Dropbox Insecure?
The article Dropbox authentication: insecure by design by Derek Newton got quite the press in the past week or so. So what exactly did he find out to come to this conclusion? Dropbox creates a config.db file in the main application data folder, a SQLite database file that can be edited with programs that can edit SQLite databases. That file is being used to identify the device to the Dropbox account. Derek's main discovery is that the file is completely portable. You can copy it to another computer, install Dropbox there and files of the original user will automatically be synchronized on that new computer without authentication whatsoever.
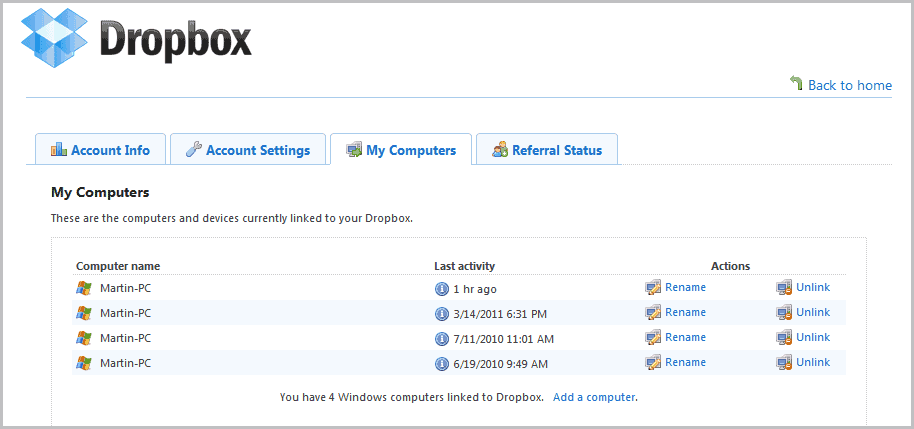
This happens completely in the background. The attacker does not have to enter the account credentials to initiate the synchronization. The original user furthermore will not be notified about the transfers, and the new device will not be added to the list of allowed devices in the Dropbox account settings.
To make matters worse, there is only one option to block the attacker from synchronizing and downloading files from the original user's Dropbox: By removing the original device from the list of authorized devices in the Dropbox account. But for that, the owner needs to know that the computer was compromised. Changing the account password does not invalidate the config.db file, it can still be used to synchronize data.
One could say that the original user has other problems if someone managed to get access to the computer, and that's definitely true. With that access, one could easily transfer data from the local Dropbox folder, access mounted True Crypt volumes or access other files like mailboxes that the user has access to.
It does not however make it less worrying that the reliance on config.db for authentication is inherently weak. One step in the right direction would be to implement safeguards, for instance by linking the file to the system it has been authorized on, and by using a notifications system to inform the user of new devices that have established a connection with the Dropbox account.
You can check for unauthorized access manually on the Dropbox website, but there is no notifications option available. And even then, the attacker's device would not appear in the list of devices.
But what about encryption? If you encrypt your Dropbox data you are safe right? Encryption is not really an option either, considering that an attacker who got local access to a computer system could very well have the means to log the decryption on the local system. And it would render the file and folder sharing on Dropbox useless.
So what is it that you can do right now? You could for instance make sure that you do not host important files on your Dropbox, and if you do, you should consider encryption as it adds another layer of protection around the Dropbox files. But as we mentioned earlier, it is not a complete safeguard.
You could also start monitoring the config.db file or try to change the rights of the file so that it cannot be accessed by standard system users.
The underlying insecurity, as rare as its exploitation may be, needs to be fixed by Dropbox. You can read Derek's article and several interesting comments on his personal website.
Advertisement
















I’m new with dropbox. but after reading this issue, i just worry with my confidential doc. Is there any alternative service like dropbox but with better security?
The security of dropbox is very important. thanks for sharing it. welcome to my website http://louisvuittonhandbagsonsale.net
What does it means “I use Dropbox not often, but I use it?
Have you installed Dropbox?
Does it run automatically when loading Windows?
If yes, then you use it ALWAYS, even if you interact with it only seldom or never.
Dropbox just answer this concern in a long blogspost detailing lots of security concerns:
http://blog.dropbox.com/?p=735
See the end of the article, saying: “The second issue involves the security of a Dropbox account on a computer that’s hacked or compromised. Unfortunately, when something like this happens, all applications and data on the computer are at risk. That said, we have developed ways to provide greater protection for Dropbox accounts on compromised computers. For example, last week’s update to the Dropbox desktop app sets more restrictive permissions on the folder that stores the authentication file, and we will soon provide a solution that will make the authentication file useless on a second computer.”
That’s great news Ronan.
You can always lock the folder where your database is stored.
Thanks for sharing this to us. I use Dropbox (not often, but I use it) and it’s good to know that there is a security hole.
It doesn’t matter how someone could get the file, there will always be a way to break into someone else system. The real problem comes from this simple file, if I get this file I can sync all the data without any authentication required, its just wrong.
By simply copying config.db inside the public dropbox folder of your victim you could track it back with a script and proceed to download it. Malware could be made with this simple task of copying the config file inside the public folder and the attacker would only have to scan through a list of public ids and request the file in question. http://www.kittybomber.com/configharvester.html
> It doesn’t matter how someone could get the file, there will always be a way to break into someone else system.
It’s like saying “there always be a way to break in any building”. Logically true but makes no practical sense (go try your bank’s vault :)
> The real problem comes from this simple file
The real problem is access to your files which implies breach of security. There is no point to complain about security in context of breached system, essentially there is no security left there.
Great article Martin :)
Keep us updated if Dropbox gives an answer to these concerns…
That is definitely a significant weakness, but I keep all of my sensitive information in an encrypted truecrypt volume
I read about this problem, too. What wondered me was that a password change had no effect. Too bad.
The problem is that none of these services intended ever to be a place to store files that need to be kept secure.
They were designed for easy picture and video storage (and the like).
So one day they wake up and see that this “cloud” thing has caught people’s attention. How do we take advantage of this they ask themselves as they are between brushing their teeth and getting their first cup of coffee?
Well – easy – let’s say we offer cloud storage, nevermind that the backbone they are using was never designed for storing files that need to be secure.
Meh – it’s worked for almost everyone else lately – screw security and if there is a breach – send an email letting your customer know that you are really really really sorry and this it won’t happen again – well at least until the next time.
Cloud = remote server = all of the security risks that are inherent with this. Find a catchy name and people forget what they are really getting.
How is this a security problem?
If you have physical access to a computer, then nothing short of a armed security guard will stop you from “breaking” into the computer.
Give me physical access to the worlds most secured Linux server and give me 5 minutes and I’ll have a root access to it.
The original article looks like coming from someone who wanted public attention.
Well the problem is that the single file can be used on other systems without authentication. Yes, someone needs access to your computer for that, and they need to know where to look for. It still stands that the file itself is not secured at all, and that is a problem.
So… If someone can access your computer he can install trojan on it. This means Windows is insecure. Windows must be fixed by Microsoft. :)
If someone has got access to your computer sufficient to just copy files away – you are finished. Yes, you can discuss relative security of the apps in more/less terms, but this is like complaining that one chair burns faster than another when house is on fire.
Of course security can be much buffed… to the point that people that use Dropbox for simplicity and convenience change their mind.
Of course Dropbox is insecure. Why the surprise?
I don’t take people seriously who pretend that privacy and security are totally different interests. If you’re not trying to secure information then you’re not trying to keep it private, and if you’re not keeping information private then you’re not keeping it secure. Uploading anything to Dropbox or any other such service is just a fancy way of failing to keep something private or secure. If you want privacy and security, hold on to what you’ve got and protected it. If you don’t, then throw your hard drives away in the trash, enjoy “the cloud”, and stop your complaining when the doing of dumb things has dumb consequences.
Yeah, notifications and manual authorisation of new devices would be great!
The config.db security issue can be voted up on Votebox:
https://www.dropbox.com/votebox/4761/add-security-measures-to-prevent-the-config-db-vulnerability
If you know the ip address of your computer, you can hover over the blue “i” icon in the Last Activity column and verify that it was your computer that was synced last. The ip address should change if someone else is syncing, and are not on your network.
Great tip Jikaido. Now if Dropbox would only add notifications that inform you asap when a new computer syncs, or implement an optional setting that a new IP on first sync requires authentication again.
Good article Martin, I have been thinking about this a lot recently in terms of securing files in the cloud. After some research I settled with SpiderOak (https://spideroak.com/download/referral/3cdc8df4c0895909847eacdf0edcac49 referal link) for super important personal files. They have a policy of encrypting the entire file and its metadata before it goes to there servers. I dont know if the client has any similar flaws as this one in dropbox though.
Do you know if dropbox have commented on when a fix for this issue might be available or if they have acknowledged its a problem?
Alec there is a thread over at the Dropbox forum http://forums.dropbox.com/topic.php?page=1&id=36146
Dropbox staff has replied with this:
“..that said, there are ways (some hinted at on this thread) that we can make it difficult (albeit not impossible) for an intruder or malicious party to gain an authentication token to your dropbox account (better guised/more complex authentication tokens, better permissions on the file system, etc). we’ll think carefully about possible security improvements (as we always do) and introduce them in newer versions of the client”.
One possible solution (for Windows OS) in my view is that, user can encrypt config.db file using Windows build in encryption provided for NTFS filesystem (which I think most people use). I once used these encryption on several folders in my older PC. When I copied those folder on my new laptop and tried to open it, I got “Access Denied” error. I tried every method I knew but failed. I think it got something to do with User SID ID or something like that (don’t know exactly what its called)
Good point, that could work