Firefox 82.0.3, Firefox 78.4.1 and Thunderbird 78.4.2 patch a critical security issue
Mozilla has released new stable versions of the Firefox web browser and the team behind the Thunderbird email client has released a new stable version to address a critical security vulnerability.
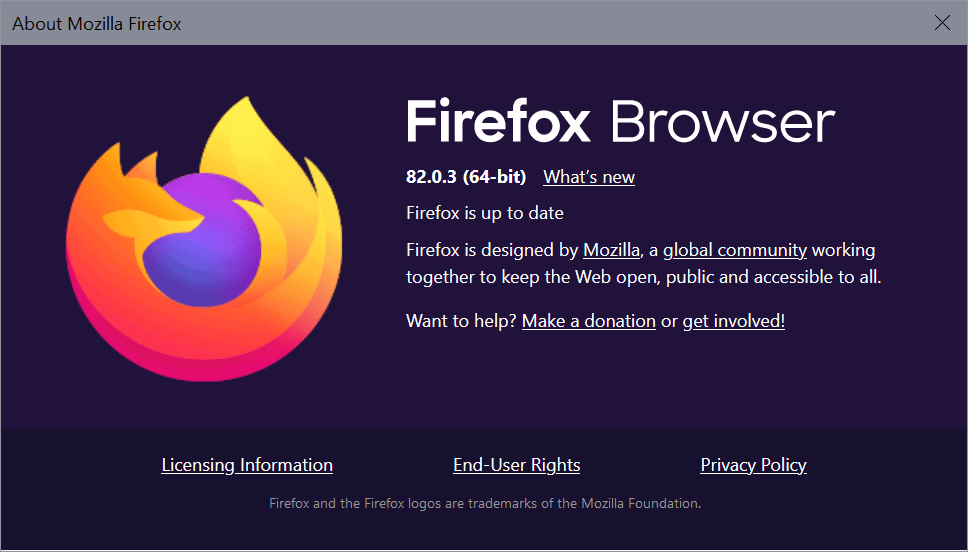
Firefox 82.0.3 and Firefox 78.4.1 ESR are already available. Firefox users may select Menu > Help > About Firefox to run a manual check for updates to download and install the new version automatically.
Thunderbird users may select Help > About Thunderbird in the client to get the new version downloaded and installed. Both menus display the current version that is installed on the system, which can be used to verify that the update is installed.
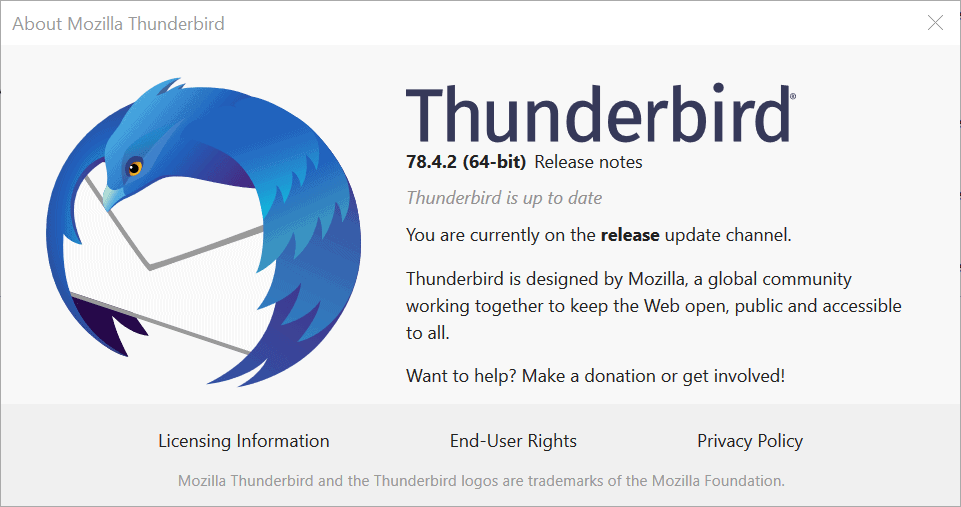
The Firefox 82.0.3 release notes and the Thunderbird 78.4.2 release notes list a security fix as the only change in the release. Both link to the official Mozilla Security website.
Mozilla Foundation Security Advisory 2020-49 reveals that the security issue that is fixed in the new versions of the browser and email client has received the highest severity rating critical.
It was revealed during the Tianfu Cup 2020 International Cybersecurity Contest held on November 7 and November 8, 2020. The contest is China's version of the Pwn2Own contest featuring security speeches, demonstrations, and a wide assortment of targets to be hacked.
Among the targets were all major browsers, Microsoft Edge, Google Chrome, Apple Safari, Mozilla Firefox, as well as other popular applications such as Adobe PDF Reader, VMWare Workstation, Ubuntu, Apple's iPhone 11 Pro with iOS 14, Samsung's Galaxy S20, Windows 10 version 2004, and other systems.
The successful exploit of a vulnerability in Firefox brought the issue to Mozilla's attention. Thunderbird and Firefox share a codebase, and that is why Thunderbird is also affected by the vulnerability.
Mozilla's public description of the vulnerability:
CVE-2020-26950: Write side effects in MCallGetProperty opcode not accounted for
In certain circumstances, the MCallGetProperty opcode can be emitted with unmet assumptions resulting in an exploitable use-after-free condition.
Mozilla reacted quickly and has produced a patch to fix the issue in all current versions of the Firefox web browser and Thunderbird.
Firefox and Thunderbird users should consider updating their browsers and email clients to the new version as quickly as possible.
The next stable version of Firefox will be released on November 17, 2020.






















Meanwhile they broke policy templates… Again!
Does anyone know what does that vulnerability description mean? practically, how would it be exploited?
it’s so match take
Has there been an improvement in memory usage.?.
Are Beta versions of Firefox and Thunderbird vulnerable to the same security issue? When do those versions get updated with a security fix – with the next Beta release?
Beta, Dev and Nightly versions do get updated earlier usually.
I guess this means I’ll have to upgrade to the 7 series even though it’s going to mean my 6 series addons will stop working. :(
@ Martin,
There seems to be a problem with the display. Sentences are being cutoff without being hyphenated. Here’s a pix: https://i.postimg.cc/Pqq2Pf7V/display-words-split-in-sentences.png
It does it even if the option for sites to use their own fonts is enabled and if addons are disabled. I’m using Waterfox Classic, but I tried it using Firefox and that behaves the same way.
> TelV: “Sentences are being cutoff without being hyphenated”
Same here, as seen in Firefox. It affects the whole page, including the comments section. The embedded inline images are also badly misaligned, eg. displayed towards the right edge of the page & away from the text area. A hard-refresh of the webpage has no effect. (In any case, my browser is set to clear its cache every few minutes & also upon exit.)
Then since around 2-3 days ago, if JavaScript is enabled, every single Ghacks webpage upon being loaded will instantly freeze the browser & max out the CPU usage, thus requiring a hard kill of the browser process. Previously (& this has been happening for the past 2-3 years), it was just the Ghacks homepage that hangs the browser in the same manner. It’s not possible to see what the misbehaving script is, since the browser becomes totally frozen.
> broken words: “Also happens with Basilisk.”
Incidentally, I switched to Basilisk (using Firefox v52.9 ESR code) because of the aforementioned issues, & Ghacks’ display looks quite okay (ie. no truncated words due to unexpected carriage-returns, no display misalignments) — although the text-column width seems unnecessarily narrow (spanning just the size of my palm, with lots of wasted huge blank space on the left & right), as if catering to hand-sized mobile displays.
My Basilisk & Firefox configs & addons are identical. The only addon that I removed from Basilisk is Fireshot (a compatible version), because its JavaScript-based “advanced features” (eg. image preview & edit function) for some reason aren’t working in Basilisk, & the addon ended up in permanent “Lite Mode”.
Can you please try and load the site directly bypassing the cache? Hold down Ctrl before you click on the reload button.
Hi, I cannot reproduce this in Firefox nor in any other browser but have forwarded this to have it checked out. If you could provide exact versions of the browsers and other information, e.g. extensions or settings that may interfere, that would help as well.
Also happens with Basilisk.
Switching off styling statements in the Inspector view indicates the culprit is “word-break: break-all;”.
There’s also IMHO excessive hyphenation due to “-moz-hyphens: auto; hyphens: auto;”, but at least this doesn’t run counter to normal typesetting conventions.
Kudos to Mozilla for responding so quickly to the Tianfu finding. Credit where due.
@Martin Brinkmann: Thanks for the article. On a side note, since you added the “related content” section, the last portion of the article (i.e. closing words, summary and comments) do not get styled as before when page scripts are blocked.
Nobody updating to a newer version of Thunderbird? Come up with a “critical security issue” in older versions, then loudly, explicitly announce what it is and how to exploit it. Anymore, I trust Mozilla about as much as I trust Google.
How dare them be transparent and fix the security issue quickly.