Malware Cause For Blue Screens After Recent Windows Update
Reports about blue screen crashes began to appear on the Internet shortly after the release of this month's security patches for the Windows operating system.
Especially Windows XP users seemed to have been affected by the crashes which were first thought to be linked to one of the updates released that month.
Microsoft addressed the issue shortly after reports began to appear, and revealed that the issues were linked to the patch MS10-015. The company did however mention at this time that it was not clear yet if the patch was the cause for the problems.
While that has not been ruled out completely the most likely cause for the BSOD after installing the updates is malware that is active on the affected computer systems.
Patrick W. Barnes found that malware was the cause of the BSOD. He first linked the infection to the Microsoft patch mentioned above by installing and uninstalling it with the help of the Windows Recovery Console.
Once the update is applied and the system rebooted, Windows will bluescreen at boot. When booted to Safe Mode, the system will freeze. Removing the update from the Windows Recovery Console or using live media will get the system booting again, at least until the update is reapplied.
He then discovered that the computer system was infected with the TDSS rootkit which infects the atapi.sys file of the operating system. The rootkit is very hard to spot and some security suites have failed until today to discover it and repair the system.
Cleaning TDSS from the computer system resulted in the computer system booting normally even after applying the security patch issued by Microsoft.
I have found that the root cause is an infection of %System32\drivers\atapi.sys, and that replacing this file with a clean version will get the system booting normally.
Microsoft's Jerry Bryant has since then confirmed in a Twitter message that malware is one cause, and that removing the malware will make the system boot without issues. He did not want to rule out other causes at that time though.
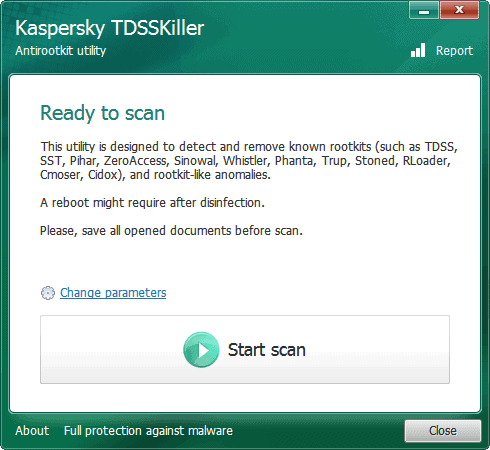
Kaspersky has created a software called TDSS Killer which we reviewed a month ago that can be used to clean the affected operating system from the TDSS rootkit.
Patrick posted repair instructions in his blog post and mentioned the atapi.sys infection may not be the only cause of the blue screen.
An atapi.sys infection may not be the only cause of this blue screen. While it does seem to be the most common cause, other infected drivers or drivers that make incorrect references to the updated kernel bits may also cause blue screens after this update is applied. Make sure you scan any computer with up-to-date antivirus software that can detect rootkits and check for updated drivers for your computer before applying this update.
Windows users who are experiencing the blue screen of death after installing the patch should scan their computer system with an antivirus software that can detect rootkits.


















It is not only XP but Vista/Win7/WHS/Servers… as well
Kaspersky has a removal tool for Tdss : Kaspersky TDSSKiller
Hi there! I own a Dell Inspirion 1520 and this has happened to me on windows xp. What steps do I need to take once in the recovery mode?? Please help and thanks. Luke
Luke just open this site https://patrickwbarnes.com/blog/2010/02/microsoft-update-kb977165-triggering-widespread-bsod/ and scroll down until you see the instructions.
Very Kind of you Martin. Thank you ever so much. Just quick also, the “administrative password” in the recovery option, bypass? Or when would it have been set etc? Is it case sensitive? It’s just I have never set one, although I do have a HD password and a log in one. If I can get past that, I may have saved my pc :)
The administrative password is an administrators password, if your user account has administrator rights then you can use that.
Ok man thanks again, I’ll give it a go and hope it works!