Encrypting USB Devices Data With True Crypt

If you do not want to end like British government officials who lose USB devices with unencrypted data in front of pubs you might want to consider encrypting the data so that it cannot be recovered if the USB device would be lost. It is not entirely true that the data cannot be recovered but if you choose a long password and make sure to pick a safe encryption algorithm then you are on the protected side for now as it would take years to brute force the password.
True Crypt is an Open-Source software that can be used to create encrypted containers on devices. One of the major advantages of True Crypt is that it can be used as a portable application which means that you can copy the True Crypt files on the USB device so that the software does not have to be installed on the computer system where the data is needed.
There is however the requirement that the user who wants to mount the True Crypt volume to get access to the data needs to have administrative rights to run the software. That is however the only requirement.
Download the True Crypt software and run the setup. The setup displays options to install or extract the contents. Choose the extract option and pick the USB device as the target. All the files needed to encrypt and decrypt data will be extracted to the USB device.
Run truecrypt.exe afterwards. We need to create an encrypted container on the USB device that can store the data that we want to protect. It is limited to the free space on the USB device.
Click on Create Volume in the main interface and select the option to create an encrypted file container. Use the standard volume type in the next screen. Now browse to the USB device and pick a random filename that should be used as the container. You can use any name or extension, it does not really matter, for example test.avi, test.txt or bigrar.rar.
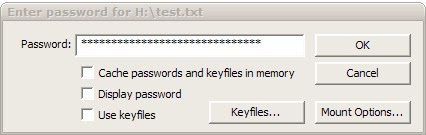
Pick an encryption algorithm (AES is fine and fast) and a Hash Algorithm (SJA-512) and define the space on the device that you want to assign. Select a password (20+ chars are recommended, the more the securer). The volume (in this case the space that you have selected) will be formatted. Move the mouse around to create random information and click the format button in the end.
This completes the creation of the encrypted container on the device. You need to mount it whenever you are going to use it. This is done by executing True Crypt from the USB device, picking a drive letter and selecting the file that contains the encrypted container.
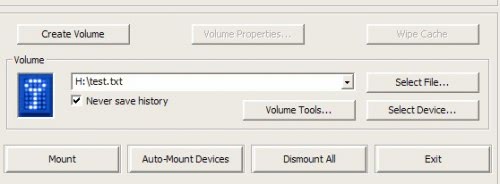
The last step would be to click on mount to enter the password that is needed for the data decryption.
The data will be secure whenever the container is not mounted on the computer system. That's one of the safest ways of transporting data from location A to B. Got any questions? Let me know.
Advertisement





















Ok There is a very imortant question that I have.
I have an external Hard drive which is like a USB.
What I want to do, is to make the hard drive ask for password no matter where u connect it. What almost every guide shows is stuff like making container and other things which force you to install truecrypt anywhere u want to access ur files.
What if I wanted to encrypt my hard drive, go to school and put it on my friends laptop and show him a video. He needs to have truecrypt inorder for the file to be opened.
In order to open the hard drive on another computer which does not have truecrypt installed on it, what should I do?
Can truecrypt help me?
Ebram, no you cannot do that with True Crypt but Microsoft’s Bitlocker To Go can do that.
The only drawback is that you must be admin to run Truecrypt in traveller mode and so at friends where they are admin, thats fine but in the office or in a webcafe … no way, so Truecrypt is excellent when it can actually work, otherwise the only flexible way is hardware encryption (within the key) which can be run on any platform w/o being admin, these key are more expensive though (Kingston Privacy Edition)
Extremely useful device! And no, I don’t want to end like britsh government officials! :-)
Hi!
If you have TrueCrypt allready installed -like me- you can create the volume on the Drive first, and then, in the Truecrypt main window, you can use “Tools -> Traveler Disc Setup” to copy all nessecary files to the drive. AND: you can configure the autorun.inf what to do (Nothing / Run Truecrypt / AutoMount truecrypt container (w/o password))
Doesn’t work if the entire Drive is encrypted, only with containers.
Do you have to copy Truecrypt to the device yourself?