Disable WebUSB and WebBluetooth in Google Chrome
Web browsers support an increasing number of APIs and features, and there does not seem to be an end in sight to that.
Recent additions to Google Chrome, the WebUSB and WebBluetooth APIs, allow sites to interact with devices connected to the device the browser is run on.
While there are certainly cases where this may be useful, it is sometimes the case that the introduction of new features has unforeseen consequences.
In the case of WebUSB and WebBluetooth, it is opening the doors for sophisticated phishing attacks that could bypass hardware-based two-factor authentication devices such as some Yubikey devices.
Security researchers demonstrated recently that the WebUSB functionality of the Google Chrome web browser can be used to interact with two-factor authentication devices directly and not Google Chrome's API (U2F) designed for that purpose.
The attack bypasses any protection that two-factor authentication devices offer that are susceptible. Devices need to support protocols for connecting to a browser other than through U2F for the attack to work and users need to interact with the phishing site for the attack to be carried out successfully.
Chrome displays a prompt when a site tries to use WebUSB or WebBluetooth. The user needs to allow the request, and type or paste the account's username and password in designated forms on the site.
While that puts a barrier in place, one that requires user interaction before it can be carried out, it still does highlight that new features may open up new possibilities for abuse.
Users need to pay attention to permission dialogs that the browser displays to them. Attack sites could be designed in a way to provide users with reassurance that such permission prompts are necessary for functionality. While it is unclear how many users would fall for that, especially those using hardware two-factor authentication devices, it is almost certain that some would.
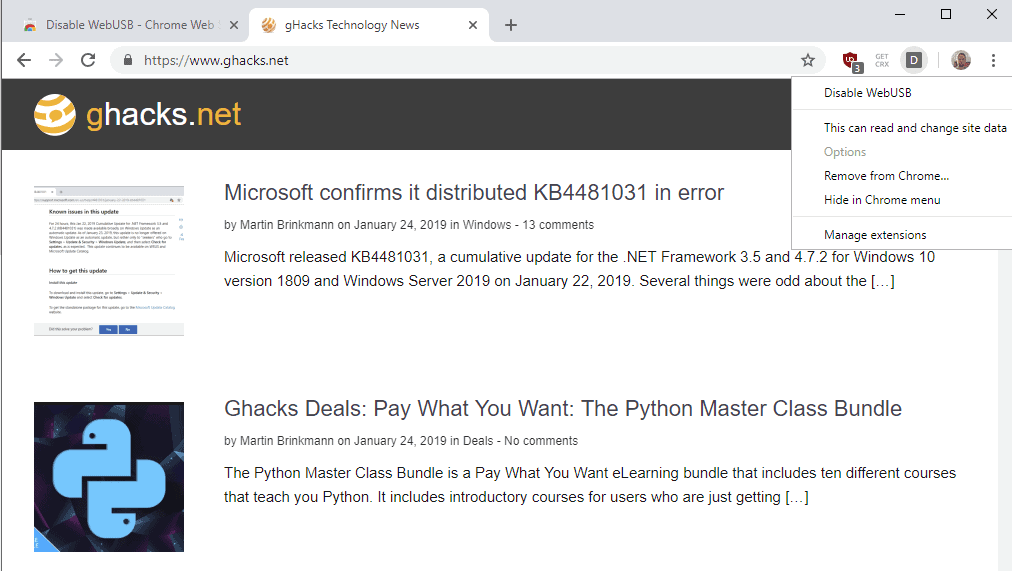
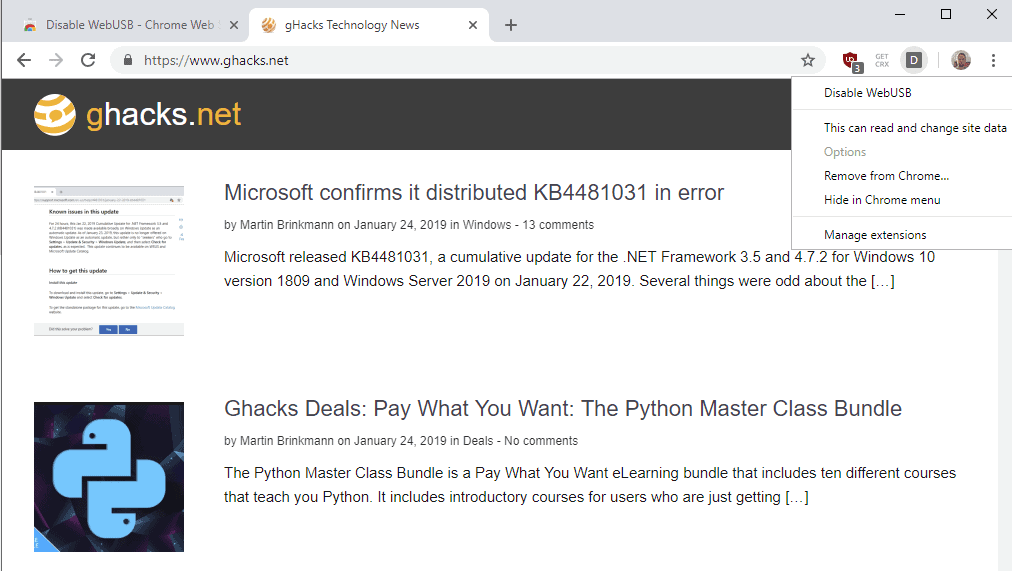
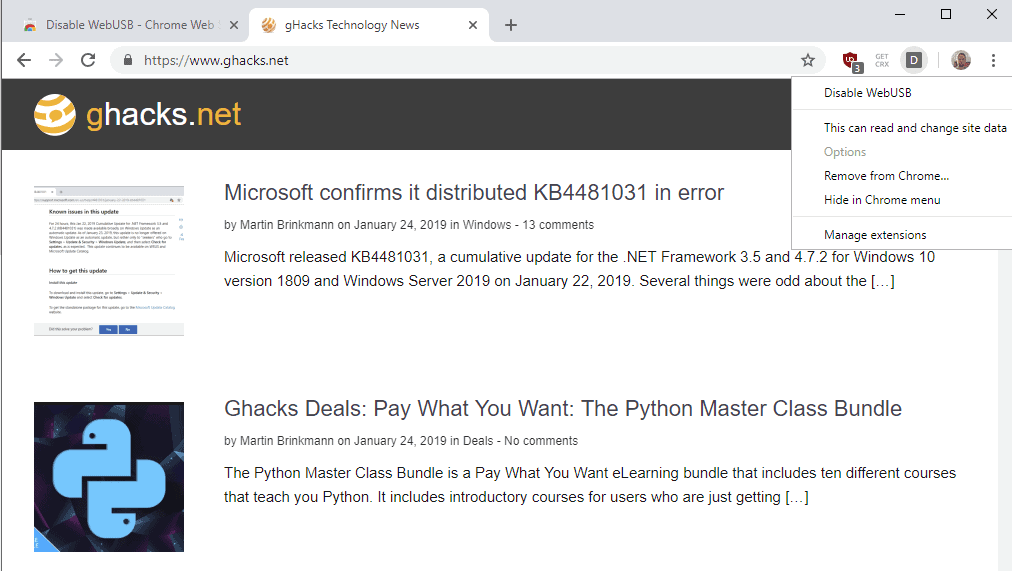
The two open source browser extensions Disable WebUSB and Disable WebBluetooth address the issue directly; they block the APIs in the browser so that they may not be abused. It should be clear that these extensions will block any interaction with these APIs; it does not distinguish between good and bad requests.
If you never use WebUSB or WebBluetooth, you may want to consider installing the extensions for that extra bit of security. The extensions run silently in the background and block any attempt to use the WebUSB or WebBluetooth API.
Now You: Do you disable certain browser features?



















How effective are these extensions? I remember back in the day when WebRTC was the thing to look out for and Chrome didn’t have a way to disable it; tons of extensions popped up claiming they could indeed disable it but web devs/security researchers kept figuring out ways to bypass these extensions, such as creating a new frame in the page where the extension wouldn’t have injected its content script into.
Ohhhhh..This could never be abused ….right?
Right?
I cannot believe how devious people are.
“Do you disable certain browser features?”
I do not want web sites to be able to directly access any of my computer’s hardware at all, so I disable everything I can that would allow such access. That used to be so much easier before HTML5.
How it works, not that it needs to exist, but…
https://developers.google.com/web/updates/2016/03/access-usb-devices-on-the-web
This is somehow even more condescending than Zuckerberg.
This is why Chrome will always suck compared to Firefox.
Something like this can usually be solved by changing a switch in about:config in Firefox, whereas, you need to install a god-d***** extension to “fix” it in Chrome. Each extension requires more memory for every tab forever.
Chrome://flags is less numerous than Firefox’s about:config & Google can retire/remove “experiments” in Chrome://flags whenever they desire without warning/notification.
And I’m not even talking about the amateur programming done by the Chromium team. The Chromium team is the only programming team that too stupid to install 64-bit software in the Program Files directory (still installed in Program Files (x86), smh).
@NotAnonymous: “Google can retire/remove “experiments†in Chrome://flags whenever they desire without warning/notification.”
Mozilla can (and does) do this with about:config settings as well. about:config is not really intended to be used as people are using it currently. That’s one of the reasons why Mozilla refuses to provide a list of what the available settings are and what they do.
It doesn’t seem like you need an extra add on to disable USB, since you can set it to “do not allow any sites to access USB devices” in settings.
Does Firefox include these APIs as well?
Maybe this: security.webauth.*
https://security.stackexchange.com/questions/185688/webauthn-configuration-differences-in-firefox
https://krebsonsecurity.com/2018/07/google-security-keys-neutralized-employee-phishing/comment-page-3/