Firefox Search Engine Security Add-On, Protects Against Referred-Based Attacks
A common attack form on the Internet is to optimize web pages or domain for specific keywords to make them appear on the first search result pages of popular search engines such as Google or Bing.
The attack is enabled once the page or domain receives first visitors from the search engines, which are more often than not unsuspecting of the dangers of the site. Different types of attacks are used on those sites, from harmless spam and popups over drive by downloads and redirects to fake antivirus offers.
Many of the pages have in common that they display different results for search engine visitors and visitors who do not come from search engines. This is relatively easy to do by checking the web browser's referrer value.
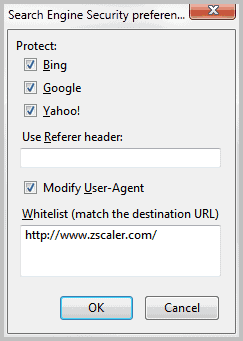
The new Firefox add-on Search Engine Security protects users from some referrer based attacks by changing the referrer of the web browser when coming from search engine pages. The extension supports Google, Bing and Yahoo currently.
It basically displays a different referrer than the one it should display. The effect depends largely on the attack site. Users may circumvent attacks if the site checks the browser's referrer to display a harmless page to non-search engine users.
While that's obviously no 100% protection against these kind of attacks, it is another layer of protection. In addition, it may be beneficial from a privacy point of view although the use is rather limited.
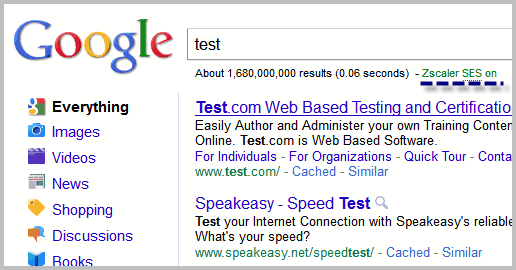
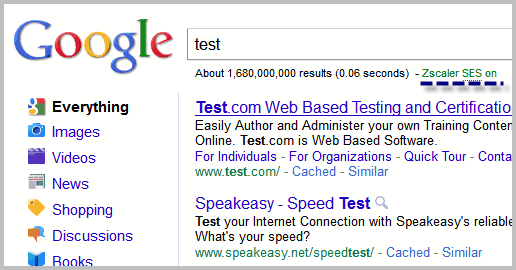
The extension works on the search engines that it supports as well as localized search engines. Zscaler SES on or off is displayed below the search form to indicate if the add-on is enabled on that particular search engine.
Search Engine Security can protect Firefox users from redirect attacks that load fake antivirus pages, videos or other malicious contents. Firefox users can download the extension from the official Mozilla Firefox add-on repository.
You can disable the add-on on for a specific search engine in the options. Here you can also add sites to a whitelist, which may be happy if a legit website checks referrers and displays different contents based on those. Lastly, it is possible to add or change the referrer itself in the preferences.
Update: The add-on has not been updated since 2011. You may want to check out Smart Referer instead which only sends referer information when links point to the same domain.

























Interesting concept and a useful add-on. Good explanations of why it is needed!
I like WOT (Web Of Trust) to protect against dodgy websites in search results but it would be of no use against a newly hacked website that is normally well rated – this add-on should help.
Another nail in the coffin of IE which doesn’t allow blocking the referrer (although you could use a firewall/AV suite to achieve it)?
bastik, thanks for the explanation. Only now I understand the purpose of this extension.
The same trick is done by websites which offer free software, but require personal information and send you a bill after you downloaded some free stuff because they claim you agreed to an pay subscription.
When you visit such a site from Google (or Bing) there’s no sign of any service that would cost you money, but when you visit the site directly the information about the costs is displayed.
The trick behind is that you search some free software through Google, enter your private data and if you get the bill you most likely visit the site directly. Then you may be afraid that you overlooked it and pay the bill.
Great article. There are other addons to control referers, of course this one is very easy to set-up.
Hi Martin,
thanks for another good FF ext!
Interesting…
I do have a simple, (maybe silly) question:
– why would a malicious website you land in,
wish to try to attack you,
ONLY if you are “refered” by Google, Bing or Yahoo?.
Suppose I _click on a link_ in “Reddit.com”
or “innocent_sheep.com”.
I’ll then land on the malicious website.
Will this bad site not try to attack,
even if I ** didn’t ** come from Google?
After all, the objective of a bad site is to attack you,
no matter where are you are coming from….right?
thanks,
One reason might be “hacked” websites.
When you set-up a domain to attack someone I agree that you most likely attack everyone who hits the page where ever he comes form. (although some try to filter IP ranges from antimalware vendors)
When you manage to break into a website (which is popular) it’s most likely that people that belong to that domain will not visit their site through web search and therefor not discover the attack. Like I visit ghacks directly and would not notice anything if there would be a problem.
Great find Martin, Thanks a mill. for this. I am constantly looking for upgrading main browser security, and naturally also the rest of main computer. And i think this is a worth-will extension to main outer security measures, despite the small delay at startup
On a outer note i wish that the developer is upgrading the Firefox add-on url-security0.10, to a newer version compatible with Firefox 4.0.1. Do you maybe know or this is happening in the near future, or do you maybe know an alternative for this add-on?
Would something like Buffer Zone work as well and perhaps more so?
That’s something like a sandboxed environment right? Sure, it protects you but you need to make sure you do not enter personal information or stuff like that.