Google improves Site Isolation in Chrome 77, adds it to Android
Google rolled out the security feature Site Isolation back in 2018 when it released Chrome 67 to the public. Site Isolation was limited to desktop versions of the Chrome web browser back then. Site Isolation limits render processes to individual sites which means that sites don't share render processes anymore when the feature is enabled. The initial release targeted Spectre-like attacks that could leak data from render processes.
Google Chrome 77 improves Site Isolation on the desktop and introduces Site Isolation in Chrome for Android.
Android users could enable Site Isolation in Android already using experimental flags but Chrome 77 enables the feature automatically for sites where users enter passwords.
Google made the decision to limit Site Isolation to sign-in pages on Android because global activation could impact the user experience on devices. Site Isolation comes with an overhead especially when it comes to memory usage.
Google revealed in 2018 that Site Isolation would require an additional 20% of memory on average when enabled on the desktop. The limitation to sign-in pages on Android and the fact that render processes on Android are shorter-lived and smaller reduces the memory overhead to about 3-5%.
Google enabled Site Isolation for 99% of all Android users who run the new Chrome version. The 1% is held back for monitoring and improving performance of the solution. The feature is only enabled by default on Android devices that have 2 Gigabytes of system memory or more.
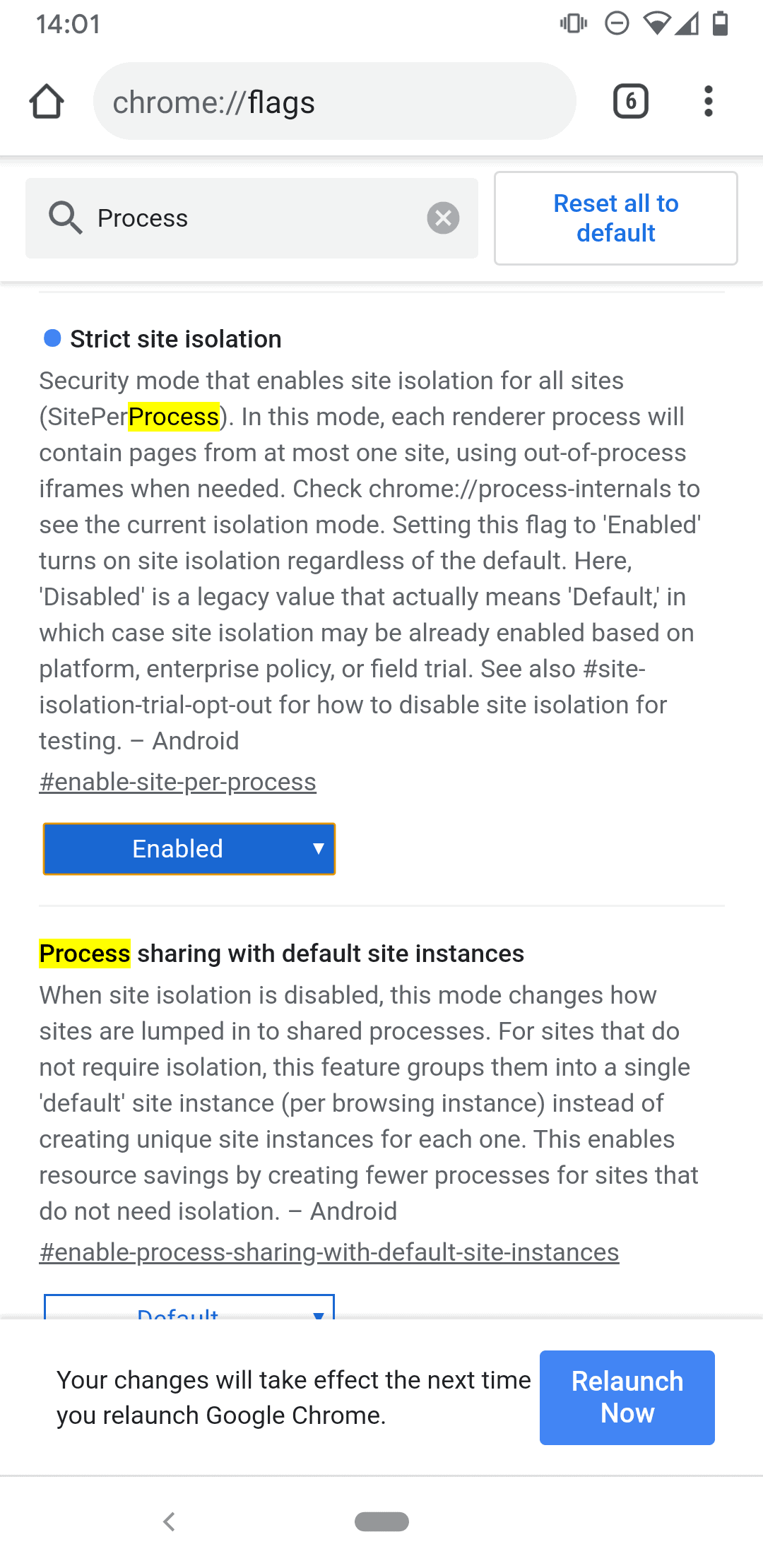
Tip: Android users who want full Site Isolation on their devices can enable it by loading chrome://flags/#enable-site-per-process in the mobile browser and setting the preference to Enabled. Full Site Isolation improves security but comes with a larger memory overhead.
Google has plans to extend the default Site Isolation behavior in Chrome for Android in the future.
In the future, we plan to add support for more ways of detecting when a site should be protected by Site Isolation. For example, we're working on allowing website operators to opt in any site to Site Isolation, without requiring user login.
For now, it may be a good idea to enable the feature on devices that are powerful enough to handle it.
Desktop Site Isolation improvements
Chrome 77 introduces new Site Isolation capabilities in desktop versions of the web browser as well. The initial launch of Site Isolation targeted Spectre-like attacks. The upgraded version of Site Isolation in Chrome 77 is capable of handling severe attacks according to Google that come into play when the render process is fully compromised.
For example, suppose an attacker discovered and exploited a memory corruption bug in Chrome's rendering engine, Blink. The bug might allow them to run arbitrary native code within the sandboxed renderer process, no longer constrained by the security checks in Blink. However, Chrome's browser process knows what site the renderer process is dedicated to, so it can restrict which cookies, passwords, and site data the entire process is allowed to receive. This makes it far more difficult for attackers to steal cross-site data.
Google lists several types of sensitive data that the upgraded Site Isolation in Chrome 77 protects against when render processes are compromised:
- Cookies and passwords can only be accessed by processes of the corresponding site.
- Sensitive resources are protected by Cross-Origin Read Blocking; resources "labeled with a Cross-Origin-Resource-Policy header are also protected".
- Render processes may only access stored data based on the process' site lock.
Google worked with extension developers in the past to reduce the number of exceptions where protections would not apply. The "affected Chrome user population" that had extensions with exceptions installed has been brought down from 14% to 2%.
Closing Words
Android users who run Chrome should expect a slightly higher memory usage than previously when they use the browser. Those who enable full site isolation in Android may notice the same overhead as on the desktop. Mozilla started to test Site Isolation in Firefox 70.
Now You: Do you run Chrome or another browser?



















Reminds me of how there was a Russian card stealing trojan that would helpfully clean the computer of other viruses upon surreptitious install…