effective or not? Even if it isn’t that effective, it does provide masked emails which by themselves seems to provide at least some degree of separation or at least the ability to protect your email address.
apart from the above mentioned check out the settings of FF itself one by one. It will teach you a lot
There is unfortunately not much you can do about fingerprinting as a tracking technique. It is completely passive, happens on the server, and is nearly impossible to detect or block in the browser. It makes extensions like this almost pointless, IMHO.
FP’ing is not completely passive. Sure, there is server-side FP’ing, but there are dozens, maybe hundreds, of elements that can be controlled client-side. And some server-side techniques can be mitigated, such as SSL session id tickets, or HTTP2 opportunities.
The problem with FP’ing is entropy, and in order to lower entropy (client-side), you have to buy into the same settings in sufficiently large numbers within the same sub-set – such as TBB. – eg claiming to be anything but Firefox is useless due to very simple feature detection, but claiming to always be the latest ESR, narrows the choices. That said, there are now so many elements to a full FP, that gaining a high enough entropy is becoming relatively easy, even if all the low hanging fruit is picked off. Take for example Panopticlick v1 with its screen-res/inner window/browser-dimensions, time zone, and UA string – 2 of these three are stlll not fully covered by Firefox internally, and that’s after 5 godamn years.
The way to defeat FP’ing is thru reducing the attack surface as much as possible – eg default deny-all JS/XSS etc. Then to harden the attack surface (block, spoof), and lastly, thru OpSec (multiple profiles, bowsers, VM’s etc). I am only talking about FP’ing, not about tracking and IP numbers etc.
Does anybody (including Martin) have a short list of must-have, set-it-and-forget-it ad/privacy extensions?
I used to use AdBlockPlus, Ghostery. Now I switched to UBlockOrigin, Disconnect with clear History when FF closes except whitelisted domain cookies.
* Does UBO catch everything or do I still need Ghostery even though they overlap?
* Does Baycloud Bouncer give added blanket protection or does it just give granular control over sites that respect the Do-Not-Track function? Do I need it if I already have Disconnect or is it overlap?
* What else do I need?
I guess what I’m really asking is for a list for the max amount of coverage with the least amount of overlap.
“A short list of must-have, set-it-and-forget-it ad/privacy extensions?”
Just my opinion of course, the only ‘must-have’ for me is uBlock. Ghostery, Disconnect and Baycloud Bouncer are fine to use but they are the definition of redundancy if your ad/content blocker is using the right(?) filters. Ghostery, Disconnect and Baycloud Bouncer are IMHO most useful if-when-after you whitelist a website in your ad/content blocker because All of your filters will then be disabled in the content blocker, otherwise I don’t see them doing much when used in conjunction with a content blocker.
For instance, using Baycloud along with uBlock I did not see a reduction of network requests in the developer tools. I’m not saying it doesn’t work, only that with the uBO filters that I use along with not allowing third-party cookies I was unable to see any change in the amount of network requests in Firefox Nightly. But… with the websites whitelisted in uBO there was an obvious reduction in network requests by Baycloud. On the two websites I tested I saw 10-15% less network requests using Baycloud vs not using anything. So, it works. IF you whitelist websites use Baycloud or something similar otherwise I wouldn’t worry about. I always also use a hosts file, that I removed for this test-drive, so it would be pointless for me to whitelist any websites. I use these ‘test-drives’ to learn what is worth recommending. As great as Ghostery can potentially work, I used it for most of a year, I wouldn’t recommend it to anyone I know because it’s a guaranteed call-back or three. Just saying. I use the default filters in uBO with the addition of ‘Fanboy’s Annoyance List’ the ‘Malvertising filter list by Disconnect’ and… ‘Youtube: Other Annoyances’. You would have to add a ridiculously large number of filter lists to uBO before it has a significant impact on cpu and memory usage, at least on my desktop or 7 year old Win7 laptop, so no need to worry about adding those lists.
uBO + a host file is it for me.
Not too worried about tracking by marketers, their ads never show up except server side ones which I can “paint over.” (cosmetic filters)
Government spying is another issue, guess there’s tor or onion router for that if it works as advertised.
Social media blocking a must IMO, more reports daily of people being stalked & killed, imprisoned, harassed by gov’t using that junk….not like the good old days when it was a novelty.
Your wondering is that of us all when concerned by security+privacy+efficiency. I guess each one of us has his recipes even if main ingredients may be shared. Privacy and security often overlap, i.e. adblocking when blocked ads contain malvertisement.
I see a computer’s defense this way and have for myself adopted the following components :
1- System-wide
– An anti-virus, anti-malware, “global defense” software : a plethora available, I use none (this is no advice).
– DNSCrypt : encrypted DNS requests + handling of address and domain blocklists (user’s choice)
– HostsMan : HOSTS file(s) manager (combines user’s choice of HOSTS files)
– Peerblock : address ranges blocker (user’s choice of blocklists)
– SpywareBlaster : protection application including Firefox dedicated cookies blacklist.
2- Browser-specific -> Firefox
2.1- about:config settings : Pants does a great job, best I know in this area : https://github.com/ghacksuserjs/ghacks-user.js
2.2- Add-ons
CanvasBlocker
CheckMyHTTPS
Clear Cache and Data
Decentraleyes
HTTPS Everywhere
Load from Cache
No Resource URI Leak
Pure URL
Redirect Bypasser
Self-Destructing Cookies
SSleuth
uBlock Origin
WebSocket Disabler
I cannot here detail these add-ons’ specifics, you’ll have to look them up on AMO
This is the basis of my defense architecture. I believe overlap is minimum.
The impact on privacy/security is the aim, the impact on speed is a sum of a gain when bad/useless connections are avoided with a loss due to the defense strategy’s delay. I believe there is more gain than loss.
Never forget that most of the above elements work better/require fine tuning.
Hope this can give you an idea. But again it’s every user’s choice, depends of him, his aims, his OS.
Good luck.
@Pants, hi there … > 0- Network-wide
I did mention DNSCrypt, included in the system-wide category. Isn’t the ‘Network’ category a sub-group of the System? OK, true that a computer can handle more than one OS if that is what you have in mind… and that I use but one OS, Windows VII :)
Tom .. before step 1 comes step zero
0- Network-wide
– eg Router – DNS, VPN, Privoxy etc etc
Network->OS->App
Sasuke, there is a lot that you can do against tracking, but at the bare minimum, consider blocking third-party cookies, and using a content blocker such as NoScript or uBlock Origin that support whitelisting.
TrackerScope, much like Visual Trace, tools always amaze me. All of the unintentional threads that one really visits when visiting one site.
When does it stop? The need for all of these privacy add-ons?
Needing to find an old friend from 40 years ago, it was possible, without Zaba or any tool like it, to find him in about five minutes by using a State Resident Database. I mean, the State he last lived in showed where he moved, and that State had all of his contact information, all of his contact information and current employment. Rather scary . . . the State or some other entity watches everything.
There certainly is far more privacy in Europe than in the States, country I love by the way because I’ve spent a wonderful childhood there. But Americans is one thing, the American administration, establishment and corporations is another. Liberty for all, so perhaps forbidding a whatever entity to violate an individual’s privacy would be a denial of freedom. I still prefer old Europe. I love American people but, frankly, I don’t envy their environment.
I’ve just installed/tried (more than thoroughly tested) this ‘Baycloud Bouncer’. I’m not convinced. But, as I say, no thorough testing.
– The site’s homepage is hosted by Microsoft. OK, why not?
– The add-on is heavy (5MB). OK, sometimes required. I haven’t opened the add-on to see what required so much occupation.
– The add-on proposes to register (free) and log-in to have extra features. Not fond of login required protection. What extra features.
– Overall impression is that of heaviness, but I must say I haven’t noticed an impact on pages’ rendering.
— I don’t understand accepting tracking is offered as a per-site option (off by default which means blocking is automatic) : why would a user accept a whatever tracking?
The add-on enforces the browser’s DNT feature. Here I followed pants’ advice when he mentioned that enabling DNT is useless because most — or no — sites don’t give a damn. Maybe enforced with ‘Baycloud Bouncer’ makes a difference yet it sets the user apart, as the whole add-on’s features does. I may be totally wrong but I prefer the scheme of asking/refusing nothing and have tracking blocked by uBlockO, cookies removed by ‘Self-Destructing Cookies’, just to name a few among my add-ons’ privacy arsenal ( about a dedicated dozen) all under tha authority of system wide protection (great handling a browser’s privacy but let’s not forget the OS because many connections don’t call the browser to be active!).
I’m not convinced, as such, first/fast approach. But it is very likely to be an interesting defense for a browser out of the box.
New version of Apple’s Safari to include build-in “Intelligent Tracking Prevention”
https://techcrunch.com/2017/06/05/apple-adds-a-tracker-blocker-to-desktop-safari/
@Martin: Do you think that it is better than Ghostery overall?