Google: timeline for distrusting all Symantec Certificates in Chrome
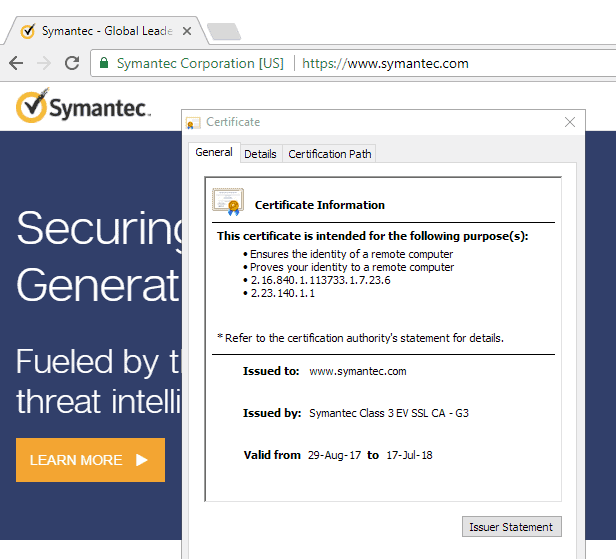
Google published a timeline recently on the Google Security blog which highlights the timeline for dropping support for Symantec-issued certificates in Chrome.
The company plans to drop full support in Chrome 70, but will distrust certificates that were issued before June 1, 2016 as early as March 15, 2018 (Chrome 66).
The core of the issue surrounding Symantec certificates -- the business operates under brand names such as VeriSign, Thawte, Equifac, RapidSSL or GeoTrust -- is that Symantec "entrusted several organizations with the ability to issue certificates without the appropriate or necessary oversight" according to Google.
Symantec was aware of these security deficiencies, and incidents in the past showed just how bad it was. In 2015 for instance, certificates were created covering five organizations including Google and Opera without the knowledge of the organizations involved.
Symantec came to an agreement with DigiCert under which DigiCert will acquire Symantec's website security and PKI solutions business.
Google plans to remove trust from all Symantec-issued certificates in Chrome in the coming year. The company published a timeline that highlights the most important dates of the process.
- October 24, 2017 -- Chrome 62 Stable -- Chrome highlights if a certificate of a site will be distrusted when Chrome 66 gets released.
- December 1, 2017 -- DigiCert's new infrastructure will be "capable of full issuance". Certificates issued by Symantec's old infrastructure from this point forward will cease working in future updates. This won't affect certificates issued by DigiCert.
- March 15, 2018 -- Chrome 66 Beta -- Any Symantec issued certificate before June 1, 2016 is distrusted. Sites won't load but throw a certificate alert instead.
- September 13, 2018 -- Chrome 70 Beta -- Trust in Symantec's old infrastructure is dropped entirely in Google Chrome. This won't affect DigiCert issued certificates, but will block any site that uses old certificates.
Chrome users cannot really do anything about this, as website operators need to switch to a certificate that is still trusted by Google as early as March 14, 2018. The only option that users of the browser have is to let website operators know about certificate issues should they not be aware of this.
Mozilla will match the dates proposed by Google according to a post by Gervase Markham on the Mozilla Dev Security Policy group.
Webmasters who run sites with Symantec certificates need to add new certificates to their web properties before the deadline to ensure continued access to those properties. One option that webmasters have is to use Lets Encrypt which offers free and automated certificates.




















So where to go for trusted certificates? Looking for a one-stop-shop for all our needs – codesigning, SSL, wildcard… but most of the issuers I find seem to be problematic.
Any good recommendations on where to go?
Question about the “highlights” mentioned above. I tried Chrome62 beta to see what would show in browser with a Symantec issued cert (pre-7/16) and saw no noticeable warnings or “highlights.” Is this a difference between beta/stable? If not, what am I missing that potential customers can/will see?
TIA
Beta is still a work in progress, so it may not have been implemented yet.
How can I remove old Symantec certificates in Firefox if I don’t want to wait until 2018?
@someone
There is a cert8.db file in your profile folder (profile can be accessed from the about:support page), deleting that file will remove a ton of certificates. I’m thinking they are mostly intermediate certificates that are automatically added to the browser when visiting some websites. Some will be from Symantec, some from Comodo which is another problem-child and also some from other authorities. You can view the current certificates at Menu/Options/Advanced. I occasionally delete the cert8.db (once every month or two) and its never caused me any problems. I never save the file but others might want to save it to the desktop or somewhere for a day or two just to see if anything gets broken. When the cert8.db file is deleted the file will be recreated with the next browser startup. The new file will usually be like three times smaller when I do it. I don’t know enough about it to give examples of any scenarios that will be impacted by deleting the file, I just know it works for me. ;)
“This file stores all your security certificate settings and any SSL certificates you have imported into Firefox.” – Mozilla
@Richard Allen
I think the Symantec certificates referred in the article are built in and are not affected by deleting cert8.db which stores intermediate certificates and certificate exceptions that user manually has added.
Did you read this part of the article?
“Mozilla will match the dates proposed by Google earlier according to a post by Gervase Markham on the Mozilla Dev Security Policy group.”
I wonder if Mozilla, Apple and Microsoft will follow suit.