Millions of Lenovo devices affected by BIOS vulnerability
Millions of Lenovo notebooks are affected by a serious BIOS vulnerability. Lenovo informed its customers about the vulnerability on its support website this week. The company released firmware updates for some of the affected devices already and plans to release the remaining updates in early May.

Lenovo reveals on the website that several of its notebook devices are affected by three different vulnerabilities -- CVE-2021-3970, CVE-2021-3971, and CVE-2021-3972 -- that could allow attackers with elevated privileges to execute arbitrary code or disable SPI flash protections during the operating system runtime.
ESET, the security company that discovered the vulnerabilities and reported them to Lenovo, discovered that two of the vulnerabilities affect UEFI firmware drivers that were meant only for use in the manufacturing process. It appears that Lenovo did not deactivate these properly in production devices.
Affected devices and firmware fixes
The vulnerabilities affect several Lenovo device families, including Lenovo IdeaPad 3, Flex 3, L340, Legion 5 and 7, Legion Y540, S14, S145, S540, Slim 7 and 9, V14 and V15, and Yoga Slim 7 devices. The full list of affected devices is available on the Lenovo support website.
Lenovo released updated firmware versions for some of the affected products. For others, it aims to deliver firmware updates on May 10, 2022. Devices that have reached end of servicing won't receive firmware updates.
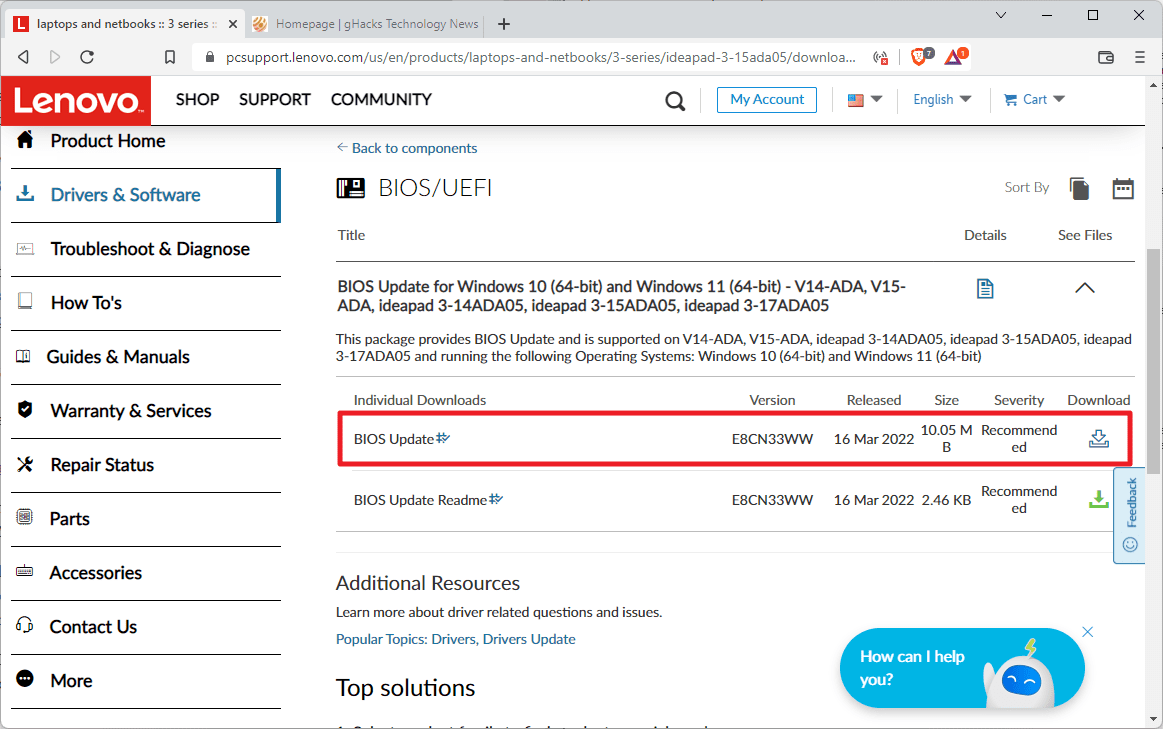
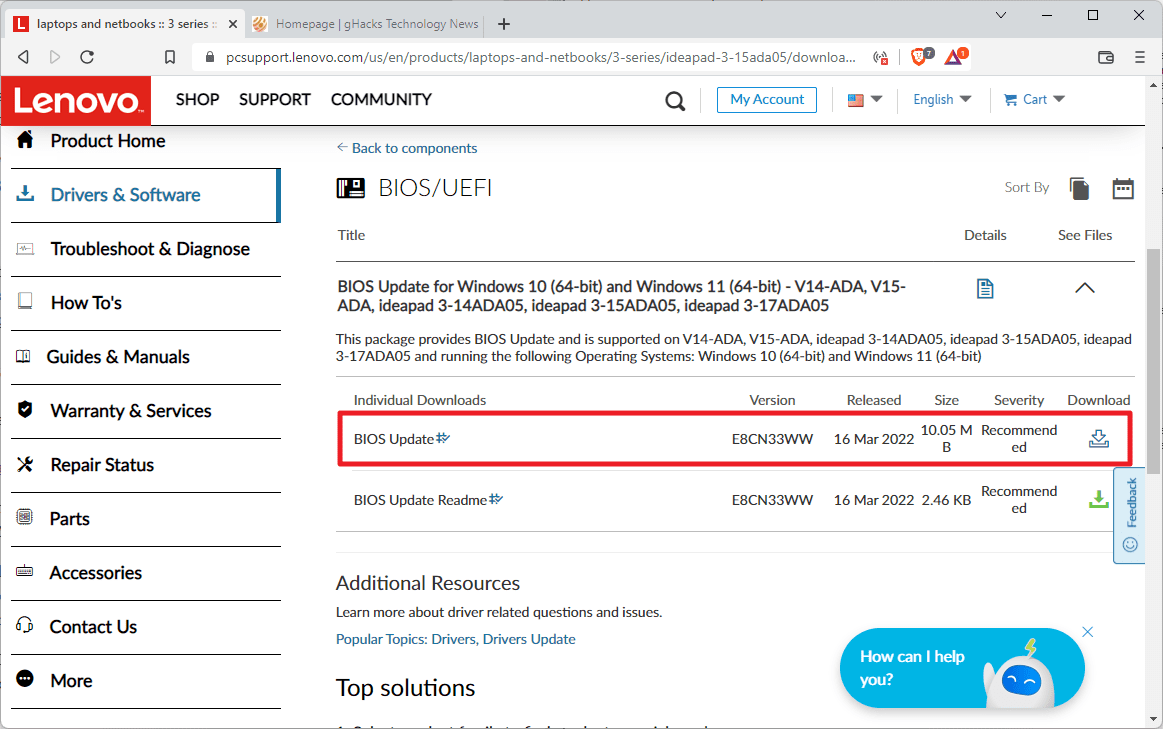
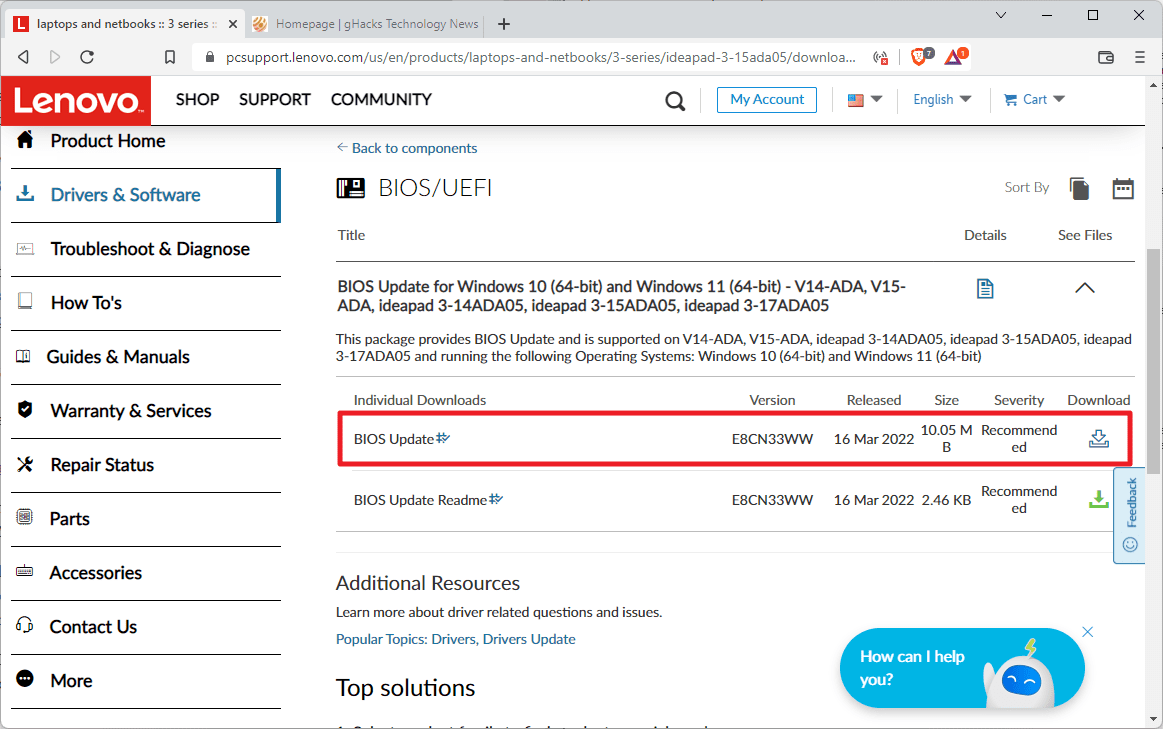
Some devices are not affected by all three of the vulnerabilities, but most are affected by all three of the confirmed vulnerabilities. Updated firmware drivers are provided by Lenovo; customers need to click on the device's support link on the Lenovo website to open the driver website.
There, they need to select BIOS/UEFI to display the available firmware updates to download the update. The support page, that lists the vulnerabilities, lists the firmware versions that contain the security fixes.
The updates can be installed directly from the Windows operating system by running the downloaded executable file. A readme file is available for each firmware file, that provides instructions on installing the update on the device.
Customers may also visit the main Lenovo support website to look up updates for their devices this way.
Analysis of the vulnerabilities in Lenovo notebooks
Security company ESET reported the vulnerabilities to Lenovo in October 2021. Lenovo confirmed the vulnerabilities in November 2021 and requested a postponing of the public disclosure date to April 2022. Lenovo published the security advisory on April 18 and ESET its findings and details a day later.
The vulnerability CVE-2021-3971 can be exploited to disable SPI protections on Lenovo devices. UEFI firmware is usually stored on the in an embedded flash memory chip on the computer's motherboard. It is connected to the processor via the Serial Peripheral Interface (SPI).
The memory is independent of the operating system, which means that it remains even if the operating system is reinstalled or another system is installed. An administrator could erase a device's hard drive, install another operating system, and the memory would not be changed by the procure. Since it is non-volatile, it is a high-level target for threat actors.
Malwares such as LOJAX, the first UEFI rootkit found in the wild, MosaicRegressor, or MoonBounce, targeted the memory in attacks.
Manufacturers created several security mechanisms to protect the SPI flash against unauthorized modifications. The primary line of defense is "provided by the special memory-mapped configuration registers exposed by the chipset itself – the BIOS Control Register and five Protected Range registers".
CVE-2021-3971 may be exploited by creating the NVRAM variable. Successful exploitation disables SPI flash write protections. With the variable set, the platform's firmware will skip the execution of code that is "responsible for the setting up BIOS Control Register and Protected Range register-based SPI flash protections".
The attacked system allows SPI flash to be modified, even when executed from non-SMM code, resulting in attackers being able to write malicious code directly to the firmware storage. SMM, System Management Mode, is used for various tasks, including the secure updating of a device's firmware or the execution of proprietary code by OEMs.
ESET notes that any Windows administrator, with the SE_SYSTEM_ENVIRONMENT_NAME privilege, may exploit the vulnerability using the "Windows API function SetFirmwareEnvironmentVariable".
The vulnerability CVE-2021-3972 gives attackers control over several UEFI firmware settings. Among them are the UEFI Secure Boot state or the ability to restore factory settings. Attackers may exploit the security issue for various tasks, including the disabling of Secure Boot on the device.
Secure Boot is part of the UEFI specification. Its main purpose is to verify boot component integrity to ensure that components are allowed to be executed. Secure boot uses databases to determine the trusted components. Usually, third-party UEFI drivers, applications and OPROMS are being verified, while the drivers on the SPI flash "are implicitly considered trusted".
The disabling of Secure Boot, and thus the disabling of its component verification process, allows any component, including those that are untrusted or malicious, to be loaded during boot. Resetting the UEFI firmware to factory defaults may have severe consequences as well, especially if it would lead to the loading of components with known security vulnerabilities.
An attacker needs to set a UEFI variable on unpatched Lenovo devices to exploit the vulnerability. A Windows administrator account with the SE_SYSTEM_ENVIRONMENT_NAME privilege is required to carry out the attack during runtime of the operating system.
The third vulnerability, CVE-2021-3970, was discovered by ESET during the company's investigation of the two other vulnerabilities. The vulnerability allows arbitrary read and write operations from and into SMRAM; this may lead to the "execution of malicious code with SMM privileges" and potentially to the "deployment of an SPI flash implant".
Closing Words
Lenovo published a security advisory, that describes the three vulnerabilities and the affected devices, and firmware updates for most affected devices. Customers are encouraged to update the device firmware immediately to protect the device against attacks targeting the vulnerabilities.
Some devices will receive the firmware update on May 10, 2022. These remain vulnerable until at least that date. Customers may want to check the support page again on the date to download and install the update on their devices.
Several Lenovo devices won't receive firmware updates. ESET recommends using a "TPM-aware full-disk encryption solution capable of making disk data inaccessible if the UEFI Secure Boot configuration changes".


















If you have a Dell, HP, Asus, Acer, Toshiba, Lenovo or any other laptop computer then you need to know about the Bios Key. The Bios key is often called a BIOS password so if you don’t know what this is, please read on.
https://www.lenovo.com/ca/en/d/deals/laptops/
As a repair technician on the front-line, I can advise that Lenovo’s latest BIOSes that are supposed to rectify the security hole, they’re bricking a lot of the laptops they are being installed on. I’ve had it go horribly wrong on a V15 and I’ve seen it on one-day-old Laptops that we have configured on behalf of the purchasers. We successfully returned it as DOA, but this proves, something is wrong, or can go wrong, with their BIOSes and it is bricking devices.
Lenovo=dirt
Dave, you hit the nail on the head and this is the extremes I had to go to, in order to fix:
https://forums.lenovo.com/t5/Lenovo-IdeaPad-1xx-3xx-5xx-7xx-Edge-LaVie-Z-Flex-Laptops/Re-Black-screen-after-BIOS-update/m-p/5159390
People have their lives on their laptops these days, family photos etc. This is really poor show and a rushed/botched attempt to close the holes too quickly at the expensive of customers.
Lenovo appear to have rushed / botched this BIOS patch, be warned. I installed last night as prompted directly by Lenovo Vantage on an Ideapad 3 17ADA05 bios update E8CN36WW. The instructions were followed to the letter. The laptop is only 18 months old cost GBP429 and is now black screened. There is no signal from HDMI to view from a secondary monitor, the Novo pin reset hole makes no difference, battery drain hard reset and windows key + Shift + ctrl + B. also does not remediate. This is beyond poor and timing co-incidentally just months outside most people’s warranty given the release date of the model. Any advice on how to fix most welcome and will try!?
Is this why I have a trolley full of Lenovo laptops that just constantly restart pending a firmware update that never installs?
Martin,
Thanks for posting this incredibly useful and informative story.
All I wanted was the ability to physically write-protect the firmware on my motherboard in order to prevent it from being replaced by an attacker in the event that I happen to run a malicious program. Instead, the industry has made the boot process so overly complicated that you can now play Doom right in UEFI without even loading an OS.
https://doomwiki.org/wiki/Doom_UEFI
It’s like, I ask for a door lock that actually works, and in response, they just make a more complicated door that still can’t be locked correctly.
serial nuber ideapad 3-15IILO5
my lenovo not turn on how to upgrade or flash the bios
does not start on any system crashes on the lenovo logo even with live systems on a usb key I have already set the default bios settings remove and put back the RAM even change ram my lenovo not turn on how to upgrade or flash the bios
with the boot on a key one for example is this possible
I have a Lenovo Laptop and it’s on the list of vulnerable computers. But since my laptop is out of warranty, they didn’t bother to inform me via email and the Lenovo software also kept silent. But a manual search turned showed the BIOS update and it installed no problems. As to another chip that MS requires, all I have to add is when will the governments of the world stop allowing the Big Five from having that much sway over the hardware?
The BIOS is a very important or even the most important piece of the hardware. I dislike so much the way that the companies inform the users about the BIOS updates and also I dislike a lot the lack of criteria to set the updates in a right way to be understandable. For example, HP offers its BIOS updates with not too much sense, and the last days version F.61-rev.A was available, while today only version F.54-rev.A is available. Where is the version F61? I updated to F61 and now I am thinking where is the the problem that made HP to delete the latest version. However, after reading the article, Lenovo seems to have more sense to publish their updates. Thanks for the article! :]
“Secure Boot”, what a joke. Soon they’ll roll out “Super Duper Double Secret Secure Boot”, and charge the sheeple an extra $100 each to keep them safe from all the evil l33t haxxors.
Microsoft already has a new super-duper Double Secret Secure Boot chip called : Pluton processor which it will force OEMs to use.
https://www.microsoft.com/security/blog/2020/11/17/meet-the-microsoft-pluton-processor-the-security-chip-designed-for-the-future-of-windows-pcs/
Not only that but AMD will have it in their next CPU gen. Intel will also in 14XXX series afaik. Soon, no one will be safe from cloud based firmware updates with 0 user interaction.
5G connectivity will also boost this on mobile devices and everything else in your smart home in the future. You heard it here first!
>cloud based firmware updates
I think Microsoft Surface lineup is already part of the devices capable of doing that, at least Microsoft states so, yet I’ve never seen it on my SP7. The only way to update its firmware is to download the latest driver pack from Microsoft, install it, then restart. It should update the firmware on the next boot, but I’ve never seen it doing this on its own via WU, and I even ran W11 on it for a few months. I honestly thinnk it’s too risky, people will just force shut down the device and may brick it.
Intel will integrate Pluton in the 14th generation already? So, they will skip it in Raptor Lake yet and postpone it for another year? Fall 2023?
Probably, and then 50% of the now “computer meets requirements” for Windows 11 will not meet the requirements for Win 11 or Win 12.