MultiObfuscator, Advanced Cryptography Software
Sometimes you may want to protect some files or maybe even just one document from third party access. While you could use an encryption software like TrueCrypt to create a container to put those files into, you sometimes may prefer an easier solution.
MultiObfuscator is a free program for Windows that uses multiple security layers to protect data from third party access. In particular, the program uses a three layered approach that combines cryptography with data scrambling and based whitening. Users can furthermore use deniable cryptography to use less important data as a decoy in case someone's forcing them to decrypt the data.
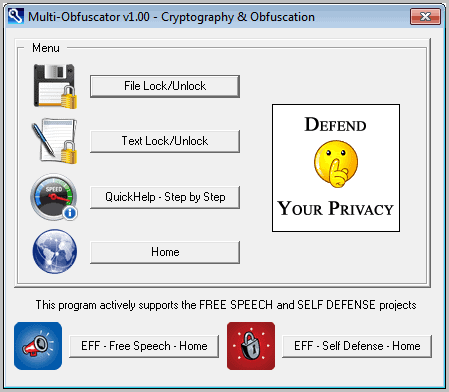
The encryption software is portable. Once executed, users will see the following screen.
Here they can access the help which offers a step by step guide explaining how to use the program. The two options to lock files or texts open configuration menus where users can configure the encryption and obfuscation individually.
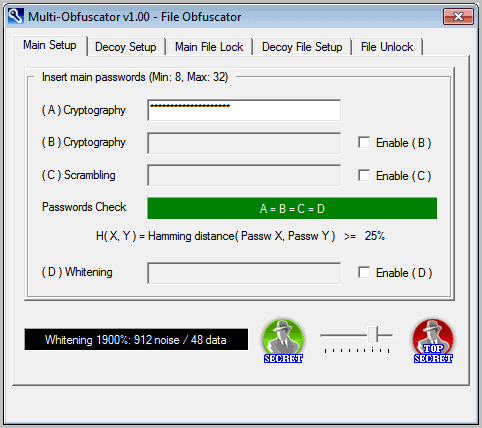
The program divides the necessary steps into tabs in the program window. Users need to configure settings in a minimum of two tabs. First in the main setup tab where the protections are configured, and then in the main file lock tab where the file to protect is selected. Two additional tabs are added to the setup if a decoy file needs to be added.
The excellent help file gives lots of examples and tips on how to lock and unlock files with the help of the program. All usage scenarios are described in detail here.
Windows users who are looking for an easy to use advanced security software that is portable and Open Source, should take a closer look at MultiObfuscator. The software is available for download at the developer's website. The software is compatible with all recent 32-bit and 64-bit editions of the Microsoft Windows operating system.
The program refers to those options as easy, medium and expert setups. An easy setup for instance would just encrypt the selected file, while an advanced setup would use multiple protection methods to protect the file.
Advertisement





















Unless my eyes are failing me and I missed it, here’s a link to the developer website:
http://embeddedsw.net/MultiObfuscator_Cryptography_Home.html
You are right, link added.
You forgot to include a link to the developer website. There’s no download link, which is not necessary.
Sorry added.