Vytal: browser extension to spoof your location and user agent
Vytal is an open source browser extension for Google Chrome and other Chromium-based browsers, that will spoof the location, locale, timezone and user agent manually or automatically.
Vytal uses the chrome.debugger API, which the developer believes makes the use of the extension undetectable by websites and will spoof the data during the initial loading of webpages as well as in iframes and web workers.
One of the main ideas behind Vytal was to give VPN users a tool at hand to match location-based identifiers to the VPN's location. Sites may use scripts to find discrepancies between the VPN's location, based on the IP address, and other location data, which the browser may provide.
The Vytal extension is available in the Chrome Web Store. Just visit its profile page there and install it, just like any other Chrome extension. You may check the source code of the extension on GitHub.
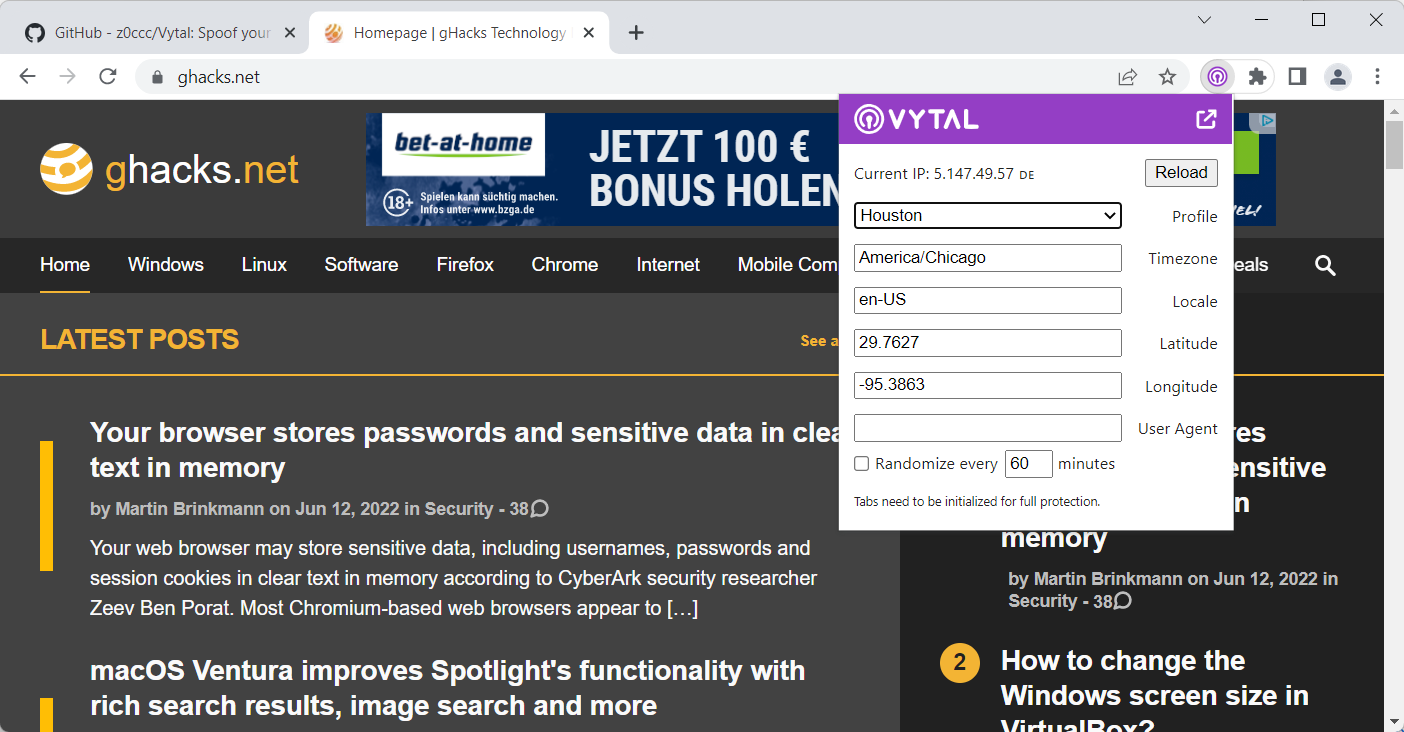
Installation adds an icon to Chrome's main toolbar that you may interact with. A click displays the available options and information about the current IP address and region. The profile menu lists dozens of regional profiles that you may apply manually, e.g., to spoof your location, timezone and locale to Houston, Jersusalem, or Bangkok.
You also find an option to match the regional settings to the active IP address; this is what VPN users may want to activate, as it automates the process of matching the VPN server location to the spoofed data of the browser. A custom option is available next to that, to enter data manually into the fields.
There is an option to randomize the data every 60 minutes, or any other period that you set the randomizer to.
Last but not least, you may also set a different user agent, but none appears to be provided, which means that you need to set it manually.
Vytal has two shortcomings that users need to be aware of. Chromium-based browsers display a "started debugging this browser" message at the top when extensions are active that use the debugging API. The notification is displayed at the top in the browser when Vytal is being used.
Chrome and other Chromium-based browsers support the command line switch --silent-debugger-extension-api, which supresses the message in the browser.
The second issue weights more heavily. There is a slight delay between opening a new tab and the start of the debugger. Sites may use this delay to retrieve information before the actual spoofing takes place. Since this is tab-based, users might get around this by loading safe sites in tabs first before loading sites that might detect spoofing this way.
The browser extension is not available for Firefox, as the browser does not support the debugging API according to the developer.
Closing Words
The browser extension Vytal may be useful to Internet users who run into location-based issues when using sites; this may affect users who are abroad on vacation or because of their job, and users who use VPN's to access content in different locations in the world.
Sites have other means to block access to content, for example, by detecting that IP addresses that are linked to a VPN service are being used.
Still, it may be worth a shot for users who can't use certain services because of their location.
Now you: do you use VPNs to spoof your location?





















@Martin: how/where does one integrate the command line switch –silent-debugger-extension-api? I am on macOS.
Sorry to have bothered you with this question, Martin. I found a solution:
https://wpguru.co.uk/2016/11/how-to-launch-a-mac-app-with-command-line-parameters-from-the-dock/
I don’t use Mac Os, but these pages may help:
https://stackoverflow.com/questions/29510815/how-to-pass-command-line-arguments-to-a-program-run-with-the-open-command
https://www.chromium.org/developers/how-tos/run-chromium-with-flags/
There is “Location Guard” for Firefox, isn’t this similar to described here?
From the description, it appears that it is only protecting against a very specific JavaScript feature to look up the location of a user. It is limited in comparison.