How to detect and remove spyware
This guide will provide you with the means to detect and remove spyware that is installed on your system. Before we start we should define the term spyware. There are different categories of spyware, like adware and malware, that make it difficulty for users to distinguish between them and select the right tool for their removal.
There is a huge difference between a cookie from a website which tracks your movement on that website / network of sites and a software that permanently phones home and transmits information about the computer, the software installed and the user.
The main purpose of spyware is to track information about the user of a computer or device and submit those information to a remote server on the Internet.
Where does it come from?
Many users are baffled when they find out that spyware is installed on their system. They have no idea how it was installed and most suspect that a malicious virus or worm installed it.
There are numerous ways how spyware can make it into your system:
1. Software
Spyware can be a standalone application that a user installs on the system. The software is not labeled spyware of course and often tries to trick users. Sometimes, spyware is attached to seemingly legit programs that work really well for the purpose they have been designed for. The spyware component is running in the background then.
The second variation is more common, spyware comes bundled with software the user wants to install. Kazaa for instance has been famous for installing spyware in addition to the p2p software itself.
2. Websites
Sometimes websites prompt the user to install a component or software before the website can be viewed in the browser of choice. This can be some harmless plugin that is not installed on the users PC, like the Macromedia flash player for instance which is not spyware, or an Active X component that may install spyware on the users computer system.
Some websites use security holes to install spyware without a prompt at all making it impossible for the average user to find out where this spyware came from.
A good advice would be to use a different browser than Microsoft's Internet Explorer as it is often the target of such attacks. Its not a 100% safety measure though. You should never install something that you don't know about. Better leave the website than installing spyware on your system.
First Look
Sometimes you can tell that something is wrong with your system without using a program to verify it. It is slower than usual, you see network traffic to a site that you don't know, a new toolbar appeared in Internet Explorer or a webpage loads as the homepage that you did not choose. All of these could have the cause in spyware that was installed on your system.
You could check the task manager and have a look at the active processes of your computer and take a look at the installed software. Maybe this is enough to detect a tool that you did not install. If that is the case you might want to perform a search on the internet for the process or tool to find a solution that removes it again.
You could try to kill the process or uninstall the software but most of the time it is only a matter of time until it will appear again. It's better to fight the root of the cause.
Good tools that can help you detect spyware are Autoruns (lists all programs that are automatically started with windows), Process Explorer (better version of the process tab of the task manager, more options), Filemon (monitors file activity and shows dependencies) and finally Portmon (shows the systems open ports and applications that use them).
Second look
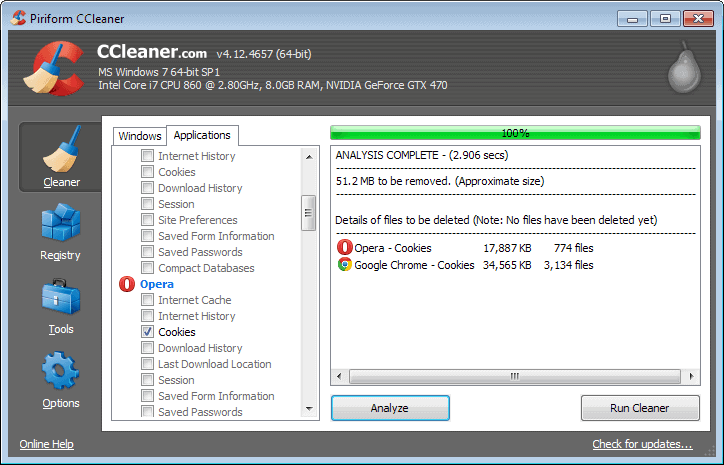
If you think that spyware might be installed on your system you should use anti-spyware tools to detect them. No tool is perfect and its wise to use more than one. I suggest ad-aware se and spybot search & destroy for a first scan of the system.
Both tools detect a variety of spyware, ranging from cookies to worms. Just run a default scan and make sure you read the instructions from the homepage and the program itself before removing detected spyware.
Browser Hijacking:
The homepage that opens when you start your browser has been changed and it was not you. If you encounter this phenomena you might be the victim of a browser hijacking. To find out if that is the case use a software like CW-Shredder or Hijackthis to remove the thread and turn things back to normal.
Safety Measures:
- Use a modern web browser like Firefox.
- Keep your system up to date. This means the operating system itself, but also the software that runs on it.
- Know what you are doing. Don´t install suspicious software. Perform a web search before installing the software.
- Keep your anti-spyware tool up to date. Perform regular scans.
- Use an anti-virus tool.
- Use a firewall.
Links that educate:
Spywareinfo.com
Top 10 tricks causing spyware epidemic
Wikipedia Spyware

















I’ve had good luck with ad aware as you mentioned above. Thanks.