Google Chrome 111 update fixes 8 security issues

Google released another security update for Chrome 111 that addresses security issues in the web browser. The new update is available for all desktop and mobile platforms.
The eight security issues have an aggregate severity rating of high, and include several use after free and out of bounds vulnerabilities. Google makes no mention of exploits in the wild, which suggests that these vulnerabilities are not exploited actively at the time of writing.
Chrome users, at least those on the desktop, may want to update the browser to the latest version immediately to protect their systems against potential exploits.
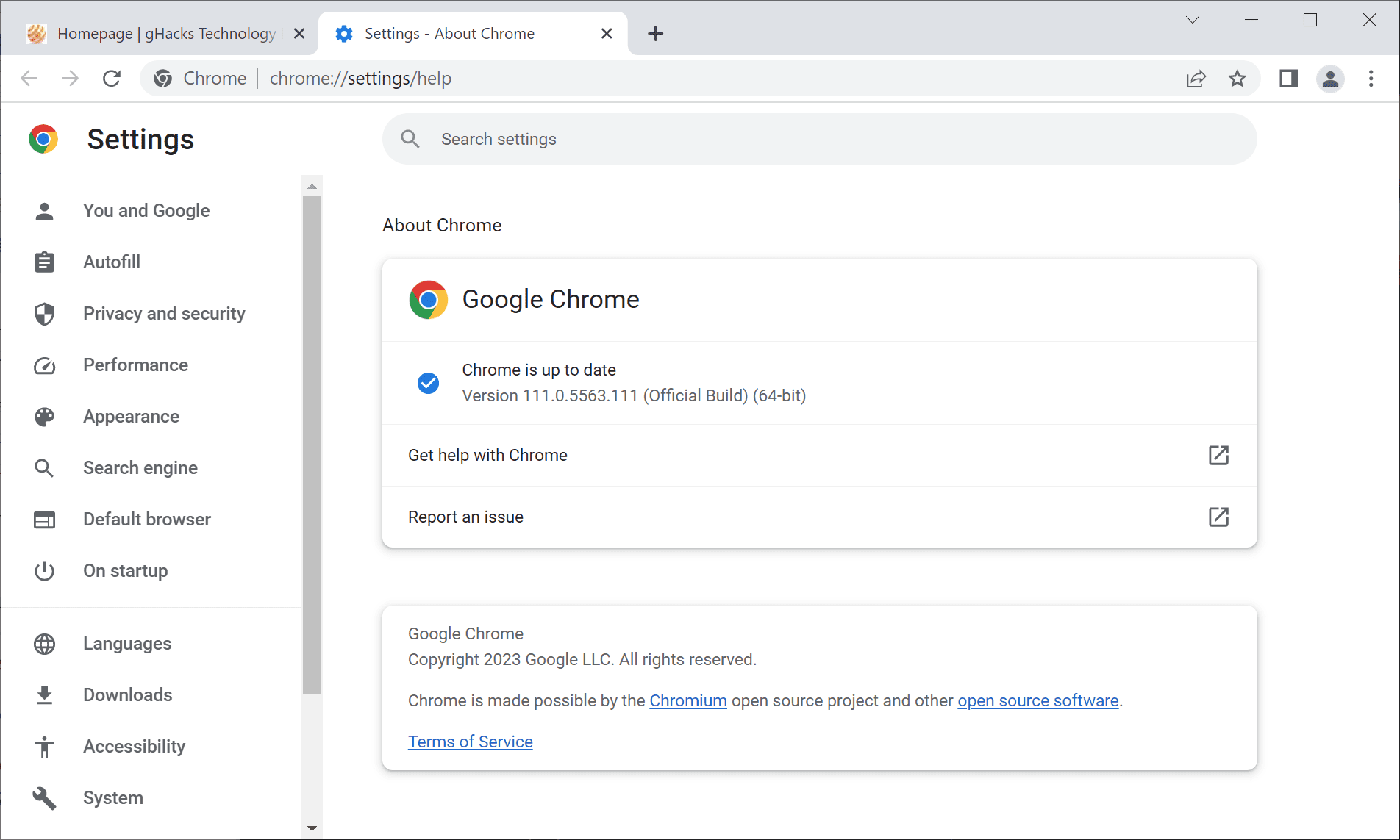
Selecting Menu > Help > About Google Chrome displays the current version of the web browser. Chrome runs a check for updates when the page is opened, and it will download and install updates when it discovers them during the scan. A restart of the web browser is required to complete the process.
The following version should be returned after the installation of the update on the device:
- Chrome for Mac 111.0.5563.110
- Chrome for Linux 111.0.5563.110
- Chrome for Windows 111.0.5563.110 or 111.0.5563.111
- Chrome Extended for Windows and Mac: 110.0.5481.208
- Chrome for Android: 111.0.5563.115 or 111.0.5563.116
Chrome 111: the security issues
Google lists seven of the eight vulnerabilities on the Chrome Releases blog. The company does not reveal security issues that it discovered internally in its release announcements.
All seven of the publicly disclosed vulnerabilities have a severity rating of high:
- [$10000][1421773] High CVE-2023-1528: Use after free in Passwords. Reported by Wan Choi of Seoul National University on 2023-03-07
- [$8000][1419718] High CVE-2023-1529: Out of bounds memory access in WebHID. Reported by anonymous on 2023-02-27
- [$7000][1419831] High CVE-2023-1530: Use after free in PDF. Reported by The UK's National Cyber Security Centre (NCSC) on 2023-02-27
- [$TBD][1415330] High CVE-2023-1531: Use after free in ANGLE. Reported by Piotr Bania of Cisco Talos on 2023-02-13
- [$NA][1421268] High CVE-2023-1532: Out of bounds read in GPU Video. Reported by Mark Brand of Google Project Zero on 2023-03-03
- [$TBD][1422183] High CVE-2023-1533: Use after free in WebProtect. Reported by Weipeng Jiang (@Krace) of VRI on 2023-03-07
- [$NA][1422594] High CVE-2023-1534: Out of bounds read in ANGLE. Reported by Jann Horn and Mark Brand of Google Project Zero on 2023-03-08
The next major version of Google Chrome will be released on March 29, 2023.




















>”resistance against exploits on part of Chromium-based browsers”
Where is this resistance against exploits? Record setting numbers of CVE’s, record setting numbers of zero-days. Doesn’t seem very resistant to my untrained eyes.
@Andy Prough
They are more resistant to exploitation by virtue of having exploit mitigations that Firefox doesn’t even include. There are CVEs assigned for existent escapes out of said exploit mitigations, those do count into the total number of CVEs as well, assuming that amateur CVE counting is a valid way of measuring security, which it isn’t.
I think we have come full circle here. So long, I think your clown makeup is now complete.
>”They are more resistant to exploitation by virtue of having exploit mitigations that Firefox doesn’t even include”
>”There are CVEs assigned for existent escapes out of said exploit mitigations”
These statements seem contradictory. It seems Google is saying something like this:
a) “We have more exploit mitigations”
b) “Our exploit mitigations have hundreds of CVEs because of our programming errors”
c) “Due to our programming errors, our browser is constantly exploited and is the favorite playground for blackhat hackers”
Whatever. Goodbye for now. I’m glad that we have a new friend, “steel buns” – I’m assuming he’s related to you? Maybe a metallurgical cousin?
always so many high rated CVEs with memory and use after free, literally hundreds per year – perhaps they should learn how to do it properly with Rust instead of just talking about it for the last five years, or focusing on hardening C++ usage
so glad I stuck with Firefox
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=chrome
– 2023 (less than 3 months): 67
– 2022: 375
– 2021: 326
https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=firefox
– 2023: ZERO
– 2022: 157
– 2021: 132
chrome and chromium will never run out of finding these bugs
Wow those are amazing statistics, steel. Clearly it is true that Firefox is vastly more secure than Chrome/chromium, and therefore is much more secure than all chromium-based browsers, like Brave.
However, Netsurf and Seamonkey have zero CVE’s since 2015 and links2 browser has zero CVE’s since 2014, so they are clearly miles ahead of Firefox or Chrome/chromium/Brave in terms of security. And Luakit has never had a CVE, so that has to be considered perfect security. madaidan should write a new blog post telling everyone to use Luakit as their web browser.
@Andy Prough
Except @madaidan does actual code analysis and not CVE counting like an amateur.
Low CVE can mean that the product is hardly attacked due to irrelevance. Firefox is far less relevant than Chromium, the other browsers listed are not on the radar at all.
CVE’s have nothing to do with the numbers of attacks, that is a silly argument. CVE’s have to do with errors made while coding which leave the browser open to attack and exploitation. Google programmers simply make far more errors than nearly all other programmers combined, and so anyone who bases their browser on Google’s code inherits all those errors.
@Andy Prough
You don’t find such errors without attacking the browser. High CVEs correlate with high popularity and consequently a high number of attacks / attack pressure. It does not immediately correlate with code quality or lack thereof.
Plus, hilariously and ironically, there are CVEs assigned for things like process / site isolation escapes. Firefox doesn’t even have site isolation. So there is a CVE assigned for an escape that’s not even necessary in Firefox as Firefox just lacks the protection entirely. Shows how stupid and amateurish CVE counting really is, but go ahead with it.
I’m pretty sure that Firefox delivered site isolation with Project Fission in December 2021, with version 95. I don’t use Firefox, so I’ll have to let you check your own version to see if you have a bunch of “fission” config options in about:config.
You may want to stop getting all your security information from 14 year old blog posts.
@Andy Prough
Artificially limiting the content processes to eight (8) is not site isolation. Different websites can still share the same content process in Firefox, by definition that’s not isolation.
Stay big mad at @madaidan, the article itself is old but what you always miss is, that it’s constantly updated. So once Mozilla fixes their mess, @madaidan will reflect it in the article. Until then, I have the privilege to look at the foam at your mouth.
Even madaidan admits that Fission is actually site isolation, he only links to some bugzilla reports to question its integrity. But someone could easily link to thousands of chromium bug reports/CVE’s/Zero-days/etc to question the integrity of the chromium implementation. The fact that he doesn’t do so only goes to strengthen the argument that he’s nothing more than a google paid shill.
@Andy Prough
> allegedly a Google paid shill
> reality: Whonix developer
> Whonix uses Tor which happens to be based on Firefox
Funny, funnier, Andy Prough. Your CVE counting is also funny, again, it does not directly correlate to code quality or a lack thereof.
Why don’t you offer your expertise to the Pale Moon forum again?
Obviously he is wise enough not to entrust the security of the users of his GNU/Linux distro with a chromium-based browser. Could have chosen Brave with its own Tor implementation, but he knows better. I should give him a lot more credit.
@Andy Prough
> Obviously he is wise enough not to entrust the security of the users of his GNU/Linux distro with a chromium-based browser. Could have chosen Brave with its own Tor implementation, but he knows better.
Actually, the reason is that Tor has a common fingerprint which is the fingerprint of a Gecko-based browser, as Tor is based on Firefox since even before Chromium existed. He can’t use a Chromium-based browser even if he wanted to, a Blink-based browser logically can’t have the same fingerprint as a Gecko-based browser, the engines are different. The common fingerprint is the reason here, not a lack of security i.e. resistance against exploits on part of Chromium-based browsers.
It’s funny how you prove that you know nothing with every single post, it’s like a clown putting on his makeup step by step. You still lack the red nose though, so I am eagerly awaiting your next reply.
@steel buns
No browser is written in Rust. Firefox is not more secure than Chromium. Most of the security issues of Firefox as described by madaidan are still not addressed. Firefox is hardly attacked as it is hardly used / irrelevant. That does not automatically make it more secure. It just means it is less attacked.
Stop spreading your misguided and laughable propaganda. It gets old.
Chrome has and always will suck period! Safari is the way to go! THE END!!
After this update, RAM consumption seems to be highter than before. :S