Watch out for that Chrome update - Spoofed websites spreading
This is not a new problem, but it is an ever-growing one. Whenever something is popular the underbelly of the web tries to corrupt it for personal gain, and yesterday's Chrome update is no different. Almost immediately upon release, the spoof sites began popping up to take advantage of unsuspecting users.
According to Net Security "Malware peddlers are taking advantage of yesterday's release of the latest version of Google Chrome and have already set up a spoofed page of the initial rollout page in order to deliver their malicious wares".
The problem is that many users pay no attention to a URL in their browser address bar. Over the years, that has allowed countless attacks to be carried out by placing a look-alike site at, for example, PayPaI.com as opposed to PayPal.com.
If, for some reason, the fake URL does not jump out at you then you should be able to rely on Chrome itself to detect the malicious software when the file attempts to download.
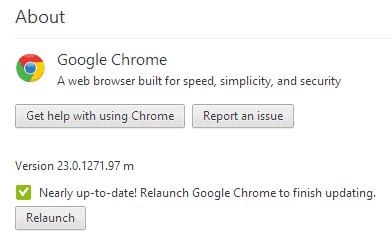
In the vast majority of cases Google will push out Chrome updates automatically to every browser. If you do not receive it then you can click on "Tools" and choose "About Chrome" and the browser will begin checking for, and installing, any updates available. If you are installing Chrome for the first time then just make sure you head to the official Google site.
The security bulletin goes into very little detail about how this may be happening to users, but my guess would be that it is less prevalent than what is being portayed. With auto-updating, it is likely that the problem may be arising from ads appearing to users that claim to link to an update that they need. Given that the browser tends to still be used by the more tech-savvy users it may be less of problem than this bulletin makes it appear. Still, it is worth keeping in mind because even the best of us can get suckered in from time to time.
Advertisement

















“to a URL in their browser menu bar. ” I’ve NEVER seen an URL in my menu bar. Mine’s in my *address* bar. #typo
Thanks, corrected.
The fake update installs Zeus botnet which is capable of stealing banking credentials on user Windows PCs.
http://www.gfi.com/blog/fake-google-chrome-updates-return/?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+SunbeltBlog+%28GFI+Labs+%28OLD%29%29