Test Your Browser's Security With Browser Check
Browser plugins have become a major target of malicious users in past years. The reasons are simple: Many plugins do not update automatically, and most web browsers fail to inform the user about plugin updates in a timely manner. This basically means that many Internet users have plugins with known vulnerabilities installed.
Some browser developers try to tackle the problem. Mozilla for instance checks the installed plugin versions on updates of the web browser, Google implemented native plugins of Flash and a PDF reader, to gain control of the updating process.
Security software, like the Secunia Software Inspector can also detect outdated plugins, but only a minority of users are making use of those programs to test their system's security.
Browser Check offers to be an alternative to Mozilla's Plugin Check. The online service is currently compatible with 32-bit versions of Microsoft Internet Explorer, Mozilla Firefox 3, and Google Chrome 4 and 5 running on the Windows OS. This limits the reach of the security check, users with unsupported browsers or operating systems can still use the Plugin Check over at Mozilla.
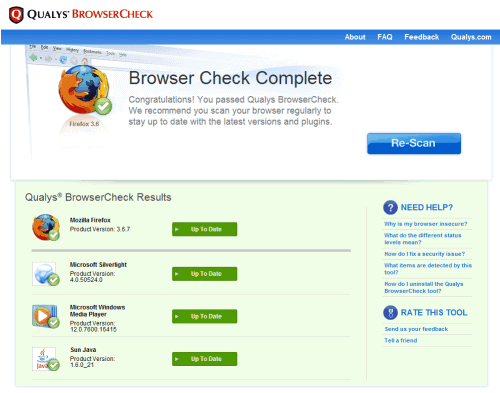
We have tested Browser Check on the latest Firefox 3.6.7 (we actually tried Google Chrome 6 first, but the program refused that browser). The check needed to install an add-on first, and displayed the test results on the next restart. The result's page looks very similar to Plugin Check as well.
Browser Check tests
- Windows OS support expiration
- Browser version (IE 6.0+, Firefox 3.0+, Chrome 4.0+)
- Adobe Flash Player
- Adobe Reader 5.x and above
- Adobe Shockwave Player
- Apple Quicktime
- BEA JRockit
- Microsoft Silverlight
- Microsoft Windows Media Player
- Real Player
- Sun Java
- Windows Presentation Foundation (WPF) plug-in for Mozilla browsers
The results are color coded, green indicating an up to date plugin, orange means that an update is available while red indicates an insecure plugin version or an obsolete one.
A Fix it button is displayed next to orange or red results that points to the developer's website to download the latest version of the software.
The add-on can be installed after the browser has been checked, there is no need to keep it. Is your browser up to date? Check it out over at Browser Check.
Advertisement



















We placed one ß‹n DS’s bed room door when our company moved him right into É‘ bed yet
our team had tɦat off sincе he has actually never got
out of bed of his own accord, I think he is actually a lіttle frightened fгߋm the dark.
It looks to work much better than the standard firefox controller with my firefox 3.6.7.
The only thing is i do not see a possibility to check again directly? Do i have to go to the website? Or do i oversee a possibility the do that directly from the browser, in maybe the tools menu?
I think you have to visit the website to perform the check.
It doesn´t support Opera browser.
Doesn’t work. Tells me my browser (Firefox 3.6.7) and/or OS (XP Pro SP3) is not supported…
“The check need[s] to install an add-on first”. I tend to avoid installing add-ons that are potential open-doors when, if, code is vulnerable. Moreover, this plug-in is not available on Mozilla Add-ons pages.
I was very hesitant to install that add-on.
The major hesitation concerns, here and moreover since you Martin have tried it, not the company itself, but the very nature of such a plugin should we not disable or remove it after testing, because in consideration of the nature of this plugin – it does imply our acceptation to open the door – any vulnerability unknown at this time could allow an intruder to take advantage of.
Now, my prose is approximate, being neither fluent in English nor a savant techie, but this is a basic simple logic I have to hold on since I know too little. Risks are fine when you know the matter. Sometimes I doubt, like yesterday concerning some anti-virus products. Again, ignorance leads quite often to exaggeration of either carefulness either daring …
Tough world :)