Computer Security Software ESET SysInspector
Scanning a computer system with a computer security software like ESET SysInspector can reveal security related problems in short time. Those security software programs are by far not the all-knowing and -seeing eye but they provide an in depth analysis of a computer system that can be used to find some of problematic files that could be a security risk.
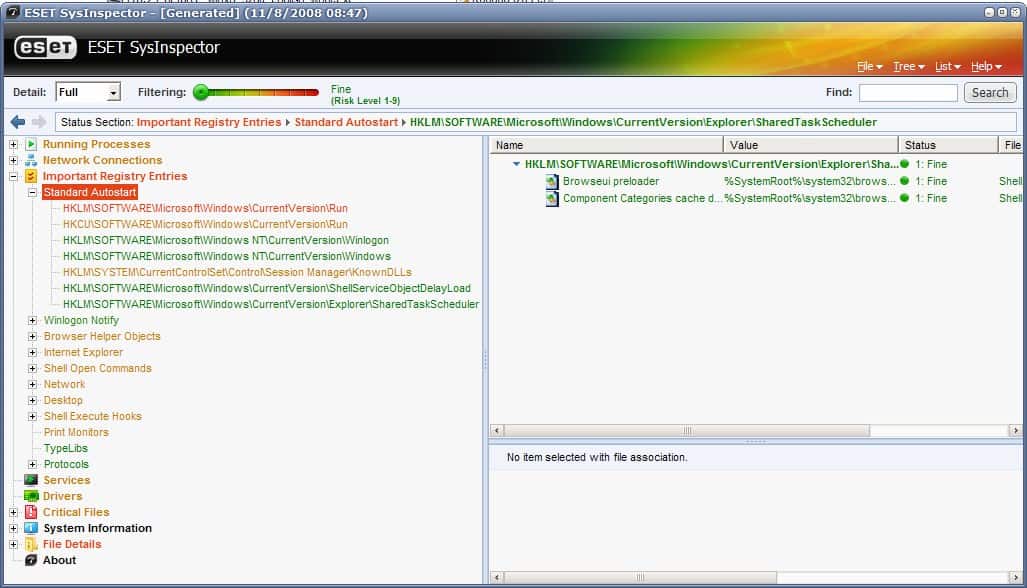
ESET SysInspector does that by scanning the computer's hard drive and Registry. It assigns a risk level to every item that has been analyzed which ranges from fine (1) to risky (9) with three always bundled together. Risk levels 1 to 3 are assigned to files that have passed the check, 4-6 for unknown files and 7-9 for files that have been identified as being risky. The different levels are also colored differently (from green to red) to make identification as quickly as possible.
The computer security software will build a report that provides access to eight different categories including Running Processes, Network Connections or Important Registry Files. Each category is displayed in the color of the item with the highest risk level that it contains. That's excellent for identifying the highest risks with one glance without having to look at the actual items at that time.
Opening a category can reveal subcategories or items. Each item is (again) listed in a color that depicts its risk level. Some categories can contain dozens of items and the risk level slider at the top helps reducing the amount of items displayed by selecting a minimum risk level to be displayed. Every item with a lower risk level will be hidden from the display so that the system administrator can concentrate on the higher risk items.
A higher risk level does not necessarily mean that an item is dangerous. That would be subject to further analysis. ESET SysInspector is providing some tools and shortcuts for this. A right-click on an item will open a context menu with options to open the path in the Windows Registry or to open the file's location on the computer's hard drive. There is also the possibility to perform an online search using the default web browser and the Google search engine.
A set of reports can be created that contain various level of information. One interesting feature is the ability to compare logs which can give additional clues on system changes in a time period.
Advertisement




















Powerfull stuff! Makes checking your registry files very easy. I’ve been using nod32 for some time now and just recently i discovered SysInspector.
Great find and great review!