Microsoft Security Updates October 2017 release
Microsoft released security updates for the company's Windows operating system, and other company products on the October 2017 Patch Tuesday.
Our monthly series provides you with information on Microsoft's Patch Day. It features an overview of all security and non-security updates that Microsoft released since the last Patch day in September 2017.
The monthly guide lists how different versions of Windows -- client and server -- and Microsoft's browsers Edge and Internet Explorer are affected. It features links to resources, direct download links for cumulative Windows updates, new and updated security advisories, and information on how to download the updates to Windows machines.
Microsoft Security Updates October 2017
You can download the following Excel spreadsheet if you want a list of all security updates for all Microsoft products that the company released since the September 2017 Patch Tuesday.
Click on the following link to download the basic Excel spreadsheet to your device: (Download Removed)
Click on this link to download the full (with all details) Excel spreadsheet instead: (Download Removed)
Executive Summary
- Windows 10 version 1511, the November Update, won't receive security updates anymore. Click here to open Microsoft's blog post on the topic.
- Microsoft released security patches for all versions of Windows.
- Security updates were also released for Internet Explorer, Microsoft Edge, Skype for Business and Lync, and Microsoft Office.
Operating System Distribution
- Windows 7: 20 vulnerabilities of which 5 are rated critical, 15 important
- Windows 8.1: 23 vulnerabilities of which 6 are rated critical, 17 important
- Windows 10 version 1607: 29 vulnerabilities, 6 critical, 23 important
- Windows 10 version 1703: 29 vulnerabilities of which 6 are rated critical, 23 important
Windows Server products:
- Windows Server 2008 R2: 18 vulnerabilities, of which 3 are rated critical, 15 important
- Windows Server 2012 and 2012 R2: 23 vulnerabilities, of which 6 are rated critical, and 17 important
- Windows Server 2016: 29 vulnerabilities of which 6 are rated critical, 23 important
Other Microsoft Products
- Internet Explorer 11: 5 vulnerabilities, 4 critical, 1 important
- Microsoft Edge: 16 vulnerabilities, 14 critical, 2 important
Security Updates
KB4041676 -- Windows 10 Version 1703
- Addressed issue where some UWP and Centennial apps show a gray icon and display the error message "This app can't open" on launch.
- Addressed reliability issue that causes the AppReadiness service to stop working.
- Addressed issue where applications that use the Silverlight map stack stop working.
- Addressed issue where VSync prevents devices from entering Panel Self Refresh mode, which can lead to reduced battery life.
- Addressed issue where user customizations (like pinned tiles) made to an enforced partial Start layout are lost when upgrading to Windows 10 1703.
- Addressed issue where the Universal CRT caused the linker (link.exe) to stop working for large projects.
- Addressed issue that prevents Windows Error Reporting from saving error reports in a temporary folder that is recreated with incorrect permissions. Instead, the temporary folder is inadvertently deleted.
- Addressed issue where the MSMQ performance counter (MSMQ Queue) may not populate queue instances when the server hosts a clustered MSMQ role.
- Addressed issue with the token broker where it was leaking a token that caused sessions to remain allocated after logoff.
- Addressed issue where Personal Identity Verification (PIV) smart card PINs are not cached on a per-application basis. This caused users to see the PIN prompt multiple times in a short time period; normally, the PIN prompt only displays once.
- Addressed issue where using the Cipher.exe /u tool to update Data Recovery Agent (DRA) encryption keys fails unless user certification encryption already exists on the machine.
- Addressed issue where using AppLocker to block a Modern app fails. This issue occurs only with Modern apps that come pre-installed with Windows.
- Addressed issue with form submissions in Internet Explorer.
- Addressed issue with the rendering of a graphics element in Internet Explorer.
- Addressed issue that prevents an element from receiving focus in Internet Explorer.
- Addressed issue with the docking and undocking of Internet Explorer windows.
- Addressed issue caused by a pop-up window in Internet Explorer.
- Addressed issue where a Vendor API deleted data unexpectedly.
- Addressed issue where using the Robocopy utility to copy a SharePoint document library, which is mounted as a drive letter, fails to copy files. However, in this scenario, Robocopy will copy folders successfully.
- Addressed issue where MDM USB restrictions did not disable the USB port as expected.
- Addressed issue where creating an iSCSI session on a new OS installation may result in the "Initiator instance does not exist" error when attempting to connect to a target.ressed issue where connecting to RDS applications published using Azure App Proxy fails. The error message is, “Your computer can’t connect to the Remote Desktop Gateway server. Contact your network administrator for assistanceâ€. The error can occur when the RDP cookie size limit is exceeded. This update increased the size of the RDP cookie limit.
- Addressed issue where USBHUB.SYS randomly causes memory corruption that results in random system crashes that are extremely difficult to diagnose.
- Addressed issue that affects the download of some games from the Microsoft Store during the pre-order phase. Download fails with the error code 0x80070005, and the device attempts to restart the download from the beginning.
- Addressed issue where the ServerSecurityDescriptor registry value does not migrate when you upgrade to Windows 10 1703. As a result, users might not be able to add a printer using the Citrix Print Manager service. Additionally, they might not be able to print to a client redirected printer, a Citrix universal print driver, or a network printer driver using the Citrix universal print driver.
- Security updates to Microsoft Windows Search Component, Windows kernel-mode drivers, Microsoft Graphics Component, Internet Explorer, Windows kernel, Microsoft Edge, Windows Authentication, Windows TPM, Device Guard, Windows Wireless Networking, Windows Storage and Filesystems, Microsoft Windows DNS, Microsoft Scripting Engine, Windows Server, Windows Subsystem for Linux, Microsoft JET Database Engine, and the Windows SMB Server.
KB4041691 -- Windows 10 Version 1607 and Windows Server 2016
- Addressed issue where the Universal CRT caused the linker (link.exe) to stop working for large projects.
- Addressed issue with form submissions in Internet Explorer.
- Addressed issue with rendering a graphics element in Internet Explorer.
- Addressed issue with docking and undocking Internet Explorer windows.
- Addressed issue caused by a pop-up window in Internet Explorer.
- Addressed issue where a vendor API deleted data unexpectedly.
- Addressed issue where SD propagation stops working when you manually trigger Security Descriptor propagation (SDPROP) by setting the RootDse attribute FixupInheritance to 1. After setting this attribute, SD propagation and permissions changes made on Active Directory objects don't propagate to child objects. No errors are logged.
- Addressed access violation in LSASS that occurs during startup of domain controller role conditions. A race condition causes the violation when account management calls occur while the database is refreshing internal metadata. A password reset or change is one of the management calls that may trigger this problem.
- Addressed issue where USBHUB.SYS randomly causes memory corruption that results in random system crashes that are extremely difficult to diagnose.
- Addressed issue where the ServerSecurityDescriptor registry value does not migrate when you upgrade to Windows 10 1607. As a result, users might not be able to add a printer using the Citrix Print Manager service. Additionally, they might not be able to print to a client redirected printer, a Citrix universal print driver, or a network printer driver using the Citrix universal print driver.
- Security updates to Microsoft Windows Search Component, Windows kernel-mode drivers, Microsoft Graphics Component, Internet Explorer, Windows kernel, Microsoft Edge, Windows Authentication, Windows TPM, Device Guard, Windows Wireless Networking, Windows Storage and Filesystems, Microsoft Windows DNS, Microsoft Scripting Engine, Windows Server, Microsoft JET Database Engine, and the Windows SMB Server.
KB4041689 -- Windows 10 Version 1511 -- End of Support after this update.
KB4042895 -- Windows 10 RTM
KB4041693 -- Windows 8.1 and Windows Server 2012 Monthly Rollup (see also security-only update KB4041687)
- Addressed issue with docking and undocking Internet Explorer windows.
- Addressed issue with form submissions in Internet Explorer.
- Addressed issue where Internet Explorer stops responding to a navigation request.
- Addressed issue that occurs in the WebView Control of Internet Explorer in certain scenarios.
- Addressed issue with URL encoding in Internet Explorer.
- Addressed issue that prevents an element from receiving focus in Internet Explorer.
- Addressed issue caused by a pop-up window in Internet Explorer.
- Addressed issue with the rendering of a graphics element in Internet Explorer.
- Addressed issue in Internet Explorer caused by a redirection link.
- Addressed issue where messages that should be in a non-English language display in English in Internet Explorer.
- Addressed issue where USBHUB.SYS randomly causes memory corruption that results in random system crashes that are extremely difficult to diagnose.
- Security updates to Microsoft Windows Search Component, Windows kernel-mode drivers, Microsoft Graphics Component, Internet Explorer, Windows kernel, Windows Wireless Networking, Windows Storage and Filesystems, Microsoft Windows DNS, Windows Server, Microsoft JET Database Engine, and the Windows SMB Server.
KB4041681 -- Windows 7 and Windows Server 2008 R2 Monthly Rollup (see also security-only update KB4041678)
- Addressed issue with docking and undocking Internet Explorer windows.
- Addressed issue with form submissions in Internet Explorer.
- Addressed issue with URL encoding in Internet Explorer.
- Addressed issue that prevents an element from receiving focus in Internet Explorer.
- Addressed issue with the rendering of a graphics element in Internet Explorer.
- Addressed issue where USBHUB.SYS randomly causes memory corruption that results in random system crashes that are extremely difficult to diagnose.
- Security updates to Microsoft Windows Search Component, Windows kernel-mode drivers, Microsoft Graphics Component, Internet Explorer, Windows kernel, Windows Wireless Networking, Microsoft JET Database Engine, and the Windows SMB Server.
KB4040685 -- Cumulative Security Update for Internet Explorer -- The fixes are included in the Security Monthly Quality Rollup.
KB4041671 -- Security Update for Windows Server 2008 -- Patches information disclosure vulnerability that could lead to a Kernel Address Space Layout Randomization (ASLR) bypass.
KB4041679 -- 2017-10 Security Only Quality Update for Windows Embedded 8 Standard and Windows Server 2012.
KB4041681 -- 2017-10 Security Monthly Quality Rollup for Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2
KB4041683 -- 2017-10 Security Update for Adobe Flash Player for Windows 10 Version 1607, Windows 10, Windows 8.1, Windows RT 8.1, Windows Server 2012 R2, Windows Embedded 8 Standard, and Windows Server 2012
KB4041690 -- 2017-10 Security Monthly Quality Rollup for Windows Embedded 8 Standard and Windows Server 2012
KB4041944 -- Security Update for Windows Server 2008
KB4041995 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042007 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042050 -- Security Update for Windows Server 2008
KB4042067 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042120 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042121 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042122 -- Security Update for Windows Server 2008 and Windows XP Embedded
KB4042123 -- Security Update for Windows Server 2008
KB4042723 -- Security Update for Windows Server 2008 and Windows XP Embedded
Known Issues
- After installing KB4041691, downloading updates using express installation files may fail.Workaround:
- Download updates from the Microsoft Update Catalog
- Run the following commands from an administrative command prompt:
- sc config bits start= disabled
- net stop bits
- Install the update.
- Run the following commands from an administrative command prompt:
- sc config bits start= delayed-auto
- net start bits
- After installing KB4041681, package users may see an error dialog that indicates that an application exception has occurred when closing some applications. This can affect applications that use mshtml.dll to load web content. The failure only occurs when a process is already shutting down and will not impact application functionality.
- Installing KB4034674 may change Czech and Arabic languages to English for Microsoft Edge and other applications.
- Systems with support enabled for USB Type-C Connector System Software Interface (UCSI) may experience a blue screen or stop responding with a black screen when a system shutdown is initiated (KB4041676).
- After you install KB4040685, Internet Explorer 11 package users may receive an error message that states that an application exception has occurred when some applications are closed. This can affect applications that use mshtml.dll to load web content. This problem occurs only when a process is already shutting down. It does not affect application functionality.
Security advisories and updates
ADV170012 | Vulnerability in TPM could allow Security Feature Bypass - A security vulnerability exists in certain Trusted Platform Module (TPM) chipsets. The vulnerability weakens key strength. It is important to note that this is a firmware vulnerability, and not a vulnerability in the operating system or a specific application. After you have installed software and/or firmware updates, you will need to re-enroll in any security services you are running to remediate those services.
ADV170013 | September 2017 Flash Security Update
ADV170014 | Optional Windows NTLM SSO authentication changes -- Microsoft is releasing an optional security enhancement to NT LAN Manager (NTLM), limiting which network resources various clients in the Windows 10 or the Windows Server 2016 operating systems can use NTLM Single Sign On(SSO) as an authentication method. When you deploy the new security enhancement with a Network Isolation Policy defining your organization's resources, attackers can no longer redirect a user to a malicious resource outside your organization to obtain the NTLM authentication messages.
ADV170015 | Microsoft Office Defense in Depth Update
ADV170016 -- Windows Server 2008 Defense in Depth
ADV170017 | Office Defense in Depth Update
Non-security related updates
KB4043766 -- 2017-10 Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7 on Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2
KB4043767 -- 2017-10 Quality Rollup for .NET Framework 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7 on Windows 8.1, Windows RT 8.1, and Windows Server 2012 R2
KB4043768 -- 2017-10 Quality Rollup for .NET Framework 2.0 on Windows Server 2008
KB4043769 -- 2017-10 Quality Rollup for .NET Framework 3.5, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7 on Windows Embedded 8 Standard and Windows Server 2012
KB890830 -- Windows Malicious Software Removal Tool - October 201
KB4038801 -- Update for Windows 10 Version 1607 and Windows Server 2016
- Fixed a Lock Workstation setting for smart cards.
- Fixed an issue in the Credentials Manager when saving empty passwords (system could stop working when using those credentials).
- Fixed WMI query issue where access tokens were improperly closed.
- Cloned file issue on ReFS systems.
- Fixed error STOP 0x44 in Npfs!NpFsdDirectoryControl.
- Fixed error 0x1_SysCallNum_71_nt!KiSystemServiceExitPico.
- Fixed computer losing access to its domain when MSA (Managed Service Account) renews the password automatically.
- Fixed RemoteApp issues when minimizing and restoring to full screen mode.
- Patched delay issues when accessing Office documents from remote network drives.
- Fixed user logon delay issues.
- Addressed issue where the Get-AuthenticodeSignature cmdlet does not list TimeStamperCertificate even though the file is time stamped.
- Fixed errors "Multiple Bugcheck BAD_POOL_CALLER (c2) 0000000000000007; Attempt to free pool which was already freed" and "0xCC PAGE_FAULT_IN_FREED_SPECIAL_POOL".
- Fixed Remote Desktop idle timeout warning not being displayed.
- Fixed "he user name or password is incorrect. 0x8007052e (WIN32: 1326 ERROR_LOGON_FAILURE)" in CA management console when revoking certificates associated with disabled user accounts.
- Fixed a multi-factor authentication issue on devices that use custom culture definitions.
- Addressed issue where the cluster node stops working when using async replication on very high-speed disks.
- Fixed kernel memory leak issue caused by ksecdd.sys.
- Fixed excessive memory usage issues in LSASS.
- Fixed deadlock during RDP and console logons at "Applying user profile settings".
- Fixed "get-tpm : An internal error was detected. (Exception from HRESULT: 0x80290107). At line:1 char:1" during TMP-related operations using PowerShell.
- Support for OIDC logout using federated LDPs added.
- Addressed Windows Hello CEP and CES-based certificates issue with gMSA accounts.
- RPC reliability improved.
- Fixed smart card log on issue on Remote Desktop Server.
- Fixed issue where Hibernate Once/Resume Many" cannot be enabled on Windows Server 2016 IoT with Unified Write Filter.
- Fixed error 8409: "A database error has occurred".
- Addressed issue where Windows Server 2016 domain controllers (DC) may log audit events with ID 4625 and 4776.
- Fixed "There is not enough space available on the disk to complete this operation" and "Not enough available capacity" when trying to extend a Clustered Shared Volume beyond 2 Terabyte using Disk Manager.
- Addressed issue where the Windows Internal Database (WID) on Windows Server 2016 AD FS servers fails to synchronize some settings because of a foreign key constraint
- Addressed issue where Windows Server Essentials Storage Service stops working if a tiered virtual disk is created on a storage pool that has HDD and SSD
- Addressed access violation in LSASS that occurs during the startup of the domain controller role conditions
- BitLocker.psm1 won't log passwords if logging is enabled.
KB4040724 -- Update for Windows 10 Version 1703
- Fixed performance issues or lag in Microsoft Edge after installing KB4038788.
- Reliability improvements and fixes for cellular connectivity.
KB4036479 -- Update for Windows 8.1 and Windows Server 2012 R2 -- Eliminate restarts in virtual machine initial configuration in Windows Server 2012 R2
Microsoft Office Updates
Microsoft Office 2016
- Access 2016 October 3, 2017, update for Access 2016 (KB4011142)
- Excel 2016 October 3, 2017, update for Excel 2016 (KB4011166)
- Office 2016 Description of the security update for Office 2016: October 10, 2017 (KB4011185)
- Office 2016 Description of the security update for Office 2016: October 10, 2017 (KB2920723)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011167)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011139)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011135)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011036)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011144)
- Office 2016 October 3, 2017, update for Office 2016 (KB4011158)
- Outlook 2016 Description of the security update for Outlook 2016: October 10, 2017 (KB4011162)
- PowerPoint 2016 October 3, 2017, update for PowerPoint 2016 (KB4011164)
- Project 2016 October 3, 2017, update for Project 2016 (KB4011141)
- Skype for Business 2016 Description of the security update for Skype for Business 2016: October 10, 2017 (KB4011159)
- Visio 2016 October 3, 2017, update for Visio 2016 (KB4011136)
- Word 2016 October 3, 2017, update for Word 2016 (KB4011140)
- Word 2016 Description of the security update for Word 2016: October 10, 2017 (KB4011222)
Microsoft Office 2013
- Access 2013 October 3, 2017, update for Access 2013 (KB3172543)
- Excel 2013 October 3, 2017, update for Excel 2013 (KB4011181)
- Office 2013 Description of the security update for Office 2013: October 10, 2017 (KB3172524)
- Office 2013 Description of the security update for Office 2013: October 10, 2017 (KB3172531)
- Office 2013 October 3, 2017, update for Office 2013 (KB4011148)
- Office 2013 October 3, 2017, update for Office 2013 (KB4011169)
- Outlook 2013 Description of the security update for Outlook 2013: October 10, 2017 (KB4011178)
- Project 2013 October 3, 2017, update for Project 2013 (KB4011156)
- Skype for Business 2015 (Lync 2013) Description of the security update for Skype for Business 2015 (Lync 2013): October 10, 2017 (KB4011179)
- Visio 2013 October 3, 2017, update for Visio 2013 (KB4011149)
- Word 2013 Description of the security update for Word 2013: October 10, 2017 (KB4011232)
- Word 2013 October 3, 2017, update for Word 2013 (KB4011150)
Office 2010
- Office 2010 Description of the security update for Office 2010: October 10, 2017 (KB2553338)
- Office 2010 Description of the security update for Office 2010: October 10, 2017 (KB2837599)
- Office 2010 Description of the security update for Office 2010: October 10, 2017 (KB3213627)
- Outlook 2010 Description of the security update for Outlook 2010: October 10, 2017 (KB4011196)
- Word 2010 Description of the security update for Word 2010: October 10, 2017 (KB3213630)
Office 2007
- Office Compatibility Pack Description of the security update for Office Compatibility Pack: October 10, 2017 (KB3213647)
- Word 2007 Description of the security update for Word 2007: October 10, 2017 (KB3213648)
- Word Viewer Description of the security update for Word Viewer: October 10, 2017 (KB4011236)
SharePoint Server 2016
- Office Online Server Description of the security update for Office Online Server: October 10, 2017 (KB3213659)
- SharePoint Server 2016 Description of the security update for SharePoint Enterprise Server 2016: October 10, 2017 (KB4011217)
- SharePoint Server 2016 October 10, 2017, update for SharePoint Server 2016 (KB4011161)
SharePoint Server 2013, Project Server 2013, and SharePoint Foundation 2013
- Office Web Apps Server 2013 Description of the security update for Office Web Apps Server 2013: October 10, 2017 (KB4011231)
- Project Server 2013 October 10, 2017, update for Project Server 2013 (KB4011182)
- Project Server 2013 October 10, 2017, cumulative update for Project Server 2013 (KB4011175)
- SharePoint Enterprise Server 2013 October 10, 2017, cumulative update for SharePoint Enterprise Server 2013 (KB4011177)
- SharePoint Enterprise Server 2013 Description of the security update for SharePoint Enterprise Server 2013: October 10, 2017 (KB4011170)
- SharePoint Foundation 2013 Description of the security update for SharePoint Foundation 2013: October 10, 2017 (KB4011180)
- SharePoint Foundation 2013 October 10, 2017, update for SharePoint Foundation 2013 (KB4011183)
- SharePoint Foundation 2013 October 10, 2017, cumulative update for SharePoint Foundation 2013 (KB4011173)
- Word Automation Services for SharePoint Server 2013 Description of the security update for Word Automation Services for SharePoint Server 2013: October 10, 2017 (KB4011068)
SharePoint Server 2010
- Project Server 2010 October 10, 2017, cumulative update for Project Server 2010 (KB4011192)
- SharePoint Server 2010 October 10, 2017, cumulative update for SharePoint Server 2010 (KB4011195)
- SharePoint Server 2010 Office Web Apps Description of the security update for SharePoint Server 2010 Office Web Apps: October 10, 2017 (KB4011194)
- Word Automation Services for SharePoint Server 2010 Description of the security update for Word Automation Services for SharePoint Server 2010: October 10, 2017 (KB3213623)
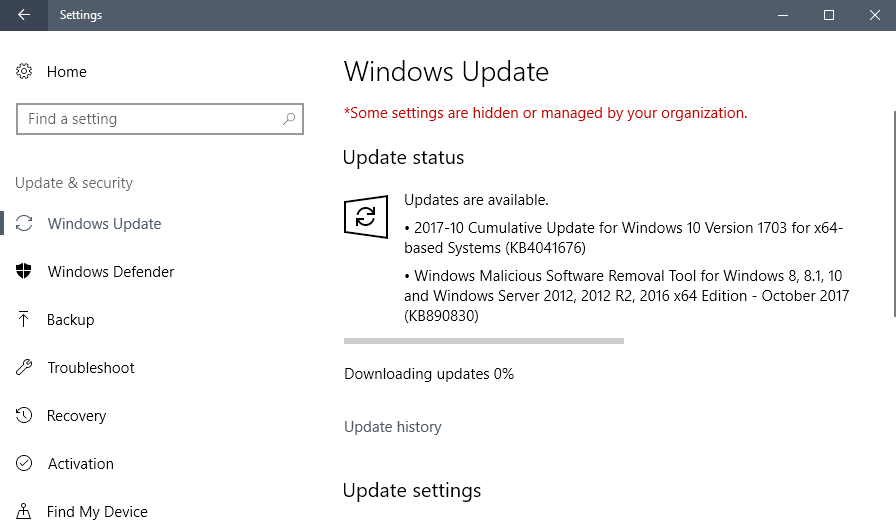
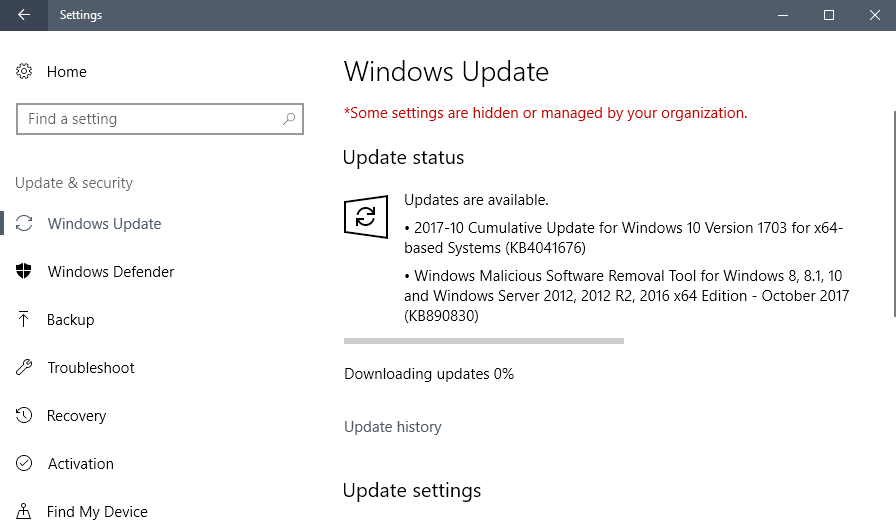
How to download and install the October 2017 security updates
The October 2017 security updates are made available via Windows Updates. All client versions of Windows are configured to check for and download important updates automatically.
This is not a real-time check though, and you may run a manual check for updates to get the updates earlier.
As always, create a backup before you update so that you can restore the system to a pre-update state if things go wrong.
- Tap on the Windows-key, type windows update, and select the result from the list of items Windows displays.
- Select "check for updates" if Windows Update does not check for updates automatically on the page.
- Select the updates you want to download if updates that are found are not downloaded automatically.
You may download the cumulative updates for Windows 10, Windows 8.1 and Windows 7 from Microsoft's Update Catalog website as well. Direct download links are listed below.
Direct update downloads
Windows 7 SP1 and Windows Server 2008 R2 SP
- KB4041681-- 2017-10 Security Monthly Quality Rollup for Windows 7 for x86-based Systems
- KB4041678 -- 2017-10 Security Only Quality Update for Windows Embedded Standard 7 for x64-based Systems
Windows 8.1 and Windows Server 2012 R2
- KB4041693 -- 2017-10 Security Monthly Quality Rollup for Windows 8.1 for x86-based Systems
- KB4041687 -- 2017-10 Security Only Quality Update for Windows 8.1 for x86-based Systems
Windows 10 and Windows Server 2016 (version 1607)
- KB4041691-- 2017-10Â Cumulative Update for Windows 10 Version 1607 and Windows Server 2016
Windows 10 and Windows Server 2016 (version 1703)
- KB4041676 -- 2017-10 Cumulative Update for Windows 10 Version 1703
Additional resources





















https://www.ghacks.net/2017/10/10/microsoft-security-updates-october-2017-release/#comment-4250010
I has had the same problem and KB4019990 was installed. I don’t know , may there is
a special microsoftlike procedure but a shortcut microsoft obvious wanting:
Install NET Framework4.7, automatic deinstall NET Framework4.5.2.
After,
KB4043766 — 2017-10 Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7 on Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2
is up.
MS jet driver updates in this version cause excel driver to no longer select any data and returns empty values…
Yup. Luckily we have a couple of C# programs using Jet and XLS files that are only run on a couple of PCs. The update, Jet and XLSX files work fine. For the time being the rollup KB has been removed from a couple of PCs.
Interestingly, if you open up a XLS file in EXCEL, keep it open and run a .NET (C#) program that opens the same XLS, the program runs fines.
I had (very small) hopes that if you opened up a XLS in Excel over a network and started up one the programs on another PC grabbing the same XLS, that it would work. Unfortunately it did not work, but I never really expected it to.
I also ran into issues with excel oledb driver on many machines after this update
Get KB4041681 on Windows7 but not the Update for .NET Framework
KB4043766 — 2017-10 Quality Rollup for .NET Framework 3.5.1, 4.5.2, 4.6, 4.6.1, 4.6.2, 4.7 on Windows Embedded Standard 7, Windows 7, and Windows Server 2008 R2
https://support.microsoft.com/kb/4043766
What’s the reason for?
Maybe a missing component? > Important: All updates for .NET Framework 4.6, 4.6.1, 4.6.2, and 4.7 require the D3 Compiler to be installed. We recommend that you install the included D3 Compiler before applying this update. For more information about the D3 Compiler, see KB 4019990.
Martin – can you tell me if this was included in the update? Thanks!
ISSUE
After installing the August 8, 2017, update for Word 2016 (KB3213656) or the September 5, 2017, update for Word 2016 (KB4011039), you may encounter the following issues:
If you merge vertical cells in a table, the cell content disappears, and you can’t select the merged cell.
If you open an existing document that has a table with merged cells, the cells will appear to be blank.
This issue occurs only for those who receive Office 2016 updates using Windows Installer technology (MSI). If you have a Click-to-Run edition of Office, such as Office 365 Personal, you won’t encounter this issue.
WORKAROUND
As a workaround, you can uninstall both KBs and your tables will return to normal. We anticipate releasing the fix for this issue in the next monthly update, tentatively scheduled for October 3, 2017.
It was fixed on October 3, 2017.
https://support.microsoft.com/en-us/help/4011039/september-5-2017-update-for-word-2016-kb4011039
KB4011140 replaced that broken update.
https://support.microsoft.com/en-us/help/4011140/october-3-2017-update-for-word-2016-kb4011140
Is is interesting to me on Windows 10 x64 Home latest CU update, M$ chose to not add a new Flash feature to Edge and IE11 – per
http://get.adobe.com/flashplayer/about/ they remain at version 27.0.0.130.
The latest Opera and Chrome x64 beta run Flash at 27.0.0.159 .
Now the latest Flash update for Chrome 64 beta and latest Opera stable is Flash 27.0.0.170 . Windows 10 x64 CU Flash re EDGE and IE11 remain back level at 27.0.0.130 . Perhaps Microsoft will update them in the FCU?
At 13:05 EDT Windows Update made available the Flash version 27.0.0.170 for Edge and IE11 with KB4049179. This is prior to any offer to install the FCU.
Microsoft has contacted some of their larger EA customers and told them to not install the October 2017 windows 10 updates as they may cause the system to no longer boot.
Yep I confirm ! Some of our computers can’t boot after the update !
Exemple: https://www.reddit.com/r/sysadmin/comments/75o0oq/windows_security_updates_broke_30_of_our_machines/
Thanks for the spreadsheet. Is this something you created or got from somewhere else? It’s very handy. Hope you keep doing it!
Martin, you didn’t mention the updates for NET Framework: https://support.microsoft.com/en-us/help/4043767/october-2017-security-and-quality-rollup-for-net-framework-3-5-4-5-2-4
Thanks. Microsoft is often a tad slow when it comes to publishing all update information. I edit the guide.
October 2016 – October 2017 Windows 7 Windows Updates : none processed, and I’ll keep it that way as long as I remain using Windows 7, avoiding the mess.
2017-10 Cumulative Update for Windows 10 Version 1703 for x64-based Systems (KB4041676) won’t install and then uninstalls itself and screws up my computer. Any ideas how to fix this?
You correctly mention KB4041676 for Windows 10 x64 CU, but there is no mention of KB890830 re the Malicious Software Removal Tool, nor the two update levels of KB2267602 for Defender also installed on my PC today in the Patch Tuesday Update. If this omission is intentional, why so?
To avoid all this nonsense, just disable automatic updates and run WSUS and get the security updates without the rollup telemetry.
http://download.wsusoffline.net/
Careful. A friend and I use WSUS Offline Update with the Security Updates Only option selected on our Windows 7 systems, and a couple of Patch Tuesdays ago we both noticed that a bunch of telemetry and diagnostics features had been re-enabled after the “security-only” updates had been applied. It didn’t happen the following month, but still, it doesn’t inspire confidence in Microsoft’s definition of “security only.” Now we have added an additional step to our updating routine, namely, to run WPD (a privacy utility) after each month’s “security-only” patches have been applied.
@www.com:
In WPD I just disable all the telemetry and diagnostics that WPD targets, and I apply the Firewall block list. I don’t think I’ve run into any problems with the block list so far. (I run Windows 7, and I seem to recall that WPD is the only privacy tool Martin mentioned that supports 7 rather than just 10, or 8/8.1/10.)
Yeah, when my “security only” patches from a few Patch Tuesdays ago — applied via WSUS Offline Update, but still from Microsoft — re-enabled a bunch of telemetry and diagnostics, I may have been only half surprised but I was fully pissed off. You see, it turns out that a couple/few months before Windows 10 was released, a rogue Microsoft “Windows 10 readiness” diagnostics update started running every night on my laptop, starting in the wee hours of the morning. When I investigated, I figured out that it had been pegging out one core of the CPU at 100% and running the fan at full speed for hours at a time. Unfortunately, by the time I realized what was going on, it had already completely melted the thermal compound between the CPU and the heatsink and burned out the ventilation fan, requiring hours of painstaking surgery to repair, not to mention the cost and shipping delay of parts and supplies. It was actually my friend (who also sticks to “security-only” updates) who tipped me off to the more recent diagnostics re-enabling. He noticed that the fan on the computer closest to his bedroom was going into high gear for no apparent reason in the wee hours of the morning. I instantly suspected that the (then) most recent round of “security-only” updates had re-enabled telemetry and diagnostics, and sure enough, that was the case. And that’s why I’m going to continue double-checking telemetry and diagnostics after every Microsoft update — “security only” or not.
So M$ is lying about what their updates are. Color me surprised.
I still think using WSUS is the best option.
And after running WPD (https://getwpd.com/) takes care of this for you?
What settings do you use?
Addendum: It didn’t happen this month, either, but I’m still going to run WPD after every Windows “security-only” update.
Thanks again Martin, for this month October 2017 list of upgrade with I use to control my self or everything main system should install on updates is correctly and also completely installed.
Ferry useful is also the 2017-10-10 – Ms. Security updates links – 2017-10 – (October 2017) spreadsheet (.xlsx) you have given the link to (Wow 187 updates to choose from this list becomes more and more a forest by which you cant see the trees anymore (What you really need))
And maybe that I image things but are taking the updates longer than they use to do even with a faster internet connection, than a few mounts ago?
For the spreadsheet’s “forest and trees” problem, use filtering.
Thanks for the information, always appreciated.
Things always go much smoother for me when I simply download the cumulative update and install it manually.
Also wondering, do we need to install the Delta Update for Windows 10 Version 1703 for x64-based Systems (KB4041676)?
Thanks a lot !
Martin, FYI:
https://about.flipboard.com/inside-flipboard/flipboards-self-service-platform-opens-for-publishers-around-the-world/
I’ll wait for Simplix Pack to be updated so I’ll update my Win7 PC ^^ WU is completely disabled here.
I’m not familiar with Simplix Pack. Any advantages over WSUS Offline Update?
same here, ive integrate the updates with simplix script and windows 7 is running smoth. WU is a real-non needed pain
Hopefully this fixes the issue with Outlook2010 and having to create a new profile every other day.
Am I wrong, or are Windows updates are getting more and more complicated? A few years ago, updating Windows took just a few minutes more time than checking the weather. Today, the process is definitely not user friendly.
@A different Martin
AllFrTV (To register programs in real time):
http://forum-racacax.ga/viewtopic.php?f=69&t=1057
Zip files: http://racacaxtv.ga/setupl.php?type=zip
@A different Martin, ok I’ll wait here to see your progress…
Downloading from LCP using captvty: https://s1.postimg.org/115h6s9len/LCP.gif
Back from a busy weekend, with a fairly busy week ahead of me. Thanks for all the tips!
Given all the caveats in Moon Tester Tool’s description, I’m a little wary of using it to install Video DownloadHelper in Pale Moon — at least until I have used it successfully in Firefox and seen that it offers markedly better functionality than NetVideoHunter. I don’t keep unlimited versioned backups of my profiles, and if a latent problem were to crop up far down the line, it might take me more work to recover from than I’d like.
Yes, I could try using a fresh profile in Firefox and/or Pale Moon. I’m not enthusiastic about it, because I love my profiles, but it would be a good troubleshooting tool. My Google Chrome isn’t too far from plain-vanilla, and I couldn’t get the LCP video to work in that. I didn’t think to try Internet Explorer, and my IE is very close to plain-vanilla (only Flash and Java have been added — it’s now my secondary fallback browser, after Chrome). I think I’ll give IE a shot before messing with profiles in my Firefox-family browsers.
It’s going to take me a little while to check out your links and suggestions and implement them, but I’ll get back to you when I have.
Again, many thanks for the tips!
@A different Martin; about LCP particularly I read “You can watch it online from anywhere in the world”. So maybe have you an issue with your browser or something? first you should try with a fresh profile…
That’s “by design.”
In France since by all means they started the economic war.. all US companies are now considered “not user friendly” anyway.
@A different Martin
It seems you have to change your IP effectively
https://frenchtogether.com/watch-french-tv/
Or try to download the tv programs with this software: https://captvty.fr/
VDH 6.31 is compatible with Pale Moon, just install it with the add-on “Moon Tester Tool” made by Justoff: https://addons.palemoon.org/addon/moon-tester-tool/
@ Anonymous:
You’re preaching to the converted. I have a pretty good idea of what my country actually is, how its corporations behave, whom our government actually works for, and what our government and corporations do here and abroad on behalf of their true principals. As for Microsoft, I’ve been following its business practices since before the US v. Microsoft case, the outcome of which marked the death of public antitrust enforcement in the US. If it’s any consolation, I expect that when the US can no longer use its military to force other countries to sell their oil for dollars and the petrodollar sputters out, the US will sink to the ranks of former world hegemons like Spain and Britain. The downside is that I don’t expect whatever country replaces it — probably China — will behave any less rapaciously than Spain, Britain, and the US did in their day.
As for the video, while I’ve been reasonably successful at downloading streaming videos using NetVideoHunter and DownThemAll, I went ahead and installed Video DownloadHelper in Firefox, Firefox ESR, and Chrome. (It’s not compatible with Pale Moon, so I installed the recommended alternative, Complete YouTube Saver, instead.) The problem with the LCP video is that I can’t start or even detect a stream, even though the page is okayed in uBlock Origin and all domains are allowed in NoScript. (I don’t have a script-blocker installed in Chrome, since it’s my fallback for pages that are just too much hassle to get working in my “Firefox-family” browsers.) Maybe LCP doesn’t like Malwarebytes Anti-Exploit Beta or the fact that I’m streaming to a non-French IP address. I suppose I could try using a French proxy, but it’s starting to seem like an awful lot of effort at this point. ;-)
@A different Martin, Microsoft is like other major US companies, like GE in my example, on the one hand they use the NSA to spy and threaten foreign competitors etc, an army of lawyers and “lobbyists” to circumvent the laws of states, to steal the tax departments, on the other side they corrupt deputies and senators to steal public markets, to invade public school, to spy on our army etc etc, destroying our country etc. To download streams on LCP just use the addon “Video DownloadHelper”.
@ Anonymous:
I’m already familiar with the very broad strokes of the Alstom turbine sale — who opposed it, who pushed it through, and how seriously General Electric took its commitments to France afterwards — but I wouldn’t mind seeing this program. The problem is, I can’t see that LCP offers on-demand podcasts of its shows. Is it just real-time streaming, on a schedule? I’m on the US Pacific Coast.
I only offered my link because it pertained to Microsoft in France (more relevant to the blog, the article, and the comments than Alstom), not because the story is more important and definitely not because the “gotcha” journalism of Cash Investigation is a paragon of documentary excellence. Still, I have to wonder what kind of open-source expertise, customizations, and code contributions the French Ministry of Defense could have developed in-house for €120 million.
@A different Martin, better this one:
http://www.lcp.fr/emissions/droit-de-suite/285363-alstom-une-affaire-detat
@ Anonymous:
You’d probably be interested in the Cash Investigation segment on Microsoft’s contract with the French Ministry of Defense (YouTube, Cash Investigation, “Marchés publics, le grand dérapage”, starting at about 41m32s).
The latest scandal, for a majority of people, General Electric against Alstom sabotaging our energy independence with the help of the NSA was felt as a declaration of war. Not only the fault of The Clown.
I blame MacDonald, Coca-Cola, Sprite, 7up, Philips Morris, Donald Trump and myself.
Ms should change update policy for edge, it gets very few updates in current cycle, if they want to attract users towards edge, they need to release updates at a faster rate
Well, it doesn’t say anything about fixes in regards to W8.1 signing into your MSN account from a local account or otherwise.
Here are the updates for IE 11 http://www.catalog.update.microsoft.com/Search.aspx?q=kb4040685
I’m glad you posted that because the link on the summary update site at https://support.microsoft.com/en-hk/help/4040685/cumulative-security-update-for-internet-explorer opens the catalog updates for September, not October. Trust Microsoft to screw up again!
Hopefully this fixed the problem that is preventing sign in on a clean/restore of 8.1
Mine is still downloading…
I am sure it will be full of bugs… but hey, them bugs got some good protein too! :D
KB 4041676 causes ODBC connections to MS Access with linked Excel tables to fail with error:
Microsoft OLE DB Provider for ODBC Drivers error ‘80004005’
[Microsoft][ODBC Microsoft Access Driver] Unexpected error from external database driver (1)
This is beyond annoying – can’t continue development of an important project !
See also:
https://www.computerworld.com/article/3233260/microsoft-windows/excel-access-external-db-driver-errors-linked-to-this-month-s-patches.html