HTTP Nowhere for Firefox blocks all but encrypted traffic
Protecting your privacy online is a hot topic right now, with PRISM looming over the heads of all Internet users. But even if you take PRISM aside, there is a drive towards privacy on the Internet.
One of the things that users need to be aware of is the difference between http and https requests on the Internet. While browsers provide those information visually, for instance by adding a lock symbol to requests or changing the color of the protocol, it is not standardized and they are easy to ignore, especially with recent changes to how they are displayed in the browser.
Firefox users can improve the visualization by installing extensions such as Safe. That does not take care of situations where unsafe or insecure contents are loaded on secure websites. Mozilla has plans to tackle those situations as well.
Sometimes though you may want even more assurance than that, make sure that your browser is protected when you visit important websites that offer https.
Encrypted-only Mode
An idea that has been expressed recently is to create an encrypted-only mode in web browsers, much like the private browsing mode works today. But instead of making sure that no session date is recorded by the browser that may reveal the sites you have visited in it, it makes sure that only encrypted connections are allowed in it.
That's where the Firefox extension HTTP Nowhere comes into play. You can use it to block any insecure traffic in Firefox, so that only https connections are permitted.
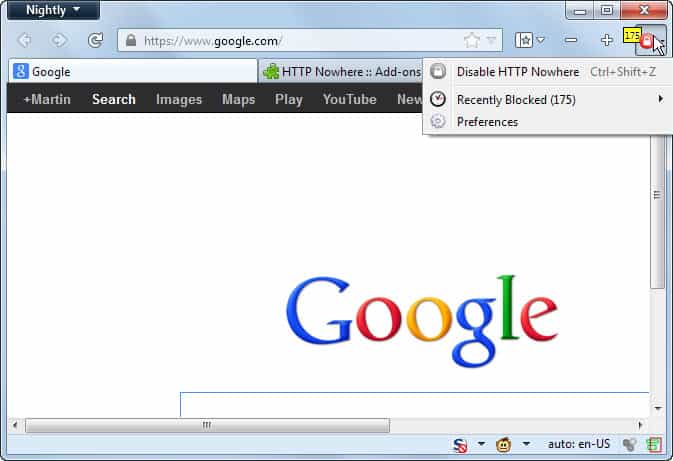
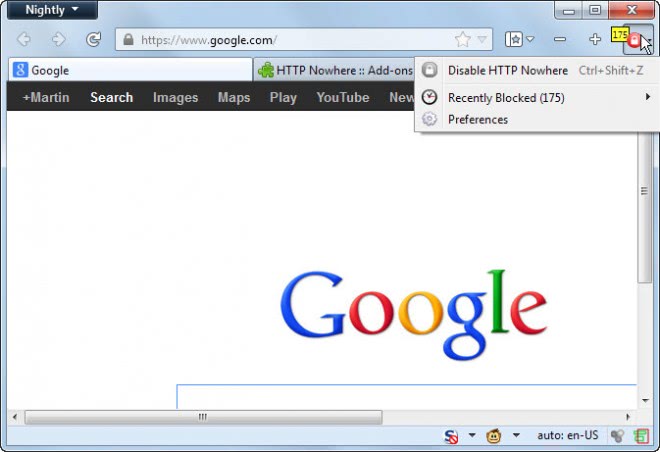
The extension adds a single icon to the address bar that indicates whether it is active or not, and how many insecure connections it has disabled. A click on the icon lets you switch between encrypted mode and normal mode.
The idea here is to enable encrypted mode when you need to access security or privacy related websites such as your online banking website.
So, you enable HTTP Nowhere before you connect to your bank's website or another important website, do whatever you need to do there, and disable the extension once you are done and have closed the tab.
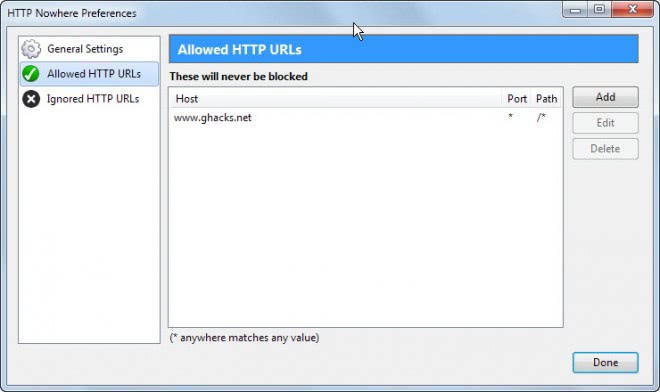
You can use the extension with its strict default rules, that is disallow all but https connections, or white list specific hosts that you want allow. You can white list hosts using the recently blocked menu, or by opening the preferences of the extension to add hosts, ports and paths manually.
The developer of the extension notes that it is compatible with the TOR browser bundle. Tor users can make use of it to improve their privacy and security while using the software even further. Note though that Tor onion links are by default blocked by the extension, and that users who want to access them need to whitelist onion urls to do so.
The extension is also compatible with HTTPS Everywhere but as the author notes, the latter is not able to use its automatic https redirecting when both extensions are running in the Firefox web browser.
Verdict
Firefox is the browser when it comes to security and privacy extensions. Sure, extensions are also available for other browsers, but it is predominantly Mozilla's web browser that is setting new standards in this regard.
The extension adds another extension to an already impressive arsenal of extensions the Firefox browser offers. While it may be too specialized for many, it may be ideal for specialized cases where security is of utmost importance.
Advertisement



















Auto Green Adress Bar
I find turning the firefox address bar green on secure sites useful.
Simply type
#urlbar[level] .autocomplete-textbox-container { background-color: #A0FFA0 !important; }
into the firefox userchrome.css file
C:\Users\username\AppData\Roaming\Mozilla\Firefox\Profiles\yournumber.default\Chrome
Currently I use HTTPS Everywhere in combination with HTTPS Finder.
“HTTPS Finder automatically detects and enforces HTTPS connections when available. It also provides one-click creation and in-browser editing for HTTPS Everywhere rules.”
The concept of HTTP Nowhere seems stricter, though.
I read in an article on ExtremeTech that The NSA already has HTTPS covered.
Allegations that NSA tool can neutralize common online security:
http://rt.com/usa/allegations-nsa-tool-decrypts-https-085/
Had been “thinking” about using this one, Martin – but after reading your complete review (as usual), I’m going to give it a shot. Your banking example was exactly the use I had in mind. Stopped using HTTPS Everywhere a while ago due to its memory resource demands. I’ve been using HTTPS Finder – not totally sure how effective it really is, but with this, I’m feeling like I’ll have added protection. Going to rearrange my financial toolbar icons next to this one as a reminder to click on this one! LOL!