Improve KeePass security with this simple configuration change
KeePass, like many other password managers, relies on a primary password that protects the entire database of passwords and information. If an attacker manages to obtain that single password, all other passwords and information is unlocked.

The password manager stores its database locally, which means that users do not have to worry about server breaches that steal password vaults, like the recent LastPass incident. Some KeePass users host their password files in the cloud, which opens up the possibility of the password database being copied again through server-side attacks.
Brute force attacks are still very common when it comes to cracking encrypted password databases. Most attackers use dictionaries for that, which contain hundreds of thousands or even millions of common passwords. Real brute force attacks are expensive, as every combination of characters needs to be tested. Considering that passwords may consist of uppercase and lowercase letters, digits and symbols, this soon gets way too expensive in most cases.
Increasing KeePass security
The primary key that unlocks the KeePass database is of utmost importance. If it is weak, chance is high that a potential attacker may be able to brute force or even guess it.
KeePass users have two main options at their disposal to increase the security of the account. The first is the master password itself. Increasing the length of the password improves the security exponentially.
While that means having to memorize a new password, it is the best option to improve the security of the password database.
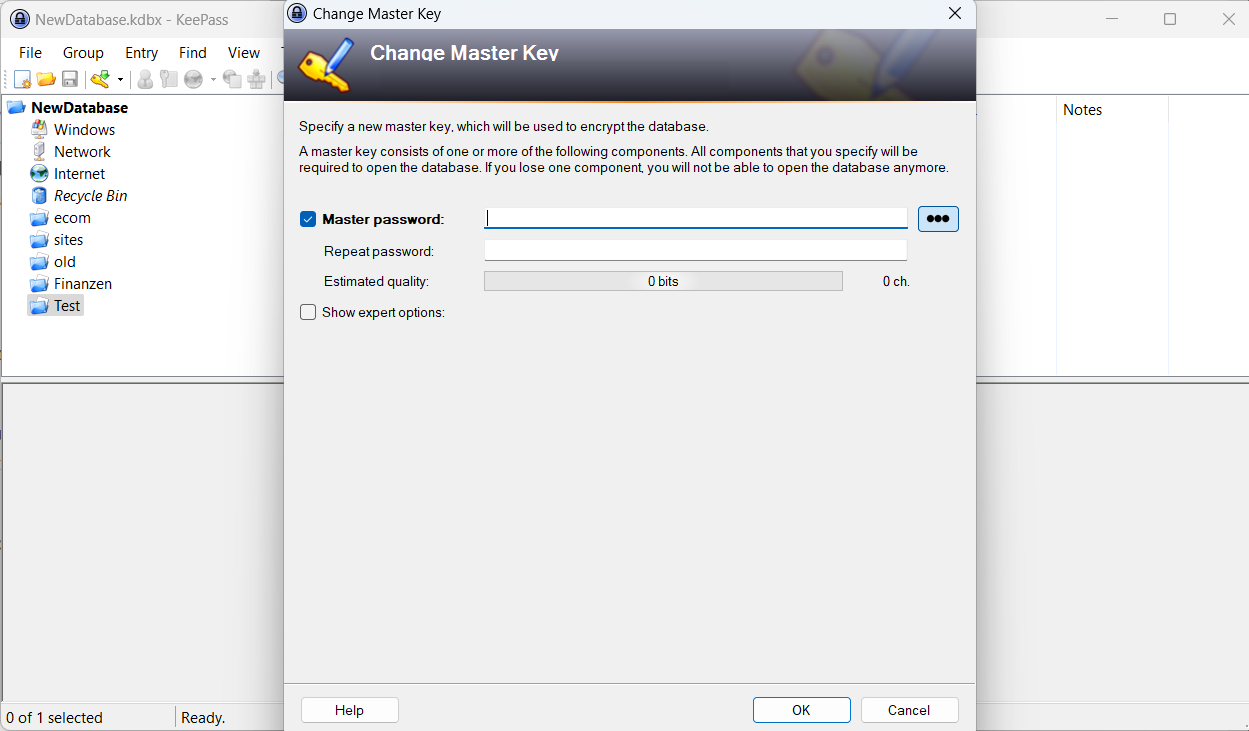
To do so in KeePass Password Safe, unlock the password database with the master password and select File > Change Master Key using the menu at the top.
Type the new primary password in the master password and repeat password field and select OK to complete the process.
Note that it needs to be longer than the old to improve security. Also, using a combination of letters, digits and symbols is recommended.
The Key Derivation settings
The second option that KeePass users have is to change the key derivation function and make changes to its number of iterations.
KeePass supports several, including Argon2d, Argon 2id and the classic AES-KDF.
If AES-KDF is selected, KeePass users may either want to increase the number of iterations from the default 60,000 to a higher value, or switch the function to Argon2d instead.
Higher iterations extend the time it takes to enter the password linear. While that may add a small delay to the user's own opening of the password database, it makes brute forcing attacks more expensive as it takes longer to test each password.
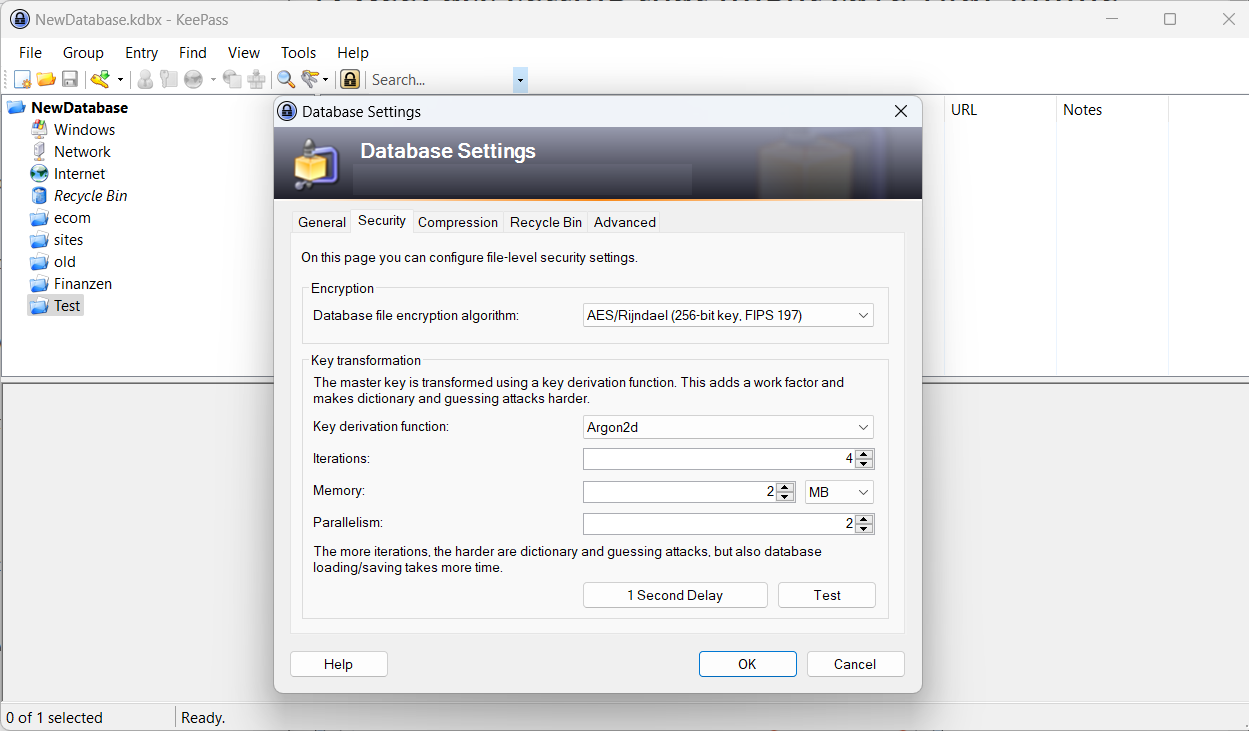
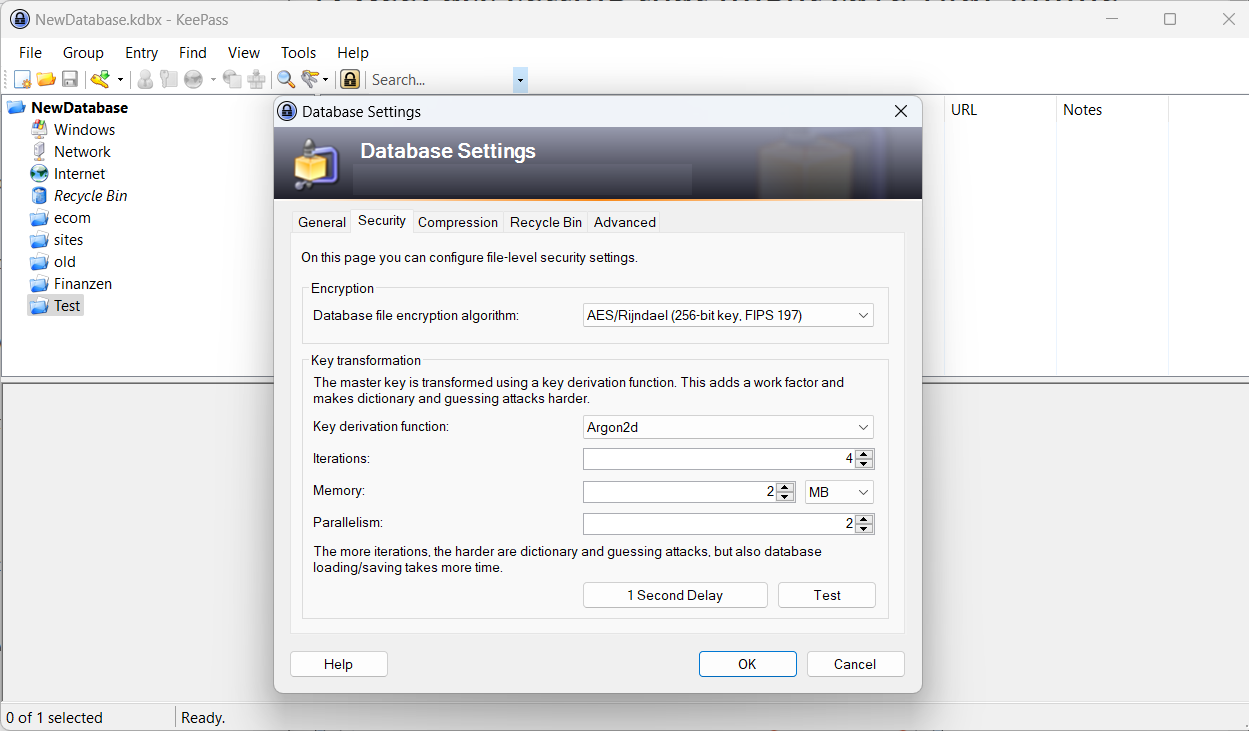
Select File > Database Setting and then Security to display the current configuration of the database that is open in KeePass.
The key derivation function lists the function that is used. AES-KDF displays just the number of iterations below, which users may want to increase to 600,000.
KeePass users may also switch to using Argon2d instead, which promises even better protection against brute force attacks.



















People who sync their database to the cloud can also increase security by using a keyfile that is NOT synced to the cloud.
Another good setting in Windows is enabling the secure desktop option is supposed to prevent keyloggers to have access to the keystrokes when you enter your master password.
Hi everyone
Memory 1 GB
Parallelism 2
How many iterations would you recommend??
Cheers
Christian
Just wanted to say thank you for this article Martin!
These esoteric tips are why I read Ghacks on a daily basis.
I have been using Keepass for years, but without this article, I would have never even known that there is an encryption for the database.
Re Database format, I went looking for an answer about whether I was using version 3 or 4. From what I can tell, if you upgraded from a version below 2.35, then you are using an old database format.
The way to upgrade it, is to change the encryption settings in this article to Argon and then it makes it into a KBDX version 4.
Source:
https://sourceforge.net/p/keepass/discussion/329220/thread/a2319df0/
Paul – 2017-05-23
The easiest is to use the KeePass version as a guide.
KeePass V2.34 or less: V3.1 database.
KeePass V2.35 upgraded from a previous V2: V3.1 database – most likely.
KeePass V2.35 and the database encryption changed to use ChaCha20 or Argon2 – File > Database Settings > Security: V4 database.
I am planing to start using KeePass in some days, and I hope that I dont find
problems, like this. Thanks for the article.
@Martin,
According to Wikipedia Argon2d introduces possible side-channel attacks. Argon2i seems to be a better option: https://en.wikipedia.org/wiki/Argon2
Argon2i makes “certain side-channel attacks slightly harder” according to the developer of KeePass. They do not appear to be a major threat on client devices, however, which is why Argon2d is the default.
https://keepass.info/help/base/security.html
For Keepass iteration use the 1second button. This increases iterations until it takes a second. For my 5 year old PC this is 24 million for KDF.
Andrew, great tip, thanks!
So if I switch to Argon2d, what are the recommended settings for these associated parameters?
– Iterations
– Memory
– Parallelism
Jojo, KeePass recommends the following:
Iterations: 2
Memory: 1GB, unless used on a device with less than 1GB of RAM, then half of that device’s RAM.
Parallelism: same as minimum number of logical processors of all devices KeePass is run on.
You may want to use the test button to find out if the wait is acceptable. If it is, you may increase the values of iterations or RAM further.
https://keepass.info/help/base/security.html
2, 1GB, 2 takes about 1.24 secs to process/open on my system. That is acceptable to me for a bit higher security.
Seems that timing I reported above is quite variable. Further repeat tests show delays in the .065 sec range on average.
My error. When I changed to try Argon2id, the 1GB memory got reset to 64MB default and I didn’t notice this. Setting it back to 1GB gives a time of around 1.1 secs.
It also recommended to always use the latest keepass database format, version 4 is the latest.
Grammar correction: “Considering that passwords may consist of uppercase and lowercase letters, digits and symbols, this soon gets way to expensive in most cases.” In this instance, use “too”, not “to”.
Where do I check the dB format?
See here if you are using the official Keepass app on Windows.
https://keepass.info/help/kb/kdbx_4.html
I’m not sure if Version 4 is default, the setting should reside in “Database -> Database Settings -> Security” for KeePassXC at least. Keepass shouldn’t be too different. For me it says the database cannot be changed, I guess downgraded since I’m already on the latest format.
Unless you have compatibility problems, V4 is superior.
Thanks and good tip regarding the database format.