Data Can Leak From Partially Encrypted Systems
A bunch of researchers, among them the famous Bruce Schneier, have discovered that features like Recent Documents list may reveal information about files on an encrypted partition even when used in conjunction with the so called deniability feature which hides data in an encrypted partition.
I'm a bit puzzled that it took them so long to figure out that every kind of application that is logging or saving temporary data might reveal information about such hidden data. Maybe I got it wrong and missed something but if that is not the case I might call this finding rather obvious.
If I have a Word document on an encrypted partition and open it with Word it gets added to the recently accessed files list in Word as far as I know. The research paper has already been published and can be downloaded freely. The name of the document is "Defeating Encrypted and Deniable File Systems:
TrueCrypt v5.1a and the Case of the Tattling OS and Applications".
The research paper is well written and understandable for users with a technical background but most other users as well. What they are basically saying is that information can be found in operating systems and applications that could link to data in encrypted and hidden partitions. Some of the examples mentioned in the paper are Word auto-saves, recent files lists and Google Desktop.
The researchers are also assuming that a user would reveal the encrypted partition but not the hidden partition located inside of the encrypted partition which is plausible. An analyst would only have to find evidence for the existence of a hidden partition to defeat its purpose. That does not mean that he would be able to decrypt the data but he could gather information by analysing the operating system and the installed applications.
Advertisement


















>I don’t understand. Portable apps were not meant nor are designed to run with a central registry. Everything is supposed to be self-contained. This is one of their advantages.
Exactly because of that they fail when interaction with registry and profile folders is required. Self-contained means app stores everything to its folder. But there are setups when this is impossible like when using diskless terminal desktops.
@Rarst – I don’t understand. Portable apps were not meant nor are designed to run with a central registry. Everything is supposed to be self-contained. This is one of their advantages.
But of course, corporate people always want control of what the user is running, so they should disallow portable apps. Some companies block off the USB ports in an attempt to effect such a policy.
>Someone needs to develop an OS that doesn’t use a central registry (everything is kept in the applications install folder) so all apps are portable for the getgo AND traces are minimized in the OS.
I don’t have much love for registry myself but don’t forget it has advantages as well. I am following one blog of admin that has to work with server+terminals corporate setup and there are lots of his complains on making popular portable stuff (users ask for) run in that environment.
Registry sucks but it’s not like it can be dumped overnight.
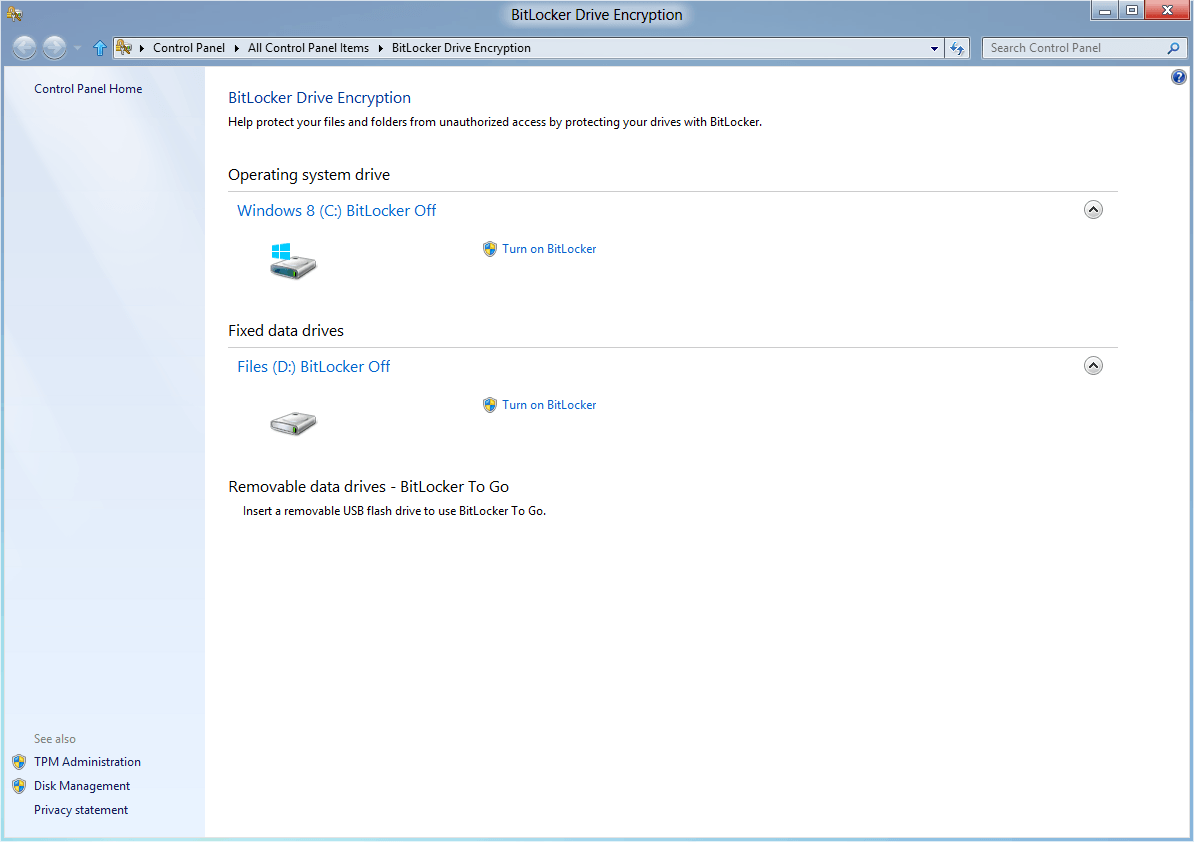
I agree that it’s common sense. Encrypting files is easy but working with them is going to create traces. In case of Windows – a lot of traces.
Trace/junk cleaners like CCleaner may or may not be enough so if person really wants to get rid of those it’s going to require a lot of tracing for all applications involved and custom cleanup routine.
Additional way to combat traces is moving temporary stuff to the RAM drive so it never reaches HDD.
Look at the abstract : we evaluate requirements of a deniable file system and see if truecrypt meets those requirements.
Thats what they have done.
I guess your question is more about you respecting academic papers and assuming that only something useful is published. YOU ARE WRONG. >95% of academic papers are “bullshit coated bullshit with bullshit fillings”(with apologies to the writers of Scrubs)
This is an example of unanticipated consequences. The application program developer thinks that there wouldn’t be any harm in traces and footprints but from papers like this, we find that there actually are.
Someone needs to develop an OS that doesn’t use a central registry (everything is kept in the applications install folder) so all apps are portable for the getgo AND traces are minimized in the OS. Don’t know if Linux does this but Microsoft would have to do a complete rewrite of the Windows OS to implement this concept.