Patches for new Retbleed AMD and Intel microprocessor vulnerability may have significant overhead
Certain microprocessors from Intel and AMD are vulnerable to a new speculative execution attack related to Spectre Variant 2. Attacks may be used to leak data from kernel memory and mitigations may cause overhead and impact performance of patched systems.
Researchers at ETH Zurich discovered the vulnerabilities, which they named Retbleed. The attacks exploit vulnerabilities in retpoline, a mitigation introduced in 2018 to mitigate certain speculative execution attacks.
Retpolines work "by replacing indirect jumps and calls with returns". Concerns that returns might also be susceptive to attacks were ignored back in 2018, as it seemed impractical at the time to many. Retpoline research confirmed that exploits are "indeed practical"
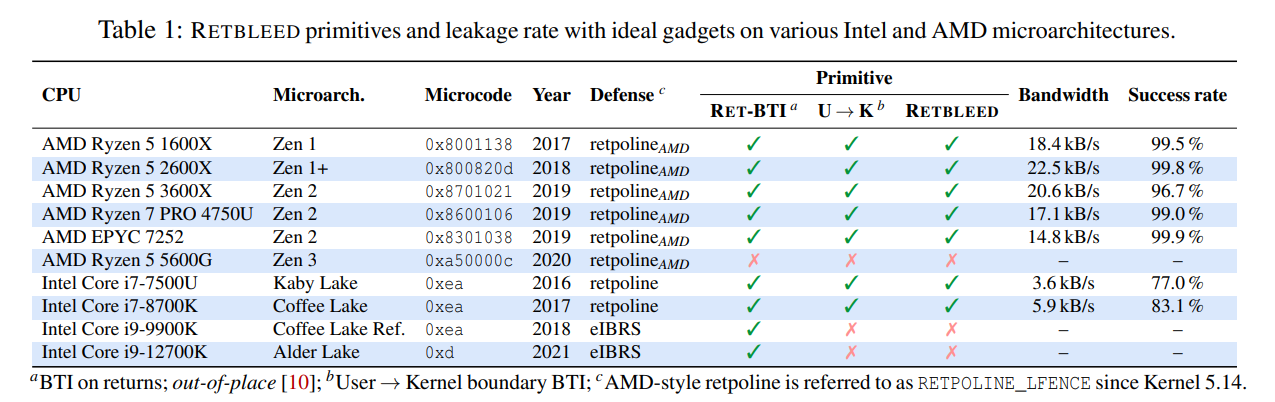
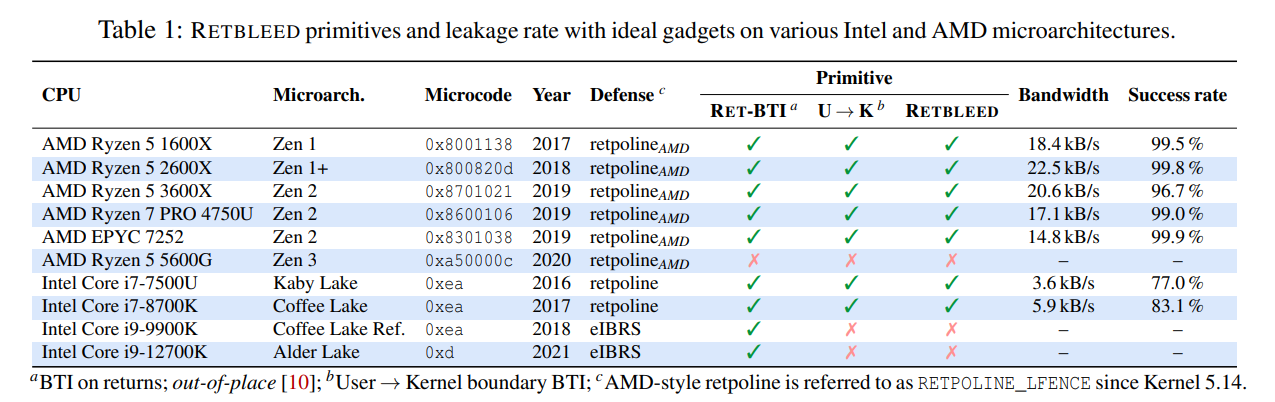
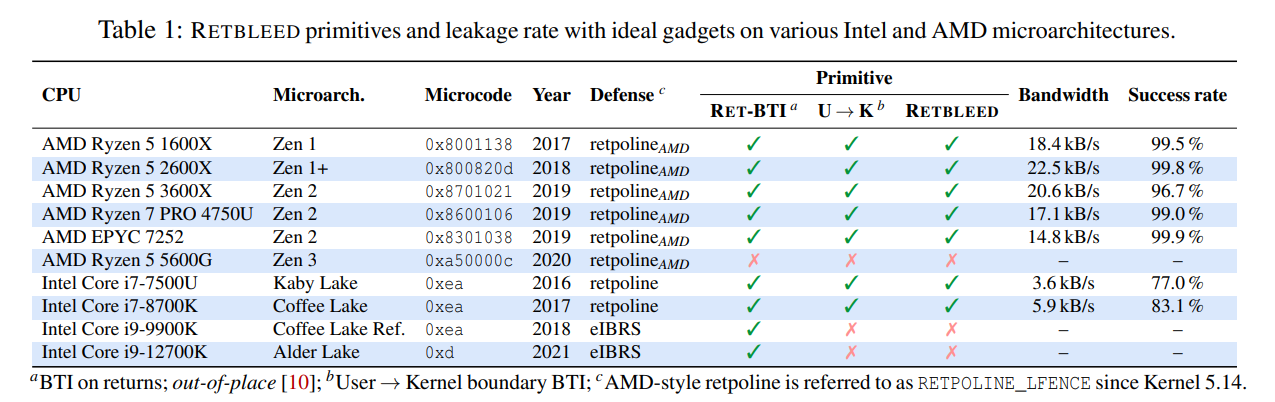
The ETH Zurich researchers confirmed the vulnerabilities in older Intel and AMD processors only. According to the released FAQ, Intel Core generation 6 to 8 processors, and AMD Zen 1, Zen 1+ and Zen 2 processors are vulnerable.
The vulnerability was confirmed by the researchers for Linux devices. The researchers state in the FAQ that Windows and Mac systems are affected as well. Intel, on the other hand, stated in a blog post, that company processors on Windows are not affected:
Intel has worked with the Linux community and VMM vendors to provide customers with software mitigation guidance which should be available on or around today's public disclosure date. Note that Windows systems are not affected given that these systems use Indirect Branch Restricted Speculation (IBRS) by default which is is also the mitigation being made available to Linux users.
AMD and Intel are not aware of exploits in the wild that target the new vulnerabilities. Patches for major Linux distributions are already being prepared. Tests will show if and by how much performance will be impacted on systems with the patches.
Here are important links that provide you with additional information:
- ETH Zurich: Retbleed: Arbitrary Speculative Code Execution with Return Instructions
- AMD CPU Branch Type Confusion bulletin
- Intel: Return Stack Buffer Underflow / Return Stack Buffer Underflow / CVE-2022-29901, CVE-2022-28693 / INTEL-SA-00702
Now You: do you run one of the affected processors?


















The 12700K should be i7?
We really need a huge class-action lawsuit to stop this trend. Otherwise the industry will eventually make a 5950x perform like a 486 “because security”. “Oh and by the way, our latest models haven’t (yet) been downgraded with performance-destroying updates!”
They want the farm to consume more energy… because it’s so anti put in. :)
Yeah, that would make sense, a class action to prevent a company from fixing security issues.
+1