Bitwarden Password Manager will add support for Argon2 KDF soon
The LastPass data breach caused uproar amongst its users and the tech community, but there are several good things that happened in the aftermath of the incident. It actually taught users a lesson in security, don't take things for granted.
It was a wake-up call for many, a rude one, yes, but it has made people think twice about their password storage methods, alternatives they can migrate to, and also to learn more about the settings that they can tweak to improve their password manager's security.
One component which gained a lot of attention was the password iterations count. Amongst other weak points in the attack, LastPass was found to have set the iterations to a low count, which is considered an insecure practice. More recently, Bitwarden users raised their voices asking the company to not make the same mistake as its rival. Bitwarden responded to their requests and has decided to increase the iterations to 600,000, as recommended by OWASP. You can set the value manually by referring to this article.
Image courtesy: Quexten/GitHub.
Let's dig a little deeper about password iterations. There are many types of Key Derivation Functions (KDFs), the most commonly used cryptographic algorithm is PBKDF2, which is the one that's recommended by the National Institute of Standards and Technology (NIST). Bcrypt is used by many websites. PBKDF2 uses SHA256 (and SHA512) for hashing and salting the passwords. The higher the number of iterations, the slower it is to run password guesses and breach a vault.
While it can be a good layer of safety, it is actually the weakest version of the KDF versions. It's not necessarily bad, but there are better ones such as Scrypt, Bcrypt, and Argon2. Argon2 is resistant to ASIC and GPU based attacks, and is considered the best of the lot.
PBKDF2 AES iterations relies on a high number of iterations to hash the passwords in an effort to deliberately slow the attacks. With 600,000 it will take a long time to brute-force a vault, and can be taxing on the CPU. Argon2 not only slows down this threat, but also consumes memory for running passes, and it also has a degree of parallelism that is determined by the number of CPU cores/threads. Let's just say it's a lot more expensive for a hacker both in terms of time and resources to attack an Argon2 encrypted database.
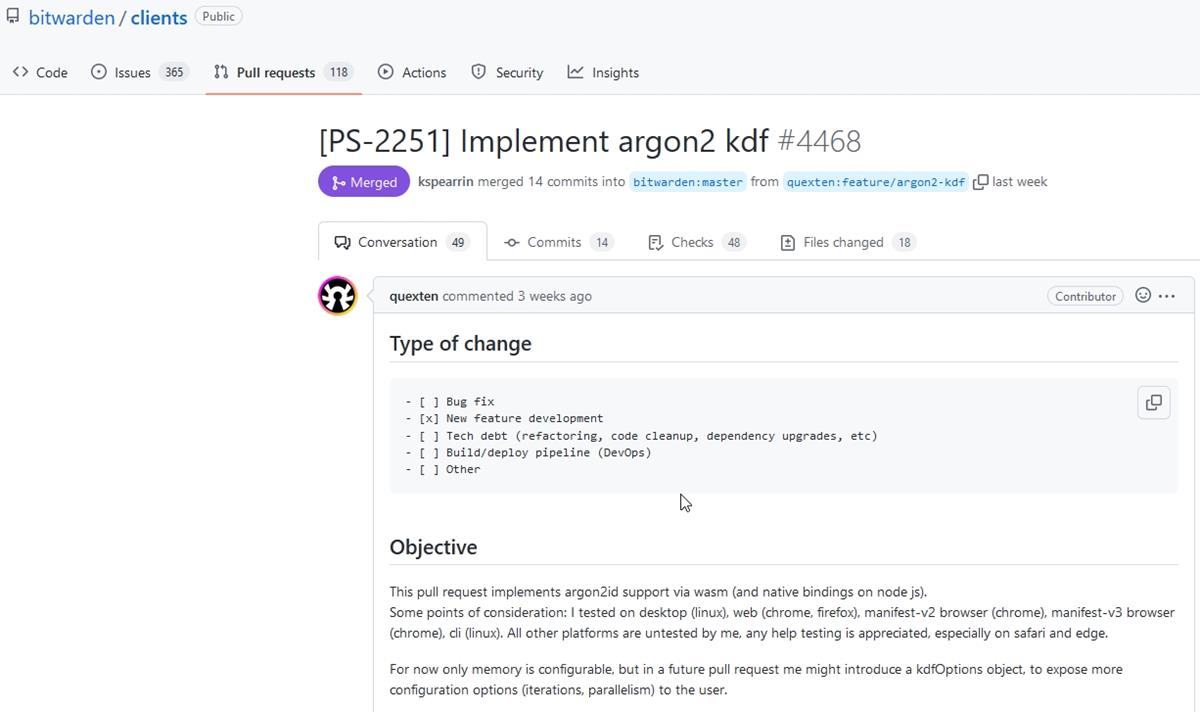
You may read more about it at its GitHub page, and on OWASP. This isn't a new request, Bitwarden users have been asking for Argon2 support since 2017 (and 2018), but the idea has only come to fruition now. Quexten, the developer who contributed the code for Argon2 support, agreed to another user's suggestion that Bitwarden would not have expedited the process now if it had not been for the recent LastPass data breach. Here is the pull request for the feature.
There are three types/versions of Argon2: Argon2d, Argon2i and Argon2id. The first one, Argon2d, is resistant to GPU based cracking attacks, but is vulnerable to side-channel attacks. Argon2i is the opposite, its strong against side-channel threats, but is prone to GPU attacks. Argon2id is a hybrid of the two, and as a result offers the best of both worlds.
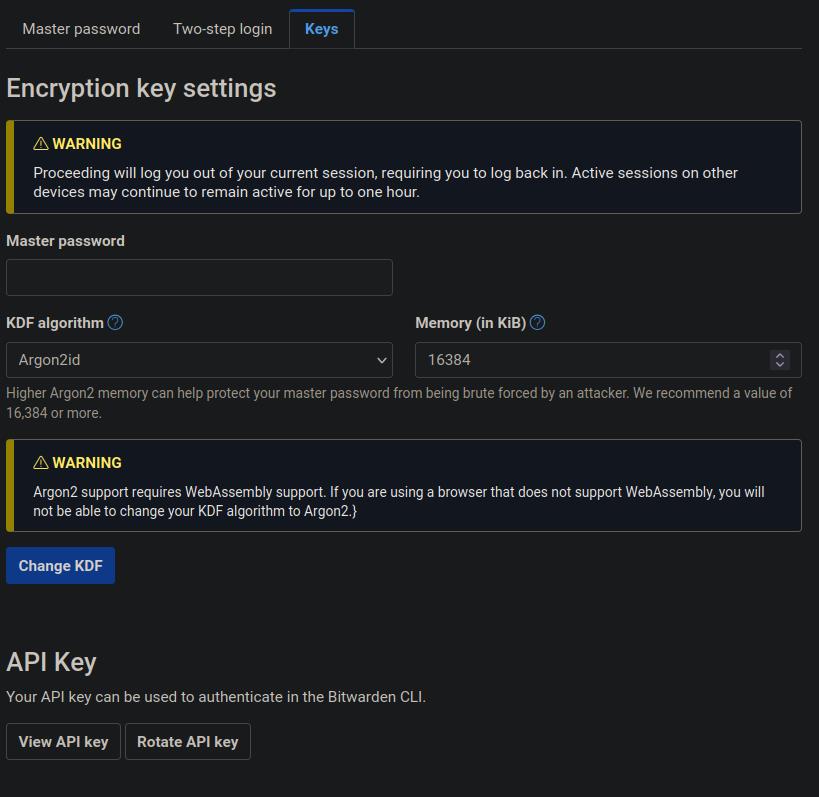
Bitwarden's implementation will use Argon2id. With PBKDF users have just one parameter that they can control, to set the number of iterations. Argon2 will offer more options, you will be able to set the number of iterations, the amount of memory to use, for example 64MB, and Parallelism lets you define the number of parallel threads to be used.
Tip: If you have KeePass, you can open the Database Settings > Security tab and check the options it has for Argon2id, it's practically the same. You can try Argon2 online at this page.
According to comments posted by Quexten at Bitwarden's community forums, the company has a 5-week release cycle, so we could expect Argon2 support to be added next month on all platforms if the tests are successful. The feature will be opt-in, and should be available on the same page as the password iteration settings in Bitwarden's web vault.


















Thanks! Everything for keeping the hackers at bay is appreciated.
Re Argon2id, it’s not the “best of both worlds”, but rather a compromise. You lose some of the side-channel-attack protection of Argon2i and some of the GPU-attack protection of Argon2d.
KeePass recommends using Argon2d, for reasons that make some sense. From KeePass documentation: “…we believe that a better protection against a really existing threat (password cracking using GPUs/ASICs is state of the art) is more important than a protection against certain side-channel attacks that may or may not become a problem on client devices in the future.”
For most users this is an academic point; all flavors of Argon2 are considered robust. But, personally, I’d use 2d.
@flerb: well-noted.
The KeePass documentation is phenomenal.
@Ashwin. Is it safe to presume you will tell us when it the feature goes live?
Yes, we are monitoring the change and will post a new article once it becomes available.