Public Internet Explorer exploit released; Fix-It available to protect your PC
A vulnerability, first announced by Microsoft on September 17, 2013, has been released to the public which may increase attacks that exploit that vulnerability significantly.
The vulnerability affects all versions of Microsoft Internet Explorer. Microsoft was aware of limited targeted attacks against Internet Explorer 8 and 9 when it released the security advisory but this situation may have changed in the meantime.
The remote code execution vulnerability may "corrupt memory in a way" that "could allow an attacker to execute arbitrary code" on the PC using the same privileges as the signed in user.
Our recommendation: Install the Fix It as soon as possible on your Windows PC, or configure Microsoft EMET so that it can mitigate the vulnerability. For details on how to do so, scroll down to the EMET configuration section of this article.
The Fix It
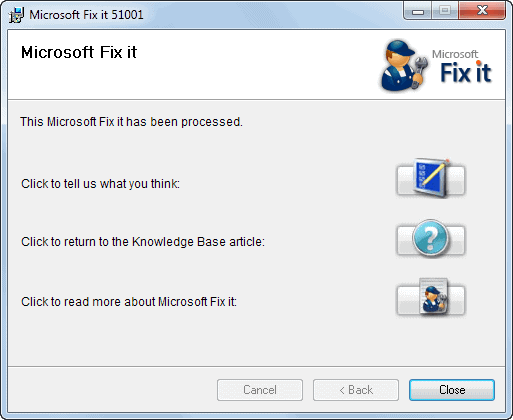
Microsoft has released a Fix It tool that patches the vulnerability on Windows PCs. This is a temporary solution as Microsoft is currently working on a patch that it will distribute via the company's Windows Update system to all users.
The main problem here is that the Fix It tool won't reach all Windows users, which means that the majority of Windows PCs will remain vulnerable to the attack until the patch is released via Windows Update by the company.
The Fix It itself requires no user interaction other than checking the license check box and clicking on next and close. The patch will be applied at once and the system is protected from the vulnerability from that moment on.
The Technet blog post provides additional details about the exploit. According to that post, it is based entirely on JavaScript and depends on the Microsoft Office DLL hxds.dll.
A Fix It to disable the protection is also provided on the same page.
EMET
Microsoft's excellent EMET program can mitigate the vulnerability as well. Microsoft has released specific configuration instructions for the software:
- Mandatory ASLR
- ROP
- Enable MemProt
- Enable Caller
- Enable SimExecFlow
- Enable StackPivot
- Heap Spray
- Find the value of HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EMET\iexplore.exe\ *\Internet Explorer\iexplore.exe
- Open HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EMET\_settings_\VALUE_FROM_STEP_1\heap_pages
- Add 0x12121212 to the list
Closing Words
It is currently not clear if Microsoft will release the patch as part of its monthly Patch Tuesday routine, or if the company needs more time to develop and test a working patch.
The next batch of security updates for Windows will be made available on October 8, 2013 by Microsoft.
Advertisement
















The IE exploit uses JavaScript and MS Office, huh? JavaScript is involved as the launch vehicle in a large majority of Internet-based attacks, I believe. Microsoft patches and anti-virus scans are reactive solutions; the better proactive approach is to disable Javascript on your browser. For secure browsing, use Firefox, and install NoScript, AdBlock, and Ghostery. For websites where JavaScript is absolutely necessary, switch to Chrome. Also, remove the Java runtime from your PC, or — if you have applications which depend on the JRE — disable it in your browsers. The best security is attained by NOT relying on reactive patches and post-hoc virus signature files, but by decreasing the exploitable attack surface your browser and PC present to the world.
Does this (and other Microsoft Fixits) have to be disabled when the patch is finally released by Microsoft or can all of the Patch Tuesday updates be applied over top of the Fixits?
Thanks!
There is usually no need to uninstall the Fix-It first.
That is what I thought but someone pointed out to me that these Fixits always have an ‘Undo the Fix’ option as well. I have never used that and applied the patches over the Fixits and I was concerned that I had been doing this wrong all this time.
Thanks for putting my mind at ease. :-)
Critical update for Internet Explorer will be on Patch Tuesday according to “https://blogs.technet.com/b/msrc/archive/2013/10/03/advance-notification-service-for-october-2013-security-bulletin-release.aspx?”
Great news, thanks!
Dear Martin, First off all I want to thank you for helping me by warning me for this threat!
Do I understand It correctly that when I have a Windows 7 with MS – IE v.10 I do not need this patch?
No, it is affecting all Internet Explorer versions, but attacks are currently only targeting IE 8 and 9. But that can change.