Improve Windows Security By Closing Open Ports
A standard Windows operating system installation has a number of ports open right after installation. Some of the ports are needed for the system to function properly, while others may be used by specific programs or features that only some users may require.
These ports can pose a security risk as every open port on a system may be used as an entry point by attackers. If that port is not needed for functionality, it is recommended to close it to block any attacks targeting it.
A port allows communication to or from the device basically. Characteristics of it are a port number, an IP address and a protocol type.
This article will give you the tools at hand to identify and evaluate the open ports on your Windows system to make decisions in the end whether to keep them open or close them for good.
Software programs and tools that we will use:
- CurrPorts: Available for 32-bit and 64-bit editions of Windows. It is a port monitor that displays all open ports on a computer system. We will use it to identify the ports and the programs that are using them.
- Windows Task Manager: Also used to identify the programs and link some ports to programs.
- Search Engine: Searching for port information is necessary for some ports that cannot be identified that easily.
It would be an impossible task to go through all of the ports that are open, we will therefore use a few examples so that you understand how to check for open ports and find out whether they are required or not.
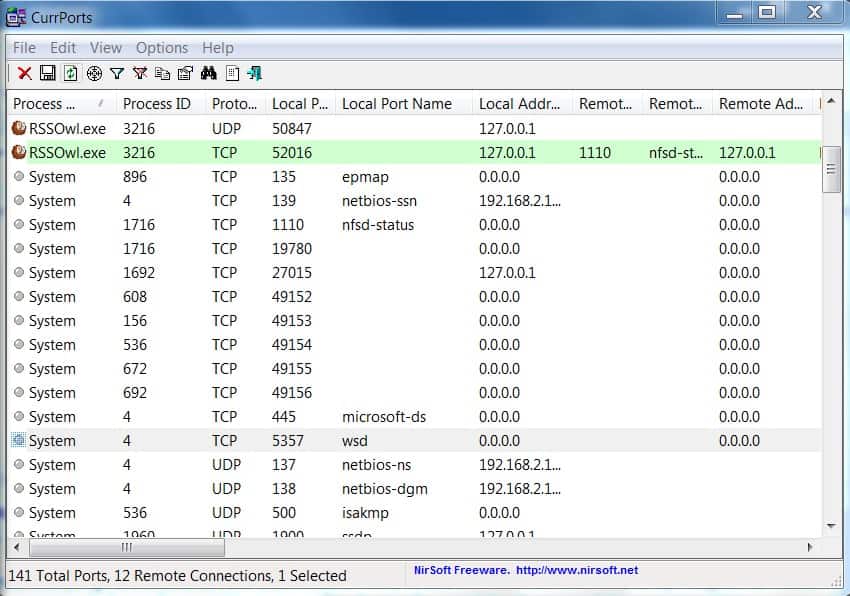
Fire up CurrPorts and take a look at the populated main area.
The program displays the process name and ID, local port, protocol and local port name among others.
The easiest ports to identify are those with a process name that corresponds to a running program like RSSOwl.exe with the process ID 3216 in the above example. The process is listing on the local ports 50847 and 52016. Those ports are usually closed when the program closes. You can verify that by terminating a program and refreshing the list of open ports in CurrPorts.
The more important ports are the ones that cannot be linked to a program right away like the System ports shown on the screenshot.
There are a few ways to identify the services and programs linked to those ports. There are other indicators that we can use to discover the services and applications besides the process name.
The most important information is the port number, the local port name and the process ID.
With the process ID we can take a look in the Windows Task Manager to try and link it to a process running on the system. To do that you need to start the task manager (press Ctrl Shift Esc).
Click on View, Select Columns and enable the PID (Process Identifier) to be shown. That's the process ID that is also shown in CurrPorts.
Note: If you use Windows 10, switch to the Details tab to display the information right away.
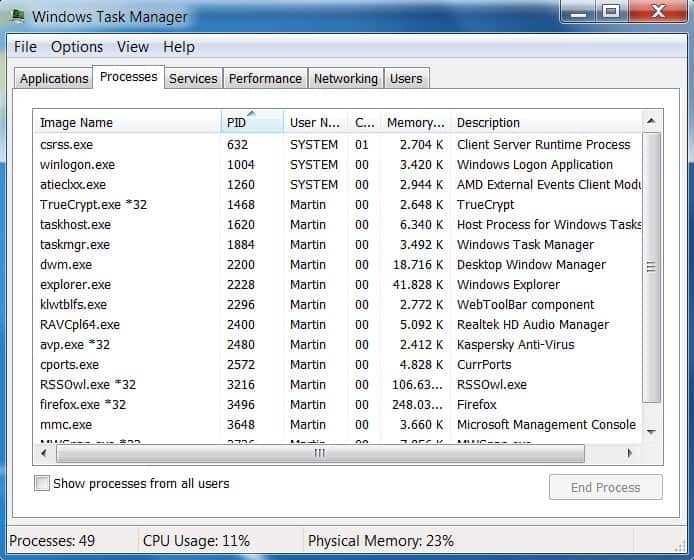
Now we can link process IDs in Currports to running processes in the Windows Task Manager.
Let us take a look at some examples:
ICSLAP, TCP Port 2869
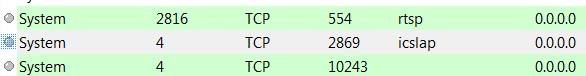
Here we have a port that we cannot identify immediately. The local port name is icslap, the port number is 2869, it uses the TCP protocol, it has the process ID 4 and the process name "system".
It is usually a good idea to search for the local port name first if it cannot be identified right away. Fire up Google and search for icslap port 2869 or something similar.
Often there are several suggestions or possibilities. For Icslap they are Internet Connection Sharing, Windows Firewall or Local Network Sharing. It took some research to find out that in this case it was used by the Windows Media Player Network Sharing Service.
A good option to find out if this is indeed the case is to stop the service if it is running and refresh the port listing to see if the port does not appear anymore. In this case it was closed after stopping the Windows Media Player Network Sharing Service.
epmap, TCP port 135
Research shows that it is linked to the dcom server process launcher. Research also shows that it is not a good idea to disable the service. It is however possible to block the port in the firewall instead of closing it completely.
llmnr, UDP port 5355
If you look in Currports your notice that the local port name llmnr uses the UDP port 5355. PC Library has information on the service. It is referring to the Link Local Multicast Name Resolution protocol which is related to the DNS service. Windows users who do not need the DNS service can disable it in the Services Manager. This closes the ports from being open on the computer system.
Recap
You start the process by running the free portable program CurrPorts. It highlights all open ports on the system. A good practice is to close all programs that are open before you run CurrPorts to limit the number of open ports to Windows processes and background applications.
You may link some ports to processes right away, but need to look up the process ID displayed by CurrPorts in the Windows Task Manager or a third-party application like Process Explorer otherwise to identify it.
Once done, you may research the process name to find out if you need it, and whether it is possible to close it if you don't require it.
Conclusion
It is not always easy to identify ports and the services or applications they are linked to. Research on search engines usually provides enough information to find out which service is responsible with ways to disable it if it not needed.
A good first approach before starting to hunt down ports would be to take a close look at all started services in the Services Manager and stop and disable those that are necessary for the system. A good starting point to evaluate those is the services configuration page on the BlackViper website.




















netstat ?
Netstat is great as it is built-in, but I prefer CurrPorts as it is easier to work with.
This is crappy advice. Why tell people to use third party tools and research third party web sites to use misinformation to make a decision? Why not reference Microsoft topics for the correct advice and direct to Microsoft endorsed tools such as tcpview from sysinternals.com?
please tell me that was sarcasm, it’s a little hard to tell
Why not reference Microsoft? Perhaps the author feels like I do… I no longer trust Microsoft — in any way, shape or form — WHATSOEVER.
That said, I use TCPView frequently and actually like it. But I think that Mark Russinovich (who coded it) is probably the only respectable MS employee currently in existence. He’s certainly far too good for them now, in their current incarnation, that’s for damned sure.
Indeed.
XP VM shows icslap open, for no apparent reason. And of course I can’t really shut down the RPC endpoint for DCOM.
Firewalls are bad–because they only cover up the true flaws, which in the case of Windows are the promiscuous opening up of the attack surface to the network, at the very least. It seems that, even now, this lesson hasn’t yet been learned, and Microsoft continues to advocate for the inappropriate solution of simply covering up the gaping holes with plaster, instead of–as one might hope–closing them.
I noticed after installing Windows 7 on two hosts on my home network that the annoying Windows Media player would ping each other incessantly with the ” icslap ” protocol. I just opened up Windows Firewall and blocked all connections involving that crap software. If i’m gonna stream something I’ll use VLC.
Nice site!
Jeff
Doesn’t a good firewall close (or block) open ports?
Sehr interessant, danke!