Google Funded Browser Security Comparison Says Chrome Most Secure
A recently conducted and published browser security comparison by Accuvant Labs comes to the conclusion that Google's Chrome browser is more secure than Firefox and Internet Explorer.
The researchers looked at specific browser security technologies and their implementation in web browsers.
That's an analytical what-if approach, and fundamentally different from analyzing a browser's vulnerabilities in the past.
Only the most recent versions of Microsoft Internet Explorer (9), Google Chrome (12 and 13) and Mozilla Firefox (5) were analyzed. Other browsers, like Opera or Safari, were not included in the research.
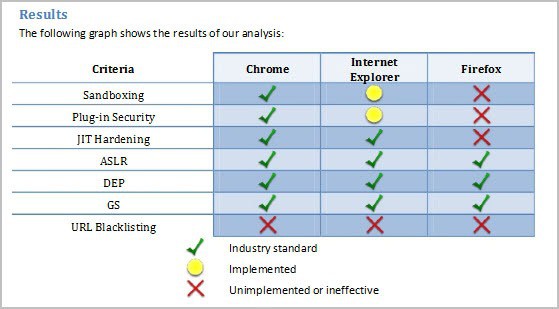
The results and areas that have been analyzed in the study are displayed in the table below.
All three browsers have implemented industry standard data execution prevention, address space layout randomization and stack cookies anti-exploitation technologies.
The researchers found Firefox's sandboxing, plug-in security and JIT hardening to be either unimplemented or ineffective. They also concluded that Chrome had the edge over Internet Explorer as the browser's implementation of sandboxing and plug-in security was industry standard, while Internet Explorer's was not.
Here is the conclusion of the research paper.
The URL blacklisting services offered by all three browsers will stop fewer attacks than will go undetected. Both Google Chrome and Microsoft Internet Explorer implement state-of-the-art anti-exploitation technologies, but Mozilla Firefox lags behind without JIT hardening. While both Google Chrome and Microsoft Internet Explorer implement the same set of anti-exploitation technologies,Google Chrome’s plug-in security and sandboxing architectures are implemented in a more thorough and comprehensive manner. Therefore, we believe Google Chrome is the browser that is most secured against attack
Neither the fact that the research was sponsored by Google, nor the missing definition of industry standard disqualifies the research paper immediately. It is however something that needs to be addressed and looked at.
It needs to be noted that core browser security plays just a part in a user's threat protection. Other factors include the operating system, up-do-date plugins and browser versions, browser extensions or security software.
What's your take on the research paper?
Advertisement

















All is in the title.
A non-info that pollutes the web,.
LOL, they didn’t include Opera, which almost always comes out ontop of INDEPENDENT security tests.
Google Chrome 159 – http://secunia.com/factsheets/Chrome-2011Q2.pdf
FireFox 72 – http://secunia.com/factsheets/Firefox-2011Q3.pdf
Internet Explorer 25 – http://secunia.com/factsheets/IE-2011Q3.pdf
Opera 36 – http://secunia.com/factsheets/Opera-2011Q3.pdf
Definitely not what we found. We found IE to be the most secure with chrome being as bad as any other. Other research dictates that IE is the most secure.
The research was in July so why have they sat on it for 5 months? Seems pointless to compare IE9 vs FF5 now whereas current is IE9 (still) vs FF8…
Research this out of date does invalidate it imho – and the Google funding is a red flag, has anyone ever come across research funded by a company that slates that company’s products? Just doesn’t happen – you get what you pay for.
Chrome may well have the edge over FF in its default state but I’d like to see comparisons using common security add-ons that FF excels in.
The date of the comparison does not matter in this case because the lack of security features that are shown in the article are still truetoday.
Yours is the first writeup that notes that the study was funded by Google. As you noted, that should not invalidate the findings. Now you know why folks visit your site.
This biased research tells us exactly what browser google wants to overtake.
United against IE… who believe this anymore?
There is a clear bias in the way this comparison was conducted.
“Only the most recent versions of Microsoft Internet Explorer (9), Google Chrome (12 and 13) and Mozilla Firefox (5) were analyzed.”
The most recent Firefox version is 8, not 5. Version 5 is a very old one and yes, it had the problems mentioned in the article. Version 8 fortunately does not have them anymore, but then again, that wouldn’t have looked well in the comparison. It is all just marketing.
All those browser versions are old and were the current versions when the report was conducted. How is that bias?
This is just more Chrome marketing by Google. They’re not content with bundling the browser with a lot of popular applications – opt out of course – they have to constantly try and persuade us it’s the browser of choice because it’s supposedly more secure.
Unfortunately, it’s those who can’t or won’t read between the lines that will undoubtedly install Chrome and will have no clue they’ve just surrendered even more of their privacy.
Seriously, Google Chrome is becoming like one of those nasty toolbars that get bundled with some applications. If one searches for “which is the most secure browser” the first several pages link to this report and it’s not until the 5th or 6th – depending on bing or google that the search result mentions it’s Google funded.
It [Chrome] may have a sandbox and out of the box, it may offer a little more security than the competition – Opera and Safari aside, as they weren’t tested – but there are many more considerations when choosing a browser.
Forgot to mention that if anybody believes or even thinks that Internet Exploder is secure, he/she only has to remind themselves of one feature that NO other Browser uses, namely ActiveX!!
Apart from the fact that IE has more security holes than a sieve, the flaws are totally ridiculous!
Some time ago, Microsoft asked the people at Mozilla to help them patch their Browser, to make it more secure!
Obviously, Microsoft was aware of the problems, but had no clue on the remedies!!
So, I’ll take the above “Funded by Google” report with a grain of slat!!
A sieve? Then what does that make Firefox? According to Secunia in their 2011 Q3 reports, IE9 has had 19 vulnerabilities. Firefox so far has had 18. IE9’s saving grace at least is that in Windows 7/Vista and it uses sandboxing so even if those vulnerabilities were exploited, they wouldn’t effect the OS.
One thing that is not evaluated: how effective are the features in chrome like sandboxing? Let’s just say that the sandbox offered isn’t very good.
And as already said above, there are other methods to improve security via addins or other programs that people should (or already are) using.
Anytime I see a “study”, it’s almost always commissioned and paid for, and of course the results favour the paying party’s app – otherwise payment for the study might take sometime to arrive in the “mail”. :)
Chromes sandbox has yet to penetrated since it’s initial release. Only once there was a claim by Vupen that they defeated the sandbox via a flash exploit and there was never even an exploit in the wild.
Such as? Remember, I’m specifically talking about exploits that have been able to break out of the sandbox. The Vupen exploit was widely publicized when it came out and there have been no other reports since.
Not true – there are numerous exploits that have been out in the wild (using address space layout randomization (or ASLR), data execution prevention (or DEP)).
No why don’t we hear about them? Well to Google’s credit, they fix the holes quickly – and you don’t see it as Chrome auto updates (even if you say not to, critical patches can be pushed). Secondly, have you ever tried to Google something that could impact Google.?
Not so easy lol
“Google Funded Browser Security Comparison”
If this research was funded by Google, stands to reason why their Browser would be rated Most Secure!!
Money talks, right?
Firefox is just as secure, with one advantage…It doesn’t call home!!
Chrome does!! May be somewhat secure, but privacy issues are wide open!
Chrome is more secure because of JIT hardening, sandboxing, and plugin-sandboxing. Firefox doesn’t have any of that.
and Firefox does phone home for updates just like Chrome does.
I use Firefox, but Firefox got no sandboxing yet and it’s unsure if it will be used to improve security. There’s no plugin security. I also think Firefox is dragging behind.
The paper only analysis an attack on the system e.g. executing code.
Chrome would have been the winner, anyway.
You can always disable the Plug ins that you don’t need and feel are insecure!!
“…the fact that the research was sponsored by Google…”
–
And if this lab determined Firefox or Internet Explorer was the most secure browser would we even be reading this article?
Totally irrelevant, huh? :)
How recently can this be conducted when there using Firefox 5 and because of that how now known worthy is this document today? I would say its old re-chewed news. Even more because a browser like opera and safari needs to be included in this kind of research publications.
It feels a bit like a cigarette firm who saying to you that you have to smoke more.
These studies typically like this one evaluate security offered by
the browser itself and do not account for methods external to
the browser that provide equal or greater security protection.
For the sophisticated user, all three browsers
can be made effectively equal in security.
The best that can be said about this study is
Chrome is the most secure browser for the
unsophisticated user which is not exactly
a strong selling point to the tech savvy.
> “The best that can be said about this study is Chrome is the most secure browser for the unsophisticated use”
I highly doubt that can be said considering chrome allows me to to view that user’s stored passwords with just the click of a button in chrome’s settings. It doesn’t even offer users the opportunity to encrypt using a master password if they were smart enough to do so.
My comment was based upon the assumptions in the study.
I did not say I agree with any of the study assumptions.
If one accepts the assumptions my comment is valid.
how do you know the research was funded by google?
Read the original article. It says so. That’s how one knows.