How To Turn Chrome or Firefox Into A Single-Site Browser
A Single-Site browser serves a very specific purpose. You use it to access one, and sometimes a handful, of websites and services on the Internet. This can be financial sites, your email accounts or other sites with personal information like a medical related sites. The basic idea is to block access to all other sites to protect the account and information from certain attack forms like cross site scripting or clickjacking.
All connections are blocked except to those sites that you have explicitly allowed. This means that third party scripts won't be loaded if they originate on a non-whitelisted domain, and that you won't be able to open third party sites manually in the browser.
This guide demonstrates how to turn Firefox and Google Chrome into a single-site browser. Inspiration has been taken from Vasa's post over at the Wilders Security Forum.
Google Chrome
Google Chrome users can make use of the --host-rules parameter to block all domain connections except the ones they whitelist. The general parameter looks like this:
--host-rules="MAP * 127.0.0.1, EXCLUDE *.ghacks.net"
This redirects all connection attempts to localhost, except for connections to the ghacks.net site or one of its subdomains.
You can also add multiple inclusions in the following way:
--host-rules="MAP * 127.0.0.1, EXCLUDE *.ghacks.net","MAP * 127.0.0.1, EXCLUDE *.microsoft.com"
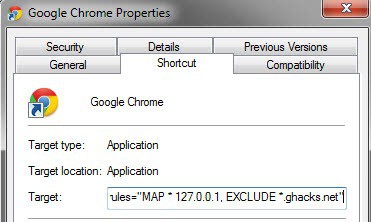
Windows users can add the parameter to Chrome in the following way:
- Locate a Chrome shortcut in the Start Menu, Taskbar or Desktop
- Right-click the shortcut and select Properties
- Append the parameter to the end of the Target listing, with a space in between.
- Click Ok to apply the settings.
You could alternatively create a second shortcut to use it for accessing your important sites, and keep the general shortcut for all other sites that you visit in the browser.
Firefox
Mozilla Firefox users need to install the SimpleBlock extension for their browser first. They then need to create a SimpleBlock.ini file in the user profile folder and add a regular expression to it to allow access to certain sites.
R: https?://(?!(My.bank.com|Second.site.com|Third.site.com))
This would allow access to the three domains mentioned above, and block all other connection attempts.
It is probably best to create a new user profile for this. You can use an add-on like Switchy or the new Firefox profile manager application.
Closing Words
It is best to create new profiles or shortcuts to work with Single-Site browsers. Security add-ons like NoScript can mitigate the issues if they are configured properly.
Advertisement


















This doesn’t work.
Could this work on Android or iOS devices?
No longer applicable?
did not work for me A message pops up each time
the name is specify box –host-rules=”MAP * 127.0.0.1, EXCLUDE *.ghacks.net, EXCLUDE *.microsoft.com”is invalid
what
You can add multiple inclusions in the following (shorter) way:
–host-rules=”MAP * 127.0.0.1, EXCLUDE *.ghacks.net, EXCLUDE *.microsoft.com”
There is no need to retype the “MAP * 127.0.0.1” part.
>This means that third party scripts won’t be loaded if they originate on a non-whitelisted domain
Or Firefox users could just use the noscript plugin. Much easier interface than SimpleBlock IMHO.
An interesting approach to create a single site browser.
Personally, I use portable versions of browsers just for this purpose.
For example, I use SRWare Iron to access Google Voice and only that site.
Which would leave you vulnerable if someone managed to post an exploit on that site.
Yes, but what is the likelihood of that?
And one could protect a portable browser
in a similar manner if one did feel vulnerable?
Yes you are right. The likelihood is slim and you could protect the browser in a similar manner.