Microsoft releases out-of-band critical security patch MS14-068 today
Microsoft released fourteen security bulletins last week on this month's patch day. If you read the patch notes or our summary, you may have noticed that two bulletins were mentioned but not released on that day.
It is unclear why the two bulletins were listed by Microsoft but not released on the day. One explanation for this is that the company needed more time to create patches for affected systems.
The first of the two, MS14-068, will be released later today. To be precise, Microsoft will make the patch available via Windows Update on November 18, 2014 at around 10 a.m. PST.
The company published an advanced notification for the patch which does not reveal all the details yet.
What we know is the following:
- The bulletin ID is MS14-068.
- The bulletin has a severity rating of critical.
- The vulnerability impact is elevation of privilege.
- The security vulnerability affects only Windows Server systems and not client systems.
- Windows 10 Technical Preview and Windows 10 Server Technical Preview are affected.
If you check the affected operating systems, you will notice that all server systems are affected critically while client systems are not affected by it at all.
Client systems are listed on the page as well but Microsoft notes that the vulnerability addressed in the bulletin is not present in client systems.
The reason why they are listed on the page is that the update "provides additional defense-in-depth" hardening instead.
This means that the update will be made available for all client and server operating systems that Microsoft supports currently.
Microsoft plans to release an update to the company's own Windows Malicious Software Removal Tool as well. It is unclear right now if the update will be made available at the same time or at a later point in time.
This article will be updated with additional information once the full bulletin becomes available.
Update: Microsoft published the bulletin a moment ago.
MS14-068 - Vulnerability in Kerberos Could Allow Elevation of Privilege (3011780) - critical - Elevation of Privilege
This security update resolves a privately reported vulnerability in Microsoft Windows Kerberos KDC that could allow an attacker to elevate unprivileged domain user account privileges to those of the domain administrator account. An attacker could use these elevated privileges to compromise any computer in the domain, including domain controllers. An attacker must have valid domain credentials to exploit this vulnerability. The affected component is available remotely to users who have standard user accounts with domain credentials; this is not the case for users with local account credentials only. When this security bulletin was issued, Microsoft was aware of limited, targeted attacks that attempt to exploit this vulnerability.




















This update did slow my Windows 8.1 to a crawl.
System Restore did solve the issue removing
the update along with any harm it made.
I have since hidden the update.
My system is set to download updates
for manual install at my discretion
and having good luck so far
I wrongly installed this.
I suspect this update will get
reworked and then re-released.
Why are Windows 8.1 updates 10 times slower than Windows 7?
Anyone having problems with this security update? I have the dreaded msimg32.dll missing file message after reboot. I cannot open any third party applications.
BEWARE Update MS14-068 trashed my computer (HP ProBook 455 G1). After applying patch, computer hung on restart. Attempts to repair with Windows System Recovery Disc and HP Recovery Disc failed.
In the end, had to restore from a system image backup.
Speculation: the full disc encryption with HP security software is what caused the patch to be destructive (an error message contained the word “boot”). If Microsoft did not test the patch on such systems it is shameful.
How can I permanently block this patch from being notified to my machine? I’ve already changed the Update setting from “automatic” to “notify but do not install automatically”. But I’d like it to be permanently excluded so that I won’t accidentally click on “Yes, install” one day.
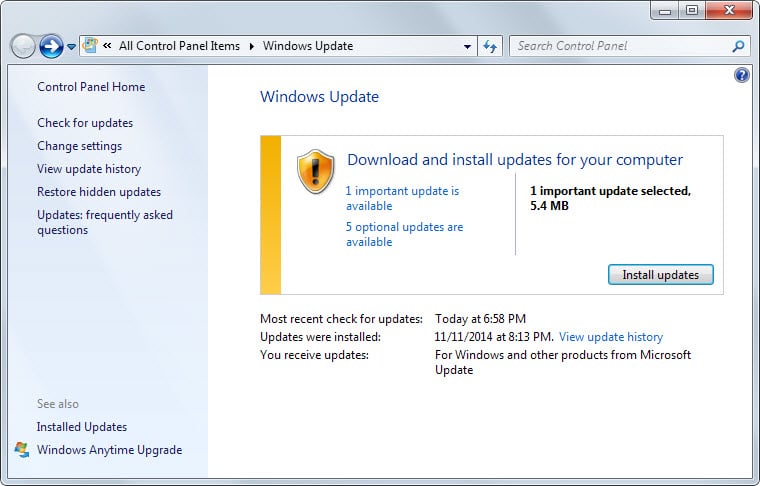
To permanently block an update, I think that you can open the Windows Update window from Control Panel and then right-click the update you no longer wish to receive notifications about and choose “Hide update.” If necessary confirm this if a UAC prompt opens, then click “OK” at the bottom of the Windows Update window. This works for me. Good luck!
724 MB update ….. I am always surprised that this kind of updates are shown under “Optional Updates”… Microsoft strongly recommends to install this update KB3000850. I wonder what ‘improved manageability’ does mean for the Windows user.
These constant “critical/important” Windows updates are quite annoying — are they really “all” that urgent for average Windows client users ?
{and Microsoft has buffooned several updates lately}
Some scattered web advice indicates many Windows updates are urgent only if you use Internet Explorer (IE), especially with javascript & Activex enabled; otherwise many (suddenly discovered) Windows vulnerabilities become less urgent issues (?)
Is there any website that explains these monthly Windows updates in plain (non-technical) language, expressing a clear, independent opinion of their actual “urgency” for various classes of Windows users ?
Hi Martin
Could you write something on KB3000850 please
This update rollup includes the following new features and improvements:
– Refreshed language packs
– Defence-in-depth security and Schannel hardening
– Support for newer hardware (boot order allowance, SD card improvements, USB debugging)
– Improved Web Services for Devices (WSD) printer support during network switches
– Performance and reliability improvements in clustered virtual machine mission-critical environments
– Improved manageability
– Additional hardware support (devices that have third-party disk encryption software enabled can now be upgraded to Windows 8.1 more easily)
Thanks ;)