Microsoft: Windows 10 Bitlocker is slower, but also better
If you encrypt the hard drive of a computer running Windows 7, and then on the same computer running Windows 10, you will notice that the encryption process is faster on Windows 7.
Bitlocker is a built-in disk encryption program that you can use to encrypt data so that it cannot be accessed by third-parties. If you don't encrypt your hard drive, anyone can access the data on it even if the PC is not on.
With Bitlocker and other encryption software, this is prevented.
Side note: Bitlocker may not be as secure as it could be on Windows 10. Windows 10 seems to decrypt data on the drive during feature upgrade processes.
Reasons why Bitlocker is slower on Windows 10
In Why Bitlocker takes longer to complete the encryption in Windows 10 as compared to Windows 7, Microsoft Support Escalation Engineer Ritesh Sinha describes why Bitlocker encryption is slower on Windows 10.
The answer is a bit technical, but it boils down to improvements made to the encryption process itself, and changes that went into Bitlocker that make it somewhat of a different product than the version for Windows 7.
The big change to the encryption process itself is a new conversion mechanism that Microsoft calls Encrypt-On-Write. It ensures that all writes to disk are encrypted as soon as Bitlocker is enabled on the operating system. This works for internal drives only at the moment. Microsoft does not use the new conversion mechanism for removable drives for backwards compatibility reasons.
This change is important for data security, as you could not place important data on a drive on older versions of Windows before the Bitlocker conversion process reached 100% due to the fact that the data may not have been encrypted immediately.
The second reason for conversions to take longer on Windows 10 is that Microsoft configured the Bitlocker process to run less aggressively. This improves system performance while the encryption process is ongoing and results in a longer conversion process.
Microsoft notes that other improvements went into Bitlocker on Windows 10. These have no impact on the encryption process but may be beneficial in certain situations.
This includes support for encrypted hard drives, HDD and SSD hybrid disks, new means of administrating Bitlocker, new FIPS-compliance, or Bitlocker Network Unlock.
Closing Words
I have not seen any report on how longer the Bitlocker encryption process takes on Windows 10 compared to Windows 7.
This is obviously not that much of a problem if this is a one-time operation. So, home users may notice the extra time it takes but it is a one-time operation.
The extra time it takes to encrypt drives using Bitlocker on Windows 10 may be an issue however for system administrators who run the operation regularly on company devices.
Now You: Better data security but slower encryption, a good trade off? What's your opinion on this?
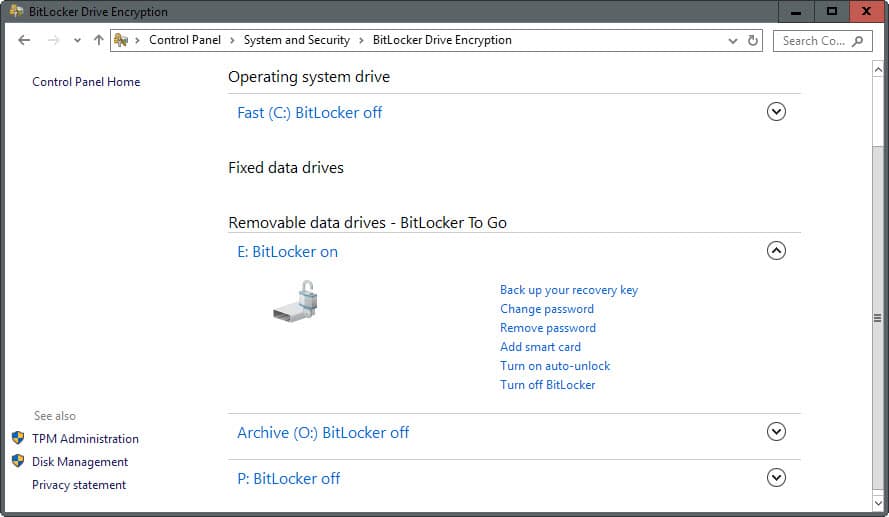




















Bitlocker does not decrypt, its designed to be an encryption algorithm. Why else would you apply it to the whole hard drive? In order to decrypt your drive you have to manually remove it in “Control Panel\All Control Panel Items\BitLocker Drive Encryption” also it should be noted Bitlocker can’t be removed from a drive wipe. A drive wipe would only erase the data on the drive not the encryption.
If you are that worried about Bitlocker’s potential, you can also install VeraCrypt on a drive encrypted with Bitlocker. This adds a double layer protection and you get the best of both worlds.
Lastly you should not install Linux or Mac or a Bitlocker drive they can’t read it, Linux can at least access a drive that has Bitlocker installed with the right app.
Windows does NOT “decrypt data on the drive during feature upgrade processes”. How can someone who writes articles like this possibly think this? Rather, Windows simply keeps the BitLocker volume unlocked (i.e. the decryption key is kept active), so that the system can reboot and update without issue. The data is still encrypted on the volume.
I think it is a poor encryption program because when upgrading to a newer build, Bit-Locker decrypts the encrypted drive!!!
Some benchmark: https://blogs.technet.microsoft.com/dubaisec/2016/03/04/bitlocker-aes-xts-new-encryption-type/
Ahh this is stats on how long it takes to encrypt the drive. I’m talking about system performance after encryption
does anyone notice any system speed loss after enabling aes-256bit encryption?
” If you don’t encrypt your hard drive, anyone can access the data on it even if the PC is not on.”
I don’t get it, Martin.
Well, anyone in theory. The date is not protected, so you could simply put the hard drive in another device, and access all files that are on it. Sorry for not making that clearer.
I’d like to add, that even if one encrypts his drive, malevolent adversaries can still access his data while he is logged on (i.e. via malware).
Full disk encryption only saves data while system is powered off or locked (and lock only saves when no physical exploit available, like for 1394 or Thunderbolt).
The main thing with Bitlocker is that it’s a matter of trust. In Microsoft. Nowadays, with Windows 10’s privacy precedent. With stupid NSA.
Bitlocker is closed source, so we’ll never see independent audits from the security community.
I’m not an open source fanatic, but trusting Bitlocker seems a bit odd to me. I don’t think there are many kinds of adversaries that lead to someone wishing full disk encryption, but being okay that it is untrustworthy.
Actually MS has been quite clever pleasing two masters – Gov and corp Windows customers – with Bitlocker. By default, BL has weak settings that Gov can brute force. Corporate customers can change those presets to good encryption, so they are happy.
There it is. See Trevor’s link. For enterprise customers who pay, Bitlocker’s code is accessible under a NDA. Although that means only strict-security companies will be able or willing to invest in doing an audit. (That shit is expensive) In that case, I would still use, as a company concerned with its data, an encryption solution that has public audits available.
Btw if you have a tendency to leave your laptop alone anywhere public, you have a bigger security problem than weak encryption :P
False, Look at Security Concerns.
https://en.wikipedia.org/wiki/BitLocker
Bitlocker is convenient and appropriate for its intended use-case; ensuring that when you leave your laptop in a taxi nobody can read your personal information.
I certainly wouldn’t trust it carrying valuable IP or when traveling somewhere like China. It isn’t strong protection against a determined skilled adversary.
Don’t forget to change the BL encryption from AES-128 to AES-256 before enabling it. Or, turn BL off, make the changes, then re-enable BL and it will encrypt to the new standard.
gpedit.msc
Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption
Enable “Choose drive encryption method and cipher strength”, set to AES-256
-> Operating System Drives
While you’re there, you can enable allowing non-alphanumerics in the password. Since the PW is max 20 chars, a good idea:
Enable “Allow enhanced PINs for startup”
Lastly, since desktops generally don’t come with a TPM, you can still allw BL to work just with your long PW:
Enable “Require additional authentication at startup” and check “Allow BitLocker without a compatible TPM”
Tim, did you compare the performance impact of turning on AES-256? Is there one?
If CPU has AES-NI, should be negligible hit for either. The only metric I have is that 4 drives operated as RAID10 under Win 8.1 storage spaces was getting 100MB/s speed copying from SSD to it before applying BL. Getting 65-70MB/s copying to the RAID10 over consumer GigE after, so hitting the network limit not the receiving drives limit.
This on Z170 chipset. Incidentally, the Intel motherboard RAID5 with 3 drives gave 10MB/s, vs 25MB/s using Win 8.1 storage spaces so I switched to RAID10 with the 4th drive. Need a RAID card for RAID5.
M$ win10 and encryption for data security sounds to me as the most extreme conceivable oxymoron