PayPal, Your Account Has Been Temporarily Limited!
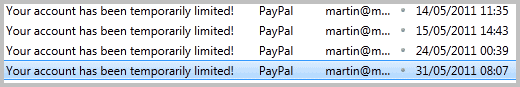
Once a week or so I receive an email from the payment processing service PayPal that notifies me that my PayPal account has been temporarily limited. When I received such a message for the first time, I went all panic for a moment thinking that PayPal - once again - would have screwed me over.
It quickly turned out however that the message was a scam, a phishing attack to steal my PayPal login credentials. Why would attackers want those information? To transfer all the money from the account, and maybe even more if a Credit Card is linked to the account.
They may use PayPal to make purchases on the Internet, or use the account as a temporary haven for illegal transactions.
Whatever it is, it is certainly not in the interest of the account owner. Lets take a closer look at one of the emails to see what it is all about, and learn how to identify if it is a phishing email.
The email reads:
Dear PayPal account holder,
PayPal is constantly working to ensure security by regularly screening the accounts in our system. We have recently determined that different computers have tried logging into your PayPal account,and multiple password failures were present before the logons.
Until we can collect secure information, your access to sensitive account features will be limited. We would like to restore your access as soon as possible, and we apologize for the inconvenience.
Download and fill out the form to resolve
the problem and then log into your account.Thanks ,
PayPal
The sender is PayPal updates-int@paypal.net, the subject: Your account has been temporarily limited. There is an attachment, a HTML page with the name Restore_your_account_PayPal.html.
When you look at the email you will notice several indicators that it is a phishing email. You do not really need to look at email headers for that.
- 1. No customer name - Phishing emails usually do not have access to customer names, which means that they will address the recipient in general terms. Dear xxx.
- 2. No contact - Companies do usually include contact information in their emails. This can be a company's street address, support phone numbers or links to web properties.
- Attachment - While it is possible that companies send attachments with their emails, it is unlikely that a company will do it in this case.
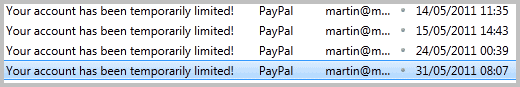
When you look at email headers you notice that the return-path and received headers do not mention PayPal but another domain (powerski.net), which more or less proves that the email at hand is a phishing email.
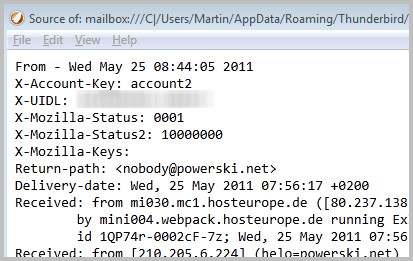
But what about the HTML email attachment? The easiest way to find out is to save it locally to open it in a text editor.
I do not really need to see the site in action, analyzing the code is all that is needed to get the information that I want.
If you double-click the HTML file in the email you will load it in your default browser locally. You will see a form and a page that resembles the PayPal site.
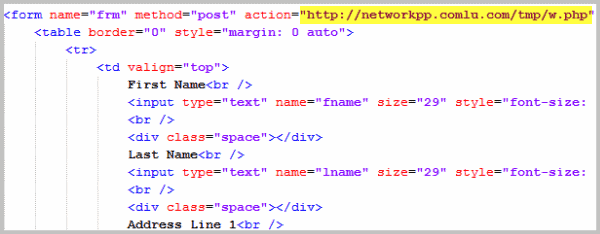
If you look at the source, you notice that the form action points to http://networkpp.comlu.com/tmp/w.php and not a PayPal domain. Form action means that your input is send to that address when you click the submit button.
The form asks for all kinds of personal and security related information, including your social security number, credit card or debit card number, expiration date, security code, mother's maiden name and email.
What can you do if you receive an email that you suspect to be a phishing email?
- Ask a tech savvy user to look at it. You can forward the email to the user for instance if necessary.
- Go to the company website manually, look for contact information and call or email support there.
- Analyze the email the way I did. All information you need can be found in the email itself.
- When in doubt do not open. Move the email to a folder for safe-keeping, or delete it outright.

















Thanks for sharing! It’s so complex, so what I am understanding is hackers? I use gmail, and never had a problem. Guess that’s how I’ll be Staying.
All anyone needs to know about the clunky PayPal:
http://forums.auctionbytes.com/vbulletin/showthread.php?p=165263
Enron / eBay / PayPal / Donahoe: Dead Men Walking.
Nice article with good info. Thanks.
I use a “private” email account for PayPal and other financial related sites and that is all that account is used for. It isn’t exposed or published anywhere. I have yet to get one of these phising emails on this account (or any other spam for that matter).
Where I do get these emails is on my public accounts. You know, the ones I list on Facebook, Yahoo, and such. When something like this shows up in one of those accounts I automatically know it is fake because PayPal, et al., have no connection to my public accounts. So far this has been 100% effective for me.
I received an email like this and immediately became suspicious – the thing I noticed was that it said something like :
please do not respond to this email it will only confuse the computer (machine?) that sent it
instead of :
Please do not reply to this email. This mailbox is not monitored and you will not receive a response. For assistance, log in to your PayPal account and click Help in the top right corner of any PayPal page.
which is what it says on other emails I’ve received form paypal.
I reported it as spam – didn’t know about the spoof@paypal.com thing – (thanks jonathan)
also – I had to look up how exactly to view the email headers in gmail
(click the arrow button next to reply and in the drop down menu select “show original”)
Never open any emails purporting to be from paypal or ebay for that matter. Instead, go directly to your account and login there. If the email was legit, whatever it was will be in your account. Paypal is the most phished brand, followed distantly by facebook.
Great advice and I agree with everything.
For me going to the company website manually
is the first thing to do if I think the email looks legitimate.
Apart from the random change in terms of service
and the notice of transactions that completed
I find emails from “PayPal” to be fake.
Like another poster(s) suggested this is exactly why I use Gmail’s verified sender option via Labs. Great feature!
i used to get these all the time, but after I began to forward them all to spoof@paypal.com, they seemed to have stopped! :) But you should always forward these messages to paypl so that they are aware of them and take steps to stop them.
It is easy to tell because it is not paypal.net, it is paypal.com
I should rephrase my comment to avoide confusion
Paypal.com is the official paypal website, not paypal.net
That’s correct, but both are PayPal properties.
If you use Gmail, Google labs has a verified id option that works with Paypal
Great tip!