Microsoft Releases Out Of Band Security Patch
Microsoft today released a new out of band security bulletin addressing a vulnerability in ASP.NET that affects all versions of the Microsoft .Net Framework when used on Windows Server operating systems, or on client systems that run a web server from their computer.
While that excludes the majority of desktop users, it may still affect some that run web servers on their desktop systems. Those users are asked to update immediately once the patch is released.
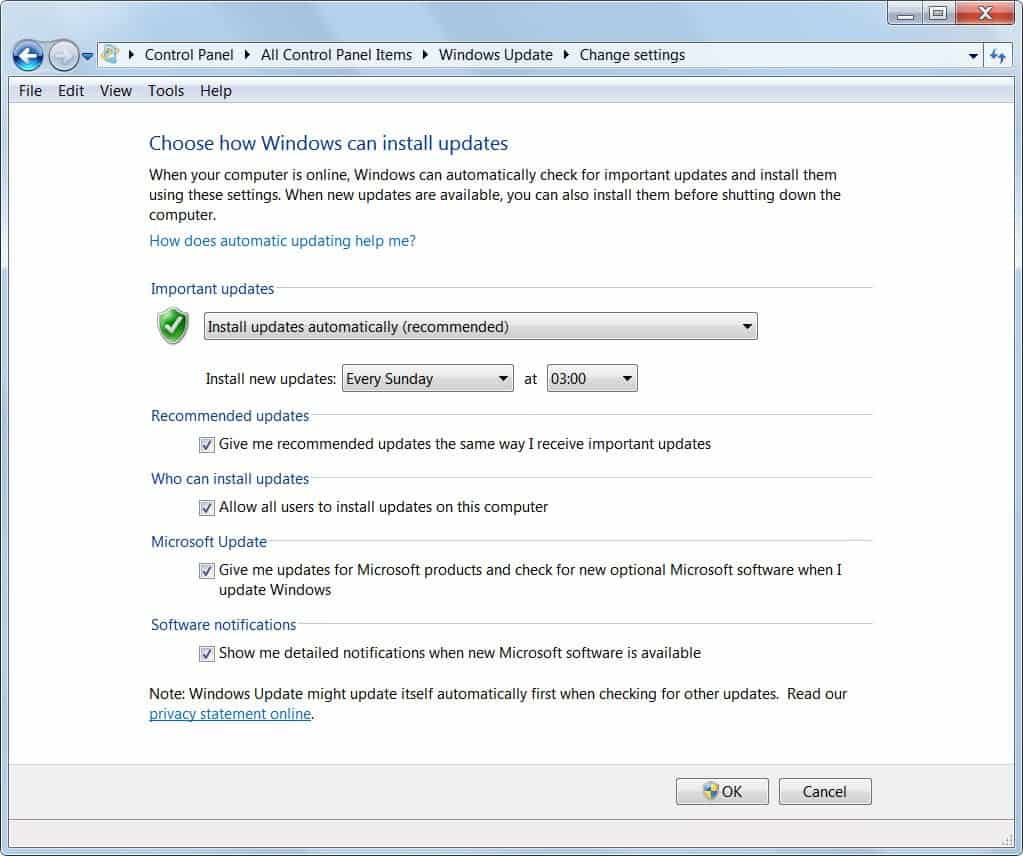
About the release: Microsoft will make the security patch available on Microsoft Download first, before it will be distributed via Windows Update. Dave Forstrom, Director, Trustworthy Computing said it will take approximately a few days before the update is released on Windows Update and Windows Server Update as well.
For now, Windows Server users and Windows client users running a web server should monitor Microsoft's Download Center for the patch, which will be made available there later today.
Admins who want additional information can take a closer look at the Microsoft Security Bulletin, which lists the affected operating systems, the maximum security impact and additional information about the vulnerability.
This security update resolves a publicly disclosed vulnerability in ASP.NET. The vulnerability could allow information disclosure. An attacker who successfully exploited this vulnerability could read data, such as the view state, which was encrypted by the server. This vulnerability can also be used for data tampering, which, if successfully exploited, could be used to decrypt and tamper with the data encrypted by the server. Microsoft .NET Framework versions prior to Microsoft .NET Framework 3.5 Service Pack 1 are not affected by the file content disclosure portion of this vulnerability.
This security update is rated Important for all supported editions of ASP.NET except Microsoft .NET Framework 1.0 Service Pack 3. For more information, see the subsection, Affected and Non-Affected Software, in this section.
The security update addresses the vulnerability by additionally signing all data that is encrypted by ASP.NET. For more information about the vulnerability, see the Frequently Asked Questions (FAQ) subsection for the specific vulnerability entry under the next section, Vulnerability Information.
Windows client users who are not running a web server are not affected by the vulnerability. Some may want to consider installing the update nevertheless.
Advertisement