Microsoft Security Bulletins For November 2014
Welcome to the November 2014 overview of Microsoft Security Bulletins and updates for all company products including client and server Windows operating systems as well as Microsoft Office.
It offers an in-depth analysis of all security and non-security updates that Microsoft has released since October 2014, the last official patch day.
Below you find an executive summary that lists the most important information about this month's patch day, a video summary by Microsoft, the operating system and other product distribution of vulnerabilities and their severity, links to security and non-security products, a deployment guide that suggests an order of deployment, and finally information about downloading and installing the updates on systems.
Executive Summary
- Microsoft released a total of 14 bulletins today that correct a total of 33 vulnerabilities and exposures
- All versions of Microsoft Windows, client and server, and other Microsoft products such as Internet Explorer or Microsoft Office are affected.
- Four of the 14 bulletins have received the highest severity rating of critical.
Video Summary
None yet.
Operating System Distribution
Windows RT is affected the least this month followed by Windows Vista and Windows 7 on the client side. The operating system with the highest accumulated severity rating is Windows 8 (and thus also Windows 8.1) which are affected by a total of nine bulletins of which four have been rated critical.
Windows Server 2012 and 2012 R2 are affected the most on the server side. Both server operating systems are affected by three critical, six important and two moderate bulletins.
- Windows Vista: 4 critical, 3 important, 2 moderate
- Windows 7:Â 4 critical, 3 important, 2 moderate
- Windows 8: 4 critical, 4 important, 1 moderate
- Windows 8.1: 4 critical, 4 important, 1 moderate
- Windows RT: 4 critical, 3 important, 1 moderate
- Windows RT 8.1:Â 4 critical, 3 important, 1 moderate
- Windows Server 2003: 3 critical, 3 important, 3 moderate
- Windows Server 2008: 3 critical, 5 important, 3 moderate
- Windows Server 2008 R2: 3 critical, 5 important, 3 moderate
- Windows Server 2012: 3 critical, 6 important, 2 moderate
- Windows Server 2012 R2: 3 critical, 6 important, 2 moderate
- Server Core installation: 3 critical, 4 important, 2 moderate
Other Microsoft Product Distribution
- Microsoft Office 2007: 1 important, 1 moderate
- Other Microsoft Office software: 1 important
- Microsoft SharePoint Server 2010: 1 important
- Microsoft Exchange Server 2007: 1 important
- Microsoft Exchange Server 2010: 1 important
- Microsoft Exchange Server 2013: 1 important
Deployment Guide
- MS14-064 Windows OLE Component
- MS14-066 SChannel,
- MS14-065 Internet Explorer
- MS14-069 Office
- MS14-067 MSXML
- Ms14-073 SharePoint
- MS14-078 IME
- MS14-071 Windows Audio Service
- MS14-070 tcpip.sys
- Ms14-072 .NET Framework
- MS14-076 IIS
- MS14-074 RDP
- MS14-077 ADFS
- MS14-079 Kernel Mode Drivers win32k.sys
Security Bulletins
- MS14-064 - Vulnerabilities in Windows OLE Could Allow Remote Code Execution (3011443) - Critical - Remote Code Execution
- MS14-065 - Cumulative Security Update for Internet Explorer (3003057) - Critical - Remote Code Execution
MS14-066 - Vulnerability in Schannel Could Allow Remote Code Execution (2992611) - Critical - Remote Code - Execution
- MS14-067 - Vulnerability in XML Core Services Could Allow Remote Code Execution (2993958) - Critical - Remote Code Execution
- MS14-068 - Release date to be determined
- MS14-069 - Vulnerabilities in Microsoft Office Could Allow Remote Code Execution (3009710) - Important - Remote Code Execution
- MS14-070 - Vulnerability in TCP/IP Could Allow Elevation of Privilege (2989935) - Important - Elevation of Privilege
- MS14-071 - Vulnerability in Windows Audio Service Could Allow Elevation of Privilege (3005607) - Important - Elevation of Privilege
- MS14-072 - Vulnerability in .NET Framework Could Allow Elevation of Privilege (3005210) - Important - Elevation of Privilege
- MS14-073 - Vulnerability in Microsoft SharePoint Foundation Could Allow Elevation of Privilege (3000431) - Important - Elevation of Privilege
- MS14-074 - Vulnerability in Remote Desktop Protocol Could Allow Security Feature Bypass (3003743) - Important - Security Bypass Feature
- MS14-075 - Release date to be determined
- MS14-076 - Vulnerability in Internet Information Services (IIS) Could Allow Security Feature Bypass (2982998) - Important - Security Bypass Feature
- MS14-077 - Vulnerability in Active Directory Federation Services Could Allow Information Disclosure (3003381) - Important - Information Disclosure
- MS14-078 - Vulnerability in IME (Japanese) Could Allow Elevation of Privilege (3005210) - Moderate - Elevation of Privilege
- MS14-079 - Vulnerability in Kernel Mode Driver Could Allow Denial of Service (3002885) - Moderate - Denial of Service
Security Advisories
- Re-released: Update for Vulnerabilities in Adobe Flash Player in Internet Explorer (2755801)
Non-security related updates
- Update for Windows 7 (KB2952664)
- Update for Windows 8.1, Windows RT 8.1, Windows 8, and Windows RT (KB2976536)
- Update for Windows 8.1 and Windows 8 (KB2976978)
- Update for Windows 7 (KB2977759)
- Update for Windows 8, Windows RT, and Windows Server 2012 (KB3000853)
- Update for Windows 8 and Windows RT (KB3003663)
- Update for Windows 8.1 and Windows RT 8.1 (KB3003667)
- Update for Windows 8.1 (KB3003727)
- Update for Windows 7 (KB3004469)
- Update for Windows 8.1, Windows Server 2012 R2, Windows 8, Windows Server 2012, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB3004908)
- Update for Windows 8.1 and Windows RT 8.1 (KB3006178)
- Update for Windows 8.1 for x64-based Systems (KB3006958)
- Update for Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2 (KB3008188)
- Update for Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows 8, Windows RT, Windows Server 2012, Windows 7, Windows Server 2008 R2, and Windows Server 2008 (KB3008627)
- Windows Malicious Software Removal Tool - November 2014 (KB890830)/Windows Malicious Software Removal Tool - November 2014 (KB890830) - Internet Explorer Version
- Update for Windows 8 and Windows RT (KB3008273)
- System Update Readiness Tool for Windows 7, Windows Server 2008 R2, Windows Server 2008, and Windows Vista (KB947821) [October 2014]
- Update for Windows 7 (KB2952664)
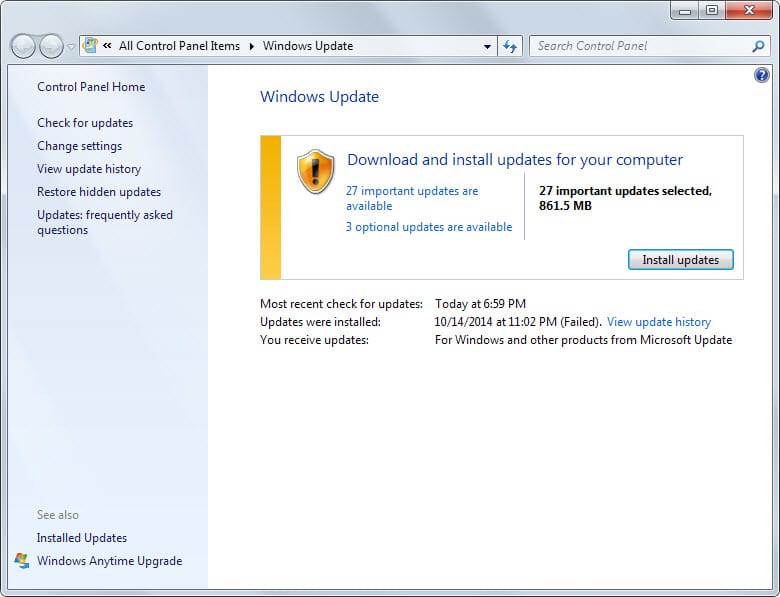
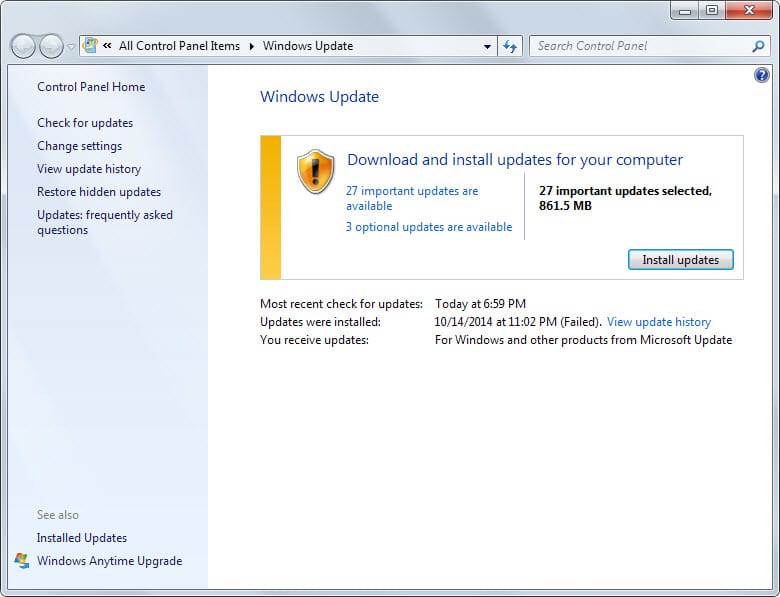
How to download and install the November 2014 security updates
Most Windows users will receive the update via the operating system's automatic update feature. While that is the case, it is also available for download on Microsoft's Download Center website.
There each patch can be downloaded individually or as a monthly security ISO image which Microsoft releases each month as well.
Updates are usually not picked up right away by the operating system. To check for updates manually, do the following:
- Tap on the Windows-key, type Windows Update and select the result from the list displayed to you.
- There you need to click on check for updates to run a manual update check.
Additional information
- Microsoft Security Response Center blog on the 2014 Bulletin Release
- Microsoft Security Bulletin Summary for November 2014
- List of software updates for Microsoft products 2014
- Our in-depth update guide for Windows




















Did everyone get the:
Update for Windows 8.1 for x64-based Systems (KB3006958)
patch? I didn’t even though I’m running 8.1(.1) x64!? What?
Not running W8 anymore, sorry, maybe someone else?
I checked the second PC exhibiting the problem. KB890830 was the only update installed on that one so KB890830 is apparently the culprit. I’m assuming it’s an internet option setting that got hammered but I don’t know which one and I don’t want to experiment.
It appears that after installing KB890830 (and some others) on two desktops running XP, I cannot access https sites.
The others installed at the same time were Office 2010 updates: KB2837602, KB2899521, KB2878251, KB2889935, KB2589386, KB2687275, and KB2889828.
Hi, I installed the updates a few days ago (Windows 7) and I just regret it… Some services could not start reporting an error 5 access denied (firewall, bfe, etc.). A system restore and a start with the last good configuration didn’t work. Finally a windows repair fixed some problems but the firewall still does not start. Any idea if similar problems are reported or if there is a solution I can try? Thanks a lot…
Look at two of the DLLs included in the latest Internet Explorer update: DiagnosticsTap.dll and F12Tools.dll. Go to Properties > Details.
WTF are those crazy characters with diacritics doing in there? Greek / Russian / Vietnamese letters… that are spelling English words but with non-English characters! A practical joke? Something worse?
Careful guys, just to be safe. It’s better to wait maybe a week or 2 before actually installing any MS updates. Else BSOD’s or serious problem might happen to some unlucky ones depending on what software or hardware they use. Just my 2 cents.
Something very strange. I have the notification for the November/14 updates for Windows 8.1, shown
as 17 in total.
When I click on Install, it says Not needed, meaning I have no way to start the Installation.
Why is that?
Just wondering why non-security updates KB2976978 and KB2977759 are not included in your list.
https://support.microsoft.com/kb/894199
Microsoft does not update all resources at the same time. It happens that information get added after the post gets published here on this site.
Emet 5.1 is also out!
Found what happened:
“Users of Microsoft’s EMET…a tool for hardening applications against attack, should upgrade the tool to the new version 5.1 before applying today’s Internet Explorer updates. Microsoft has said that the updates cause problems for users of version 5.0 of EMET.”
In both my PC and Laptop, this update messed with IE: it opens as blank window and the popup “IE has Stopped working”…
Problem details:
Problem Event Name: BEX
Application Name: IEXPLORE.EXE
Application Version: 11.0.9600.17420
Application Timestamp: 545ad233
Fault Module Name: MSHTML.dll
Fault Module Version: 11.0.9600.17420
Fault Module Timestamp: 545ae63c
Exception Offset: 00385f96
Exception Code: c0000409
Exception Data: 00000000
OS Version: 6.1.7601.2.1.0.768.3
Locale ID: 1046
Additional Information 1: 8990
Additional Information 2: 8990e19366e94df1e352bd619aeca6db
Additional Information 3: 2522
Additional Information 4: 2522ebdf06df2ddfd627f18f646f7e1d
Hi I have the some problem but I can’t find EMET on my computer – I three affected
Typo: “How to download and install the October 2014 security updates”
That should be “November 2014” of course. ;)
Thanks, corrected!
Thanks Martin, For letting me know (like you do every mouth! :-) ) where main Microsoft updates (this mount 20 for main 7 system and 2010) where all about. Its ferry handy that I can search and than click on the explaining article.
Like every patch Tuesday its :-) hard work to not only update, backup the system and completely defrag the complete system.
Please keep up the good work.